Risk Score
Risk Score is the primary parameter for vulnerability prioritization, designed to cut through the noise of traditional severity-based approaches and highlight what truly matters. Unlike standalone CVSS ratings, which often result in large volumes of “Critical” and “High” vulnerabilities, Risk Score provides a single, opinionated priority number on a scale of 0 to 10, enabling teams to focus on a concise and actionable set of risks.
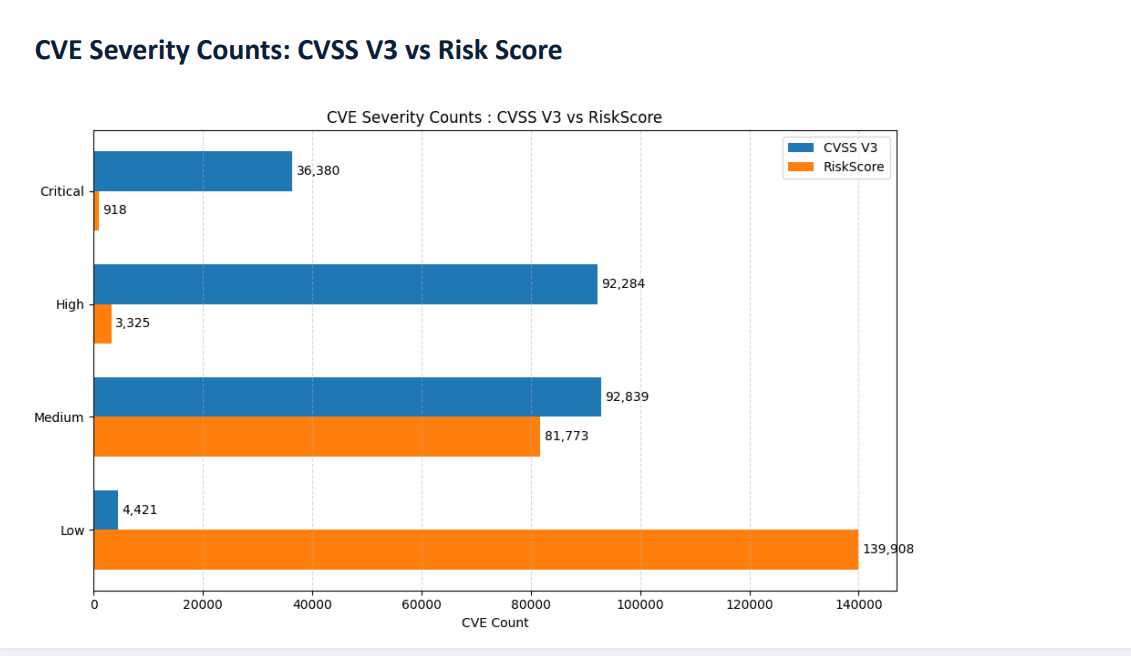
Risk Score reduces CVSS noise by prioritizing truly exploitable and high-impact vulnerabilities.
This AI/ML-driven scoring model evaluates multiple real-world factors that influence the likelihood and impact of exploitation. The model continuously analyzes:
- Exploit availability: Presence of publicly available or weaponized proof-of-concepts.
- Active exploitation: Evidence of known exploited vulnerabilities and in-the-wild attacks.
- Threat actor interest: Mentions in underground forums and ransomware affiliate activity.
- CVSS severity: Base severity score indicating the inherent technical impact.
- Predicted exploit probability: Likelihood of exploitation based on models such as EPSS.
- Vulnerability age: Duration for which the vulnerability has been exposed.
- Remediation availability: Availability of patches or mitigation measures.
- Prevalence: Number of affected endpoints within the environment.
- Exposure duration: Time period the vulnerability remains unaddressed in the environment.
- ML-driven insights: Cross-vulnerability correlations and historical exploit behavior patterns.
By correlating these diverse inputs, Risk Score significantly reduces the overwhelming volume of vulnerabilities typically classified as critical or high. Instead, it isolates the subset that is truly exploitable and high-impact, allowing security teams to act faster and more effectively.
A higher Risk Score indicates a greater likelihood of exploitation and potential business impact, making those vulnerabilities top priorities for remediation. This makes it especially useful for sorting, filtering, and SLA-driven workflows, ensuring that remediation efforts are aligned with actual risk rather than theoretical severity.
In essence, Risk Score transforms vulnerability management from a volume-driven process into a risk-focused strategy, helping teams prioritize with confidence and focus only on what truly matters. To learn how to view, prioritize, and filter vulnerabilities using Risk Score, refer to this page.




