Windows App Management
Windows mobile devices and machines form the crux of corporate productivity, especially with more organizations using both mobile devices and machines, as a part of the corporate workforce. Installing and updating apps turns out to be one of the most tedious tasks for IT admins, as they need to manually distribute the app and have it installed. MDM fully eases this process, by letting you distribute the app to multiple devices through groups and have it installed silently without any user intervention. MDM lets you manage:
- Windows application software (for machines), by adding the requisite MSI packages.
- Windows Business Store apps, by using Azure domain account to intgerate Windows Business Store with MDM.
- Enterprise apps using Code Signing Certificate (CSC)
Managing MSI software applications
You can distribute and install software on Laptops, Desktops and Surface Pro tablets by adding the MSI package to MDM. You need to add the MSI package to MDM server and provide the relevant details. The added MSI package initiates software installation on the machines, after distribution. This is supported only for Windows 10.
Distributing MSI software to Laptops, Desktops and Surface Pro tablets
Follow the steps given below, to add an MSI package to the App Repository:
- On the MDM server, navigate to Device Mgmt and select App Repository.
- Click on Add App and select MSI Software. For MSI source, provide the software MSI package file on which the requisite details gets automatically pre-filled. If you're using MDM On-Premises, go directly to Step #4.
- In case you're using MDM Cloud, the requisite details are to be manually specified. To know information such as MSI Product Code, MSI version etc., you need to download this PowerShell script . Once downloaded, open Command Prompt and run the following command:
PowerShell -ExecutionPolicy Bypass -NoLogo -noninteractive <path_to_the_downloaded_powershell_script > -Path <path_to_the_MSI_file > -Properties "ProductCode,ProductVersion,ProductName"
Once the above command is run, you'll get a JSON file containing all the requisite details, which is then to be specified in MDM. You can also use third-party software Orca MSI editor to achieve the same. - You can also optionally specify Command Line Args, which specifies the additional setup for the MSI installation. Assuming the package is to be installed as an Administrator, you can provide the Command Line Arg /a. To know more regarding Command Line Args, refer to this.
- After providing the other required details, click on Save. Now, this software has been added to the App Repository and is ready to be distributed to machines and it can be installed silently as explained here.
Managing Store Apps
MDM lets you distribute free Store apps to Windows 10 mobile devices, laptops, desktops and Surface Pro tablets. You need to integrate the Windows Business Store with MDM, by adding your Azure domain account after which all the apps purchased using the particular account gets added to the MDM App Repository automatically.
- Microsoft will deprecate Windows Business Store soon.
- You will no longer be able to add Windows Business Store apps to the App Repository and distribute them to devices.
- Managing In-house apps and Windows Business Store apps that are already present on the devices will not be affected. Learn more
Integrating Business Store with MDM
You need to integrate the Windows Business Store with MDM, for installing Store apps on managed devices through MDM. Follow the steps below for integration:
- On the MDM server, navigate to click on Device Mgmt and select App Repository, from the left pane. Now, click on the Windows Apps tab.
- Click on the Login Now button, on which you will be redirected to the Microsoft Azure Website. Login with your Azure domain admin account details.
- Click on Accept, to provide MDM with requisite permissions needed for Business Store integration. On clicking, you will be redirected back to the MDM server to activate the ME MDM app, which is done to authorize MDM managing your Business Store.
- To authorize ME MDM app, go to Microsoft Business Store and login, if need be. If you don't have an account with Business Store, you can create on free of cost. Navigate to the Management tools section and click on Add management tool.
- Search for ManageEngine MDM if you're using MDM On-Premises or ManageEngine MDM Cloud Admin if you're using MDM Cloud. Select the appropriate application and click on Add, to add it to the list of management tools. Now, click on the Activate option present under Action, against ME MDM.
- Once done, go back to the MDM server and click on Finish Integration. Now, all apps previously purchased in Business Store get automatically synced with MDM. Any future purchases will get automatically added during the daily scheduled sync or can be added immediately by using the Sync Now option. The synced apps get added to the App Repository, ready for distribution to groups and devices which can also be silently installed as explained here.
Automatic distribution/installation of ManageEngine MDM app
ManageEngine MDM app is required to be present on the devices to view distributed content, terms of use and the organization's privacy policies. The admin can choose to silently install the ManageEngine MDM app on devices or allow the user to install the app on the device as mentioned below.
- Integrate MDM with Windows Business Store, search for the ManageEngine MDM app and click Get the app.
