Steps to configure SAML SSO for Smartlook
About Smartlook
Smartlook is a product analytics and session-replay app that lets teams see exactly how users interact with their web and mobile apps—turning real user behavior into actionable insights.
The following steps will help you enable SSO for Smartlook from Identity360.
Prerequisites
- The MFA and SSO license for Identity360 is required to enable SSO for enterprise applications.
- Log in to Identity360 as an Admin, Super Admin, or Technician with a role that has Application Integration and Single Sign-on permissions.
- Navigate to Applications > Application Integration > Create New Application and select Smartlook from the applications displayed.
Note: You can also find Smartlook using the search bar located at the top.
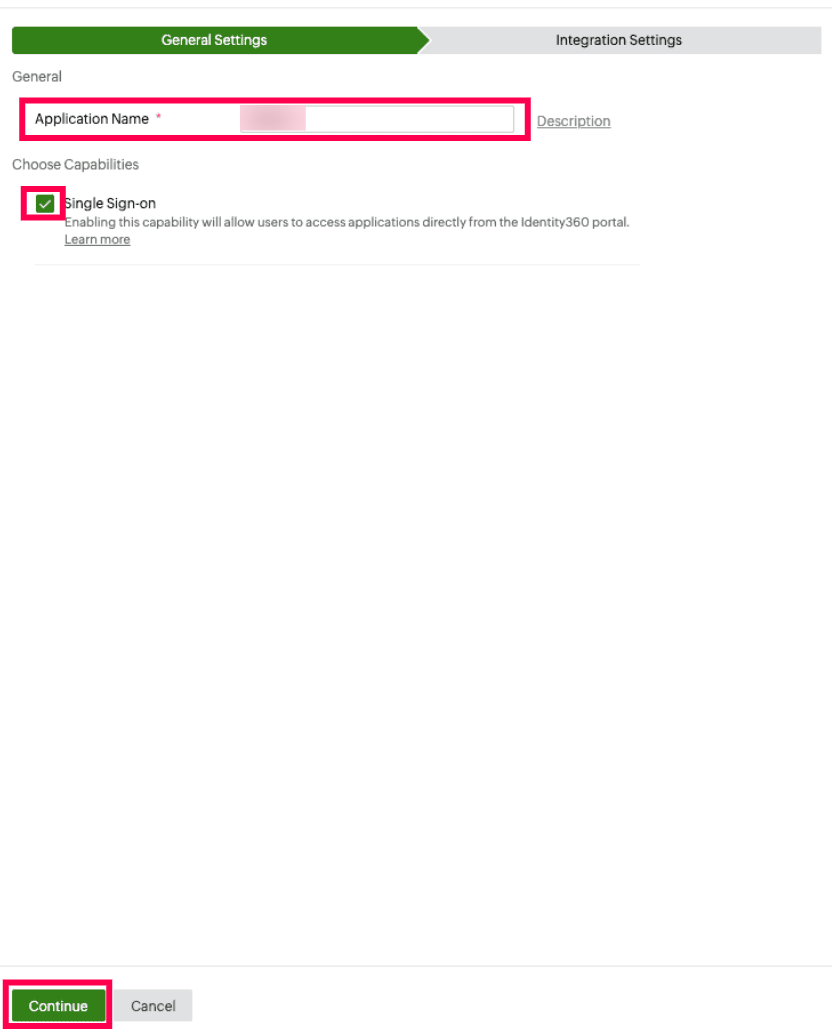
- On the General Settings tab, enter the Application Name and Description.
- Under Choose Capabilities, select Single Sign-on and click Continue.
