- Home
- SIEM use cases
- Audit tampering
How to detect and investigate audit tampering
In this page
Understanding the threat:
Audit logs form the foundation of forensic investigations and compliance verification. Attackers who gain elevated privileges often attempt to erase, modify, or disable audit logs to conceal their activity. Actions like unloading Sysmon drivers, clearing Windows event logs, or disabling event tracing can remove traces of compromise and hinder post-incident analysis. Without visibility into such tampering, organizations risk losing crucial evidence and missing early signs of intrusion.
Category:
- Internal threat
Relevant MITRE ATT&CK® tactics and techniques
Tactics:
TA0005 – Defense Evasion, TA0006 – Credential Access, TA0040 – Impact
Techniques:
T1070 – Indicator Removal on Host, T1562 – Impair Defenses
Compliance mapping:
- CMMC AU.L2-3.3.5: Supports protection of audit information by detecting unauthorized attempts to modify or delete audit logs and enabling timely investigation.
- NIST AU-9 (Audit Protection): Aligns with requirements to safeguard audit records by identifying log clearance, disabling of logging components, or attempts to impair audit capabilities.
- CIS 8.10 (IG2): Helps meet the need to monitor and alert on audit log failures or tampering attempts to maintain integrity of logging mechanisms.
Scenario explanation
A large healthcare provider’s Windows servers suddenly stop forwarding security event logs to its SIEM solution. Analysts also notice Sysmon logs missing from a few critical endpoints.
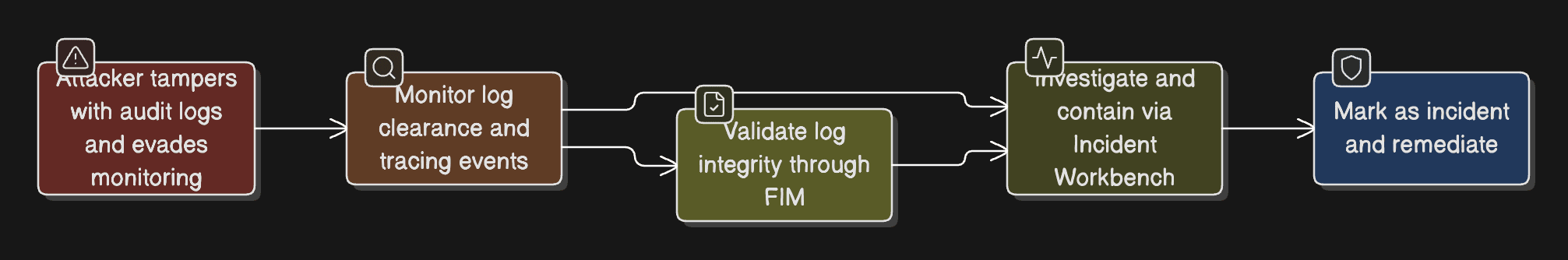
Scenario infographic:
Investigation reveals that an attacker:
- Unloaded the Sysmon driver to disable detailed process logging.
- Cleared Windows event logs to erase traces of privilege escalation.
- Disabled event tracing to block real-time monitoring of malicious commands.
Why this happens:
- Attackers remove or disable logging sources to hide traces of lateral movement.
- Privileged users or compromised service accounts can clear audit trails without detection.
- Lack of integrity monitoring on audit log folders delays visibility into tampering.
What can go wrong:
- Critical forensic evidence is lost, hindering investigations.
- Insider threats and advanced attacks go untraced.
- Compliance violations arise due to incomplete or missing audit data.
The hunt: Real-life threats
SolarWinds supply chain breach (2020): Attackers deleted and replaced log files on compromised build servers to hide traces of a malicious update injection.
NotPetya (2017): A worm cleared event logs and altered registry entries post-infection to erase system evidence and slow down recovery.
Prerequisites
- Ensure Windows security event logs (including log-clearance events) are forwarded to Log360.
- Ensure Sysmon is configured to report driver load/unload and process-level activity (for detecting Sysmon disablement).
- Ensure all domain controllers and critical servers are added as log sources in Log360.
How to detect audit tampering with Log360
1. Monitor log clearance and tracing events
Use predefined alerts like Audit Logs Cleared and Sysmon Driver Unloaded to detect deletion or suspension of key audit processes. Log360 also identifies Event Tracing Disabled and Audit Folder Modification activities, signaling potential evasion.
