Adhering to compliance standards in the network industry, especially with various industry-standard policies, is essential. These policies establish regulations to protect your IT infrastructure from external threats stemming from security vulnerabilities. One such crucial compliance policy is the CIS Benchmark compliance. On this page, we'll be looking at:
Why is CIS Benchmarks compliance crucial?
Compliance is beneficial for all types of network infrastructures, but it is especially vital for highly dynamic infrastructures where new devices from different vendors and models are continually added.
In such scenarios, relying on manual efforts often leads to employing default configurations for newly introduced systems, which may be convenient but not secure. Administrators struggle to manually monitor each device and their configurations, making it challenging to maintain a steady baseline configuration. Also, manual processes increase the risk of poorly configured systems and paves the way for external threats such as hacking, legal fines, and reputational damage.
A CIS Benchmark Compliance tool is necessary to efficiently track these benchmarks in large network infrastructures with diverse devices and vendors. This is because manually assessing each device against the extensive benchmarks, each spanning about 800 pages with over 300 recommendations, is impractical.
Achieving CIS Benchmark compliance with Network Configuration Manager
Network Configuration Manager boasts a dedicated compliance management feature to adhere to any compliance policies. Now, we have integrated CIS Benchmarks into this functionality.
The devices supported for CIS Benchmarks compliance and standards include Cisco IOS and Cisco ASA device types. If your network environment extensively utilizes these device types, you can leverage Network Configuration Manager to maintain compliance with all CIS Benchmark standards.
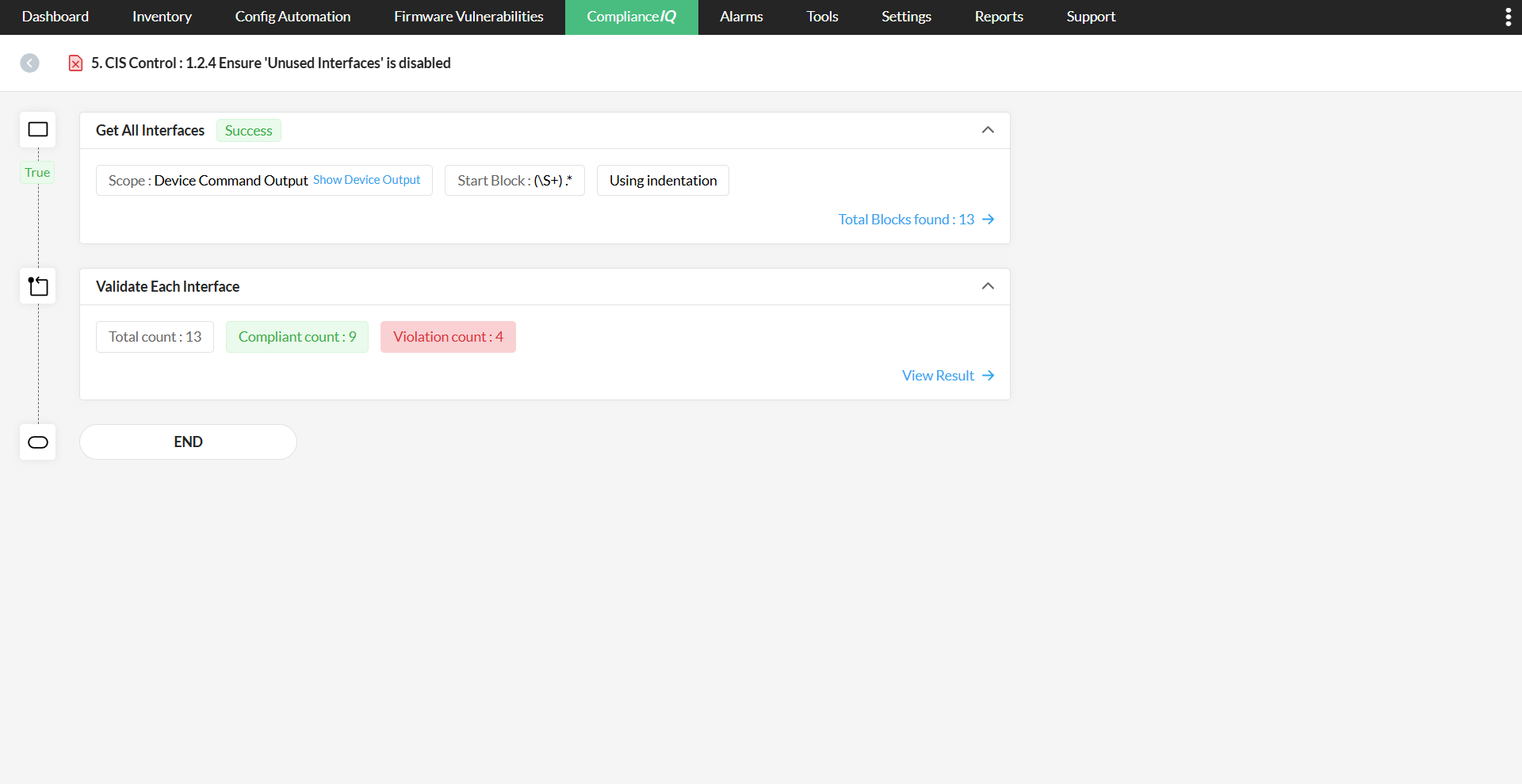
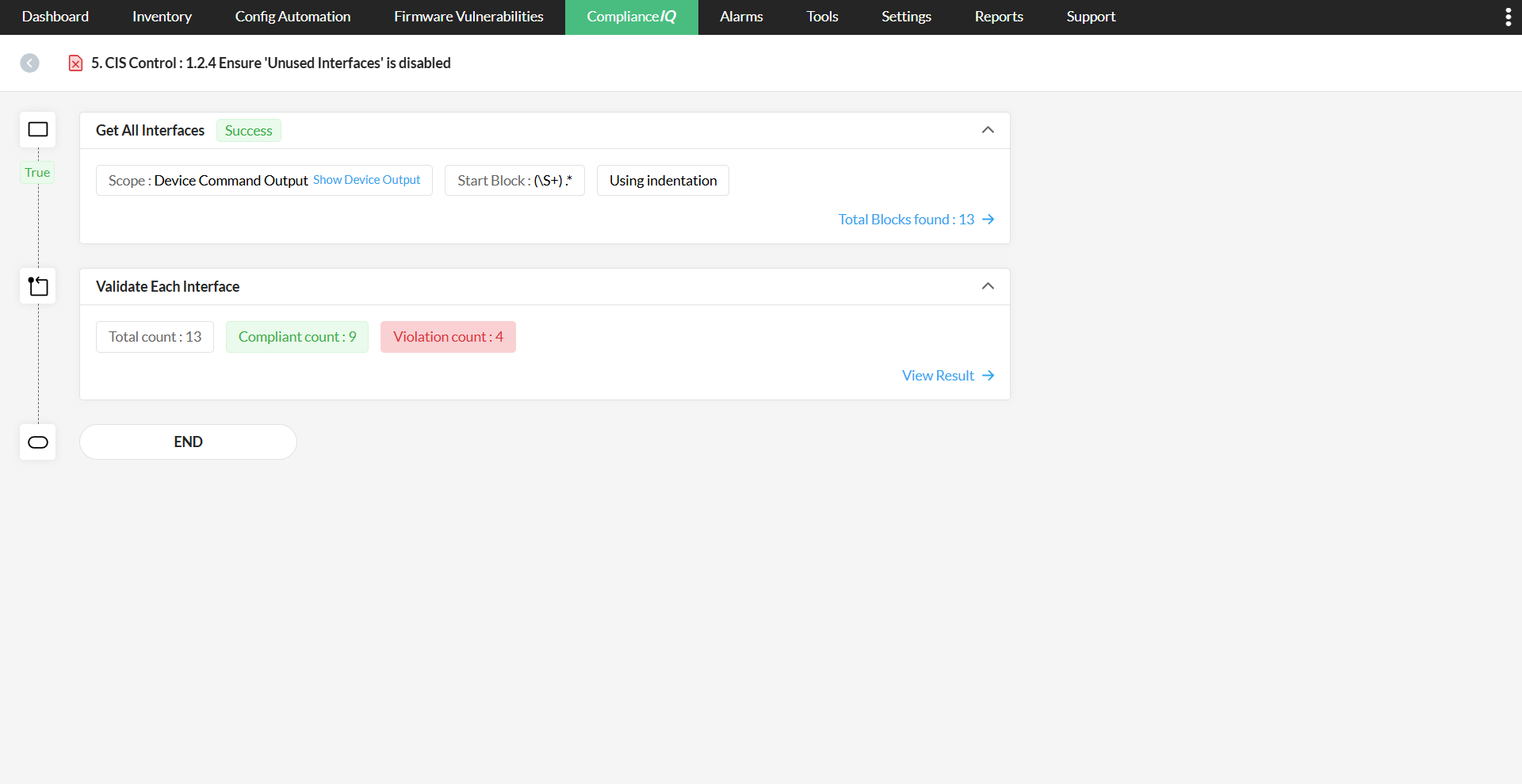
Network Configuration Manager consistently evaluates all configurations within your systems based on the recommendations outlined in the CIS Benchmarks. It promptly identifies any violations and provides detailed, step-by-step guidance to facilitate compliance. Each CIS Benchmark is tailored for a specific product, service, or system, encompassing recommendations for all configurations associated with them. Adhering to the recommendations within a CIS Benchmark ensures that the product or system is configured to meet the highest security standards.
