Hunting for security threats to keep up the network security posture is a crucial responsibility of a security operations center (SOC). Monitoring your network and detecting threats is vital to keep your organization secure. An SOC houses IT security professionals who detect, analyze, and remediate cyberattacks. However, security professionals often have to look for threats across a multitude of complicated IT infrastructures including network devices, firewalls, databases, servers, and more, which results in unnoticed cyberattacks and fatigued analysts.
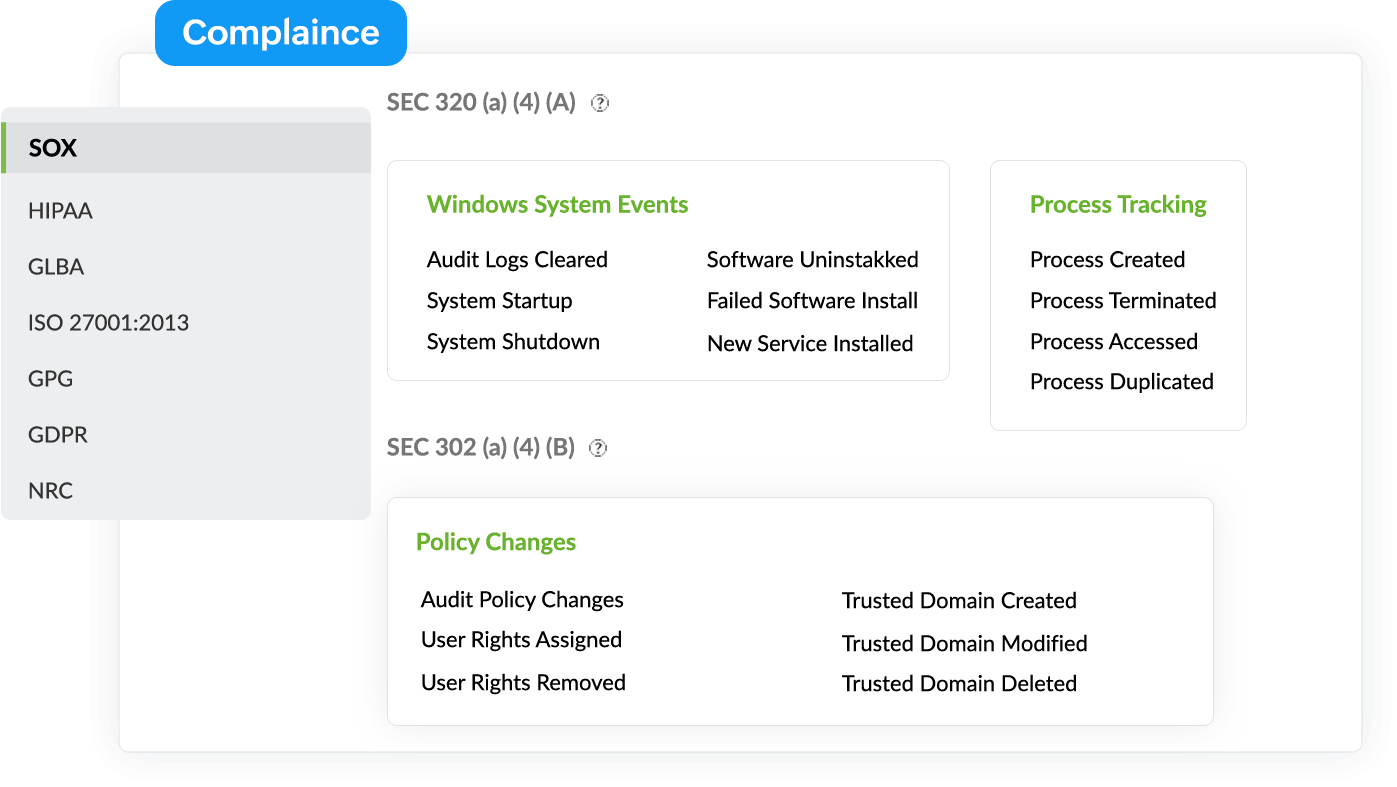
Designed to address SOC challenges, Log360 is a comprehensive security information and event management (SIEM) solution that helps SOCS detect threats, identify anomalous user behavior, trace suspicious network activity with real-time alerts, systematically resolve security incidents with workflow management, track a incident resolution processes with its built-in ticketing system, carry out regular security audits, safeguard classified data with the help of file integrity monitoring, and much more. Log360 also helps meet regulatory mandates for PCl DSS,HIPAA,FISMA,SOX, the GDPR,GLBA, and more with its integrated compliance management system.
