In-scope entities should prepare for a 24-hour initial notification and a 72-hour full notification following awareness of a qualifying incident.
On this page
The Cyber Security and Resilience (Network and Information Systems) Bill (CSRB) represents the most substantive recalibration of the United Kingdom’s (UK's) cyber resilience regime since the introduction of the Network and Information Systems (NIS) Regulations 2018. The original NIS framework established a principle-based obligation: Operators of essential services and certain digital providers were required to implement appropriate and proportionate security measures and notify regulators of significant incidents.
The CSRB does not abandon that architecture. It tightens it. It expands scope, accelerates reporting obligations, strengthens supervisory tooling, increases financial exposure, and formalizes supply chain accountability mechanisms. The result is a regime that moves from broad resilience expectations toward more structured, time-bound, and enforceable governance discipline.
For IAM professionals, this shift matters because identity controls sit at the intersection of all these reforms. Access governance becomes a primary mechanism through which organizations demonstrate that resilience is operational, not theoretical.
Where the Bill stands
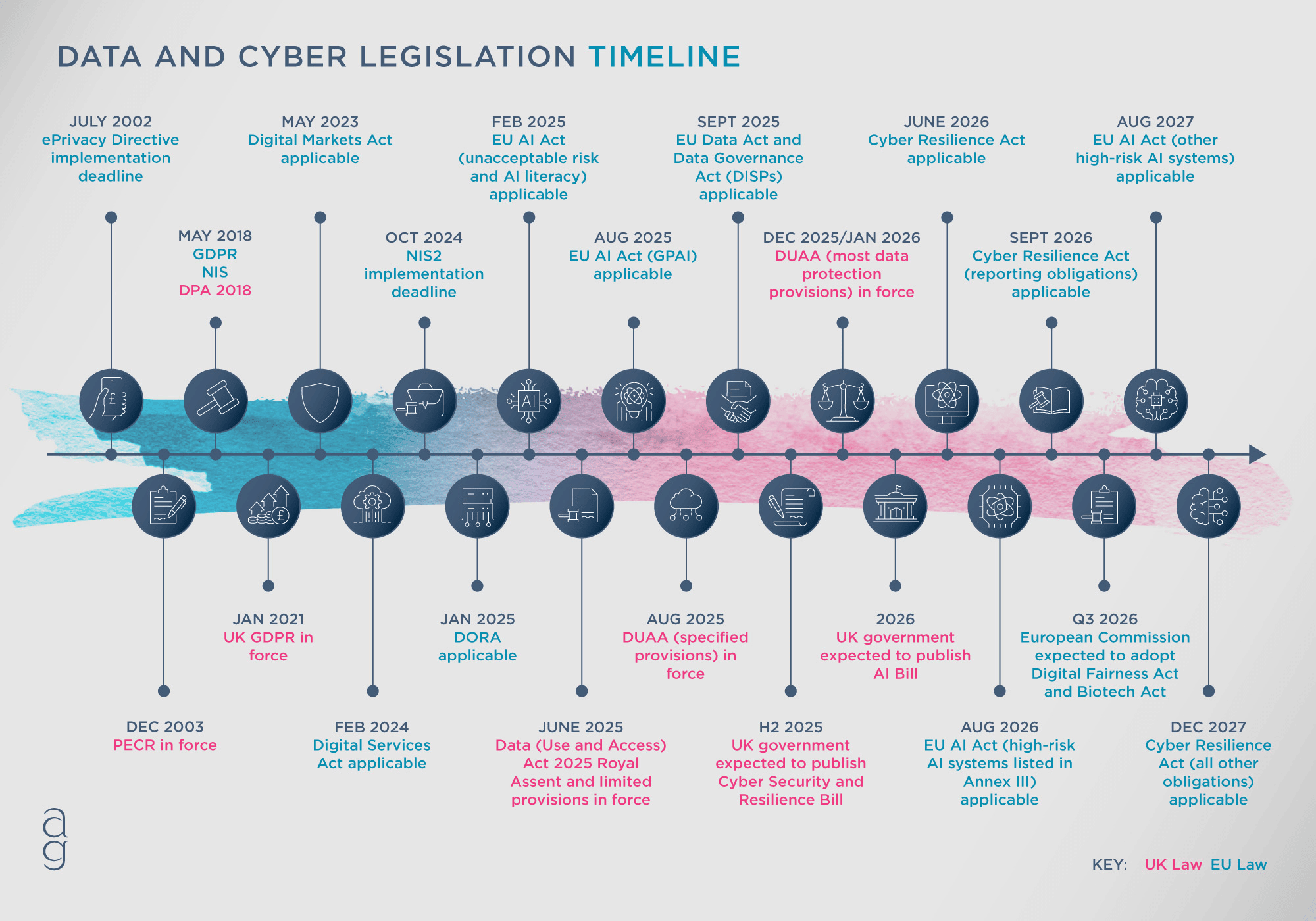
As of early 2026, the Bill has not yet received Royal Assent. However, its policy direction, supporting documents, and impact assessment provide sufficient clarity for organizations to begin alignment planning.
