- Home
- SIEM use cases
- Living-off-the-land attack
Living-off-the-land attack
In this page
Understanding the threat
Living-off-the-land attacks occur when adversaries intentionally abuse legitimate OS binaries, built-in administrative tools, and native processes to carry out malicious activity. Instead of deploying malware, attackers rely on trusted binaries like the WMI command line (WMIC), rundll32.exe, or msdeploy.exe to execute payloads, move laterally, or bypass defenses. Since these tools are part of normal operations, their misuse blends into legitimate activity, making it difficult to detect without deep behavioral and contextual monitoring.
Category
- Endpoint threat
Relevant MITRE ATT&CK mapping
- TA0005 | Defense evasion: T1218 | System binary proxy execution
- TA0003 | Persistence: T1547 | Boot or logon autostart execution
Relevant compliance mapping
- CMMC IR.L3-3.7.5
- NIST CSF DE.AE-2 (Anomalous events)
- CIS Control 8.8 (IG3)
Scenario
During a routine investigation at a company, SOC analysts discovered that several endpoints had executed WMIC commands and rundll32.exe activity late at night, long after business hours. A deeper review revealed that the attacker had compromised a workstation through a phishing email and pivoted without dropping any malicious binaries. Instead, they copied a living-off-the-land binary (LoLBin) from the system directory, used msdeploy.exe to execute additional payloads, and loaded amsi.dll through a proxy process to weaken scanning defenses. All these actions were performed using built-in Windows tools, making the intrusion appear similar to routine administrative maintenance.
What went wrong
The SOC lacked visibility into anomalous execution patterns for native binaries. Because these processes are commonly used for legitimate tasks, their unusual behavior went unnoticed. There were no behavioral baselines, no correlations between user identities and endpoint processes, and no real-time alerts on suspicious LoLBin usage. As a result, attacker activity blended seamlessly into normal system operations.
How living-off-the-land attack monitoring helps
Monitoring for the misuse of trusted binaries enables security teams to catch unexpected process launches, nonstandard command arguments, and abnormal parent-child execution chains. Behavioral analytics highlight deviations from typical user actions, enabling Log360 to flag activity that appears legitimate on the surface but is suspicious in context.
Real-world trends
- Targeted intrusion groups increasingly rely on fileless techniques that abuse OS utilities to evade EDR solution detection, reducing forensic artifacts and increasing the dwell time.
- Ransomware operations now incorporate LoLBin-based execution to stage attacks quietly before detonating encryption payloads, making early detection critical.
Detecting living-off-the-land attacks: Prerequisites
- Implement process creation logging on all monitored endpoints.
- Ensure endpoint logs, including command-line parameters, are being forwarded to Log360.
- Verify that native binary execution paths and approved administrative tools are documented for your environment.
- Enable the relevant alert profiles for detecting suspicious living-off-the-land activity in Log360.
How to detect living-off-the-land attacks with Log360
Log360 helps analysts identify the malicious use of trusted system binaries by surfacing suspicious executions, providing investigation tools, and enabling rapid incident handling. Here’s how:
1. Identify suspicious native binary executions
Log360 collects detailed endpoint process creation event logs, enabling analysts to detect unusual activity involving WMIC, rundll32.exe, msdeploy.exe, and other LoLBins. Analysts can review process execution reports to spot binaries launched at unusual times, from unexpected parent processes, or with abnormal command-line arguments.
