- Home
- SIEM use cases
- Shadow IT monitoring
Shadow IT monitoring
In this page
Understanding the threat
Shadow IT refers to the use of IT systems, devices, software, applications, and services without explicit approval from the IT department. While often involving employees using familiar tools, this unseen network of unsanctioned assets creates significant security blind spots. Enterprises should care because shadow IT introduces a host of risks, such as:
- Data leaks: Sensitive corporate data can be stored and shared on platforms that lack the necessary security controls, leading to data leakage and breaches.
- Compliance violations: The use of shadow applications can lead to noncompliance with regulations like the GDPR, HIPAA, and the PCI DSS.
- An increased attack surface: Each unsanctioned application is a potential entry point for attackers that the security team is unaware of and therefore not monitoring.
Category
- Cloud threat
Relevant MITRE ATT&CK® tactics and techniques
While shadow IT is not a specific technique in the MITRE ATT&CK framework, it is a significant enabler for various adversarial techniques, including:
- T1567 | Exfiltration over web service: Attackers can leverage existing, unsanctioned web services used by employees to exfiltrate data.
- T1071 | Application layer protocol: The use of non-standard ports and protocols by shadow IT applications can be used by attackers to blend in with legitimate traffic and evade detection.
Relevant compliance mapping
- CMMC SC.L2-3.13.5
- NIST SC-7 (Boundary Protection)
- CIS 2.3 (IG2)
Scenario
A midsize financial consulting firm, Zylker, has approximately 750 employees and a hybrid workplace. It manages corporate apps such as Microsoft 365, an approved CRM solution, and an internal file server. Employees sometimes need faster collaboration or specific SaaS tools for analytics and design, but the IT team’s approval process takes one to two weeks.
