SSH/SSL Notification Settings
Password Manager Pro allows you to enable notifications for various operations such as SSL key expiry, failed SSH key rotation, certificate management, PGP key expiry, etc. In addition, Password Manager Pro allows you to retain or overwrite existing keys. Here in this document you will learn about the following topics:
1. Configuring Notifications
You can set up to get notified via email, syslog messages in case of any of the following cases:
- If SSL certificates are expiring within a specified number of days.
- If domain names are about to expire within a specified number of days.
- If SSH keys are not rotated for more than a specified number of days.
- For certificate management operations performed from within the application.
- If PGP keys are expiring within a specified number of days. Click here to learn more about PGP keys.
Note: Notifications regarding PGP key expiration will be sent via email only.
To configure notifications:
- Navigate to the Admin >> SSH/SSL Config >> Notification Settings.
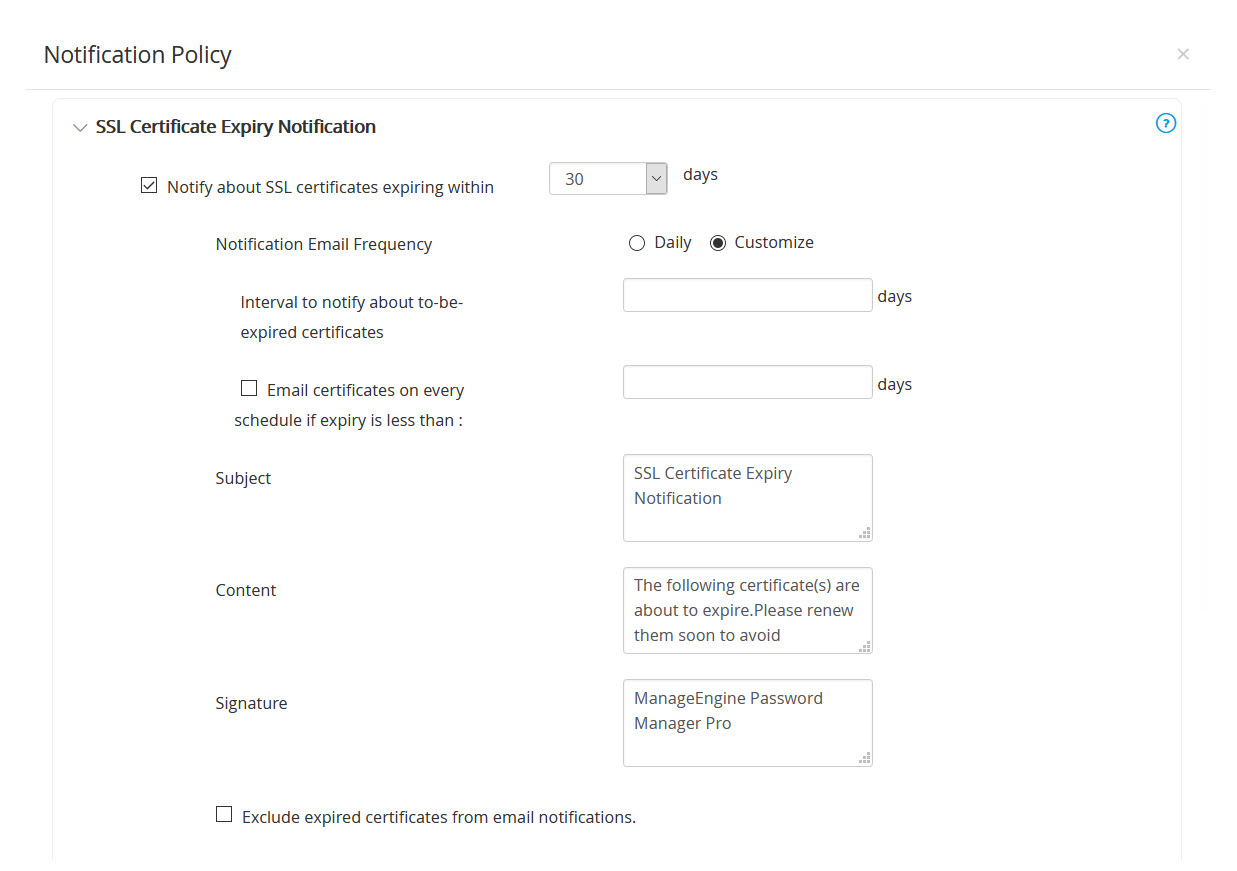
- To enable SSL certificate expiry notifications, select the Notify about SSL certificates expiring within checkbox. Choose a value for days. You will get notified about only those certificates whose expiry dates fall within the period (number of days) you enter.