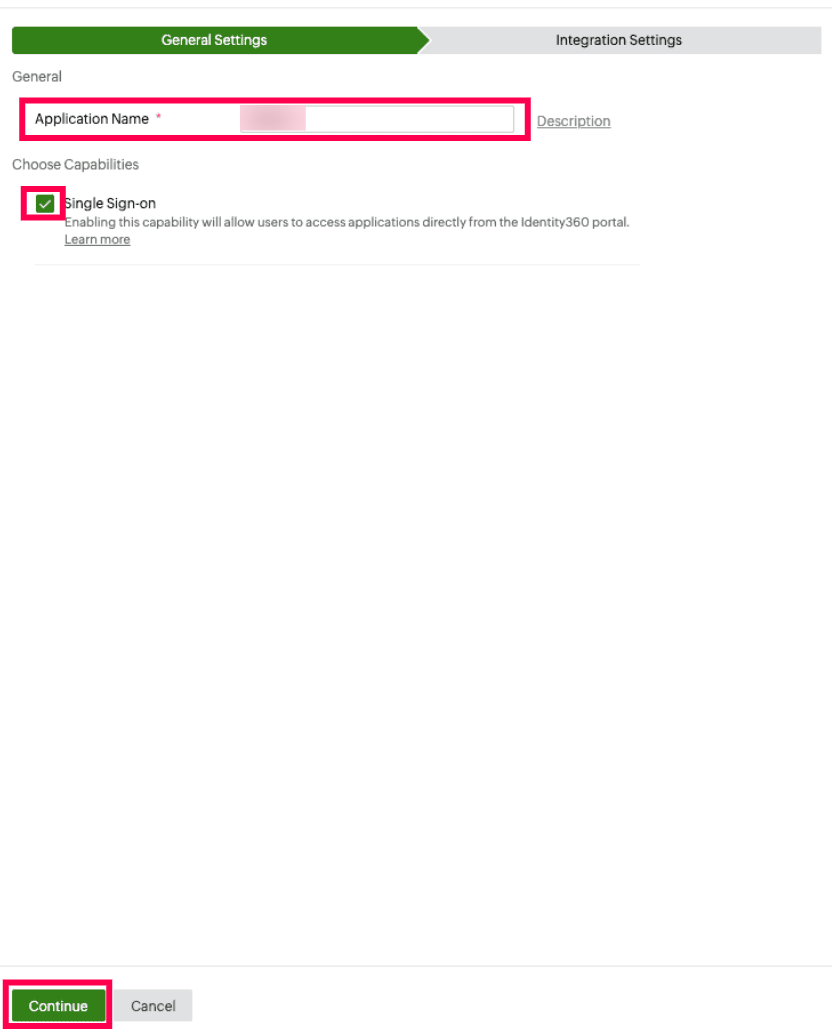 General Settings of SSO configuration for Smartlook
General Settings of SSO configuration for Smartlook
- On the Integration Settings tab, navigate to Single Sign On. Under Integration Settings, navigate to the Single Sign On tab, click IdP Details. You can configure SSO in Smartlook by uploading a metadata URL, manually configuring the settings, or automatically uploading a metadata file.
- For auto-upload of Metadata file: Download the metadata file to be uploaded during the configuration of Smartlook in Identity360 by clicking Download from the Metadata field.
- For manual configuration: Copy the Login URL, Logout URL, Entity ID, and Signing Certificate.