- The admin or any technicians with permission to enroll devices can send an app enrollment mail to the user. The user can then follow the instructions available to manually install the ManageEngine MDM app into the device
If you are using MDM Cloud, ManageEngine MDM app can be installed in the devices only by integrating with Windows Business Store
Managing Enterprise Apps
In addition to Store apps, a lot of organization use enterprise apps, customized to suit their needs. These apps cannot be usually downloaded from the Business Store, thus making it difficult for the employees to download and/or update these apps. MDM eases this process by letting IT administrators install and update the enterprise apps silently on the devices. You can distribute enterprise apps, by adding Code Signing Certificate (CSC).With MDM, admins can silently distribute enteprise apps in the following formats: .xap, .appx, .appbundle, and .msix. To test and deploy enterprise apps on Windows 10 devices seamlessly using multi version management, refer to this link.
Code Signing Certificate(CSC)
In case you need to distribute apps only to Windows 10 devices, you can use third party CA-signed certificates or self-signed certificates to sign the app. In case you're using CA-signed certificates to sign the app, ensure you upload the CA root certificate on the MDM server. Self-signed certificates are auto-generated when building a Windows enterprise, using Visual Studio. You can navigate to the output location to obtain the certificate and upload it on MDM server. Ensure the CSC uploaded is the .cer file for the certificate used to sign the MSIX app.
Generating/Using CA-signed/self-signed certificates
To sign the enterprise app with either CA-signed certificate or self-signed certificate, follow the instructions given below:
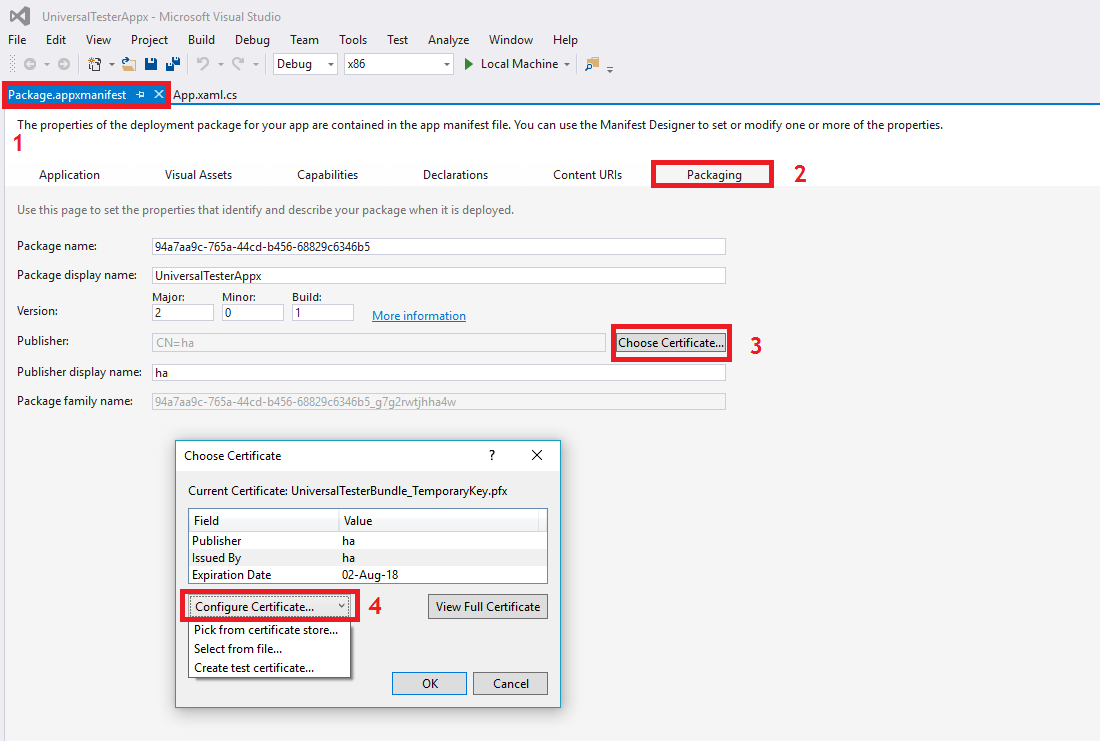
- In Visual Studio, go to the package.appmanifest tab and select Packaging.
- Click on Choose Certificate button present against Publisher and select Configure Certificate.
- Choose the appropriate option from the dropdown i.e., Select from file, in case you already have a third party CA-signed certificate or Create test certificate, in case you want you generate a self-signed certificate.