How compliance works in Network Configuration Manager:
The CIS Benchmarks and compliance standards required for compliance will be readily accessible. Upon discovery of Cisco IOS or ASA devices, the policy will automatically align with the specific requirements for these devices, eliminating the need to manually create or associate policies.
Key functionalities within Network Configuration Manager to leverage for CIS compliance
- Schedule CIS compliance checks
- Remediate CIS non-compliance issues using Configlets
- Obtain real-time, dedicated compliance reports
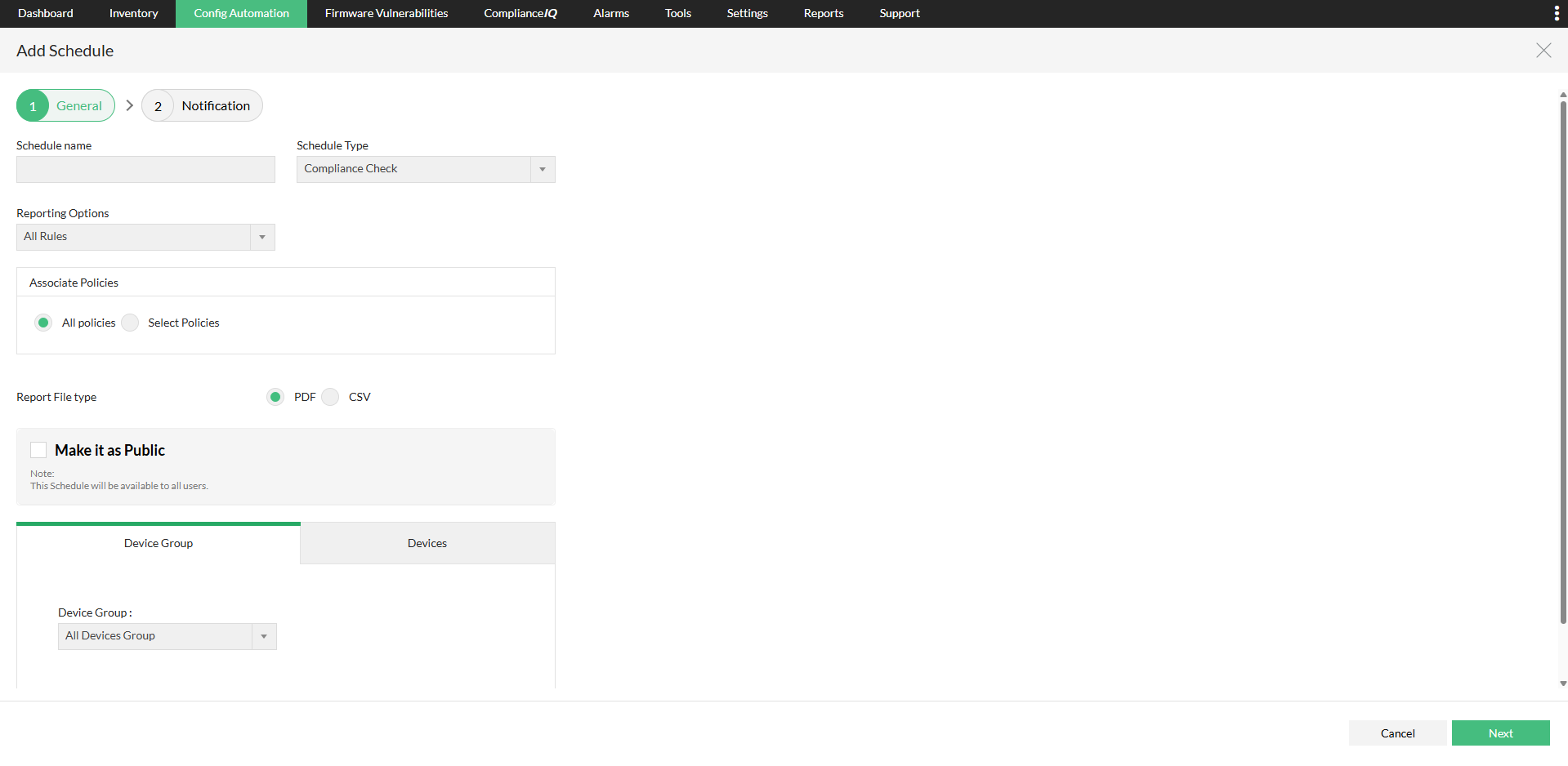
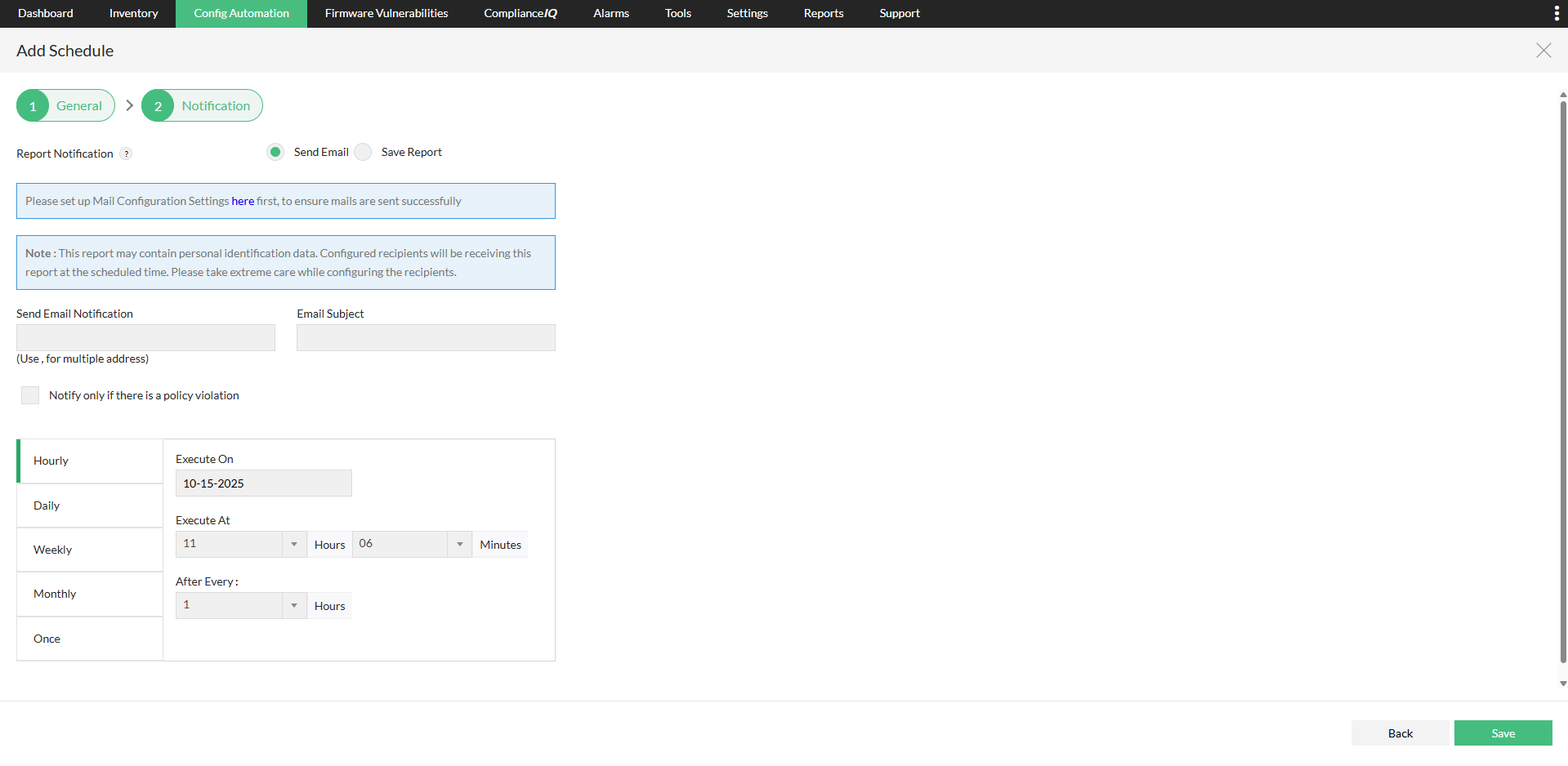
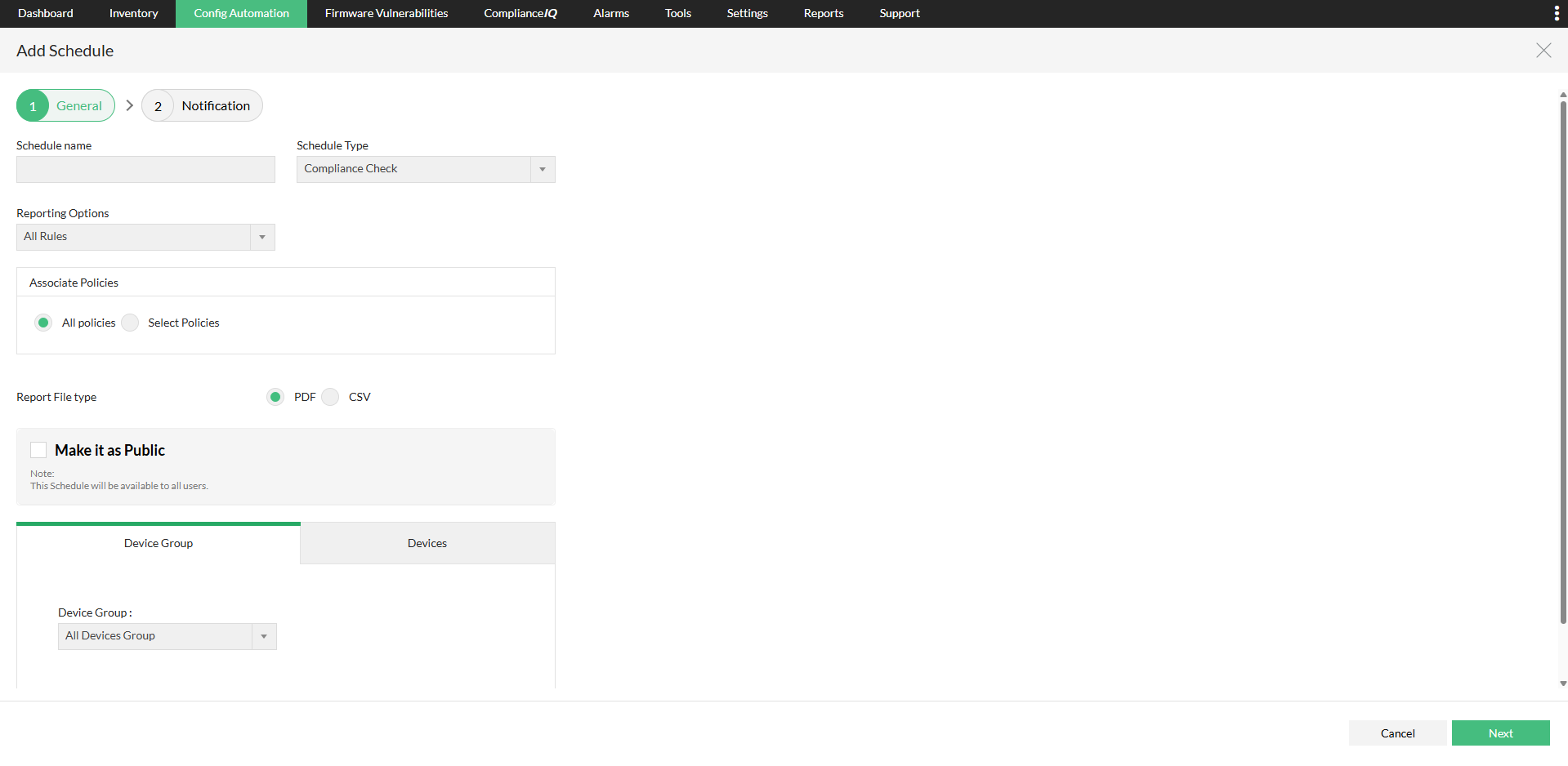
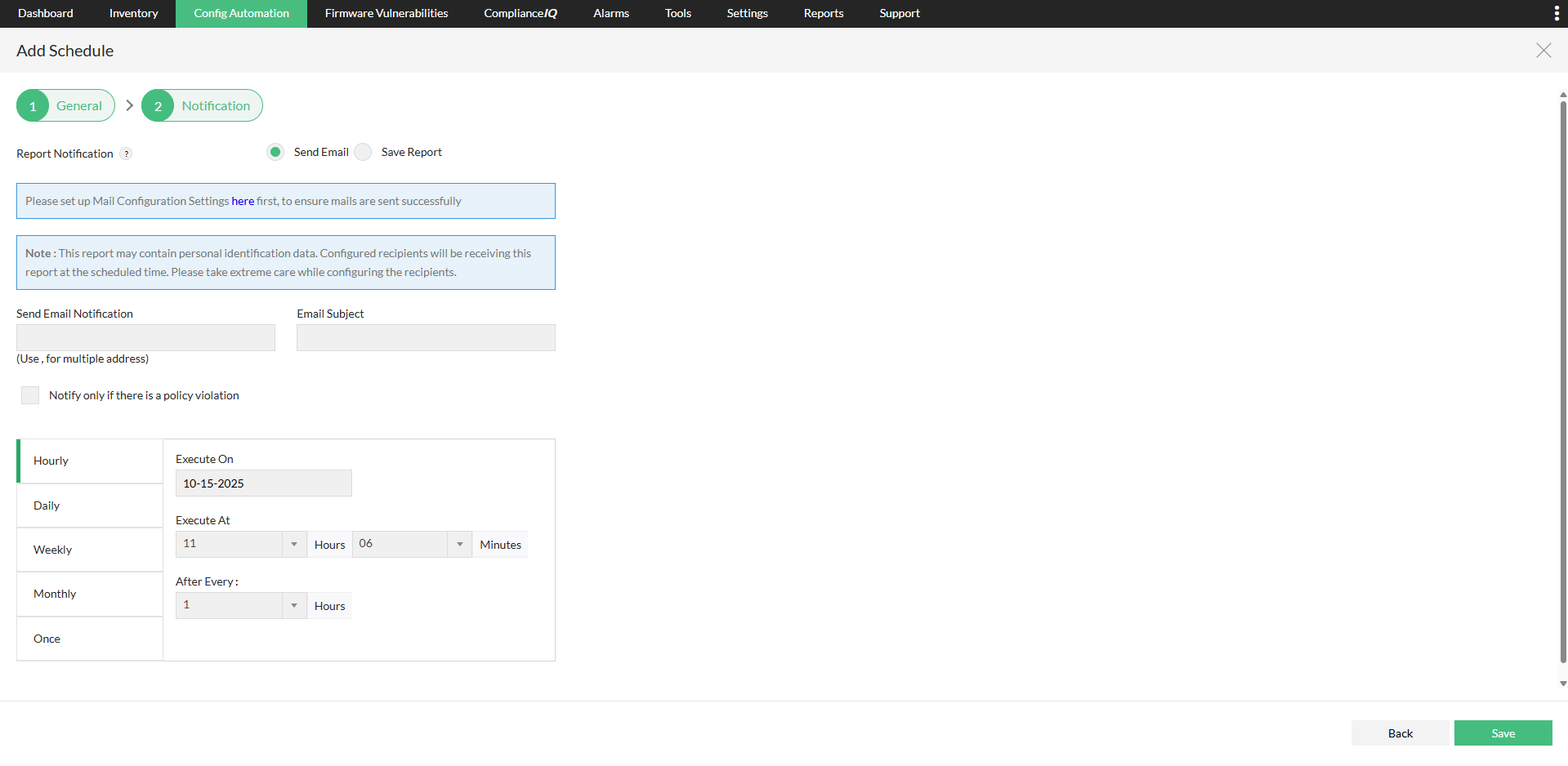
Schedule CIS compliance checks
In expansive network infrastructures, manually ensuring that the CIS compliance check has been performed on all necessary devices is impractical. With Network Configuration Manager, you have the option to use the scheduling feature, allowing you to set a specific date and time for the CIS compliance check. Subsequently, NCM will autonomously execute the checks at the designated date and time, eliminating the need for human intervention. You will receive a status report upon completion of the scheduled operation. This streamlined process ensures that all essential devices are routinely audited for compliance.
Remediate CIS non-compliance issues using Configlets
In certain instances where modifications are made to a device's configuration, the CIS benchmarks may no longer align with the device configurations, resulting in a non-compliance error. This discrepancy needs immediate rectification because, if overlooked, it can lead to security vulnerabilities and substantial fines. Network Configuration Manager offers a comprehensive solution by automating the remediation process. With Configlets, which are automated script templates, you can create a remediation template for each benchmark. In the event of a rule violation, you can swiftly execute and resolve it with a simple click of a button.
