- Home
- Play books
- Detection and response to alternate data streams
Detection and response to alternate data streams
In this page
Playbook Description
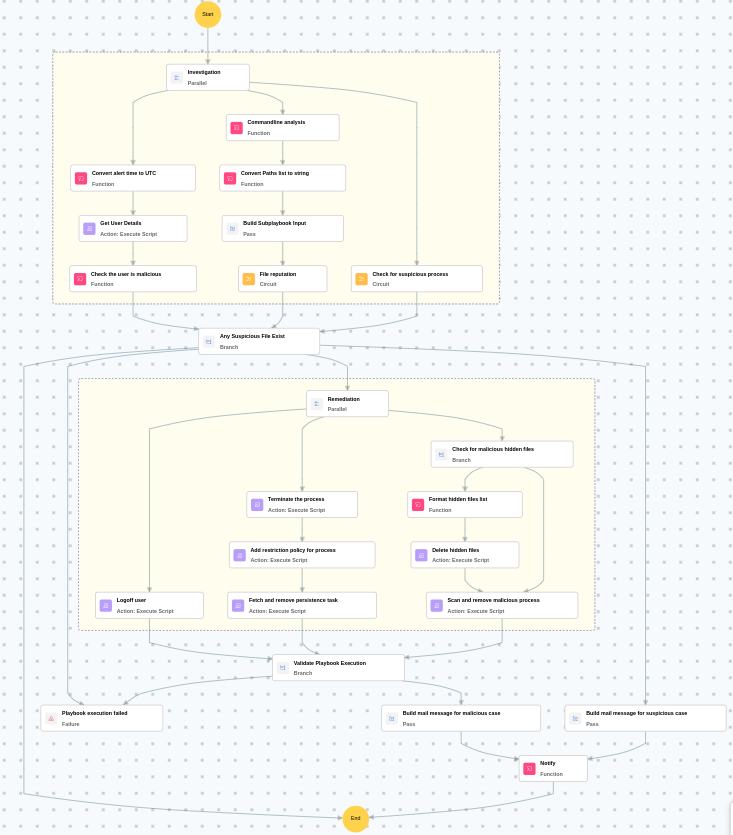
This playbook detects and responds to alternate data streams by determining if the command line is malicious and evaluating user behavior and process reputation. If flagged, it terminates processes, deletes hidden files, scans for malware, removes persistence, blocks processes, and logs off compromised users.
MITRE ATT&CK mapping
| Tactics | Techniques | Sub-techniques |
|---|---|---|
| Defense Evasion(TA0005) | Obfuscated Files or Information(T1027) | Steganography(T1027.003) |
MITRE D3FEND mapping
| Tactics | Techniques | Sub-techniques |
|---|---|---|
| Evict(D3-Evict) | Object Eviction(D3-OE) | File Eviction(D3-FEV) |
Playbook input type
Alert
Prerequisites
- PowerShell Version 5.1
- Execution Policy
- Software Restriction Policy (SRP) must not be disabled on the target host
- Provide Local Administrator/Domain Administrator privileges.
- Windows Credentials - Go to Settings -> Devices -> Windows Devices. Provide/update the credentials of the respective Windows device with admin privileges.
Dependencies
Utility functions:
- utility_convertTimeToUTC
- windows_detectMaliciousUser
- windows_commandLineAnalysis
- utility_convertToString
- utility_sendMail
Scripts
| Script Name | Description | Arguments |
|---|---|---|
| TerminateSession.ps1 | Logs off one or more user sessions using logoff , with optional RDP-only filtering by remote IP | UserNames |
| FetchPersistenceEntries.ps1 | Scans for persistence mechanisms including scheduled tasks, registry Run/RunOnce keys, startup folder entries, and services to identify potential malicious persistence | - |
| AddSoftwareRestrictionPolicy.ps1 | Creates Software Restriction Policy (SRP) rules in the Windows registry to block execution of programs from specified paths. For each path, it checks if an SRP rule already exists — if so and it's not set to "Disallowed", it updates the existing rule; otherwise it creates a new GUID-keyed rule under HKLM:\SOFTWARE\Policies\Microsoft\Windows\Safer\CodeIdentifiers\0\Paths. Enables SRP enforcement (TransparentEnabled=1, PolicyScope=0) on each run. | RestrictedPath |
| FetchUserDetails.ps1 | Fetches detailed user information (password expiry, group memberships, admin status) for both domain (AD) and local users | Name |
| FetchAndRemoveProcess.ps1 | Scans temporary directories for suspicious script files (.ps1, .bat, .vbs) containing credential-related keywords, kills any processes running those scripts, and deletes the files | AdditionalKeywords |
| CheckAndRemoveFiles.ps1 | Checks for suspicious or malicious files in specified paths and removes them if found | FolderPath |
| StopProcess.ps1 | Stops processes by PID or file path. Supports hex PIDs and comma-separated inputs. Skips protected PowerShell executables. | ProcessIdentifiers |
Sub playbooks
- Windows - File enrichment
Execution workflow
Investigation:
- Analyzes the command line for suspicious patterns, URLs, or file paths.
- Executes the "Windows - File enrichment" sub-playbook.
- Retrieves the user details.
- Checks if the user is malicious.
Decision logic:
- Proceeds to remediation based on the following conditions:
- The file or process reputation indicates high risk.
- The user is flagged as malicious based on behavior analysis.
- If suspicious but not confirmed malicious, sends a notification for manual review and stops further actions.
- If no malicious indicators are confirmed, the playbook ends with no further actions.
Remediation:
- Logs off user.
- Terminates the process.
- Adds the restriction policy for the process.
- Fetches and removes persistence task.
- Checks for malicious hidden files.
- Deletes hidden files.
- Scans and removes malicious process.
- Validates that all remediation actions are completed successfully.
- Builds the notification email with remediation details and findings.
- Sends a notification email regarding the actions taken and required next steps.
Post execution procedure
- Review the deleted hidden files and removed processes for further forensic analysis.
- Check for any remaining alternate data streams on the system.
- Investigate whether the attack resulted in data exfiltration or lateral movement.
- Confirm that software restriction policies are active and effective.
- Notify the affected user about the actions taken.


