Today's security landscape requires organizations to take a proactive approach towards securing their privileged accounts, data, and assets. To reinforce their security perimeters, enterprises are investing in security solutions that leverage AI and machine learning techniques for user behavior analytics (UBA) to spot and suspend malicious activities. UBA tools offer adaptive security controls to identify malicious users and activities, and continuously monitor and mitigate threats in real time.
Privileged UBA (PUBA) is an essential part of any privileged access management (PAM) strategy. PUBA leverages machine learning algorithms to analyze and create baseline user behavior patterns for privileged users and accounts. This helps IT teams quickly detect and suspend unusual behavior, perform root cause analysis using forensic analysis, and take effective remedial actions to minimize the risk of a data breach by drawing meaningful inferences from the event data.
ManageEngine PAM360 leverages PUBA for effective anomaly detection to identify and terminate suspicious users and activities on privileged systems. PAM360's PUBA capabilities are driven by deep learning and machine learning (ML) to monitor and build extensive user behavior patterns, which helps IT teams make informed security decisions based on further security investigations and past experience.
In addition, users can subscribe to receive real-time alerts for logged events, including privileged session activities, password changes, policy updates, and more. The notifications can be sent as emails, SNMP traps, or syslog messages to log management systems for further analysis and correlation.
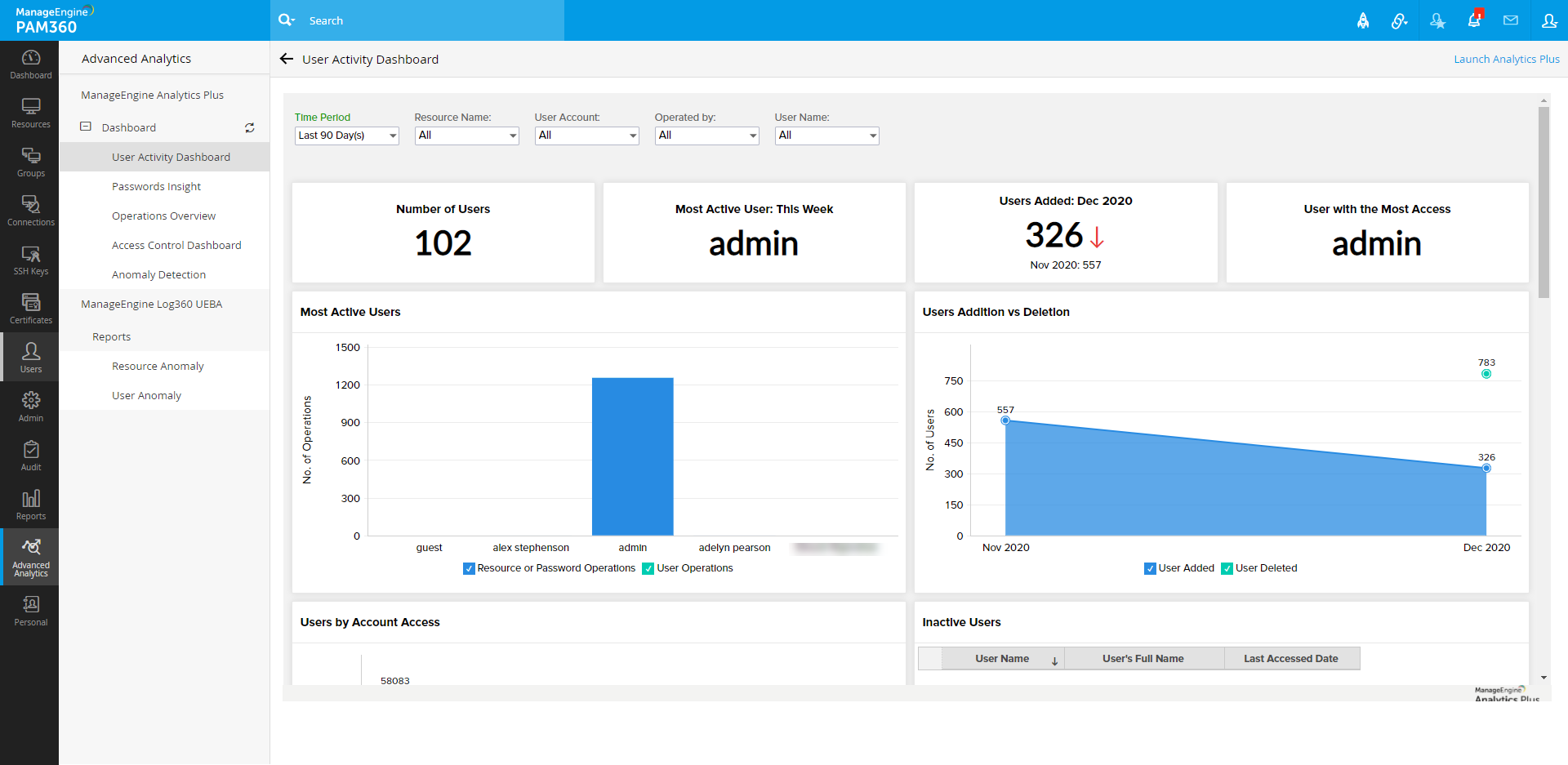
Holistic view of user activities across the privileged system through ManageEngine Analytics Plus
PAM360 integrates with ManageEngine Analytics Plus, an on-premises reporting and business intelligence solution, to provide deep insights on current user activities. Analytics Plus sources event data from PAM360 via API using user login credentials. The key benefits of this integration include continuous and real-time monitoring of privileged systems to track, collect, analyze, and build user behavior patterns. Apart from monitoring, this integration offers detailed reports about privileged users, resources, access levels, and their usage patterns along with a comprehensive history of past operations performed by users.
