Syslog configuration software
A huge network infrastructure containing many devices will have certain important and critical devices in its inventory, such as core routers or firewalls. These devices must always be under constant surveillance regarding any configuration changes.
In such a vast network, keeping track of all of these vital devices manually and triggering backups every time a new change is made is near to impossible. If an admin fails to back up configurations, the network infrastructure could come crashing down in minutes due to unnecessary or unauthorized changes.
To eradicate such issues, you need a syslog configuration management, that is, a syslog configuration software that listens to syslog messages from every device present and makes backups automatically.
Network Configuration Manager has a change detection feature that works with the help of syslog messages.
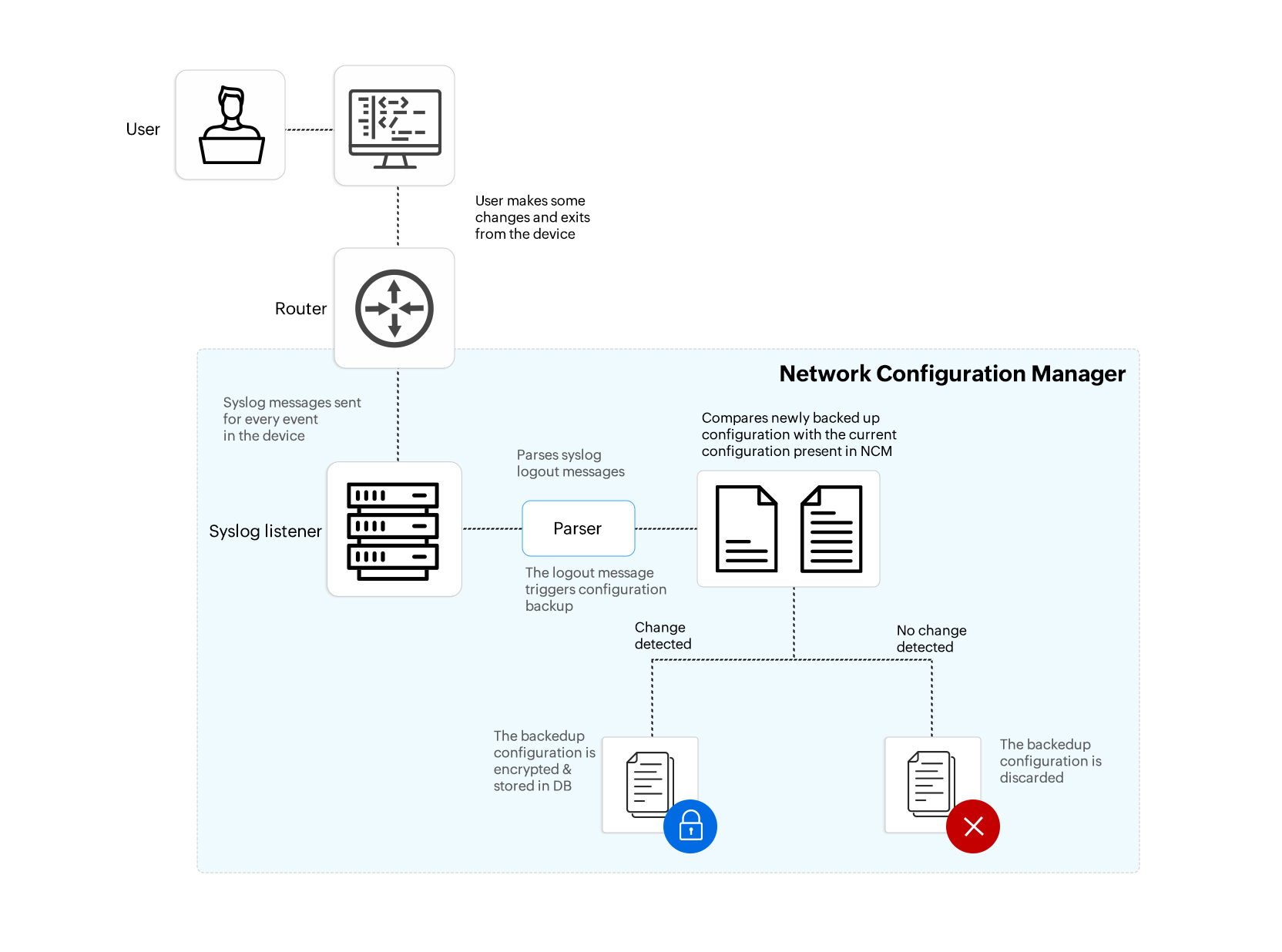
Step-by-step syslog workflow in Network Configuration Manager
- First, the user has to enable change detection in the required critical devices.