The sales unit adopts a freemium file-sharing SaaS tool to quickly exchange large client collateral. Team leads create accounts using corporate email addresses and invite others. Some staff also install browser extensions to convert their Word proposals and quotes into PDFs and upload files directly from the browser. Because the tool can be used easily and immediately, adoption spreads organically, and nobody tells the IT team.
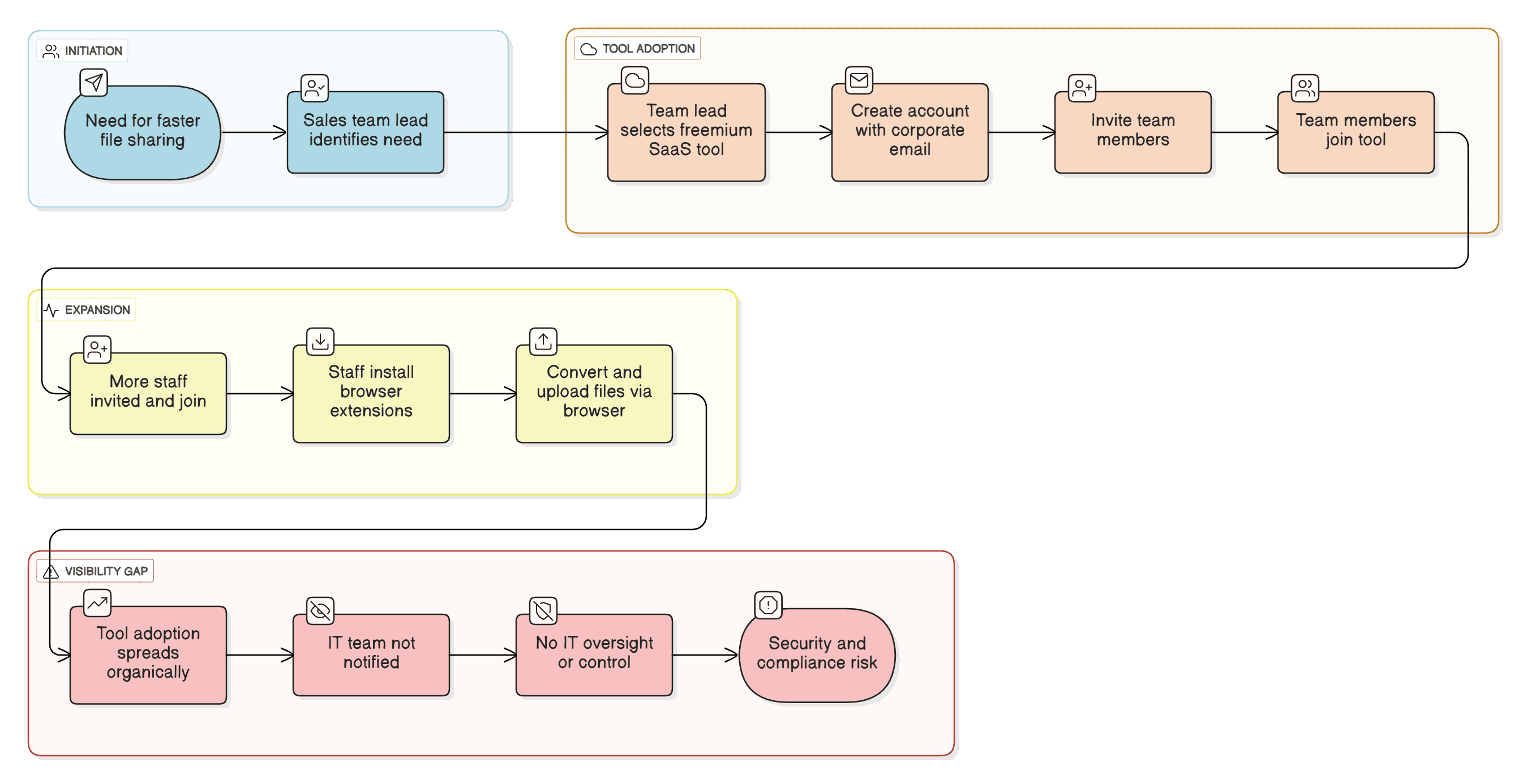
Why this happens
- A business need and a slow approval workflow lead to user self-service.
- Productivity tools are perceived to be low-risk as they’re not considered malicious applications.
What can go wrong
- Sensitive client data uploaded to a third-party cloud leads to compliance and reputational risks.
- A compromised user account or browser extension can act as a backdoor for malware.
- Browser extensions create an easy exfiltration path and increase the attack surface.
Shadow IT in the wild: Real-world trends
- The rise of shadow AI: The most significant new trend is the widespread, unsanctioned use of generative AI tools. Employees, aiming for productivity gains, are pasting sensitive corporate data (like source code, marketing plans, or financial information) on public AI platforms, creating massive new risks of data leakage and intellectual property loss.
- SaaS sprawl driven by the push for productivity: The core driver of shadow IT remains the employee need for efficiency. Slow IT approval processes lead teams to adopt their own preferred project management tools (like Trello and Asana), file sharing tools (like personal Dropbox and Google Drive accounts), and collaboration tools (like Slack and WhatsApp), creating massive, invisible SaaS sprawl that IT teams cannot secure, patch, or monitor.
Use case objective
Detect and stop unauthorized SaaS or shadow application usage that results in sensitive data uploads or creates unauthorized outward connections.
