Configuring SAML in OpManager
There are two ways to configure SAML in OpManager. You can either do it manually by providing the necessary credentials or you can upload the metadata file directly, if available.
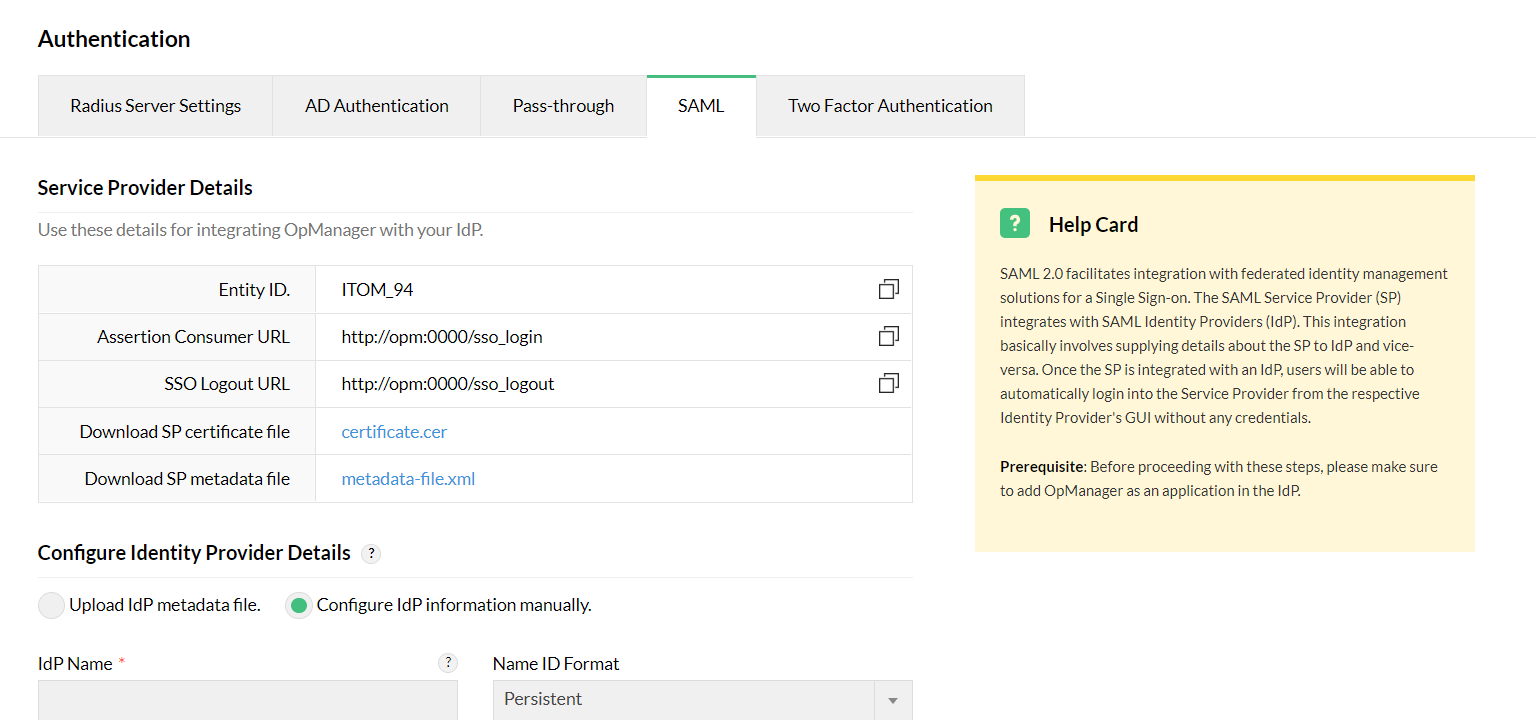
Service provider details
If you opt to configure SAML manually, you will be provided with the following details: the Entity ID, Assertion Consumer URL, SSO Logout URL, and a link to download the SP certificate file. This information, available in the OpManager UI, can be used to add OpManager as a supported application in your IdP.
You can also download the SP metadata file directly from OpManager and import it on the IdP side. This metadata file will have all the above-mentioned details in XML format.
Identity provider details
Similar to the SP details configuration, you can either configure the IdP details manually or upload the metadata file fetched from the IdP side.