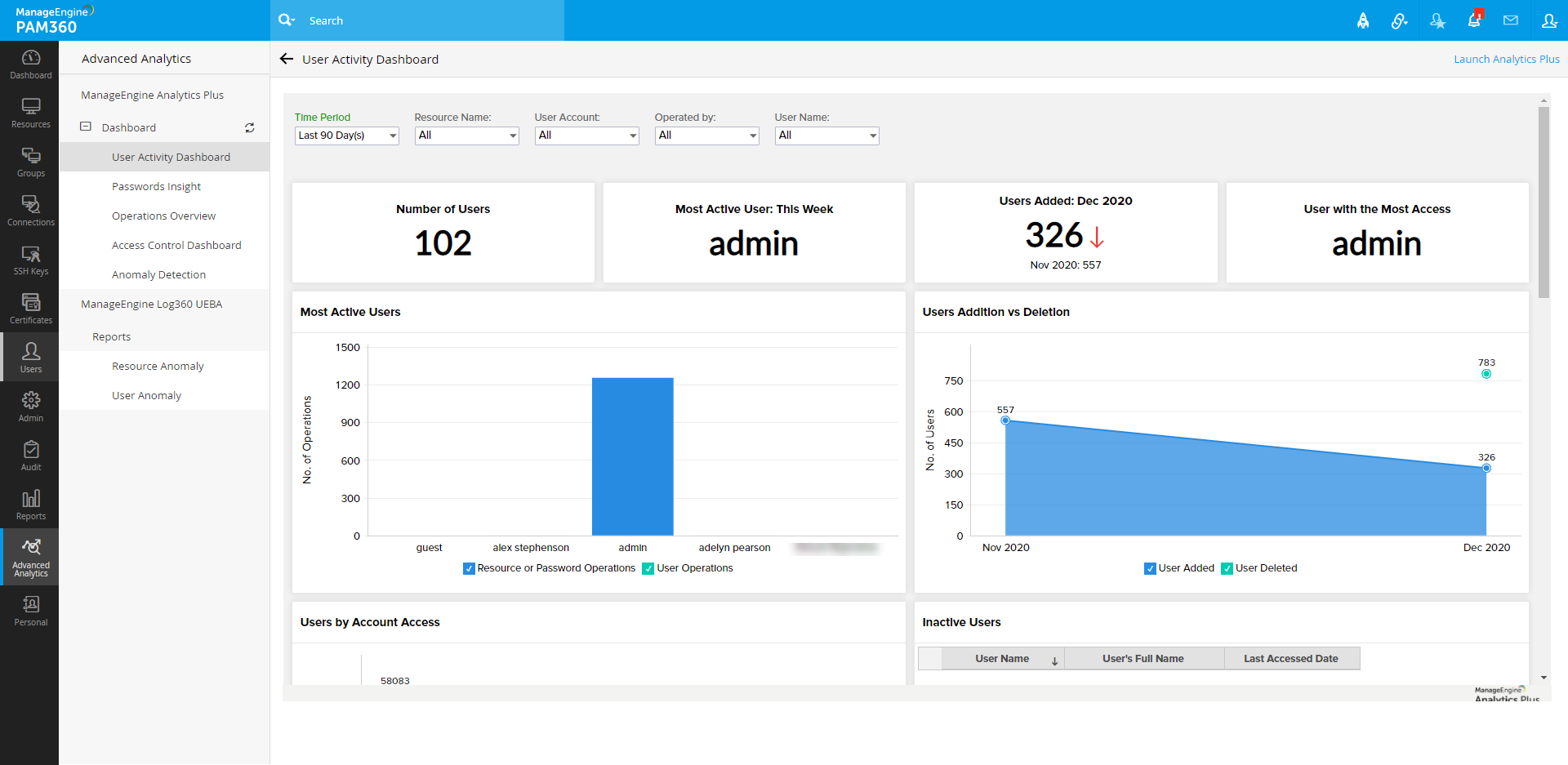
This involves analyzing and correlating user activity with logs collected and stored in log management systems. With this information, security teams can rapidly spot anomalous activities, malicious users, and suspicious traffic sources to preemptively block unauthorized users and gain control over privileged systems. While the borderline anomalous or negligent activities might not necessarily be malicious, security teams can at least stay on top of suspicious activities and carry out further investigations whenever necessary.
PAM360 offers comprehensive and interactive dashboards to delve deep into the who, what, and when of user access patterns across your privileged IT resources, and swiftly identify and isolate actions that deviate from normal behavior. This helps IT teams preemptively terminate suspicious sessions and flag anomalous activities backed by real-time event correlation, which eliminates the overhead of having to sift through huge volumes of logs and historical data.
Advanced SIEM and context-aware event correlation with Log360 UEBA
ManageEngine Log360 UEBA is an ML-based security information and event management (SIEM) solution that leverages user and entity behavior analytics (UEBA) to analyze audit logs and detect abnormal behavior based on risk scores, anomaly trends, and audit reports.
By integrating PAM360 with Log360 UEBA, event data from PAM360 can be sourced by Log360 UEBA via an API using your server details and login credentials. The audit trails from PAM360 are sent to Log360 UEBA at regular intervals, which allows admins to consolidate and visualize the resource and user audit trails, and generate comprehensive reports to enforce informed security controls.
Log360's UEBA integration enables security teams to gain deeper insight into malicious user activities, such as unauthorized logins, password rests, policy violations, and more with a detailed timeline. Further, it offers options to drill into the most minute details around events, systems, users, and so on.
Additionally, audit trails help with forensic investigations, as every activity carries a timestamp, the user's IP address, and a user-given information about said activity. With this information, security teams can compute the severity and risks pertaining to each anomaly, and take quicker remedial actions to minimize the impact of a security incident.