Source: The trajectory signals regulatory tightening rather than dilution. IAM teams should therefore treat the Bill’s direction of travel as a planning baseline rather than a speculative proposal.
Major changes introduced
The CSRB rewires the UK's NIS framework in five high-impact ways. These changes reshape how compliance risk is assessed and how identity governance must operate within regulated environments.
1. Accelerated and staged incident reporting
The Bill introduces a structured, two-stage reporting model, moving away from an approach that triggered notification only once disruption had clearly materialized. For multiple regulated categories, an initial notification is required within 24 hours of first awareness of a qualifying incident. A full notification must follow within 72 hours.
For IAM teams, this compresses investigative timelines. Identity-driven compromise, including credential abuse, privileged escalation, or token misuse, must be assessed rapidly enough to determine regulatory relevance within a single business day. Logging maturity and cross-system traceability become operational necessities rather than aspirational capabilities.
2. Explicit customer notification duties
The CSRB introduces a clear duty for data center services, relevant digital service providers, and relevant managed service providers (RMSPs) to notify customers following a full regulatory notification. Organizations must take reasonable steps to identify customers likely to be adversely affected and notify them as soon as reasonably practicable.
Identity systems frequently operate across multiple tenants or downstream relying parties. A compromise within an authentication or federation layer can propagate beyond a single environment. IAM programs therefore need documented dependency mapping and predefined impact classification to determine which customers are likely to be affected in identity-related incidents.
3. Turnover-based penalty structure
The penalty regime becomes more consequential under the CSRB. NIS penalty caps move to a turnover-based structure with defined standard and higher maximum amounts. For undertakings, the standard maximum is £10 million or 2% of global turnover, whichever is greater. The higher maximum is £17 million or 4% of global turnover, whichever is greater.
Where unauthorized access or data authenticity compromise can be traced to identity control weaknesses, enforcement exposure becomes financially material. Identity governance therefore transitions from an operational safeguard to board-level financial risk control.
4. Expanded regulator powers and cost recovery
Regulator tooling is strengthened, including explicit cost recovery and charging schemes. Regulatory tooling refers to the authorities and mechanisms regulators use to supervise compliance, such as requesting information, conducting assessments, and initiating enforcement actions. This signals a more interventionist supervisory posture. Regulators will have broader authority to request information, assess compliance maturity, and recover enforcement costs.
IAM documentation, architectural clarity, and audit readiness will increasingly influence how smoothly supervisory reviews proceed.
5. Introduction of a national security layer
The Bill adds a national security dimension. The Secretary of State gains powers to issue directions where necessary and proportionate for national security purposes. Associated information-sharing provisions may include engagement with the Government Communications Headquarters.
While these powers are exceptional, they reinforce the reality that identity compromise in critical sectors can escalate beyond organizational boundaries. Identity governance is therefore tied not only to regulatory compliance but to national resilience considerations.
A comparative view: The UK's NIS baseline and the CSRB shift
| Topic | UK's NIS Regulations baseline | CSRB direction and IAM impact |
|---|---|---|
| Incident reporting | Significant disruption focus; less structured early warning | 24-hour initial and 72-hour full notification; earlier trigger for identity-related compromise |
| MSPs | Not clearly regulated as a distinct class | RMSPs explicitly in scope; administrative access becomes compliance focal point |
| Critical suppliers | Indirect supply chain handling | Direct designation power; systemic IAM dependencies may be regulated |
| Penalty structure | Fixed monetary caps | Turnover-based caps tied to global revenue |
| Customer notification | Primarily regulator-mediated | Explicit duty to notify likely adversely affected customers |
Scope expansion and who is covered in ways that most affect IAM
The structural reforms above matter only insofar as organizations fall within scope. The CSRB expands the UK's NIS framework to cover additional categories and strengthens supply chain oversight.
Categories newly emphasized or brought into scope
The impact assessment summarizes the intent to:
- Bring RMSPs into scope.
- Include data centers and load controllers.
- Strengthen supply chain handling via critical supplier designation.
- Reinforce incident reporting and regulator powers.
For IAM leaders, the practical question is not abstract compliance. It is categorization.
1) Are we a relevant digital service provider?
- Relevant digital service providers (RDSPs) include certain digital services such as online marketplaces, online search engines, and cloud computing services. Micro and small enterprises are excluded from the primary definition.