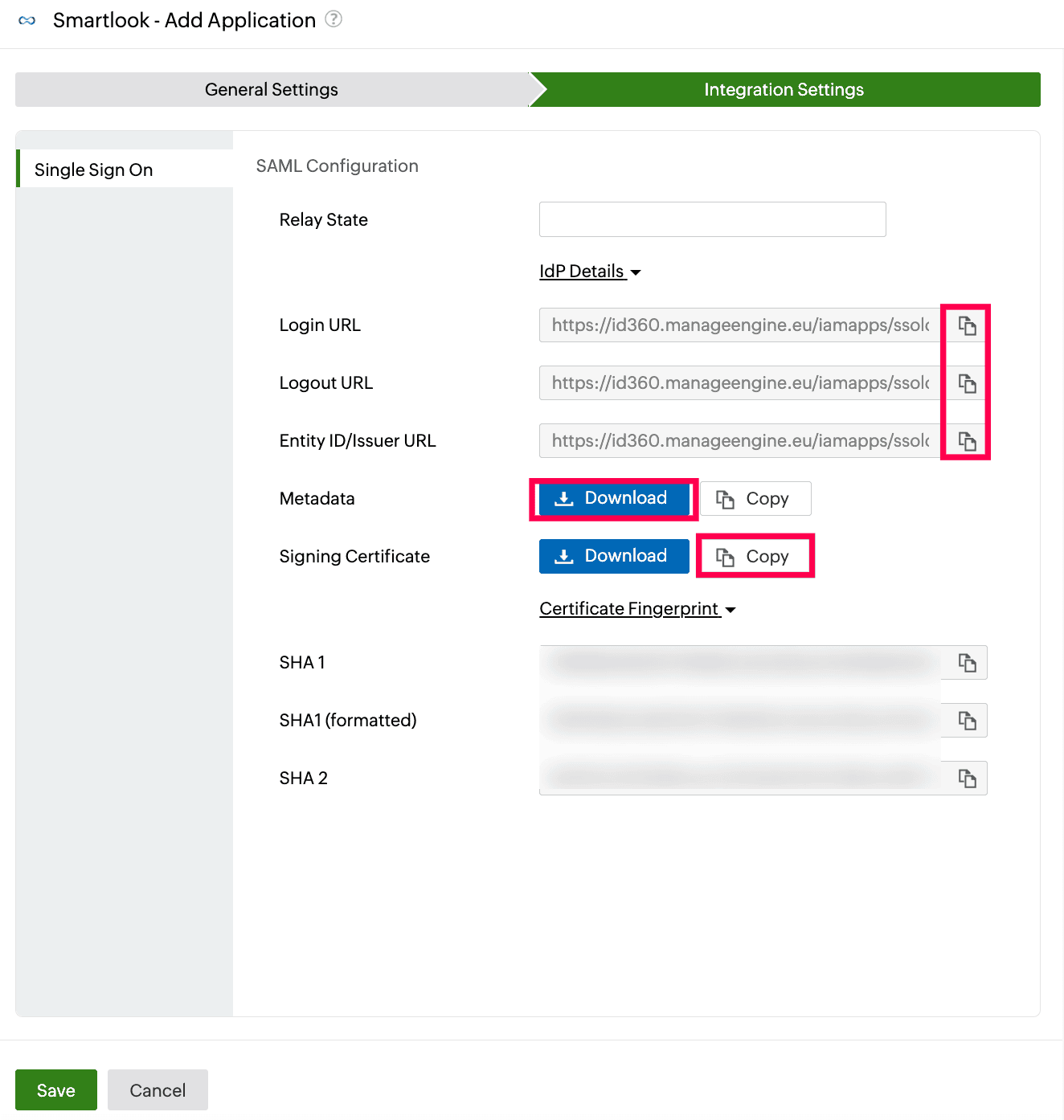 Integration Settings of SSO configuration for Smartlook
Integration Settings of SSO configuration for Smartlook
Smartlook (service provider) configuration steps
- Log in to Smartlook as an administrator
- In Organization settings, click Single sign-on (SSO).
- You can choose from three ways of uploading your SAML identity provider's metadata into Smartlook:
- Provide the Metadata URL value as instructed in these steps.
- Upload Metadata file downloaded from step 6a of prerequisites.
- Manually fill in Metadata details, including Entity ID, Login URL, Logout URL, and Signing Certificate copied from step 6b of prerequisites.
- To complete the setup, enter at least one email domain used by your organization’s members in the Domains section.
Note: Any user who signs in with an email address matching these domains will be automatically redirected to authenticate through your configured Identity360.
- Turn on SSO for your users by enabling the toggle at the top of the Configuration section.
Identity360 (identity provider) configuration steps
- Switch to Identity360's application configuration page.
- Enter the Relay State parameter, if necessary.