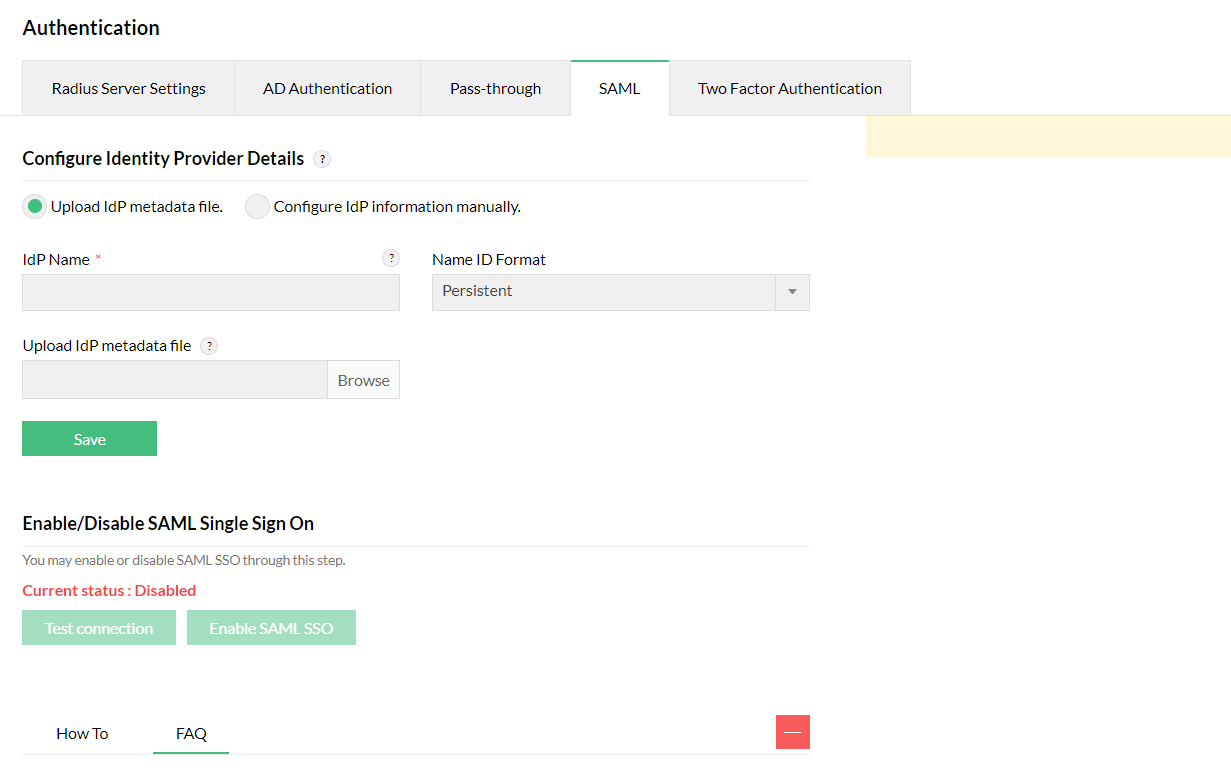
Uploading the IdP metadata file:
If you have a metadata file from your IdP, upload it directly in OpManager.
- Under Settings -> General Settings -> Authentication, navigate to the SAML Authentication tab.
- Under the 'Configure Identity Provider Details' section, choose Upload IdP metadata file and enter the IdP Name.
- Find the metadata file acquired from the IdP and click Upload.
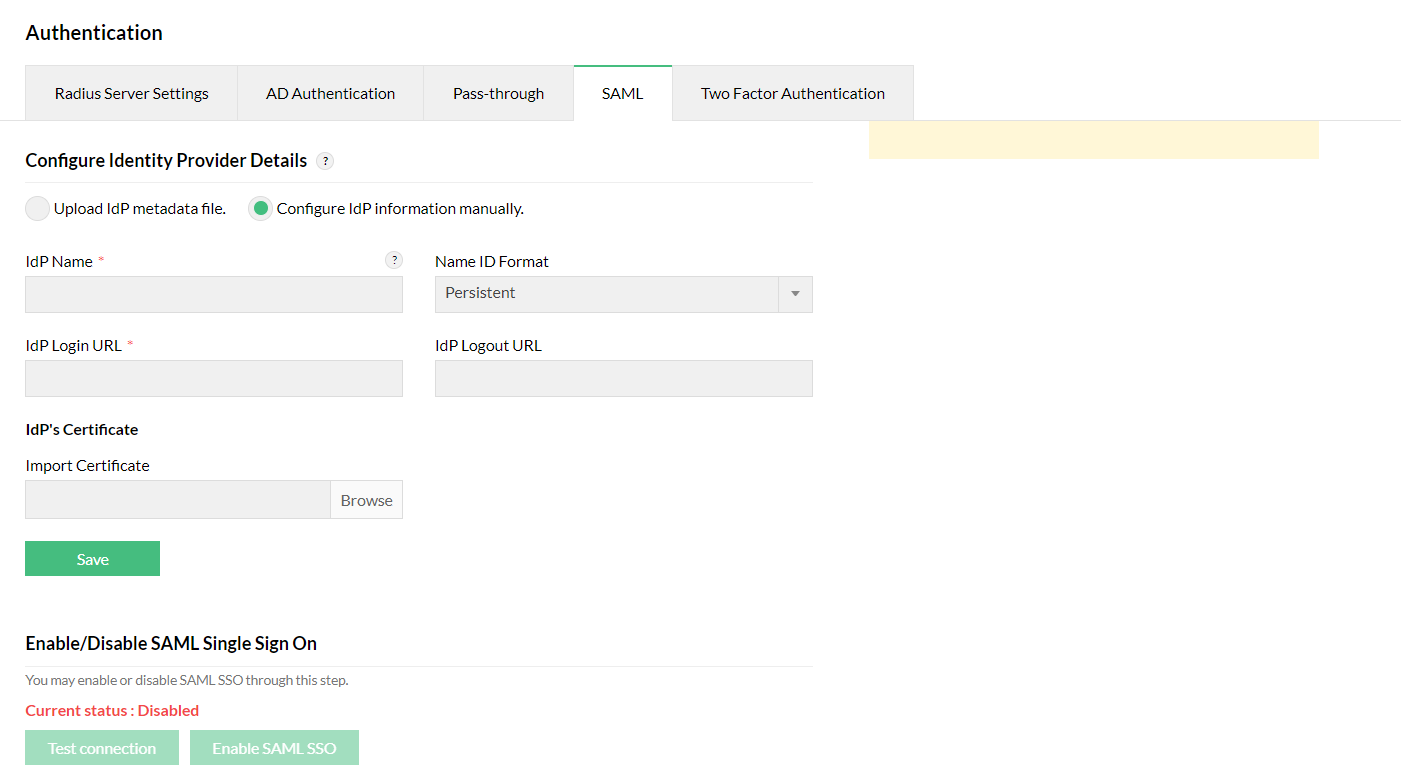
Configuring IdP information manually:
You can also enter the IdP details manually in OpManager. For this, you will need the following details:
- IdP name
- IdP login URL
- IdP logout URL
- IdP certificate
Enter the above details in the 'Configure IdP information manually' section under Settings -> General Settings -> Authentication.
- For the steps to configure SAML between OpManager and Okta,click here.
- For the steps to configure SAML between OpManager and ADFS,click here.
- For the steps to configure SAML between OpManager and Azure,click here.
- For the steps to configure SAML between OpManager and JumpCloud,click here.
- For the steps to configure SAML between OpManager and OneLogin,click here.
Note
- OpManager also offers an option called Single Logout. Similar to SSO, users will be able to log out of OpManager and the configured IdP at once from the OpManager UI by clicking the logout URL provided.
- As of now, Email address, transient and persistent name identifiers can be used for SAML configuration.
- To authenticate AD users of OpManager through SAML authentication, the name ID value from the IdP should be in the format - <domainname>\<username>.
- If more than one user have provided the same Email address while configuring the Email Address Name Identifier, they cannot login using SAML authentication.
