Understanding Endpoint Central web console
Table of Contents
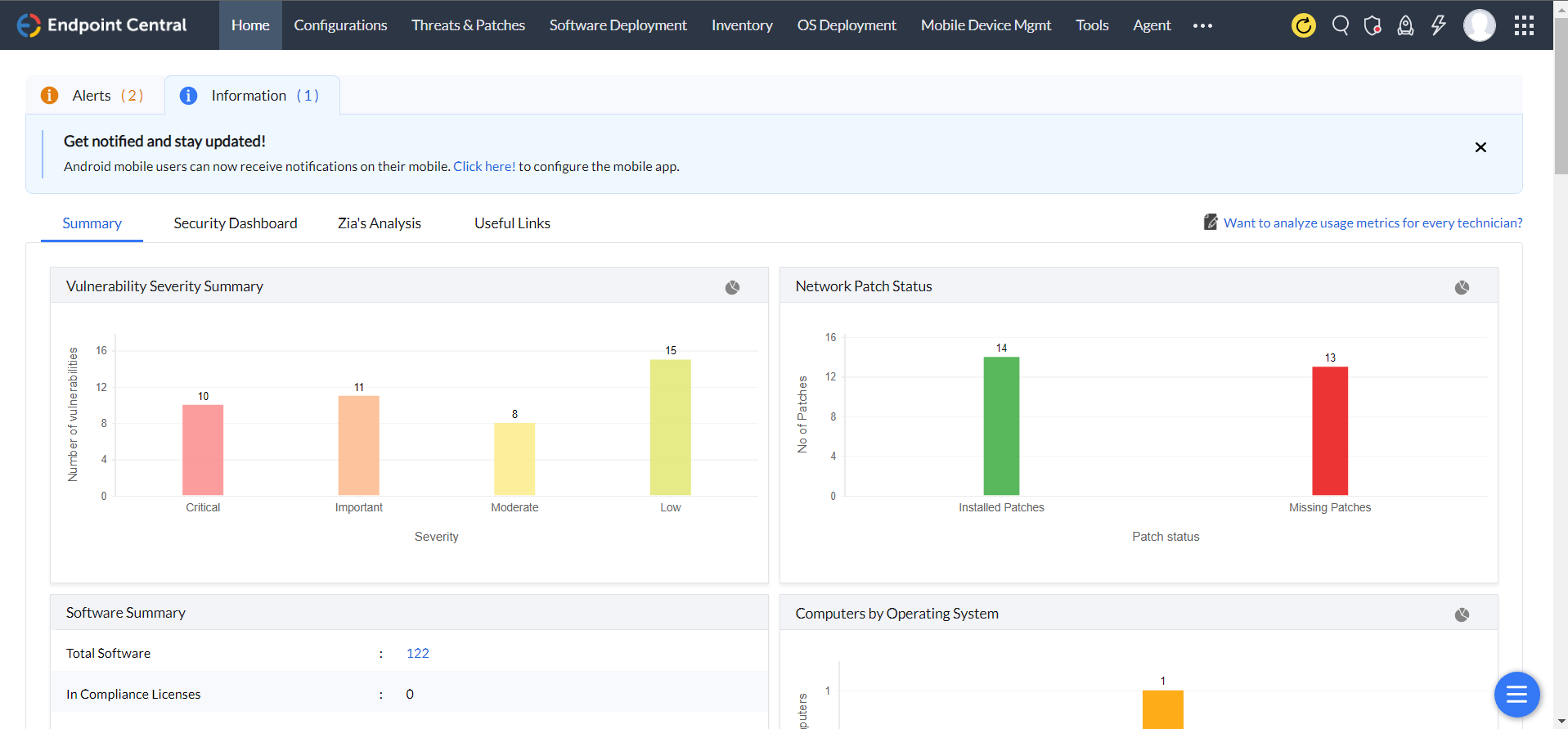
Endpoint Central web console presents information about endpoint management and security in a clear, well-organized, and easily understandable manner for administrators. The web console uses a multi-pane interface with tabs and quick links in the top pane, tab-specific links in the left pane, and object-specific views in the right pane. It resembles the image shown below:
What is a tabbed pane
Tabs make navigation between various modules/features easier. Each tab represents a specific module/feature. The content of the left pane changes based on the selected tab. The product includes the following tabs:
- Home: The home tab provides a quick overview of all the features enabled in Endpoint Central. For example: You can get a quick summary of all the software installed, different network patch statuses, severe vulnerabilities, total number of devices managed and so on.