Note: Relay State is an optional parameter used with a SAML message to remember where you were or to direct you to a specific page after logging in.
- Click Save.
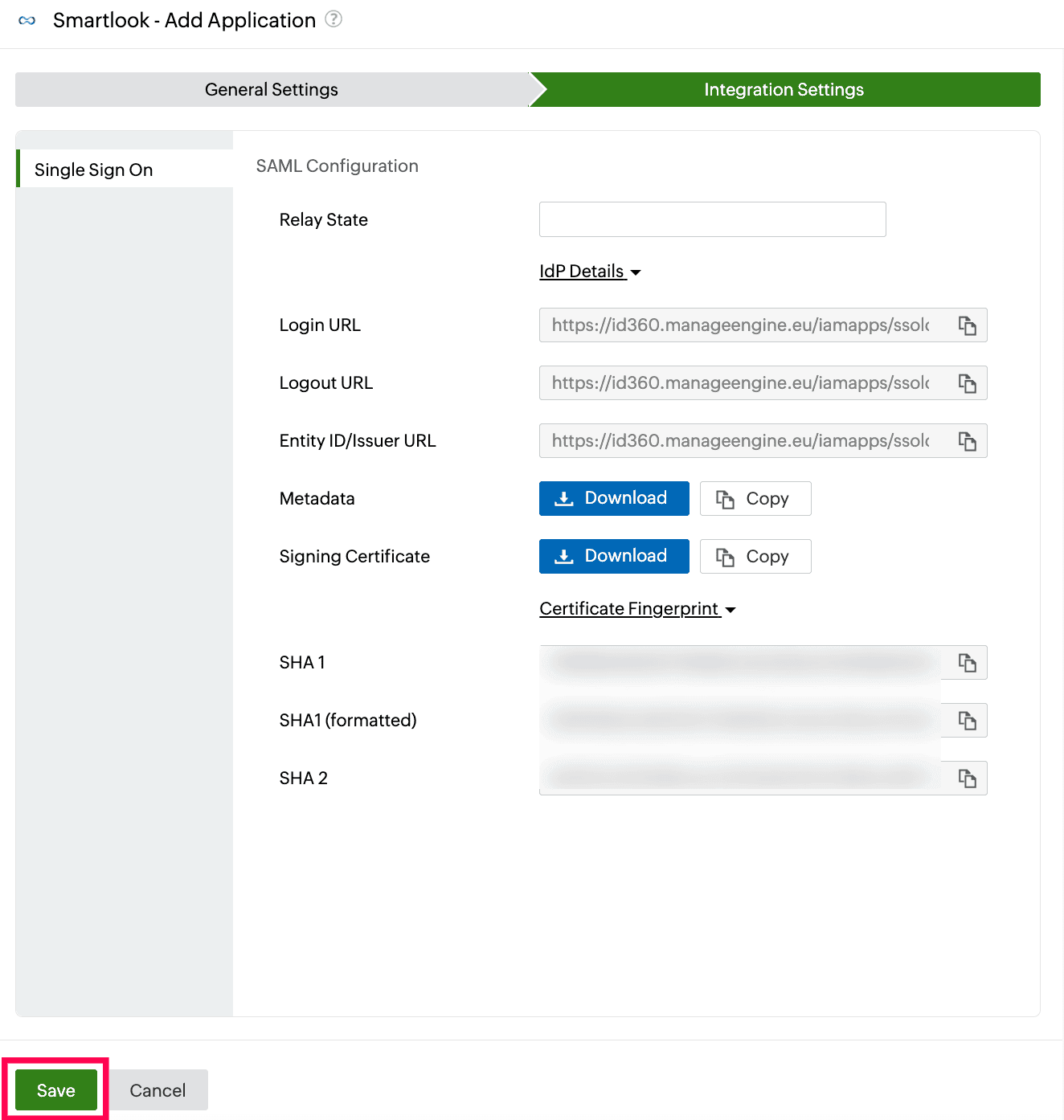 Integration Settings of SSO configuration for Smartlook
Integration Settings of SSO configuration for Smartlook
To learn how to assign users or groups to one or more applications, refer to this page.