- The Username/Email address configured in the IdP should match the same Username/Email address provided in OpManager for successful authentication.
To know more about OpManager's Authentication methods, explore the following help documents.
Frequently asked questions
1. Do we have an option to enable or disable AD and Radius authentication while using SAML?
Yes. Once SAML authentication is enabled, there will be a prompt to disable other authentications and you can disable other login methods, if necessary. Also, you will only be able to login locally via Super Admin.
2. Can we configure more than one IdP?
No, currently only one IdP can be configured at a time.
3. What are the different name ID formats supported in OpManager?
At present, Email address, Transient, and Persistent are the Name ID formats supported for SAML authentication in OpManager.
4. Can we use both SAML authentication and TFA features in OpManager?
In OpManager, you will not be able to use TFA when SAML authentication is enabled. This is because, the entire authentication flow is handled by the IdP when SAML authentication is enabled. TFA can be used only when signing in using Local, AD, or Radius authentication.
5. How do I access the product WebClient if the IdP is not reachable?
If the IdP is not reachable and the other authentication methods are disabled, you can log in locally via Super Admin. If other authentication methods are not disabled, you can login to OpManager by using the default method.
6. How to configure SAML if the certificate is expired?
If the certificate is nearing expiry, OpManager will raise an alert after the user logs in. The Service Provider's certificate can be regenerated from the OpManager UI and uploaded to IdP and vice versa. After uploading, the lifetime of the certificates will be renewed.