Configuring Cisco Devices - PIX, ASA, FWSM, VPN Concentrator
Firewall Analyzer supports the following versions of various Cisco devices.
Cisco IOS Firewalls:
- 8xx
- 18xx
- 28xx
- 38xx
- 72xx
- 73xx
- 3005
- 1900
- 2911
- 3925
Cisco FWSM Catalyst Series:
- 6500
- 7600
Cisco PIX versions:
- 6.x
- 7.x
Cisco ASA:
5500 series
Cisco VPN Concentrators Series:
- 3000
- 3500
| Model Family | Model | Cisco IOS Software Version |
|---|---|---|
8xx | c871, c876, c877,c878 | 12.4(4)T |
18xx | c1841 | 12.3(14)T |
c1811, c1812 | 12.4(4)T | |
c1801, c1802, c1803 | 12.4(4)T | |
28xx | c2801, c2851, c2821, c2811 | 12.3(14)T |
38xx | c3845, c3825 | 12.3(14)T |
72xx | 7206VXR, 7204VXR | 12.3(14)T |
73xx | CISCO7301 | 12.3(14)T |
To find out the version of your PIX firewall, Telnet to the PIX firewall and enter the show version command.
Note: | Cisco PIX does not create log files, but instead directs a log stream to the syslog server, which writes the log information into a file. Make sure the syslog server on Firewall Analyzer can access the PIX firewall on the configured syslog port. For this, you may have to make a rule specific to this situation. |
- Cisco PIX using Command Line Interface
- Cisco PIX from the User Interface
- SNMP protocol for Cisco PIX using Command Line Interface
- Cisco ASA using Command Line Interface
- Cisco ASA using ASDM
- SSL WebVPN in Cisco ASA appliance
- Cisco ASA NetFlow Logs
- SNMP protocol for Cisco ASA using Command Line Interface
- Cisco VPN 3000 Concentrator
- Cisco IOS Switch
- SNMP protocol for Cisco Firewalls using ASDM Web UI tool
- Get logs from Virtual Firewall (Virtual Domain)
- Log IDs for Security Breach reports
- Log IDs for VPN reports
Configuring Cisco PIX using Command Line Interface
- Telnet to the PIX firewall and enter the
enablemode - Type the following:
configure terminal]
logging on
logging timestamp
logging trap informational
logging device-id {context-name | hostname | ipaddress interface_name | string text}
logging host interface_name syslog_ip [17/<syslog_port>
where,
interface_name | is the interface on the PIX firewall whose logs need to be analyzed ("inside" or "outside," for example). |
syslog_ip | is the IP address of the syslog server (i.e. Firewall Analyzer), to which the Firewall should send the Syslogs. |
17/<syslog_port> | indicates that logs will be sent using the UDP protocol, to the configured syslog port on the syslog server. If left blank, the syslogs are sent through the default syslog port (UDP port 514). If the logs are sent through any other port, mention it as 17/<the UDP port number> (For example: 17/1514). |
hostname | firewall's host name (defined with the hostname configuration command). In this case, the hostname will appear in the logs sent from the Firewall. |
ipaddress interface_name | the IP address of a specific firewall interface named interface_name ("inside" or "outside," for example). In this case, the IP Address of the Interface Name will appear in the logs sent from the Firewall. |
string text | an arbitrary text string (up to 16 characters). In this case, the arbitrary text string you have entered in string <text> will appear in the logs sent from the Firewall. |
context-name | in PIX 7.x or FWSM 2.x operating in multiple-context mode, the name of the firewall context will appear in the logs sent from the Firewall. |
Example: logging host inside 11.23.4.56 17/1514
To verify your configuration, enter the show logging command after the last command above. This will list the current logging configuration on the PIX firewall.
Configuring Cisco PIX from the User Interface
Log in to the Cisco PIX user interface, and follow the steps below to configure the PIX firewall:
- Enabling Logging
- Select Configure > Settings > Logging > Logging Setup
- Select the Enable logging setup and Enable logging failover check boxes
- Click Apply.
Changes are applied to the assigned PIX firewall configuration files when they are generated. The configuration files are then downloaded to PIX firewalls at deployment.