Optimize SOC metrics with Incident Manager
Log360's actionable incident dashboard helps enterprises to streamline and optimize their security operations by providing visibility into key metrics—mean time to detect (MTTD), mean time to respond (MTTR), and more. Track the active and unresolved incidents, recent and critical incidents, and get to know the workload of security analysts from this dashboard. Triage and prioritize incident resolution to ensure optimal functioning of your SOC with Log360's Incident Manager.
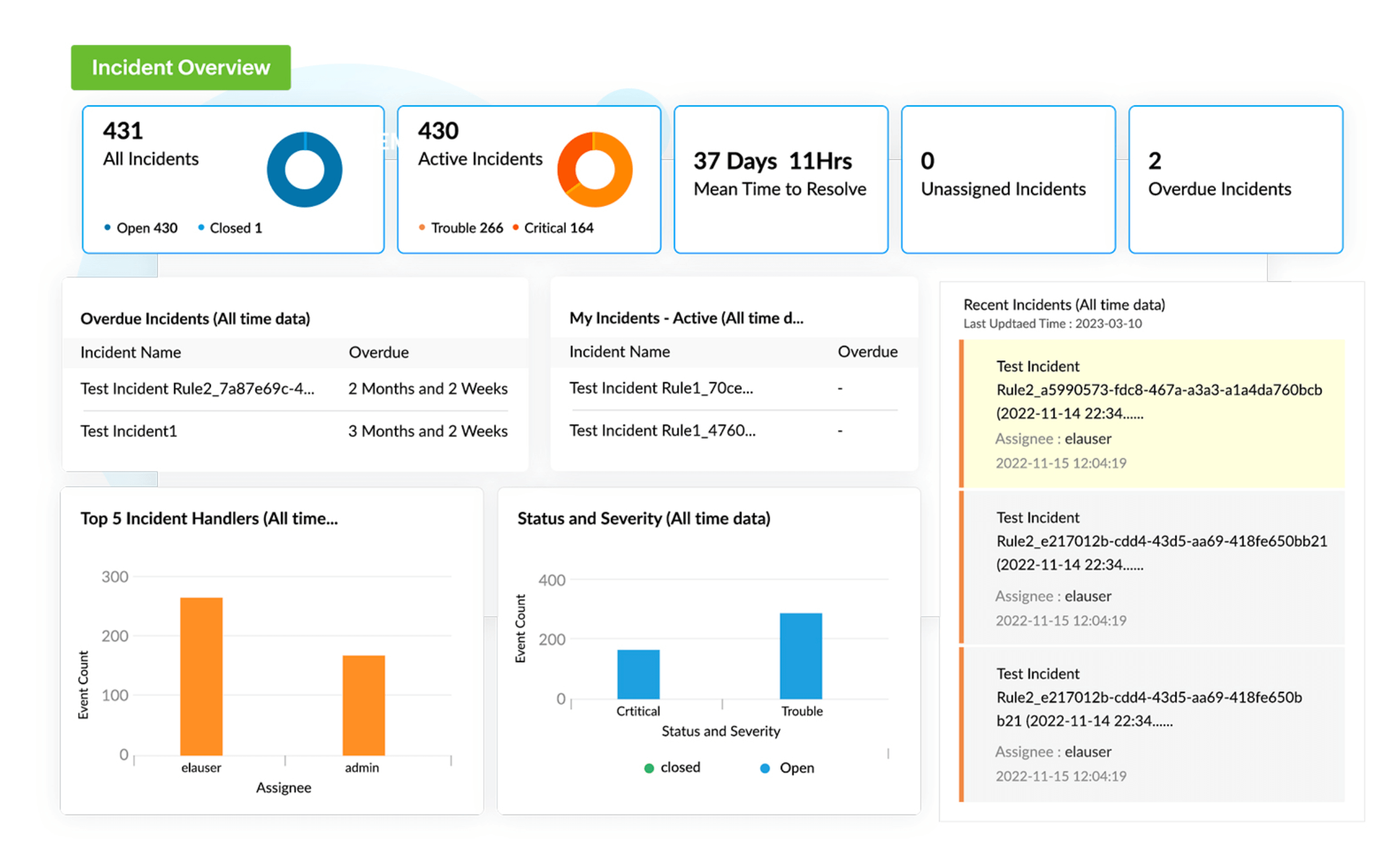
Decreases the mean time to detect incidents
Log360's incident management module, coupled with signature-based and behavior-based threat detection techniques, allows you to promptly detect, track, and report on attacks, thereby improving the mean time to detect and respond to threats.