2. Enable prebuilt detection rules and alert profiles
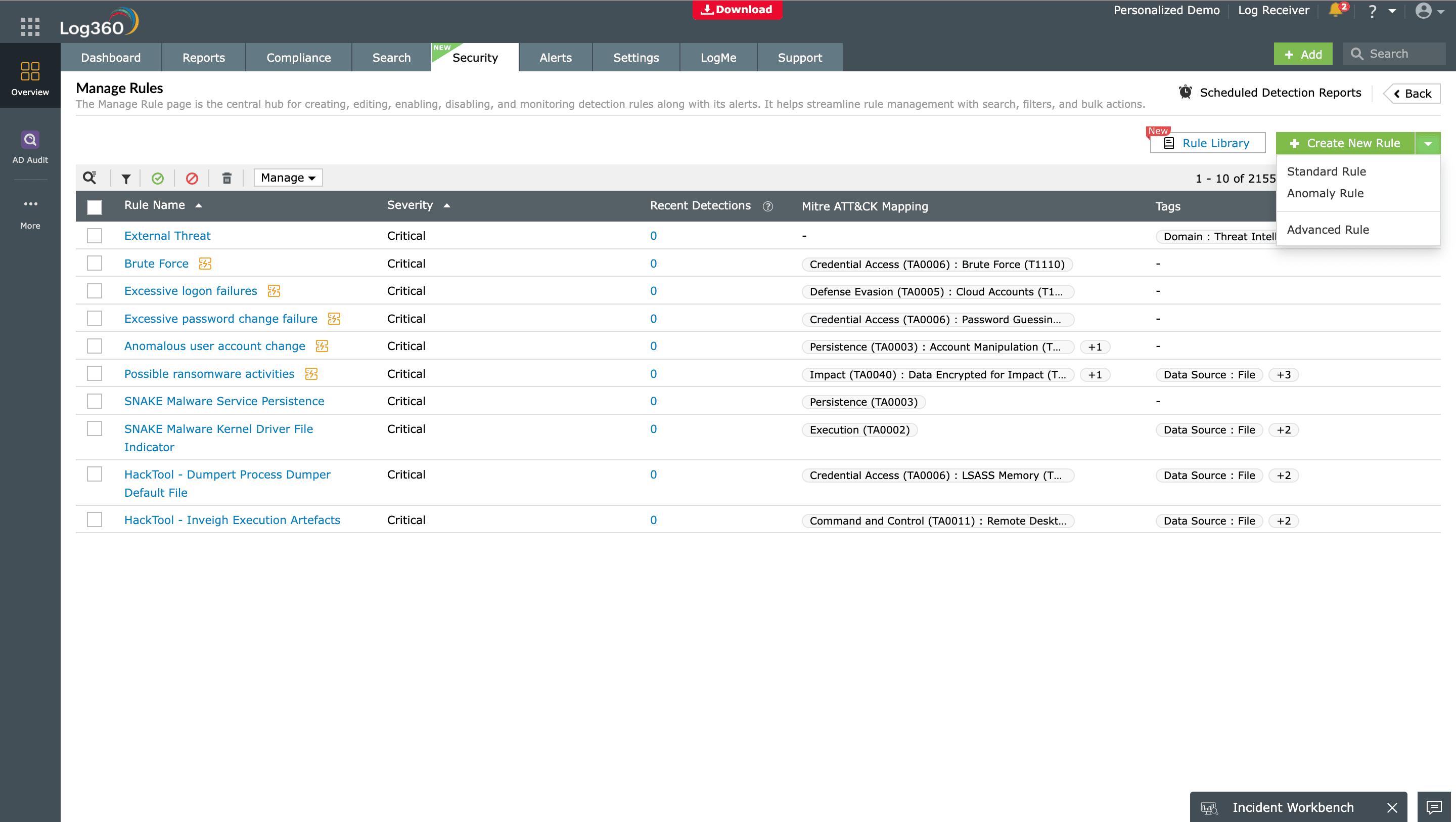
Log360 provides prebuilt detection rules designed to detect high-risk living-off-the-land behaviors. Enable alert profiles for the following detection rules to receive real-time notifications:
- Suspicious WMIC Execution Via Office Process
- LOL-Binary Copied From System Directory
- DLL Call by Ordinal Via Rundll32.EXE
- Amsi.DLL Loaded Via LOLBIN Process
- Execute Files with Msdeploy.exe
- Use of Pcalua For Execution
These alerts surface activity that typically indicates fileless or stealthy attacker behavior.