- Notification Email Frequency: Choose to receive notifications either Daily or Customize your notifications.
- If you choose to Customize, set the Interval (in days) to notify about the to-be-expired certificates.
- Select the Email certificates on every schedule if expiry is less than option if you want to receive notifications on all schedules irrespective of the above-set interval.
- Select Exclude expired certificates from email notifications to not get notified about expired certificates.
- Select Include multiple servers list for certificates to get the details about the list of servers where the certificates are placed/deployed.
- Select Send a separate email per certificate to customize each email. You can mention the Subject and/or Select the attributes to add in the subject of the expiry notification.
- You can also choose to get notifications regarding domain name expiration, PGP key expiration or SSH key rotation failure for the configured time period or both by selecting the respective check-boxes. Expiring SSL certificates, and the SSH keys that were not rotated within the specified days are notified during the mentioned Recurrence Time.
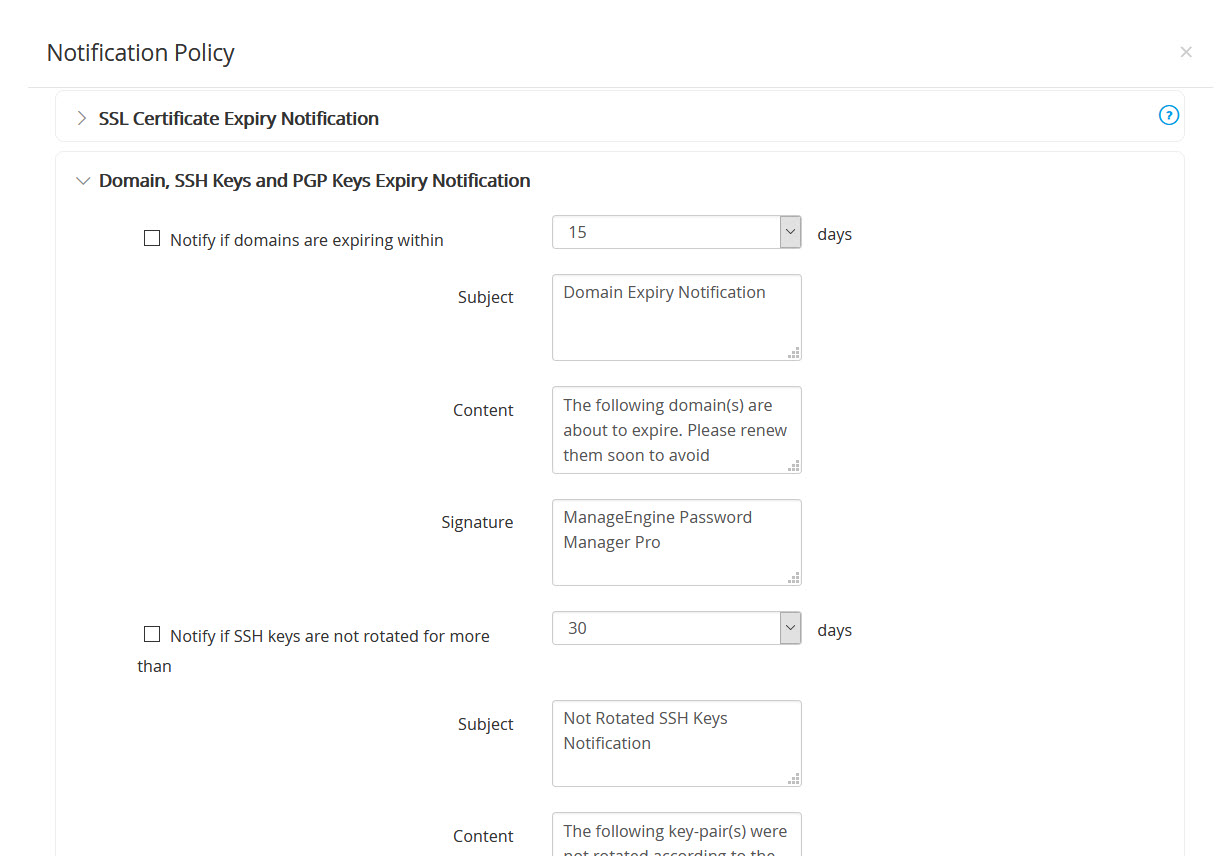
- You are also allowed to edit the Subject, Content and Signature of your email-notifications.
- You can choose to be notified in two ways:
- E-mail – Enter the To address. To enter mail server details, go to the Mail Server Settings tab.