- Configuring Syslog Server
- Select Configure > Settings > Logging > Syslog
- Check Include Timestamp.
- Click Add to add a row.
- In the Add Syslog Server page that appears, enter the following:
- Interface Name - the firewall interface through which Firewall Analyzer can be reached, the interface can be either inside or outside.
- IP Address - the IP address of the syslog server to which logs have to be sent
- Under Protocol, select the UDP radio button
- The default UDP port is 514. If you have configured a different syslog listener port on your syslog server, enter the same port here.
- Click Apply
- Configuring Logging Level
- Select Configure > Settings > Logging > Other
- Under Console Level List select Informational so that all report data is available
- Click Apply
Note: | For every transaction happening in Cisco PIX Firewall, an ACL configured in it matches. The matched ACL along with complete transaction detail is audited through Message-ID 106100. Ensure that the logging is enabled for 'Message-ID 106100' in Cisco PIX Firewall. For more information about the message ID follow the below link. http://www.cisco.com/en/US/docs/security/pix/pix63/system/message/pixemsgs.html#wp1086617 This message identifier contains the information about both accepted and denied transactions. The log information is parsed to get the 'Used' rules and is available in the 'Firewall Rules Report > Top Used Rules Report'. |
Configure/Enable SNMP Protocol for Cisco PIX Firewall device
Using CLI Console:
To enable the SNMP Manager running in Firewall Analyzer to make queries to SNMP Agent running in the firewall:
| configure terminal snmp-server host <interface name> <hostname |IP address of Firewall Analyzer> |
If you want to create a new SNMP community use the below command:
| configure terminal snmp-server community <community-string> |
Example:
| configure terminal snmp-server community public |
Configure Cisco ASA using Command Line Interface
- Telnet to the ASA firewall and enter the
enablemode - Type the following:
configure terminal]
logging enable
logging timestamp
logging trap informational
logging device-id {context-name | hostname | ipaddress interface_name | string text}
logging host interface_name syslog_ip [udp/<syslog_port>
- If there are no URL Reports available in Firewall Analyzer for CISCO ASA, enable HTTP inspection by executing the following command:
inspect httpEnabling HTTP inspection will generate syslogs with ID 304001. This ID will be used by Firewall Analyzer to generate URL Reports.
interface_name | is the interface on the ASA Firewall whose logs need to be analyzed (for example: "inside" or "outside"). |
syslog_ip | is the IP address of the syslog server (i.e. Firewall Analyzer), to which the Firewall should send the Syslogs. |
udp/<syslog_port> | indicates that logs will be sent using the UDP protocol, to the configured syslog port on the syslog server. If left blank, logs will be sent to the default UDP port 514. |
hostname | firewall's host name (defined with the hostname configuration command) |
ipaddress interface_name | the IP address of a specific firewall interface named interface_name (for example: "inside" or "outside") |
string text | an arbitrary text string (up to 16 characters) |
context-name | in PIX 7.x or FWSM 2.x operating in multiple-context mode, the name of the firewall context can also be sent. |
For more information, refer the Cisco PIX documentation.
Configure Cisco ASA using ASDM
- Load the ASDM.
- Select Configuration > Device Management > Logging > Logging Setup.
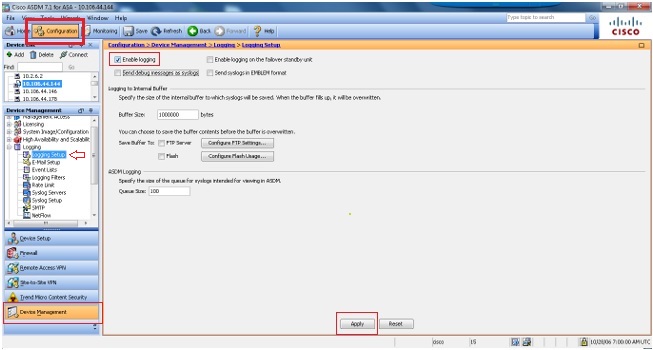
- Select Enable Logging.
- Select Logging > Logging Filters.
- Choose the syslog-servers as Informational.