Your users will now be able to sign in to Smartlook through the Identity360 portal.
Note: For Smartlook, both SP-initiatied and IdP-initiated flows are supported.
Steps to enable MFA for Smartlook
Setting up MFA for Smartlook using Identity360 involves the following steps:
- Set up one or more authenticators for identity verification when users attempt to log in to Sprout Social. Identity360 supports various authenticators, including Google Authenticator, Zoho OneAuth, and email-based verification codes. Click here for steps to set up the different authenticators.
- Integrate Smartlook with Identity360 by configuring SSO using the steps listed here.
- Now, activate MFA for Smartlook by following the steps mentioned here.
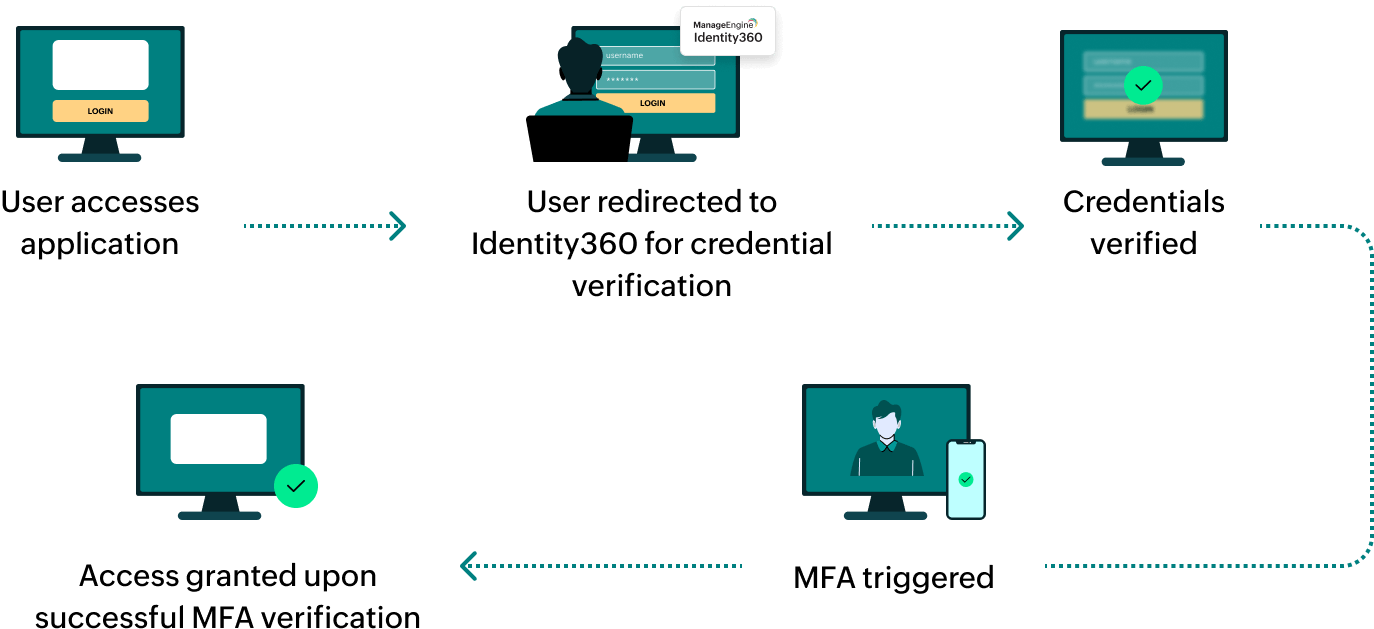
How does MFA for applications work in Identity360?