2. Validate log integrity through FIM
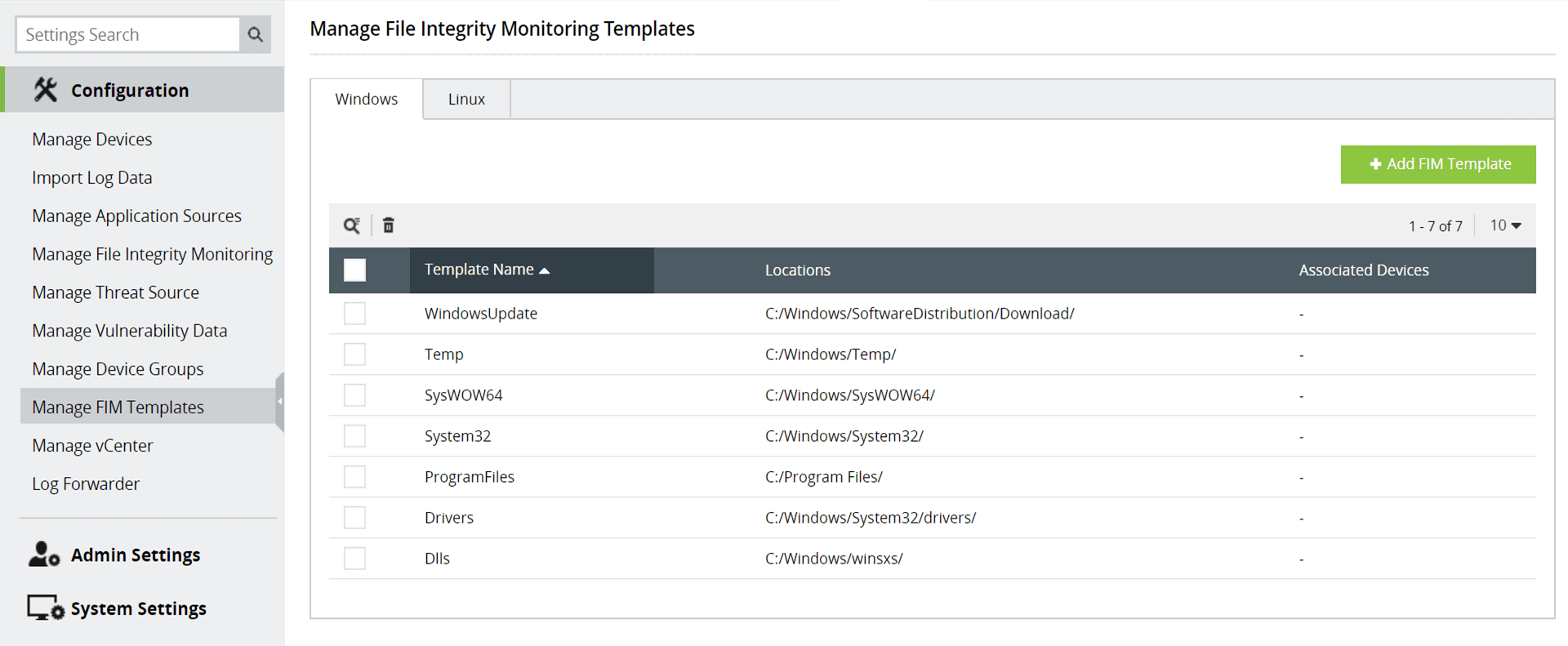
Enable file integrity monitoring (FIM) on audit directories to detect unauthorized modifications or deletions. Integrity checks instantly alert analysts when event log files are altered outside approved change windows.
3. Investigate and contain via the Incident Workbench
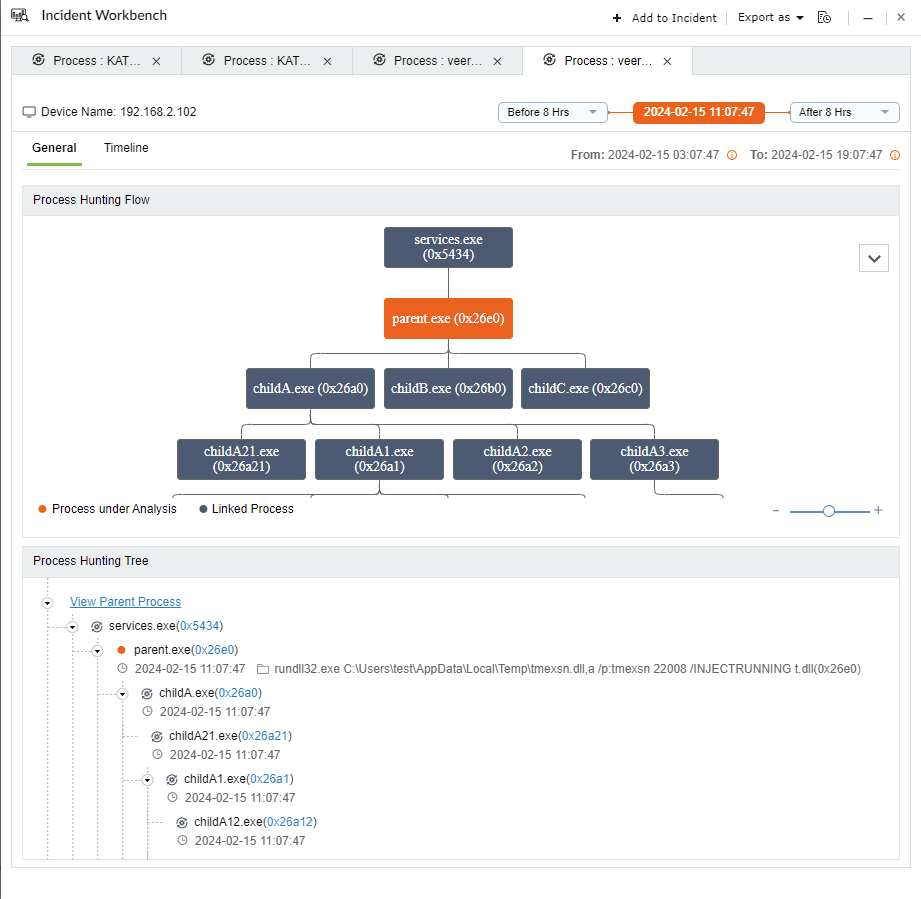
Correlate tampering alerts with recent administrative or system-level actions. Using the Incident Workbench, track command executions, event timestamps, and affected users to determine intent and scope before restoring log functionality.
Next steps
- Attempt recovery of cleared logs from replicas or backups.
- Restrict or revoke administrative privileges linked to the tampering event.
- Perform impact analysis and re-enable enhanced logging across endpoints.


