On this page
European organisations now operate under two major cybersecurity frameworks that define the new baseline for digital resilience. The first framework, the Digital Operational Resilience Act (DORA), which has been enforced since 17 Jan. 2025, has set uniform expectations for how financial institutions manage ICT risk, oversee critical third-party providers, and deliver structured, evidence-based incident reports. The second framework, the Network and Information Security Directive 2 (NIS2), applies more broadly across essential and important sectors and raises expectations for governance, continuous monitoring, and timely notification of disruptive events. The NIS2 framework became a national law on 17 Oct. 2024, and organizations are mandated to be fully compliant by October 2026 at the latest.
Although the scopes of DORA and NIS2 differ, both directives share a common objective: strengthening the overall security posture of organisations operating in an increasingly interconnected European economy. Meeting these expectations requires visibility across hybrid IT environments.
In the current threat landscape, attackers frequently use identities to enter environments rather than exploiting technical vulnerabilities. Cases involving credential reuse, MFA fatigue responses, impersonation of service accounts, and misuse of workload identities have become common across hybrid ecosystems. These techniques enable attackers to operate entirely within legitimate authentication flows, which means traditional perimeter or infrastructure monitoring may not register anything unusual at all.
Without the ability to observe how identities behave, organisations cannot reliably detect misuse early or meet the monitoring and incident-handling expectations set out in DORA and NIS2.
Identity as the operational control plane
Networks, endpoints, and applications change from environment to environment, but every action still originates from an identity and is executed under a set of entitlements. This gives the identity a unique operational role: It is the layer through which all access is granted, exercised, and recorded.
This consistency makes the identity the most reliable place to observe early indicators of misuse. Irregular authentication sequences, unexpected privilege elevation, dormant accounts becoming active and machine identities accessing unfamiliar resources are often the first signals that something is wrong. These indicators typically appear long before infrastructure or endpoint anomalies surface, which is why traditional monitoring tools struggle to detect identity-driven attacks in time.
Viewing the identity as the control plane also reframes how organisations approach regulatory requirements. Both DORA and NIS2 emphasise continuous monitoring, rapid escalation of suspicious activity, and accurate reconstruction of incidents. These expectations are difficult to meet if visibility is fragmented across systems. However, identity data, ties disparate environments together. It provides a unified lens through which organisations can understand how privileges propagate, how access is used in practice, and where deviations may indicate emerging risk.
By treating the identity as the operational control plane, organisations create a foundation for consistent detection and response across diverse architectures. This viewpoint strengthens security posture, but it also exposes a practical gap: IAM and SIEM teams need to work together to monitor identities end to end and cover the full set of expectations defined in the two security mandates.
IAM governs provisioning, authentication, and entitlements, but its visibility largely ends once access is granted. SOC teams monitor behaviour and investigate anomalies, but they only see identity misuse after it manifests in system or network telemetry. The continuous, identity-level monitoring expected under NIS2 and DORA falls between these two functions.
Unifying entitlement context from IAM with behavioural insight from the SOC and monitoring identity activity continuously across environments is a common solution to close this gap. Identity threat detection and response (ITDR) operationalises identity as the control plane by observing how identities authenticate, how privileges are used, and when behaviour deviates from approved patterns. It extends visibility beyond what IAM and SOC can deliver independently and enables the identity-centric monitoring, detection, and response discipline needed to satisfy both directives.
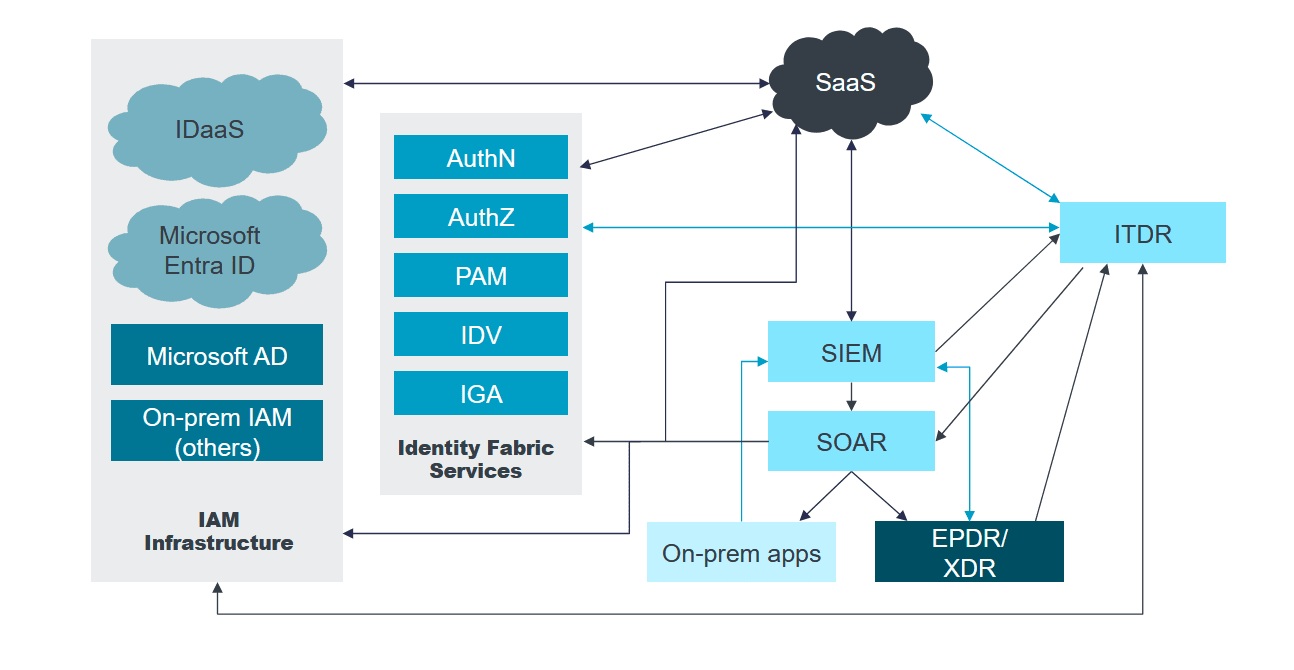
Figure 1: ITDR adds the identity analytics capabilities and insights to SIEM, SOAR, and XDR
Source: KuppingerCole Analysts AG, Leadership Compass 2025: Identity Threat Detection and Response (ITDR)
How ITDR supports NIS2 and DORA compliance
ITDR addresses the gaps that IAM and SOC cannot close on their own. ITDR focuses on understanding and responding to identity misuse at the earliest possible stage, not after misuse has already cascaded into system-level anomalies. It does this by monitoring identity behaviour continuously, correlating activity with entitlement context, and highlighting deviations that may indicate compromise. ITDR is not a replacement for IAM or SIEM. It is a complementary layer that provides visibility on the point where modern attacks commonly begin.