- Select Logging > Syslog servers.
- Click Add.
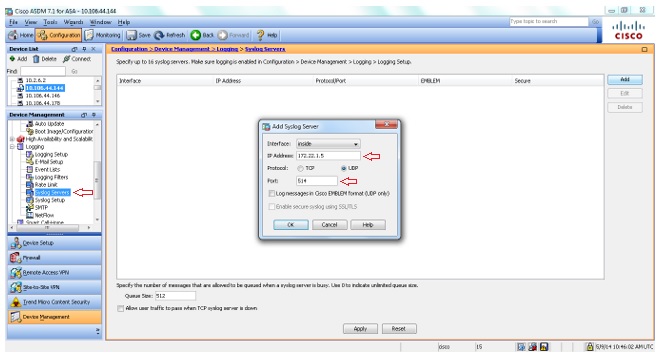
- Enter the IP address and choose the appropriate interface. Also, ensure that you choose UDP and enter the port number 514 or 1514.
- Select Logging > Syslog Setup.
- Select Include time stamp in syslogs option and scroll down to ensure the syslog IDs 302013, 302014, 302015 & 302016 are in enabled state and the logging level is set to Informational.
Refer the links for Security event syslog IDs and VPN event syslog IDs to be enabled.
Disable Logging
You can disable specific syslog IDs based on your requirement.
Note: | By selecting the check mark for the Include timestamp in syslogs option, you can add the date and time that they were generated as a field to the syslogs. |
- Select the syslogs to disable and click Edit.
- From the Edit Syslog ID Settings window, select the Disable messages option and click OK.
- The disabled syslogs can be viewed in a separate tab by selecting Disabled syslog IDs from the Syslog ID Setup drop-down menu.
For more information, refer the Cisco PIX documentation.
Configuration for SSL WebVPN in Cisco ASA appliance
Firewall Analyzer requires syslog message IDs 722030 and 722031, which by default is at debug level, to process Cisco SVC VPN logs. Set the information level to these syslog IDs by executing below commands in global configuration mode:
hostname(config)# logging message 722030 level 6 |
You can confirm by executing the below command:
hostname(config)# show logging message 722030 |
Configuring Cisco ASA NetFlow Logs and Disabling NetFlow on Cisco ASA/ADM using command line and ASDM
Firewall Analyzer support NetFlow version 9 packets, which is introduced in Cisco ASA 8.2.1/ASDM 6.2.1.
Configuring ASA device using console mode to send NetFlow version 9 packets to Firewall Analyzer is given below:
- As Firewall Analyzer is capable of receiving either Syslog or NetFlow packet from an ASA box, disable Syslog and enable NetFlow.
To disable Syslog and enable NetFlow execute the following commands:
(config)# flow-export destination inside <Firewall Analyzer Server IP> 1514
(config)# flow-export template timeout-rate 1
(config)# flow-export delay flow-create 60
(config)# logging flow-export-syslogs disable ---> This command will disable logging syslog messages
(config)# access-list netflow-export extended permit ip any any
(config)# class-map netflow-export-class
(config-cmap)#match access-list netflow-export
Associate global policy map with netflow class map
- Option 1
If you have a global policy map, associate the above netflow class-map netflow-export-class to the global policy.
For example: if your global policy map is named global_policy_asa, you need to execute the below commands:
(config)# policy-map global_policy_asa
(config-pmap)# class netflow-export-class
(config-pmap-c)# flow-export event-type any destination <Firewall Analyzer Server IP>if the above command fails use the below:
(config-pmap-c)# flow-export event-type all destination <Firewall Analyzer Server IP>
- Option 2
If you wish to create a new policy map named netflow-export-policy and make this as your global policy follow the below steps:
(config)# policy-map netflow-export-policy
(config-pmap)# class netflow-export-class
(config-pmap-c)# flow-export event-type any destination <Firewall Analyzer Server IP>if the above command fails use the one below:
(config-pmap-c)# flow-export event-type all destination <Firewall Analyzer Server IP>Make policy map netflow-export-policy as your global policy:
(config)# service-policy netflow-export-policy global
For UI mode configuration using ASDM access, refer the Cisco forum topic: https://supportforums.cisco.com/docs/DOC-6114
To disable NetFlow on Cisco ASA/ADM execute the following commands:
(config)# flow-export disable
(config)# no flow-export destination inside <Firewall Analyzer Server IP> 1514
To disable NetFlow on Cisco ASA/ADM using ASDM
- Click on Configuration > Firewall
- Click on Service Policy Rules. Look for the policy indicating netflow export
- Check the IP address if the flow is pointing to the machine where you want to forward syslog.