How to detect with Log360
Step 1: Configuring cloud protection
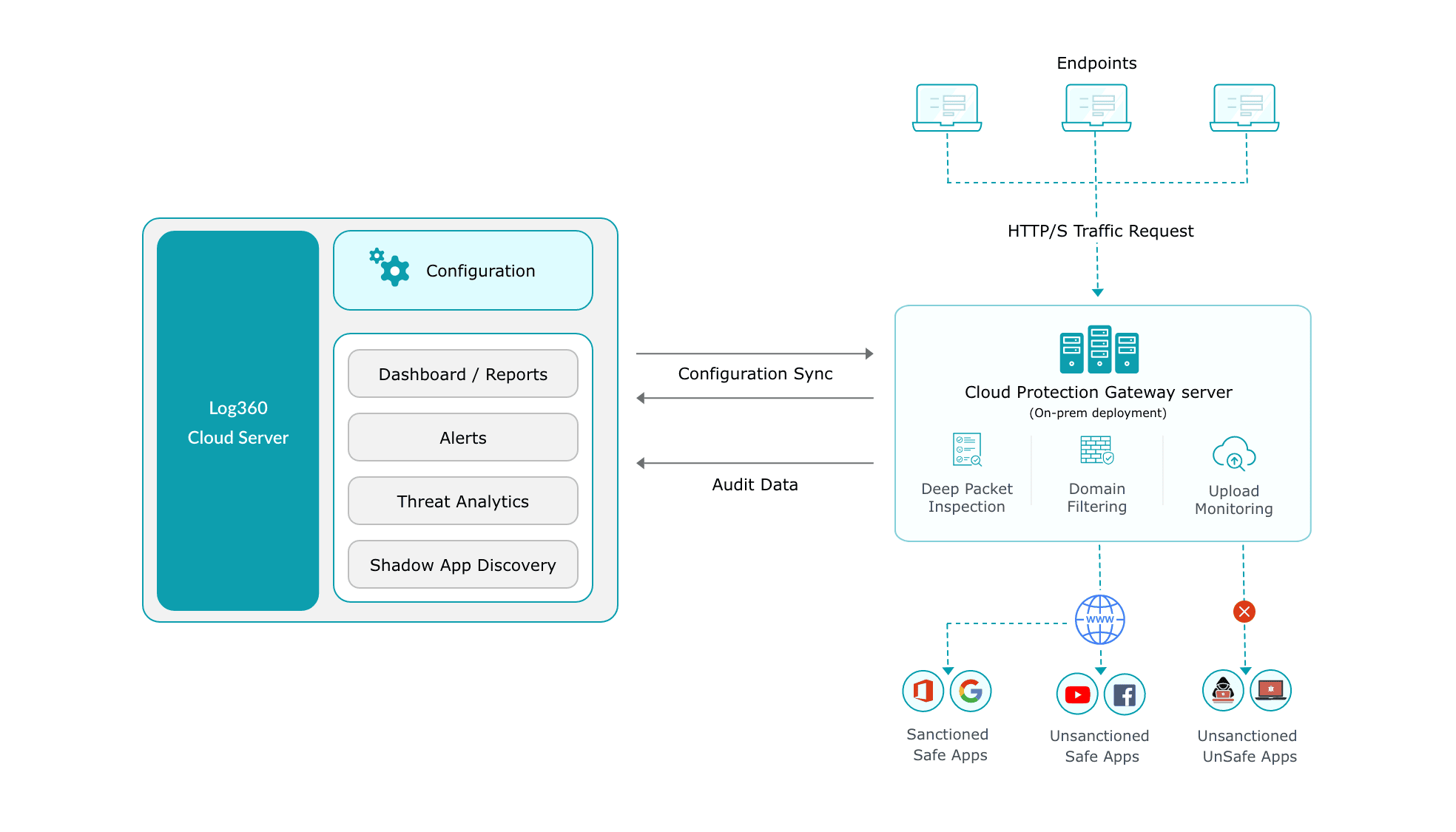
Log360 Cloud leverages a Gateway Server architecture to collect and process network traffic logs on-premises before securely sending insights to the cloud. To enable this, simply install the Log360 Cloud agent on a dedicated server to act as the gateway, and configure your firewalls and proxies to forward their syslogs to this gateway. The solution then automatically parses this traffic to identify and categorize all sanctioned and unsanctioned cloud applications.
Note: For detailed configuration steps, please refer to the Cloud Protection in Log360 Cloud page.