Offers a proactive security strategy
Log360 comes with a built-in threat intelligence platform that includes preconfigured and custom threat feeds, instant alert notification, forensic reports, and a built-in ticketing system that helps you mitigate attacks by hunting down lurking threats and thereby build a proactive security approach.
Minimizes the mean time to resolve threats
Log360 also uses contextual information to triage critical alerts, thereby reducing the mean time to resolve threats. It also comes with a built-in incident management module that helps you track the incident resolution process. Assign incidents to analysts, investigate incidents with the Incident Timeline feature, add notes on resolution processes, monitor incident resolution times, and assign workflows to remediate threats.
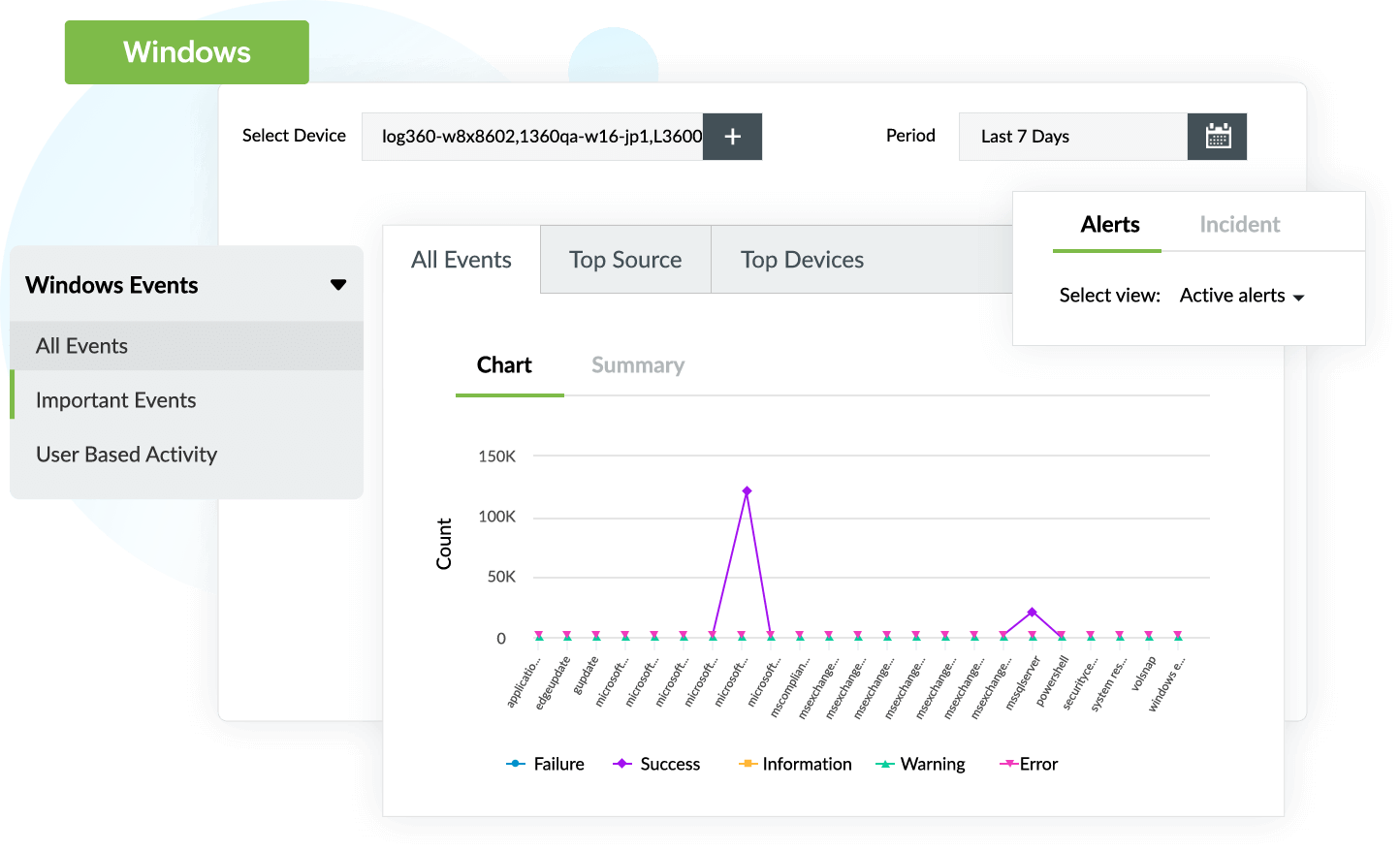
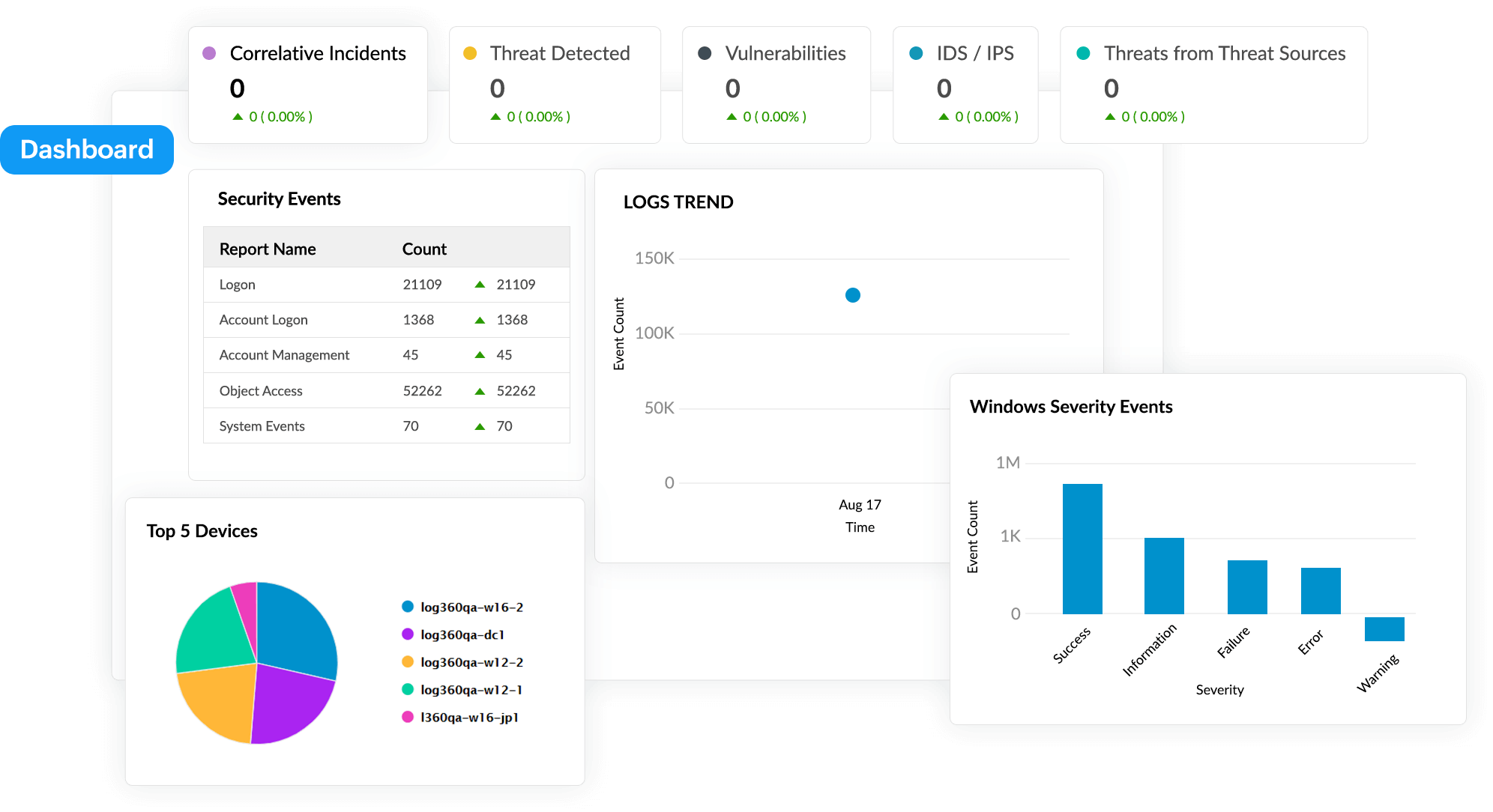
Increases the visibility of security events across platforms
You can monitor the security events across various platforms such as physical, virtual, cloud, and remote-work environments, all from a single console. Log360 also comes with a built-in threat detection module that blacklists malicious IP addresses.