- If so, delete it and write the configuration in to memory (Save it).
Note: | if you have configured Version9 Netflow logs, only Traffic reports are supported. |
Configure/Enable SNMP Protocol for Cisco ASA Firewall device
Using CLI Console:
To enable the SNMP Manager running in Firewall Analyzer to make queries to SNMP Agent running in the firewall:
| configure terminal snmp-server enable snmp-server host <interface name> <hostname | IP address of Firewall Analyzer> [poll] |
Example:
| configure terminal snmp-server enable snmp-server host inside 192.168.101.155 poll |
If you want to create a new SNMP community use the below command:
| configure terminal snmp-server community <community-string> |
Example:
| configure terminal snmp-server community public |
Configuring Cisco VPN 3000 Concentrator
Currently we support Cisco IOS Compatible Log Format and Original Log Format for Cisco VPN Concentrator.
Importing of already saved Cisco VPN Concentrator logs is not supported because those logs are saved in either of the following formats which is not supported in Firewall Analyzer:
- Multi line
- Tab Delimited
- Comma Delimited
Follow the below steps to configure the VPN Concentrator:
- Configuring Syslog Server
- Login to the Cisco VPN 3000 Concentrator Management console.
- Go to Configuration > System> Events >Syslog Servers
- Click the Add button
- In the Syslog Server text box enter the IP Address of the machine where Firewall Analyzer is running.
- Enter the Port value. The default syslog server port for Firewall Analyzer is 514.
- Facility is Local 7
- Configuring Syslog Events
- Go to Configuration > System> Events >General
- For Syslog Format you can either select Original or Cisco IOS Compatible format.
- For Events to Syslog select Severities 1-5
- All other configurations are default for this page.
- Click Apply button
For more information, refer the Cisco VPN Concentrator documentation.
Configuring Cisco IOS Switch
Follow the below steps to configure the Cisco IOS Switch:
- Login to the Cisco IOS console or Telnet to the device.
- Change the configuration mode of the device.
Use the following command:
configure terminal
- Enable logging by using the following commands:
logging on
logging trap informational
logging <IP Address>
- If there is a Firewall module in the IOS device, use the following command to enable audit trail. This will generate traffic information.
ip inspect audit-trail
For more information, refer the Cisco IOS Switch documentation.
Configure/Enable SNMP Protocol for Cisco Firewall devices using Cisco ASDM tool
Using Web UI:
Configure SNMP parameters for SNMP Versions 1 and 2c
Carry out the following steps:
- In the ASDM main window, select Configuration > Device Management > Management Access > SNMP
- In the Community String (default) field, enter default community string. This applies to SNMP Versions 1 and 2c only
- Fill appropriate values in Contact and Location fields
- In the Listening Port field, enter the port number of the security appliance that listens for SNMP requests from management stations; or retain the default port number 161
- Click Apply
With this, SNMP parameters for Versions 1 and 2c are configured and the changes are saved to the running configuration.
To enable the SNMP Manager running in Firewall Analyzer to make queries to SNMP Agent running in the firewall:
- In the ASDM main window, choose Configuration > Device Management > Management Access > SNMP
- In the SNMP Management Stations pane, click Add. The Add SNMP Host Access Entry dialog box appears
- In the Interface Name drop-down list, choose the interface on which the Firewall Analyzer resides
- In the IP Address field, enter the Firewall Analyzer IP address
- In the UDP Port field, enter the Firewall Analyzer UDP port, or retain the default port 162
- In the Community String field, enter the Firewall Analyzer community string. If no community string is specified for a management station, the value set in the Community String (default) field on the SNMP Management Stations pane is used
- In the SNMP Version drop-down list, choose the SNMP version used by the Firewall Analyzer
- If you have selected SNMP Version 3 in the previous step, in the Username drop-down list, choose the name of a configured user
- To specify the method for communicating with this management station, check the Poll check boxes
- Click OK. The Add Firewall Analyzer Access Entry dialog box closes.
