USB Blocking Software
USB blocking is a cybersecurity strategy that is crucial for preventing unauthorized USB flash drives and other auxiliary devices from connecting to your endpoints. Device Control Plus is a dedicated device control and file access management solution that lets you instantly detect and block all unverified USB devices and only allow trusted devices to be active within your network. This USB lockdown software also enables admins to monitor user actions and device file access permissions where required. The admins can configure settings to lock USB ports, by default if express permission for a device is not given.
In addition to blocking USB devices, Device Control Plus helps you control USB devices in your organization, and establishing a fair balance between productivity and security in doing so.
How to block USB devices using Device Control Plus?
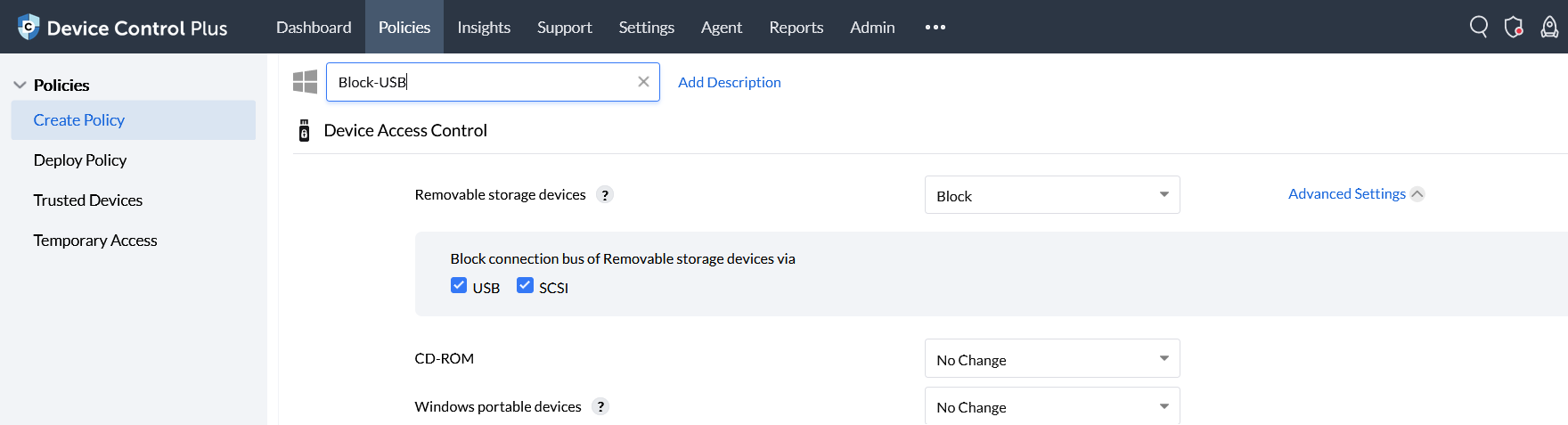
Step 1: In the product console, navigate to Create Policy section from the Policies tab.
Step 2: To block a USB device, select the Block option for Removable Storage Devices.
Step 3: You may also block connection bus of removable storage devices via USB and/or SCSI based on your preference.
Step 4: Select Save & Publish to create a policy or Save as Draft for a draft version of the policy.
By performing these steps, USB device types will be blocked.
Overview of USB Blocking and the advantages it provides for your organization.
What is USB blocking?
USB blocking is a simple data leakage prevention technique adopted to prevent malicious removable storage devices from stealing your data via USB ports. Blocking USB devices helps secure your data by preventing it from being copied into unauthorized removable devices.
Why block USB ports?
The reason why a USB port lock software is essential is because connections of all external devices takes place through USB ports. Identifying the intent of such devices is hard since malware exist on the firmware of the device. Simply put, scanning malicious USB devices may not help at all. To top it off, there are no software patches that can ensure USB port security. This by itself calls for a USB block software, or simply a USB blocker software.
What is a USB port blocker?
A USB blocking software is otherwise known as USB block or USB lockdown software, enables you to lock down your USB ports by default for all untrusted devices. It helps you block or unblock the USB devices as and when needed. By blocking USB ports, you can secure your endpoints from malware that could result in USB attacks. Simply put, you can restrict unauthorized devices from accessing your endpoints and your sensitive data by enforcing a suitable USB port blocker software, otherwise referred to as a USB blocking solution.
What is a BadUSB anyway?
A BadUSB is a security exploit wherein an attacker could turn a USB device into any malicious peripheral device of his choice. The firmware of a USB contains malware that is capable of causing USB attacks such as HID spoofing, runner ducky attack, DMA attacks and more. BadUSBs are one of the prime reasons why every organization needs to implement a USB blocker software.
Why do you need a USB blocking software?
A USB blocker, or USB blocking software ensures that your files, photos, videos or any sensitive data is not copied by your employees for their professional or personal gain. By enforcing USB port blocking policies, you can prevent any malicious activity that might otherwise take place around your USB ports.
Device Control Plus is a comprehensive data leakage prevention solution that works on the principle of zero trust. It offers the feature of USB whitelisting/ USB port blocking, wherein all devices except the ones you include in the list are blocked. Additionally, Device Control Plus alerts on the event of USB blocking whenever an unauthorized device is plugged into your port.
Why Device Control Plus is the best USB lockdown software?
- Lock USB ports and proactively prevent the entry of malware and potential data breaches.
- Do not have to rely on an external or third-party scanning software to identify an unauthorized malicious USB device every time your employee plugs in one.
- Increase your employee productivity by restricting the use of their personal USB devices.
- Stop your employees from copying your sensitive data on their personal USB drives for personal or professional gain.