Step 2: Monitor user activity with CASB reports
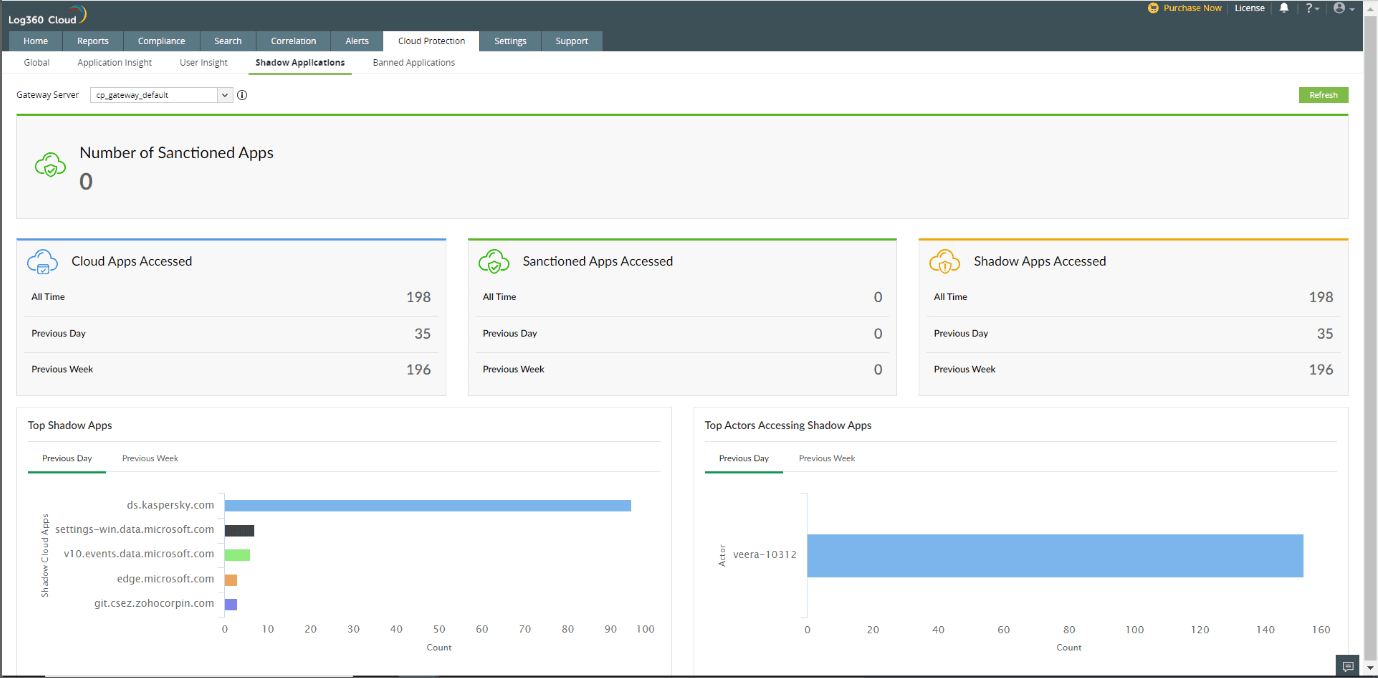
Once logs are flowing, use the Cloud Protection dashboards to investigate specific user actions.
- Navigate to the Reports tab.
- From the "Devices" dropdown or side menu, select Cloud Protection.
- Under the Cloud Access Reports or File Upload Reports section, look for the specific reports mentioned:
- Dropbox Upload Requests: Filters traffic specifically for uploads to Dropbox domains.
- All Upload Requests: Provides a high-level view of all data leaving your network, allowing you to sort by file size to find data exfiltration anomalies.
- You can also view the Shadow Applications insight dashboard under the Cloud Protection tab for a graphical summary of Sanctioned vs. Shadow apps.
Note: For detailed steps, please refer to the Manage Banned Applications page.
Step 3: Set up real-time alerting for banned apps
To move from passive monitoring to active defense, configure alerts for apps you have deemed "high risk."
- First, define your banned apps: Navigate to Settings > Configuration > Cloud Protection Settings > Cloud App Settings > Banned Applications
- On the Banned Cloud Applications page, click +Add Application.Enter application names separated by a comma in the text box. (Example - ransomeware.com, demo.malware.com, mail.phishing.com)
- Next, create the alert: Navigate to Alerts > Manage Profiles and click Add Alert Profile.
- In the alert criteria, select Cloud Protection > Access to Banned Applications alert profile.
- Configure Email or SMS notifications to alert the SOC immediately when a user attempts to access these services.
Next steps
- Establish a shadow IT policy: Develop a clear policy that outlines the process for requesting and approving new applications.
- Educate users: Conduct regular training sessions to educate employees about the risks associated with shadow IT and the importance of using approved applications.
- Create alerting rules: Based on the discovered applications, create specific alerting rules in Log360 to be notified of high-risk activities.
- Sanction applications: For frequently requested unsanctioned applications, perform a security assessment to determine if they can be officially approved and brought under the IT team's management.