- Click Apply.
With this, the management station is configured and changes are saved to the running configuration.
Configure SNMP Parameters for Version 3:
SNMP Version 3 allows you to configure additional authentication and privacy options for more secure protocol operations by means of SNMP server groups and users.
Carry out the following steps:
- In the ASDM main window, choose Configuration > Device Management > Management Access > SNMP
- In the SNMPv3 Users pane, to add a configured user or a new user to a group, click Add. To change user parameters, click Edit. To remove a configured user from a group, click Delete. When you remove the last user in a group, ASDM deletes the group
Note: | Once a user is created, you cannot change the group to which the user belongs. |
- The Add SNMP User Entry dialog box appears
- In the Group Name drop-down list, choose the group to which the SNMP user will belong. The available groups are as follows:
- Auth&Encryption, in which users have authentication and encryption configured
- Authentication_Only, in which users have only authentication configured
- No_Authentication, in which users have neither authentication nor encryption configured
- In the Username field, enter the name of configured user or new user. The username must be unique for the SNMP server group selected
- To have the password encrypted, click the Encrypt Password radio button. If you choose this option, you must enter the password as MD5 hash value.
- Indicate the type of authentication you want to use by clicking the appropriate radio button: MD5 or SHA
- In the Authentication Password field, type the password to use for authentication
- Indicate the type of encryption you want to use by clicking the appropriate radio button: DES or 3DES, or AES
- If you chose AES encryption, from the AES Size drop-down list, specify which level of AES encryption to use: 128 or 192 or 256
- In the Encryption Password field, type the password to use for encryption. The maximum number of characters allowed for this password is 64
- Click OK to create a group (if this is the first user in that group), display this group in the Group Name drop-down list, and create a user for that group. The Add SNMP User Entry dialog box closes
- The SNMPv3 Users pane lists the following information: SNMP Version 3 server group name, name of the user that belongs to the specified group, encrypted password setting, authentication setting, encryption algorithm setting, and the AES size setting
- Click Apply
With this, SNMP parameters for Version 3 are configured, and the changes are saved to the running configuration.
Virtual Firewall (Virtual Domain) logs
Prerequisite for context/vdom in Cisco Firewalls
The Cisco Firewall IP address should be DNS resolvable from Firewall Analyzer.
There is no separate configuration required in Firewall Analyzer for receiving logs from Virtual Firewalls of the Cisco physical device.
Note: | Configuration in Cisco device for Virtual Firewall |
Log IDs for Security Breach reports
Enable the below log IDs in Cisco device to get Security Breach reports.
| Event Type | Log IDs |
| Deny events | 106001, 106006, 106007, 106002, 106014, 106015, 106018, 106023, 304002, 710003, 605004, 710005, 420001, 420002, 420003 |
| Virus | 338006, 338204, 338008, 338005, 338203, 338007 |
| Attack | 400000-400050, 106016, 106017, 106021, 106022, 201003, 407002, 209003, 405001 |
| Rule | 106100 |
Log IDs for VPN reports
Enable the following syslog IDs based on your VPN connection type to get VPN reports
| VPN Connection Type | Log IDs |
| Point 2 Point | 603104, 603105, 603106, 603107, 603108, 603109, 603110 |
| IPSEC | 602303, 602304, 602305, 602306, 734001 |
| Misc | 109005, 109006, 113004, 113005, 113014, 113015, 113016, 113017 |
| Web VPN | 716001, 716002, 716038, 716039, 716055, 716056, 716057, 716058, 716059, 721016, 721018 |
| Any Connect | 113031, 113032, 113035, 113039, 751005, 751020 |
| VPN Client | 611101, 611102, 611103 |
| Other VPN events | 113019, 713228, 722030, 722031, 722051 |
Note: | Ensure the logging level for the above syslog IDs are set to Informational. |