- Home
- Play books
- Sophos Central - High-risk endpoint verification
Sophos Central - High-risk endpoint verification
In this page
Playbook Description
This playbook retrieves the impacted endpoint ID from Sophos Central to fetch recent events and file hashes, which are then added to the blocklist. It then assesses if the endpoint is of high-risk and not on the user-defined critical server list to proceed with isolation. If the endpoint is critical, the playbook automatically alerts the user via email.
MITRE ATT&CK mapping
| Tactics | Techniques | Sub-techniques |
|---|---|---|
| Defense Evasion (TA0005) | Impair Defenses (T1562) | Disable or Modify Tools (T1562.001) |
MITRE D3FEND mapping
| Tactics | Techniques | Sub-techniques |
|---|---|---|
| Process Eviction (D3-Evict) | D3-PE | Process Termination (D3-PT), Host Shutdown (D3-HS) |
Playbook input type
Alert
Prerequisites
API access with below scopes: Token
Playbook creation input
- protectedEndpointGroupName - Name of the endpoint group that is protected
- sophosConnection - Name of the Sophos Central connection
- tenantId - Unique identifier of the tenant within the Sophos environment.
- recipientEmail - Email address where notifications will be sent
- dataRegion - Region where the tenant's data is stored or processed
Dependencies
Extensions - Sophos Central
- sophoscentral_listEndpoint
- sophoscentral_getEvents
- sophoscentral_addBlockedItem
- sophoscentral_addIsolationEndpoint
Utility functions
- utility_filterAndMatchEvents
- utility_extractFieldFromList
- sendMail
- utility_validateResponses
Connections
- Sophos Central connection - Need to connect sophos central using OAuth 2.0 connection with clientId and client secret.
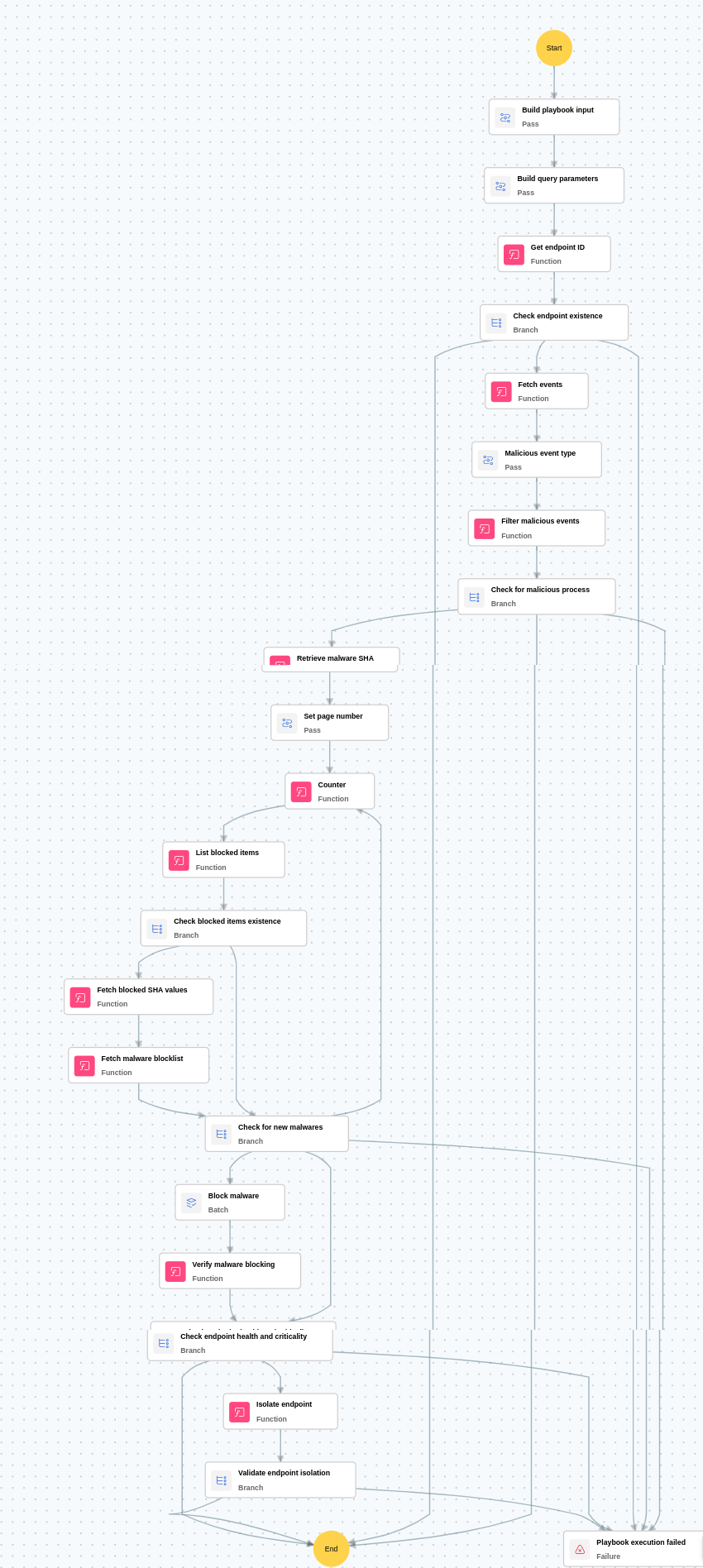
Execution workflow
Investigation:
- Gets the Sophos Central endpoint ID using the endpoint name and IP address.
- Fetches the last 1000 events from Sophos Central.
- Filters the events by endpoint ID and checks for malicious event types from the user-editable list.
- Extracts the file hash from the event data if a malicious event is found.
- Checks the endpoint health status in Sophos Central.
Decision logic:
- Proceeds to remediation if malicious events are detected.
- Proceeds to isolation and notification if the endpoint health status is bad and malicious events are detected.
- Skips remediation if no malicious events are found and the endpoint health status is normal.
Remediation:
- Adds the identified malicious file hash(es) to the Sophos Central blocklist.
- Isolates the endpoint from the network if the health status is bad and malicious activity is confirmed.
- Sends an email notification to the user informing them about the isolation action taken.
Post execution procedure
- Monitor for re-enroll attempts: Set alerts for repeated MFA enrollments, especially after recent suspicious activity.
- Audit account recovery settings: Ensure recovery options (email, SMS, etc.) are secure and not abused for bypass.
- Review all enrolled factors post-incident: Validate all MFA methods linked to the affected user to ensure no unauthorized factors remain.
- Handling false positives: If this alert is confirmed as a false positive, revert all associated remediation steps.
- Unblock non malicious IPs.
- Notify the user to enroll the required factor.