Reduces the false positives with risk management
Log360 comes integrated with a machine-learning-based user and entity behavioural analytics (UEBA) module that lets you easily identify risks and anomalies. The UEBA add-on comes with an integrated risk management system that associates risk scores depending on anomaly types. This helps analysts keep a close eye on high-risk users, reduce false positives, and accurately detect slow and advanced persistent attacks.
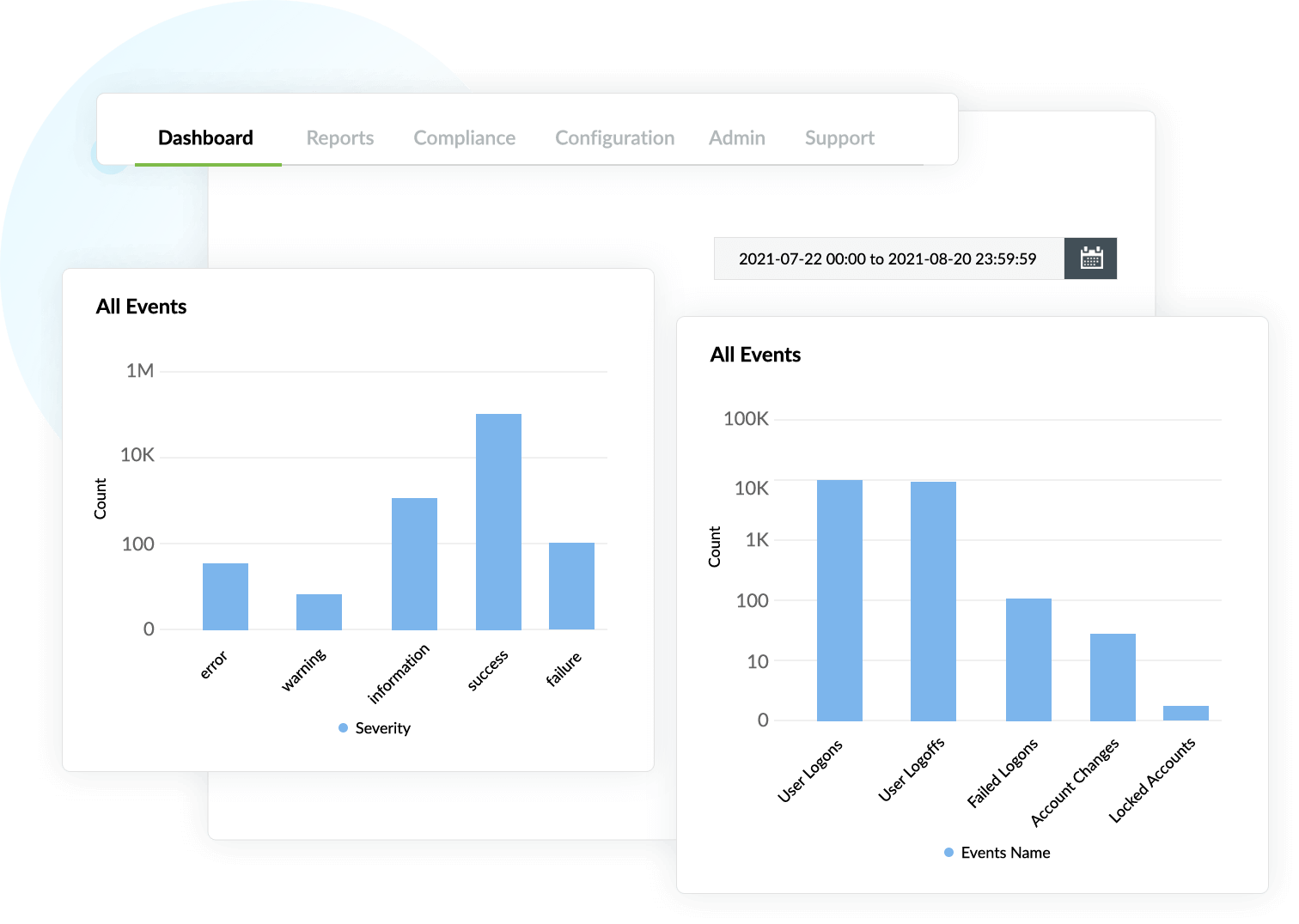
Simplifies scaling for large environments
Log360 is equipped to audit physical, virtual, and cloud environments. It provides easy security and compliance management for Windows, Linux servers, Hyper-V machines, Azure, and Amazon cloud platforms, helping scale your environment.