3. Access the Incident Workbench to analyze the timeline and process lineage
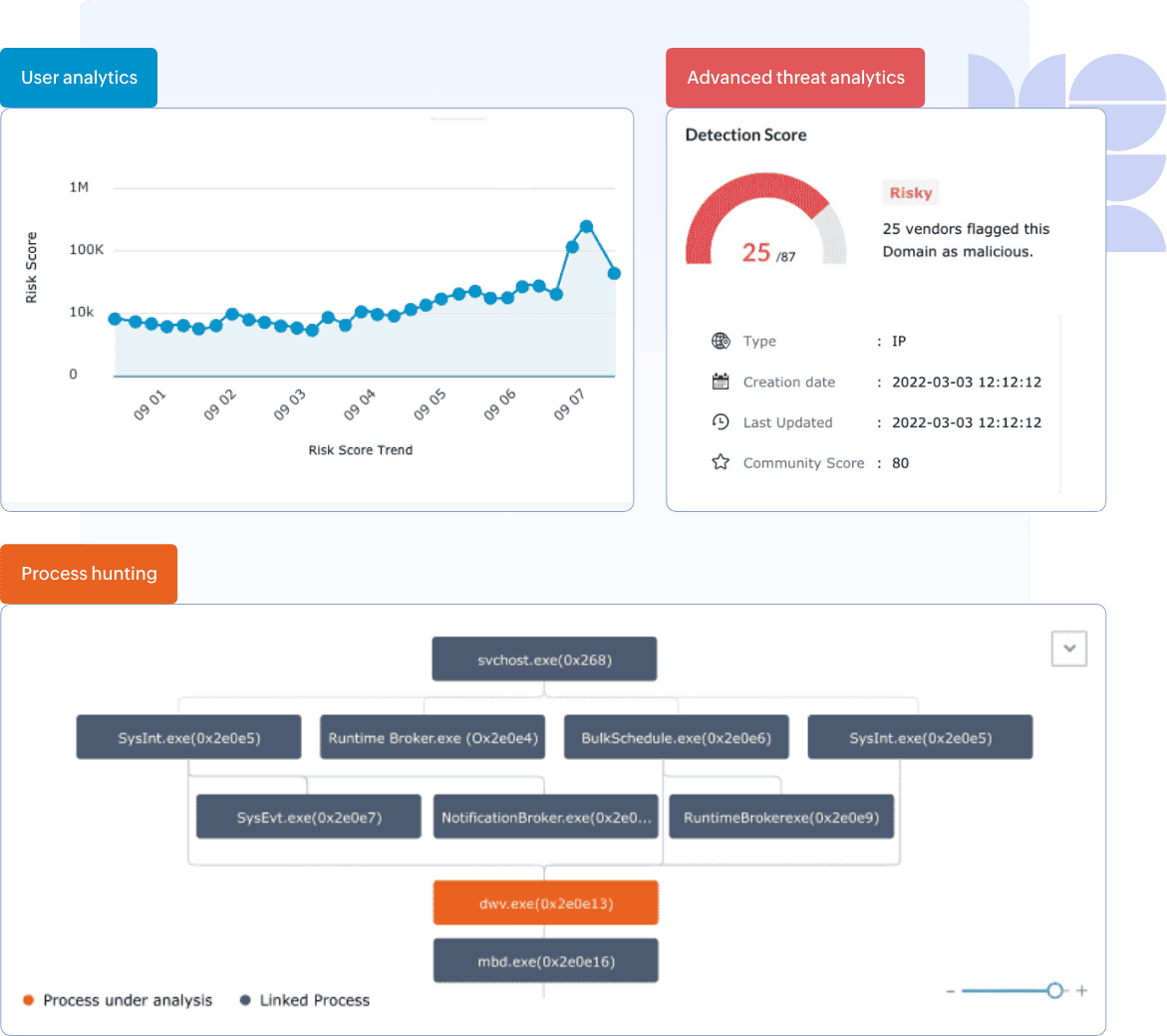
Open the Incident Workbench from any alert or report to investigate the flagged activity. Use the timeline view to understand when the native binary was executed and what subsequent actions it triggered. The Process Hunting Tree reveals parent-child relationships, helping analysts quickly identify abnormal or suspicious process chains.