Obtain real-time, dedicated compliance reports on CIS
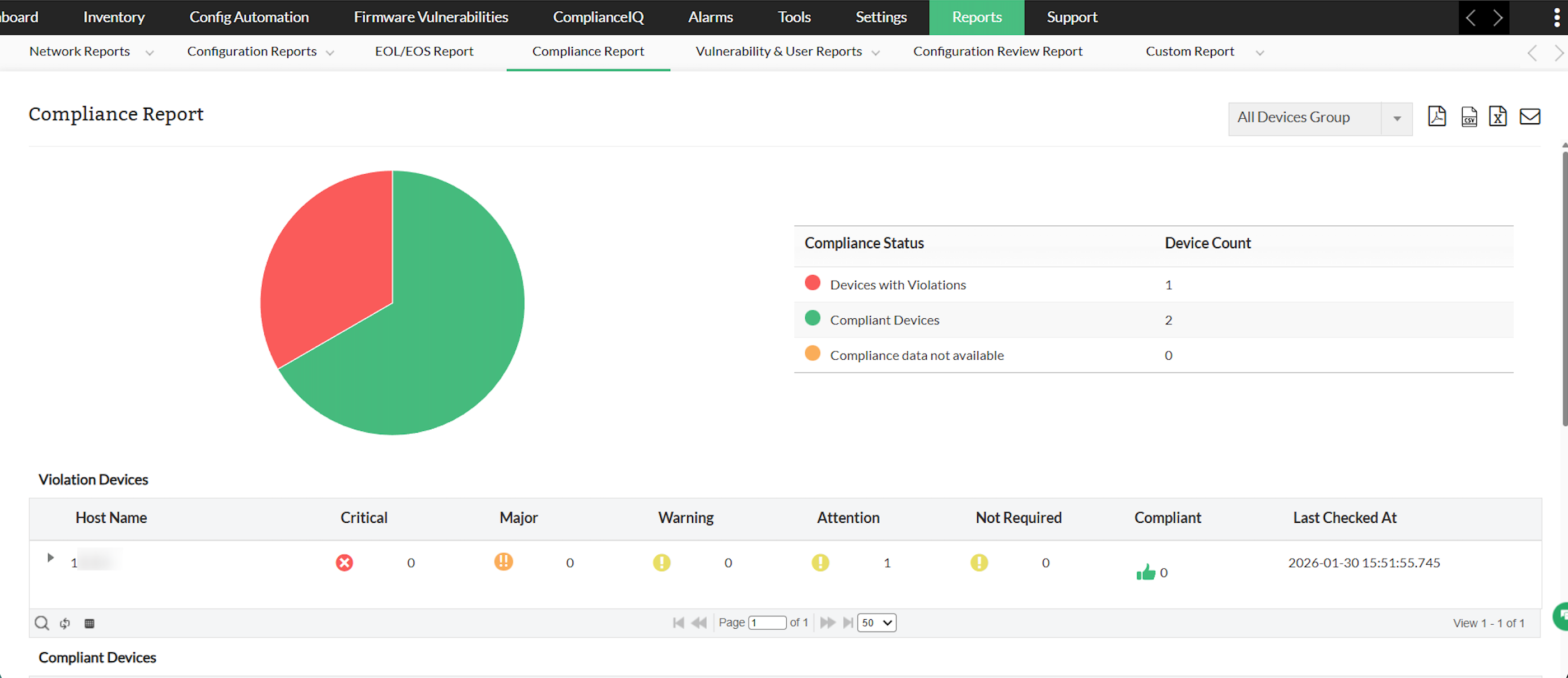
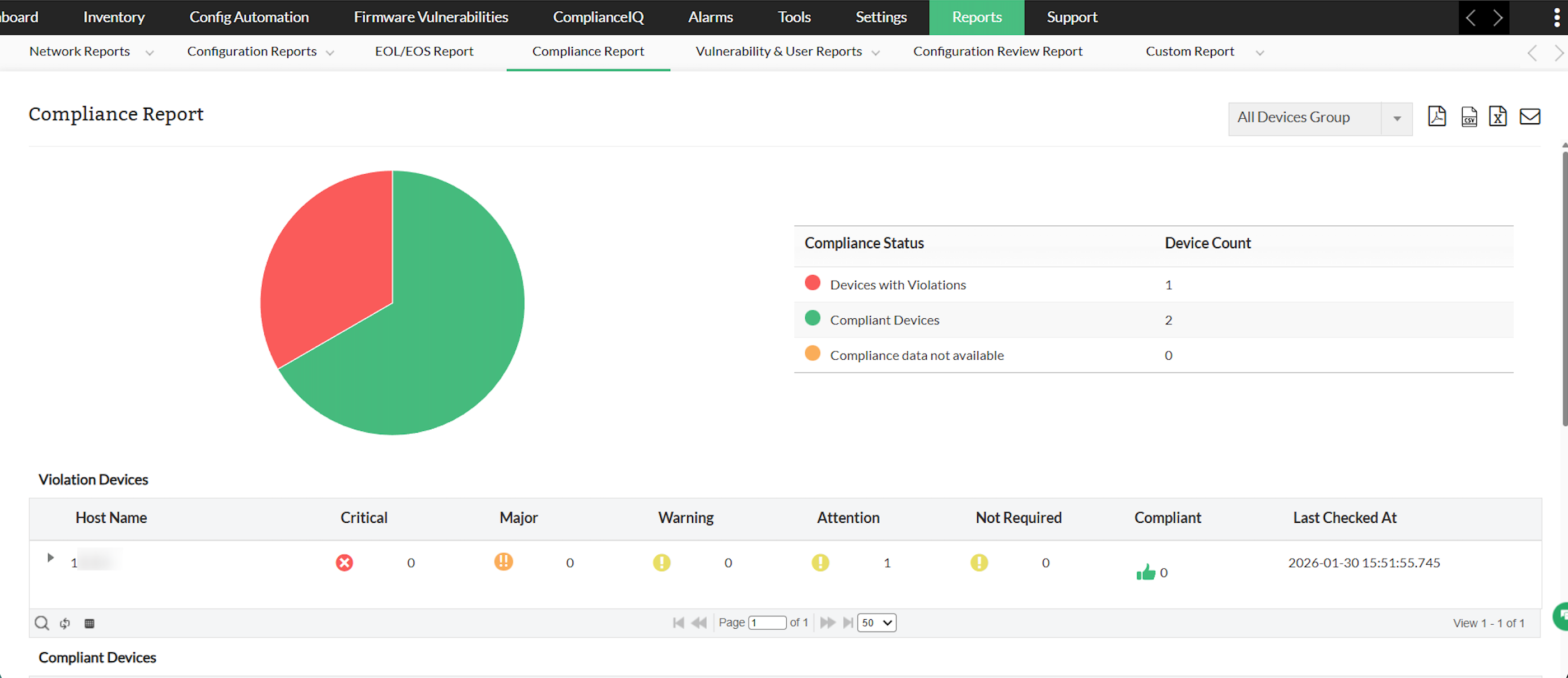
Reports play a pivotal role in any operation, as they offer a comprehensive overview of the entire process. Network Configuration Manager provides a dedicated compliance report that allows you to monitor the real-time compliance status of devices.
Key information included in this report: the device's host name, severity levels (such as critical, major, and warning), the count of compliant devices, and the timestamp of the last check. For a more detailed analysis, you can explore individual devices to pinpoint specific policy violations, along with severity levels, the amount of compliant devices, and the timestamp of the last check.
Clicking on a particular device directs you to a detailed page where you can identify which rules of the policy are violated and which ones remain compliant. This detailed view empowers you to implement remediation for the violated rules and address non-compliance issues effectively.
This flexibility extends to exporting this report in both PDF and CSV formats or sending it via email if required. Additionally, if you have organized device groups, you can tailor the report to focus on a specific group of devices.
Ready to verify your devices against CIS Benchmarks and secure your network effortlessly? Start your 30-day free trial of Network Configuration Manager to run automated compliance checks and fix misconfigurations fast, or fill out the form to get a personalized demo from an expert and see how it works in your environment.
FAQs about CIS Benchmarks & compliance
What does CIS Standards stand for?
+
CIS stands for the Center for Internet Security. CIS Standards refer to a set of security guidelines and best practices developed by this nonprofit organization. These standards offer detailed configuration recommendations and benchmarks to secure your enterprise network.
