Due to the recent crisis, organizations have been forced to consider alternative workplace options. Organizations need a virtual private network (VPN) to keep employees adapting to remote work connected to the organization's IT network.
While VPNs have a lot to offer, they also come with their own operational and security challenges. Let's explore some of these challenges, and learn about how Log360 can help resolve them.
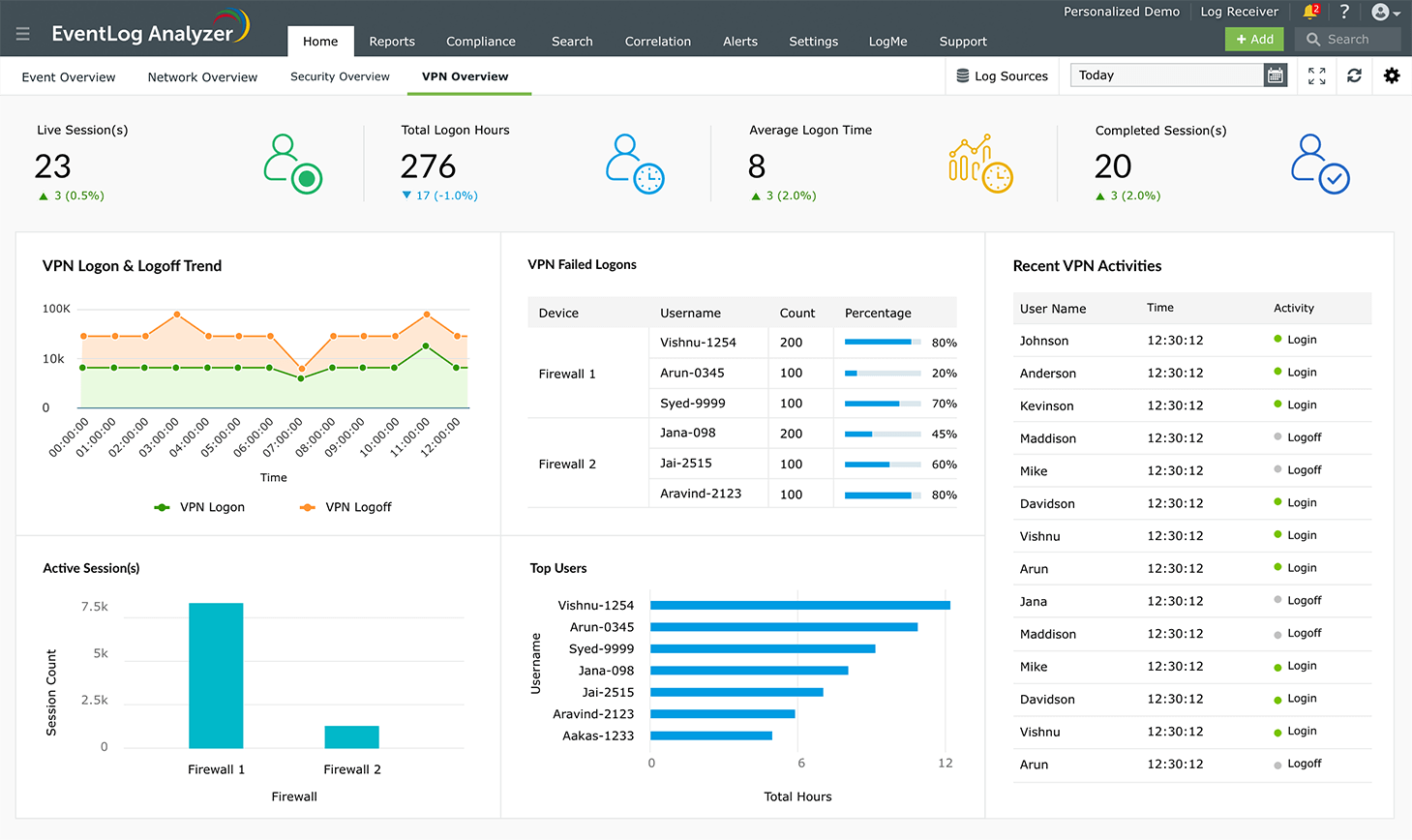
As the number of remote workers increases around the world, it's becoming harder for enterprises to track all their activity. With Log360's VPN monitoring feature, organizations can monitor their employees' VPN sessions.
The VPN Session Monitoring report provides the following critical information:
With these reports, monitoring employee productivity during remote work is easy. If your organization is on the larger side with several teams and employees, it can be difficult to keep track of what each of them is doing and how they are progressing.
With remote workers scattered throughout different regions, Log360 provides a central log management solution. Data on employees' active VPN sessions, the device on which the user is logged on, the duration of each session, and the status of the connection helps you measure employees' productivity.
With employees and data residing outside the traditional perimeter, cybercriminals are leveraging the extended attack surface remote environments present to carry out cyberattacks. Using Log360's VPN monitoring feature, organizations can receive VPN-related alerts to warn them about potential security risks. You can create a custom alert profile, which helps trigger an alert when the number of active VPN sessions exceeds a particular value. This option can be configured based on the organization's needs.
Recent cyberattacks indicate that cybercriminals are targeting VPN connections to establish a foothold in the organization's network. With Log360, an alert can be created at the event of a remote VPN connection established from a blacklisted VPN source location. This gives security admins the upper hand to detect malicious intrusion attempts immediately, and respond as quickly as possible.
Log360 also provides correlation alerts that will warn organizations about potential security threats.
When multiple VPN logon failures from the same user account occur within a short time period, Log360's correlation rule will trigger an alert, as this is a potential security threat.
When multiple successful VPN connections occur from the same user at different locations within a given time period, an alert will be triggered. These correlation alerts are crucial in combating unusual security threats, as they save time and help security admins prioritize security incidents.
Log360 provides an overview dashboard and a set of built-in reports. These help security admins constantly monitor changes in the network with instant access to crucial information regarding VPN security, including:
When it comes to cybersecurity, everyone's role matters. During uncertain times like these, here are some best practices that organizations can follow to strengthen their remote access architecture.
For more information on securing your network during this global crisis, check out our remote work page including regularly updated resources on how to secure your remote workforce.