A mature ITDR capability covers several quantifiable areas that together form a broad defensive surface:
1. Continuous monitoring and early detection
ITDR provides real-time visibility into how human, machine, and service identities authenticate and use their entitlements. This supports NIS2’s requirement for appropriate technical measures that enable early detection of abnormal activity and aligns with DORA’s emphasis on continuous ICT risk monitoring. When identity behaviour deviates from its normal pattern, ITDR alerts teams immediately, reducing the time between misuse and detection.
2. Incident classification and multi-stage reporting
DORA requires detailed incident classification and structured reporting, while NIS2 mandates initial and final notification of significant incidents. ITDR produces identity-specific evidence such as the identity involved, the privilege used, the access path, and the surrounding context. This helps organisations classify incidents accurately and provide the level of detail expected under both frameworks.
3. Privilege misuse and lateral movement detection
Both directives expect strong oversight of privileged access. ITDR identifies how entitlements propagate across systems, uncovers privilege escalation attempts, and detects identity-driven lateral movement. These capabilities support NIS2’s access governance expectations and DORA’s requirement for robust control over high-risk permissions.
4. Containment and mitigation actions
NIS2 requires immediate mitigation, and DORA emphasises containing ICT disruptions quickly. ITDR integrates with IAM, SIEM, SOAR, and access brokers to trigger actions such as session revocation, enforced reauthentication, privilege restriction, or temporary account suspension. These responses limit attacker movement and support timely containment.
5. Oversight of third-party identities and dependencies
DORA places clear focus on ICT third-party oversight. ITDR monitors identities associated with external providers, federated access paths, and shared service accounts. This helps organisations assess identity risks tied to vendors and demonstrate ongoing supervision of third-party ICT dependencies.
6. Post-incident reconstruction and root-cause analysis
Both directives require organisations to explain how an incident originated, how it progressed, and which assets were affected. ITDR maintains identity-level logs that reveal the exact sequence of access, the privileges involved, and the systems touched. This supports NIS2’s final reporting expectations and DORA’s root-cause and impact analysis requirements.
7. Strengthening governance and reducing systemic risk
NIS2 places emphasis on governance and accountability. ITDR provides a consolidated view of identity posture by highlighting dormant accounts, excessive privileges, and misaligned access paths. These insights support proactive risk reduction and help organisations demonstrate that they are addressing vulnerabilities before they are exploited.
8. Supporting operational resilience exercises
DORA requires regular resilience testing for critical functions. ITDR contributes to these exercises by modelling how identity misuse could unfold and by enabling teams to test their detection and response workflows against identity-driven scenarios. This improves operational readiness and supports the resilience maturity expectations set out in DORA.
Resilience is the new standard
Some assumptions still affect how organisations approach these mandates. One common belief is that complying with DORA alone is sufficient, even when NIS2 also applies. This overlooks NIS2’s broader obligations around cross-sector reporting, coordination with national authorities, and oversight across essential and important sectors. Another misconception is that outsourcing ICT operations shifts responsibility to the provider, even though both directives make it clear that accountability remains with the organisation.
DORA and NIS2 both expect early detection, timely escalation and evidence-based reporting, and these expectations cannot be met through infrastructure-centric monitoring alone.
By aligning IAM and SOC capabilities, treating identity as the operational control layer and having systems in place to monitor identity behaviour continuously, organisations can meet the detection and response expectations of both directives while strengthening their broader security posture. This shift creates a more resilient foundation in an environment where credentials and entitlements increasingly define the real risk surface.
Related solutions
ManageEngine AD360 is a unified IAM solution that provides SSO, adaptive MFA, UBA-driven analytics, and RBAC. Manage employees' digital identities and implement the principles of least privilege with AD360.
To learn more,
Sign up for a personalized demoManageEngine Log360 is a unified SIEM solution with UEBA, DLP, CASB, and dark web monitoring capabilities. Detect compromised credentials, reduce breach impact, and lower compliance risk exposure with Log360.
To learn more,
Sign up for a personalized demoThis content has been reviewed and approved by Ram Vaidyanathan, IT security and technology consultant at ManageEngine.