Signing enterprise apps
Provide the following command on the command line, if you are signing xap file:
BuildMDILXap.ps1 -xapfilename <ME MDM app xap file> -pfxfilename <path_to_PFX_Certificate_File> -password <private_key_provided_for_PFX_certificate>
Provide the following command on the command line, if you are signing appx file:
BuildMDILAPPX.ps1 -appxfilename <ME MDM app appx file> -pfxfilename <path_to_PFX_Certificate_File> -password <private_key_provided_for_PFX_certificate>
Identifying Package Family Name
If you're adding .appx or .appxbundle files to the App Repository, you need to provide a package family name, which can be obtained as explained below:
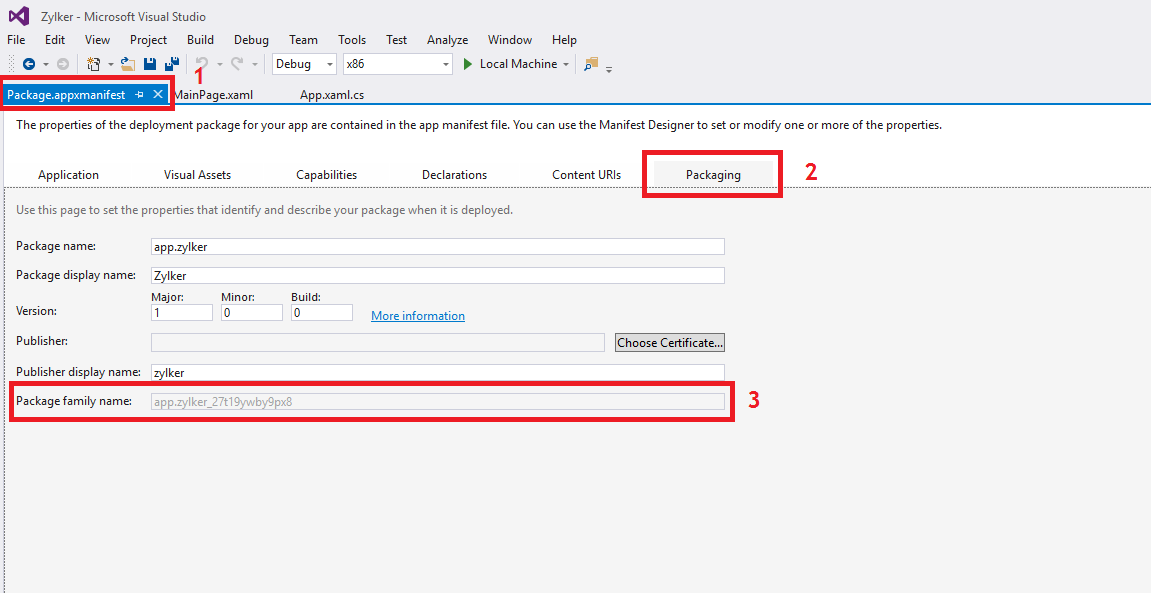
- In Visual Studio, go to the package.appmanifest tab and select Packaging.
- Copy the Package Family Name present and provide it while adding the app to the App Repository
Creating MSIX apps
MSIX is a Windows app package that provides modern packaging experience to all Windows apps. With the MSIX packaging tool, admins can create an MSIX package from an .exe or .msi app. With MDM, admins can silently install MSIX apps on devices running Windows 10, version 1803 or above. Follow the steps given in this document to create MSIX apps.
Distributing enterprise apps
After the Code Signing Certificate (CSC) is uploaded, you can distribute enterprise apps as explained below:
- Add the signed Windows enterprise app as explained here. In case you are uploading .appx or .appxbundle file, provide the Package Family Name as explained here.
- In case you are uploading an .msix file, ensure you remove the version number, architecture and file extension from the file name to generate the bundle identifier. The file name of an MSIX has the following format: package name[_version number_architecture_]_hash.msix. The bracketed information needs to be removed to generate the bundle identifier.
- Distribute it to devices and/or groups. Ensure you select Force install enterprise apps for Distribution Options, which lets the apps get installed silently on devices.
App Configurations
App Configurations lets you customize the apps to suit the needs of the organization. You can also secure devices by restricting apps from accessing data and/or resources of the managed devices. The app developer provides a set of key and their value, that specifies the configurations, which have to be entered on the MDM server. These configurations are pushed automatically with the apps.The app developer must support app configurations for the app, to implement it using MDM.
Pushing app configurations based on user-specific/device-specific parameters such as E-mail, UDID etc., to different users can be a cumbersome task as the app configuration needs to be modified every time before it is pushed. However, MDM supports dynamic variables which ensures once the app configurations with user-specific/device-specific parameters are setup using dynamic varaiables, they needn't be configured again as the dynamic variables fetches all the required data from device/enrollment details.
Dynamic Variables
Here is the table of parameters for which MDM supports dynamic variables:
| PARAMETER | DYNAMIC VARIABLE |
|---|---|
| Device UDID | %udid% |
| Device Name | %devicename% |
| User Name | %username% |
| %email% | |
| Domain name | %domainname% |
| Serial Number | %serialnumber% |
| IMEI | %imei% |
| Exchange ID | %easid% |
| UPN | %upn% |
| APN Username | %apn_username% |
| APN Password | %apn_password% |