 General Settings of SSO configuration for Smartlook
General Settings of SSO configuration for Smartlook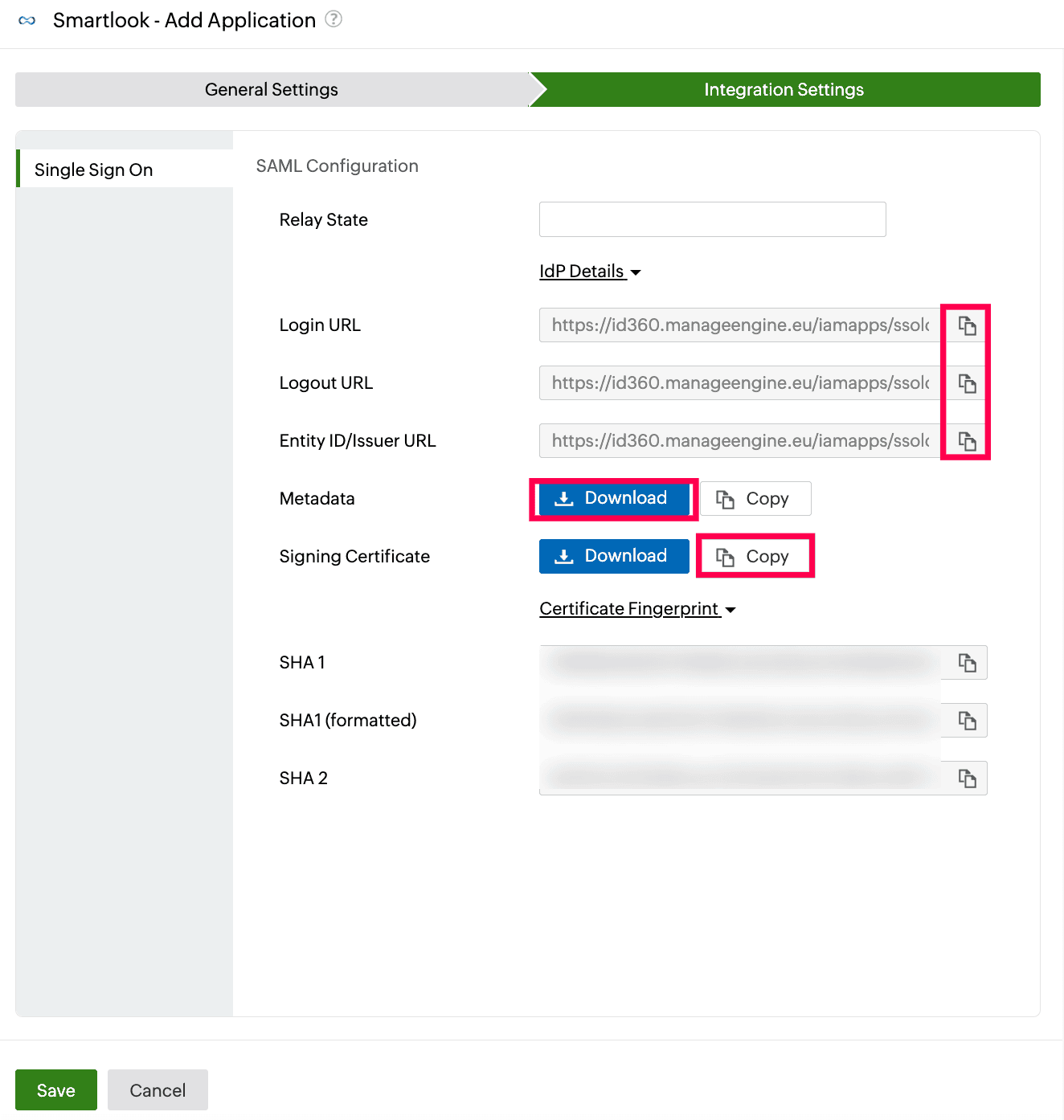 Integration Settings of SSO configuration for Smartlook