4. Raise incidents and assign analysts
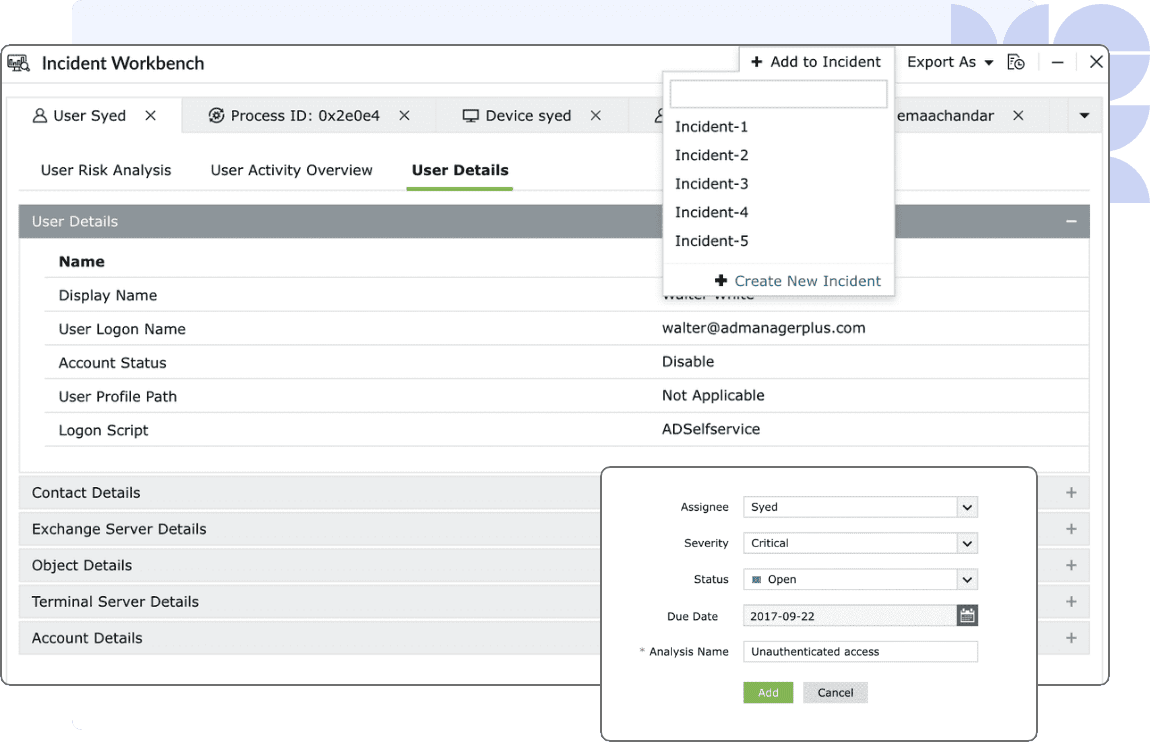
From within the Incident Workbench, convert suspicious events into incidents. Assign them to analysts for deeper investigation, documentation, and responses. This ensures accountability and consistent handling of potential fileless attack activity.
Next steps
- Define suspicious LoLBin criteria: Identify which native binaries are commonly used in your environment and document the behaviors, command-line patterns, and parent processes that should be considered suspicious.
- Implement alerting rules: Enable and tune Log360 alert profiles for unusual executions of WMIC, rundll32.exe, msdeploy.exe, and other high-risk binaries.
- Review LoLBin activity regularly: Periodically review reports and process lineage views to identify recurring abnormal executions or newly emerging misuse patterns.
- Create an incident response playbook: Establish a clear workflow for investigating and containing suspicious native binary activity, including steps for validating the execution context and isolating affected endpoints.