What is the purpose of CIS Benchmarks?
+
The purpose of CIS Benchmarks is to provide industry-recognized guidelines for secure system configuration. These benchmarks assist organizations in enhancing their security posture, mitigating risks, and ensuring compliance with industry standards and regulatory requirements.
What are the CIS Benchmarks?
+
CIS Benchmarks encompass standards and best practices for configuring the security settings of various applications, operating systems, servers, and databases. This unique consensus-based process involves communities of cybersecurity professionals and subject matter experts worldwide.
Who will benefit from CIS compliance?
+
Organizations across all industries can benefit from CIS compliance, as CIS Benchmarks are globally recognized and developed by experts from diverse sectors, including government, business, industry, and academia.
How are the CIS Benchmarks developed?
+
The community-driven approach is fundamental to the development of CIS Benchmarks. Each recommendation in the benchmarks is established through a consensus reached by a global community of experts from various roles and sectors, such as threat responders, technologists, IT operators, vulnerability finders, and more.
What are CIS Benchmark profiles?
+
Each recommendation in a CIS Benchmark is assigned a profile, indicating the security level of the recommended configuration.
- Profile Level 1 signifies a minimum configuration recommendation, generally considered safe for most systems with minimal performance impact.
- Profile Level 2, categorized as defense-in-depth, includes configuration recommendations for highly secure environments, requiring more coordination and planning for implementation with minimal business disruption. Policies with Level 2 profiles contain both Level 1 and Level 2 configuration recommendations or rules.