- IAM organizations offering SaaS-based identity capabilities must evaluate whether their service model falls within a defined digital service category or whether exposure arises indirectly through customers.
2) Are we an RMSP?
- If an organization provides ongoing management to customers by obtaining access to their systems, it is much closer to the definition of an RMSP than a pure software vendor.
- This distinction is critical for IAM providers that administer customer directories, manage authentication policies, or operate privileged access on behalf of clients. Administrative access is the regulatory hinge point.
3) Could we be designated as a critical supplier?
- Even where an organization does not meet primary RDSP or RMSP definitions, it may face exposure under the critical supplier designation regime. If a product or service represents a systemic dependency for essential or regulated services, designation risk exists regardless of organizational size.
- Identity providers, federation platforms, and privileged access infrastructure frequently underpin multiple regulated entities. This creates potential regulatory gravity around identity-layer services.
Connecting scope expansion to identity governance obligations
The scope analysis above flows directly into practical IAM implications. If an organization qualifies as an RDSP or RMSP, or if it faces potential critical supplier designation, then the five structural reforms previously outlined become operational realities rather than theoretical developments.
Accelerated reporting timelines require mature identity telemetry. Customer notification duties require clear mapping between identity services and downstream customers. Turnover-based penalties elevate privilege governance to financial risk management. Expanded regulator powers increase scrutiny of authentication strength and access control discipline. National security overlays underscore the systemic nature of identity compromise.
Scope determines exposure. Exposure determines governance expectations.
Enforcement, financial exposure, and identity risk concentration
Turnover-based caps transform the economic calculus of identity failure. Where identity control weaknesses enable unauthorized access or compromise data authenticity, regulators may assess whether appropriate and proportionate measures were in place.
Privileged access segmentation, strong authentication for administrative accounts, and structured logging are therefore not merely technical enhancements. They are demonstrable indicators that an organization exercised reasonable governance.
Identity risk concentration tends to reside in privileged accounts, delegated administration paths, and federated trust relationships. Under a tightened supervisory regime, weaknesses in these domains may be interpreted as governance shortcomings rather than isolated operational errors.
Strategic alignment for IAM leaders
The CSRB does not require named technologies. It requires demonstrable control. For IAM leaders, that means shifting from questions like, "Do we have the right tools?" to "Can we prove disciplined access governance under regulatory scrutiny?"
Four areas matter most.
Privileged access governance
Privileged identities will sit at the center of supervisory attention. Organizations should be able to demonstrate that:
- Administrative accounts are individually attributable.
- Standard and privileged identities are segregated.
- Least privilege is enforced through structured role design.
- Elevated access is time-bound where possible.
- Privileged activity is logged and reviewable.
Under a 24-hour reporting model, the ability to clearly identify which privileged accounts were involved in an incident is not optional. It is foundational to regulatory credibility.
Strong authentication and access proportionality
The Bill does not explicitly mandate MFA, but strong authentication for high-risk access paths will likely be treated as a baseline expectation. IAM leaders should assess whether privileged, remote, and federation control paths are protected by authentication mechanisms proportionate to their risk.
Inconsistent enforcement of strong authentication weakens the defensibility of the overall control framework.
Identity observability and reporting readiness
Accelerated reporting timelines mean IAM teams must rapidly articulate:
- What happened
- Which identities were involved
- What systems may be affected
This requires structured identity logging, retained audit trails, and rehearsed incident response playbooks. Without mature observability, compliance timelines become difficult to meet.
Supplier and third-party access oversight
Where vendors or MSPs obtain access to internal systems, their identities should be governed under the same discipline as internal administrators. Access should be scoped, monitored, and time-bound.
The CSRB’s supply chain emphasis means identity risk does not stop at the organizational boundary.
Frequently asked questions
No. Exposure depends on whether the organization qualifies as an RDSP, an RMSP, or is designated as a critical supplier.
Yes. While certain definitions exclude micro and small enterprises from primary categories, critical supplier designation may apply where systemic impact is plausible.
Because unauthorized access and compromise of data authenticity are explicitly framed as security failures. Identity controls are the primary mechanism for preventing and evidencing such failures.
Related solutions
ManageEngine AD360 is a unified IAM solution that provides SSO, adaptive MFA, UBA-driven analytics, and RBAC. Manage employees' digital identities and implement the principles of least privilege with AD360.
To learn more,
Sign up for a personalized demoManageEngine Log360 is a unified SIEM solution with UEBA, DLP, CASB, and dark web monitoring capabilities. Detect compromised credentials, reduce breach impact, and lower compliance risk exposure with Log360.
To learn more,
Sign up for a personalized demoThis content has been reviewed and approved by Ram Vaidyanathan, IT security and technology consultant at ManageEngine.