- Then, whenever an admin or any user logs in to a critical network device, makes some changes to configurations, and logs off from the device, the device creates a syslog message.
- Network Configuration Manager has a built-in syslog server that contains the syslog messages received from the device, which looks specifically for a logoff message.
- After Network Configuration Manager receives the logout message, it starts the backup operation because there is a higher probability that the user has made a change to the configuration of the device.
- This backed-up configuration is compared with the latest configuration to check for any new changes.
- If there is a change, then the backed up configuration is stored. If not, then it is discarded.
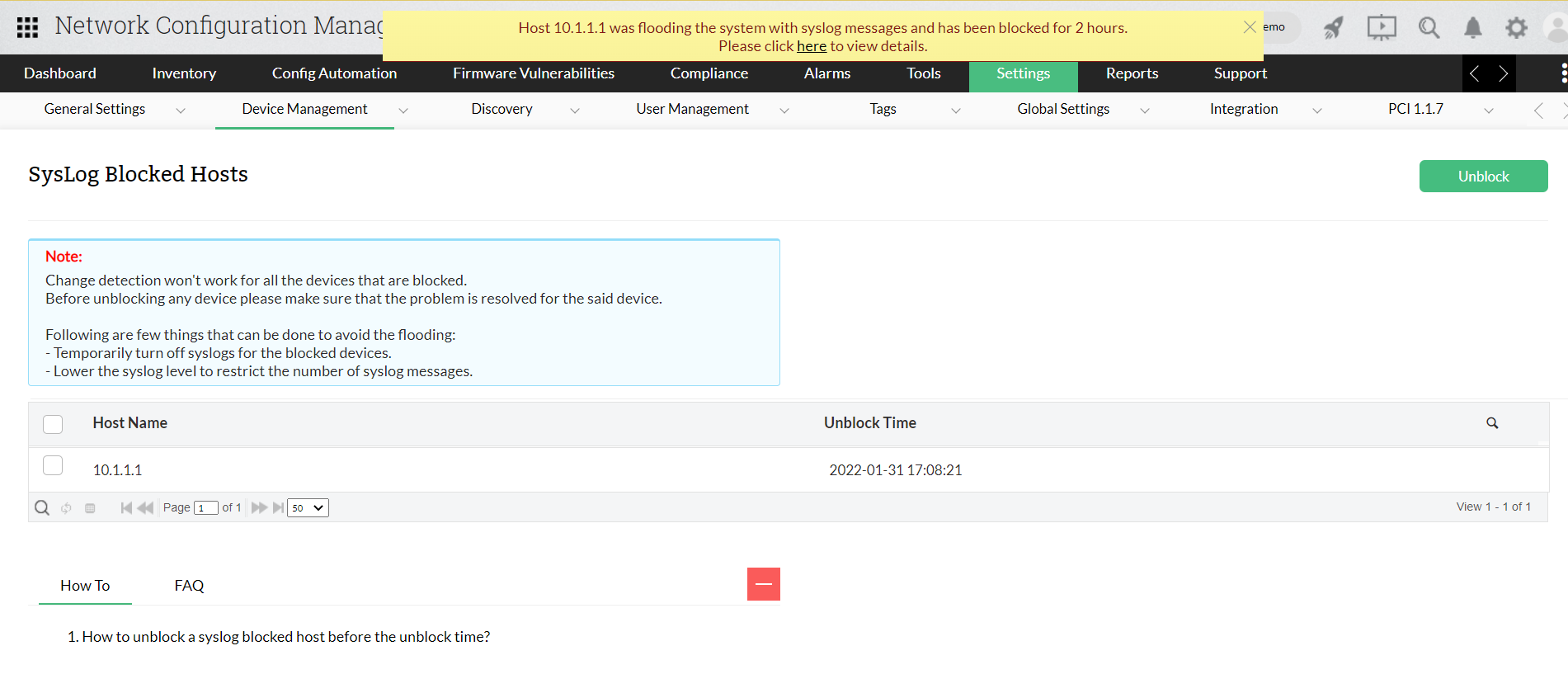
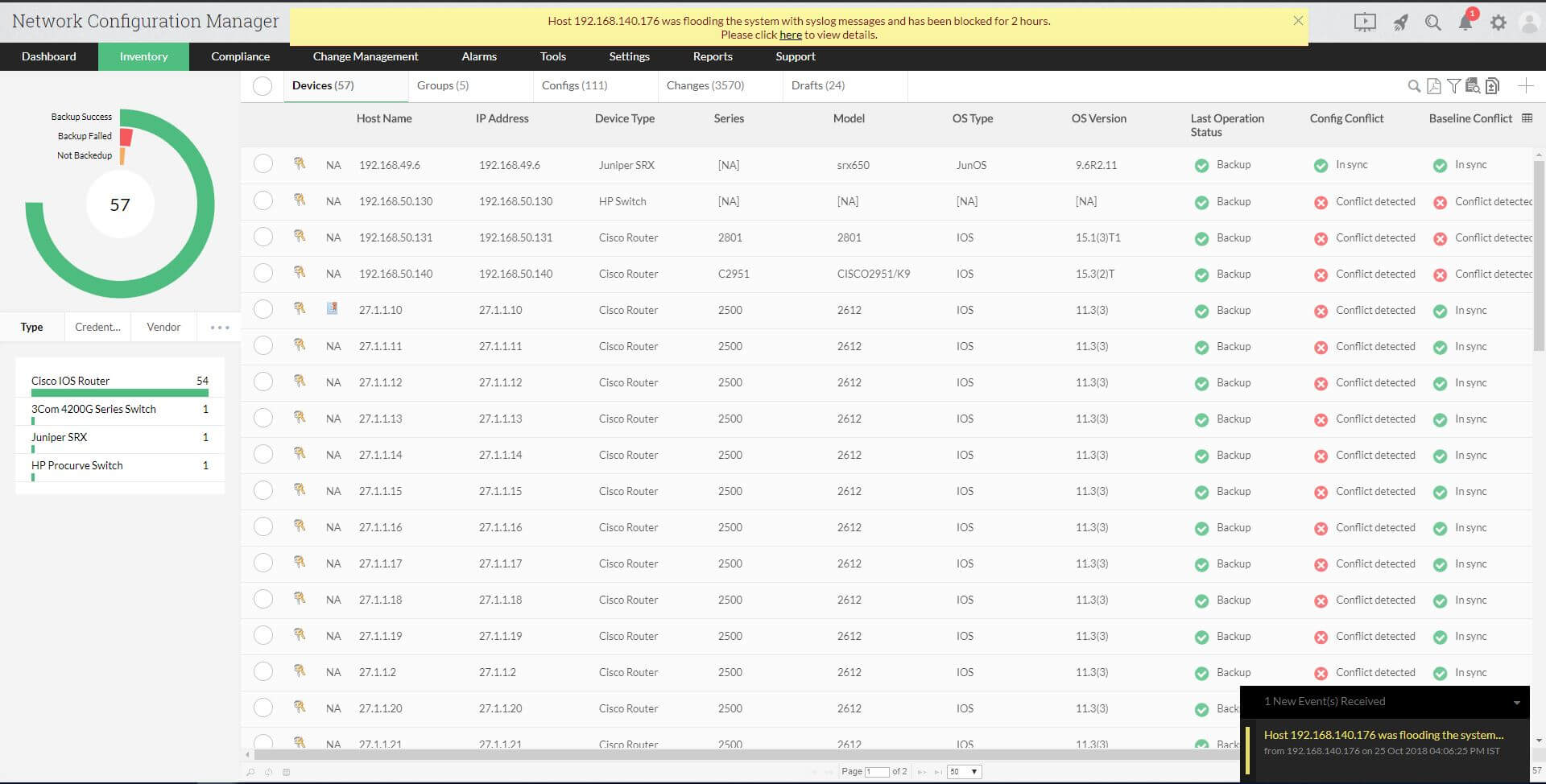
Syslog flooding and how to prevent it
- In a critical network environment, users tend to log in and log off from their devices at regular intervals. This leads to syslog flooding for that device. This will affect the efficiency of syslog configuration software.
- Network Configuration Manager solves this critical flaw by blocking the syslog messages from the flooded device and immediately notifying the user with a pop-up message.
- Syslog-blocked devices can be found in Settings > Device Management > SysLog Blocked Hosts.
- You can unblock syslogs whenever you want if the flooding has receded.