Integration Settings of SSO configuration for Smartlook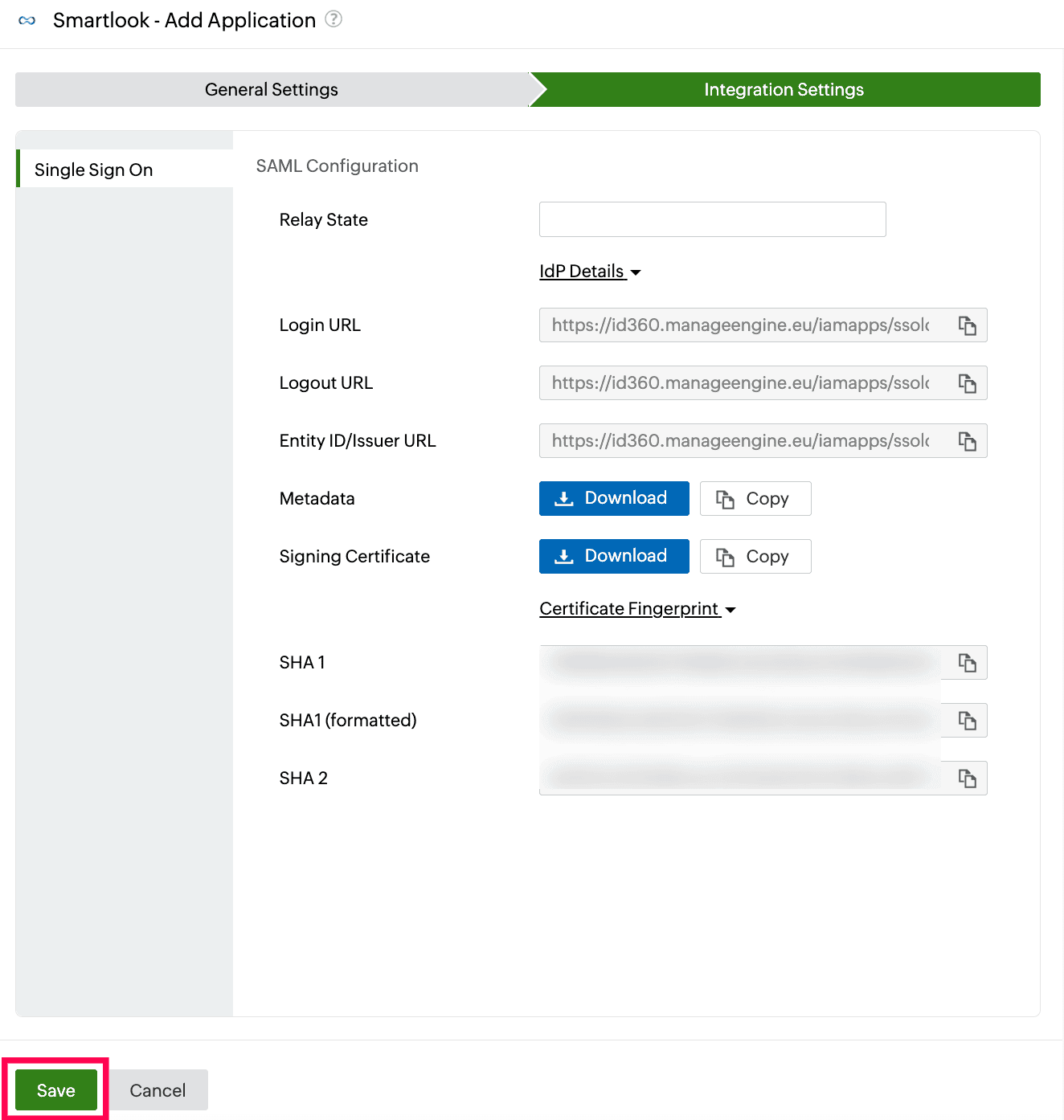 Integration Settings of SSO configuration for Smartlook
Integration Settings of SSO configuration for Smartlook