- Configurations: The configurations tab provides core functions of the product. It allows to enable essential features and helps defining configurations and collections, as well as viewing configurations based on type and status.
- Threats and Patches: This tab provides details of available and missing patches, along with options to install them.
- Software Deployment: The software deployment feature allows to distribute software in all the managed devices. It provides options to create a repository for MSI and EXE packages, which can be used to deploy software to Windows/M Linux/Mac machines on the network.
- Inventory: Provides details of software and hardware inventory of the network. It enables managing software licenses and prohibited software.
- OS deployment: The OS deployment tab coupled with the zero-touch deployment feature enables administrators to efficiently deploy and manage operating systems across multiple endpoint devices, streamlining the provisioning process and ensuring consistent configurations.
- Mobile Device Management: The mobile device management feature allows administrators to centrally monitor, secure, and manage mobile devices within the network, ensuring compliance, data protection, and efficient device administration.
- Tools: The Tools tab allows sharing and controlling a remote desktop through a web browser. It also provides the ability to schedule tasks such as Disk Defrag, Check Disk, and Disk Cleanup on different machines in the network.
- Agent: The Agent tab provides a centralized view and management of the deployed agents on endpoint devices, allowing administrators to monitor and configure various settings and policies for efficient endpoint security management.
- Reports: The reports tab offers comprehensive reports of defined configurations based on users, computers, and type. It also provides ready-made reports of Active Directory components. For more details on available reports, refer to the Viewing Reports topic.
- Admin: The admin tab helps customize the product for the specific environment. It allows defining the management scope, managing inactive users in the domain, managing MSI/EXE files and scripts, and offers other personalization options. For further details, refer to the setup section.
- Browser: The browser security feature ensures secure and protected browsing by implementing various security measures, such as URL filtering, malware detection, and data encryption etc.
- Device Control: The device control security feature enables administrators to manage and control the usage of peripheral devices to enhance data security and prevent unauthorized data transfers.
- App Ctrl: The Application control feature allows administrators to manage and control the usage of applications, ensuring compliance, preventing unauthorized software installations, and mitigating potential security risks.
- Bitlocker Management: The BitLocker management feature enables administrators to centrally manage and control the encryption settings and recovery keys for BitLocker-protected drives on endpoint devices, enhancing data protection and security.
- Anti-Ransomware: The anti-ransomware feature provides advanced protection against ransomware attacks by actively monitoring and blocking suspicious file activities, ensuring the integrity and availability of data on endpoint devices.
- Endpoint DLP: The Endpoint DLP (Data Loss Prevention) feature offers comprehensive data protection by monitoring and preventing sensitive data from being leaked or mishandled on endpoint devices within the network.
- Support: If you want to reach us out for your needs such as getting technical support, requesting new features, participating in user discussions and so on, navigate to the support tab. The support tab provides self-diagnostic details about the product.
Apart from the tabs, it also has the following links on the top right corner:
- Contact Us: To reach us to support, feedback, sending logs, joining web conference to troubleshooting, etc.
- Personalize: To customize the skin, password, and session expiry time.
- License: To upgrade to the licensed version of the software and to view the license details.
- About Us: To view the product version details.
- Help: To view the product help documentation.
- Sign Out: To sign out the client.
What are quick links?
Quick links enables you to navigate to the frequently visited pages instantly.
What is a left pane?
The navigation links in left pane enables navigation across the various features in the tab. The left-side navigation links changes dynamically according to the tab selected.
What is a content pane ?
The content pane displays the specific view of the currently selected item from the tabbed pane, quick links or the left pane.