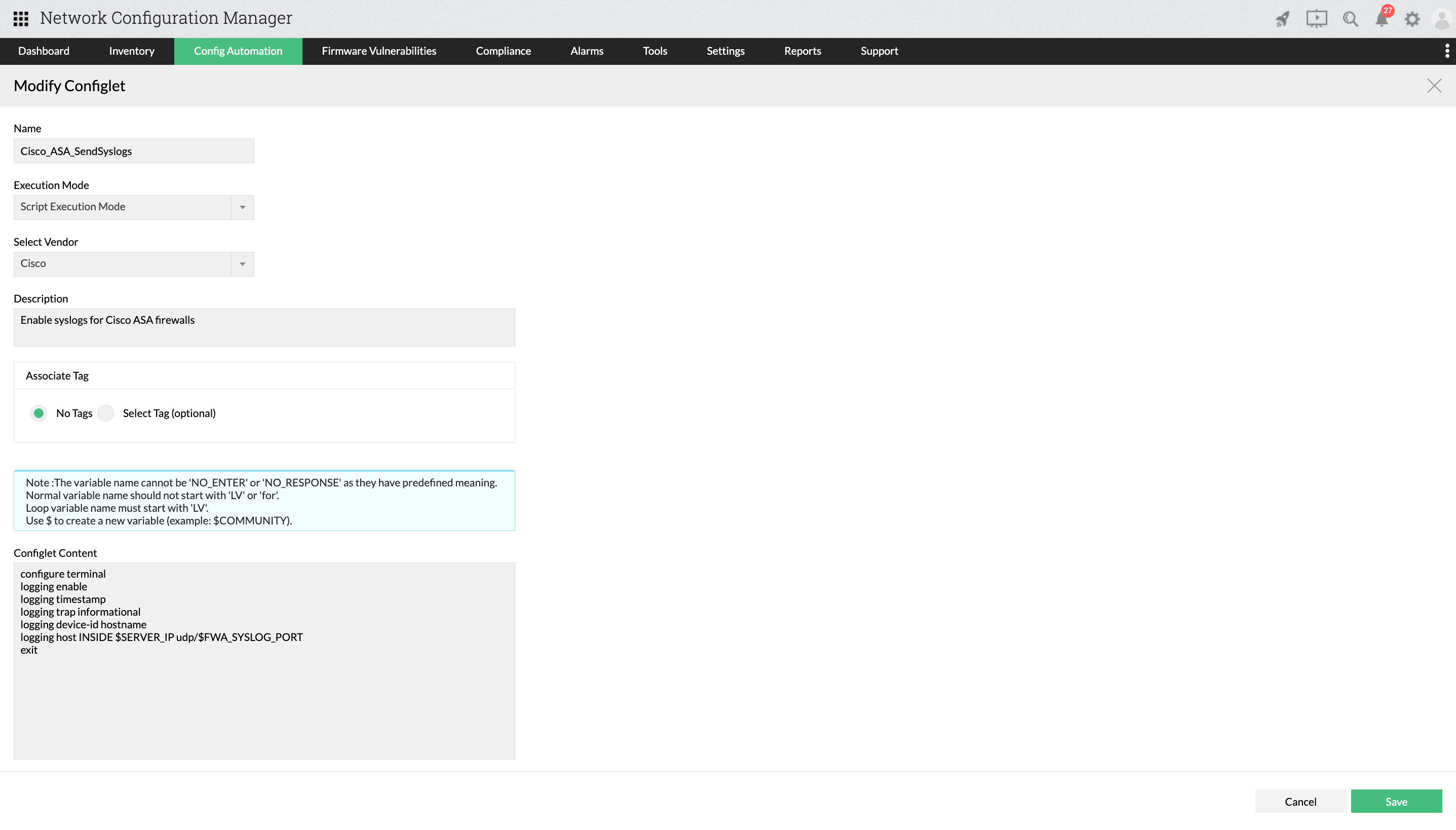
How to enable or disable syslogs in multiple devices
- If you want to enable syslogs for any number of devices of different types, you can use Network Configuration Manager's automation script templates called Configlets. Select the vendor you want, and then provide the Configlet content or the script required to enable or disable syslog.
- You can also use these script templates to forward syslog messages instantly.
- If you require this Configlet to be executed at a chosen date and time, you can schedule it accordingly. Network Configuration Manager also provides real-time reports after the execution of Configlets.
Download Network Configuration Manager now and enjoy 30-day, free trial.
Want a personalized price quote? Click here.
Need a demo conducted by our experts? Try our free online demo.
FAQs for syslog configuration
What is syslog configuration in Network Configuration Manager?
+
Why is syslog configuration software important?
+
How to configure syslog in Network Configuration Manager?
+