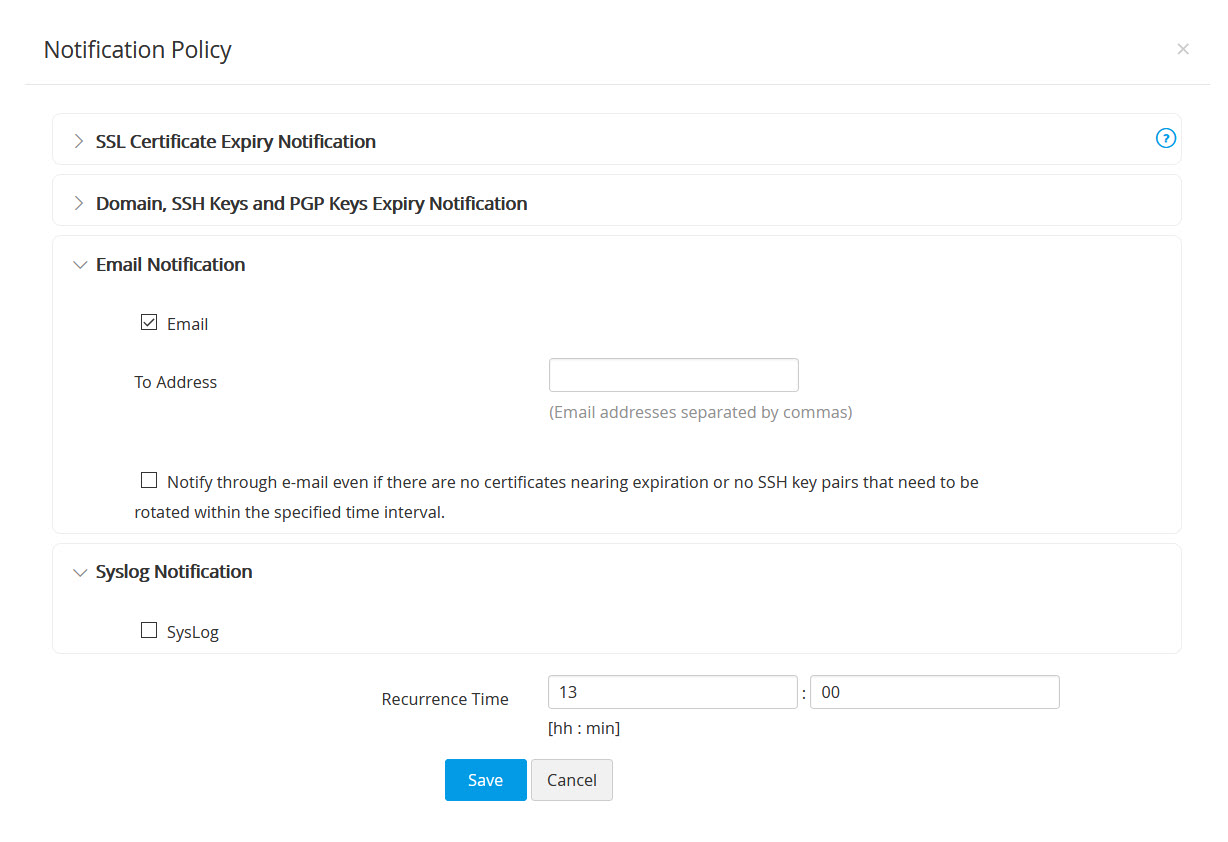
- Syslog – Mention the IP address of the server and the port to which the syslog is to be delivered. To know more about Syslog click here. Refer to the Syslog format given below:
- E-mail – Enter the To address. To enter mail server details, go to the Mail Server Settings tab.
- After filling in the details, click Save.
Note: The number of days specified in the SSH key rotation and SSL certificate expiry notification policy will be applied to the dashboard settings also.
2. SSH Policy Configuration
Password Manager Pro allows you to create a high level policy on SSH keys management. You can specify whether to retain or overwrite the existing keys. That means, when Password Manager Pro creates new keys if they are to be appended to the existing ones or they should be deleted. The second option helps you to remove all existing keys and have a fresh start. Your SSH environment will have only the keys that were generated by the Password Manager Pro. Password Manager Pro carries out these changes in the authorized_keys file directly.
From the SSH Policy, you can set the option for adding keys to the authorized_keys file. You can choose from:
- Append – Allows you to retain existing keys as well the new ones deployed by Password Manager Pro.
- Overwrite – Removes all existing public key information from the authorized keys file and retains the public keys deployed from Password Manager Pro only. This is what we call as clean start.
To change the policy configuration:
- Navigate to the Admin >> SSH/SSL Config >> SSH Policy Configuration.
- Select to either Append or Overwrite the keys.
- Click Save.
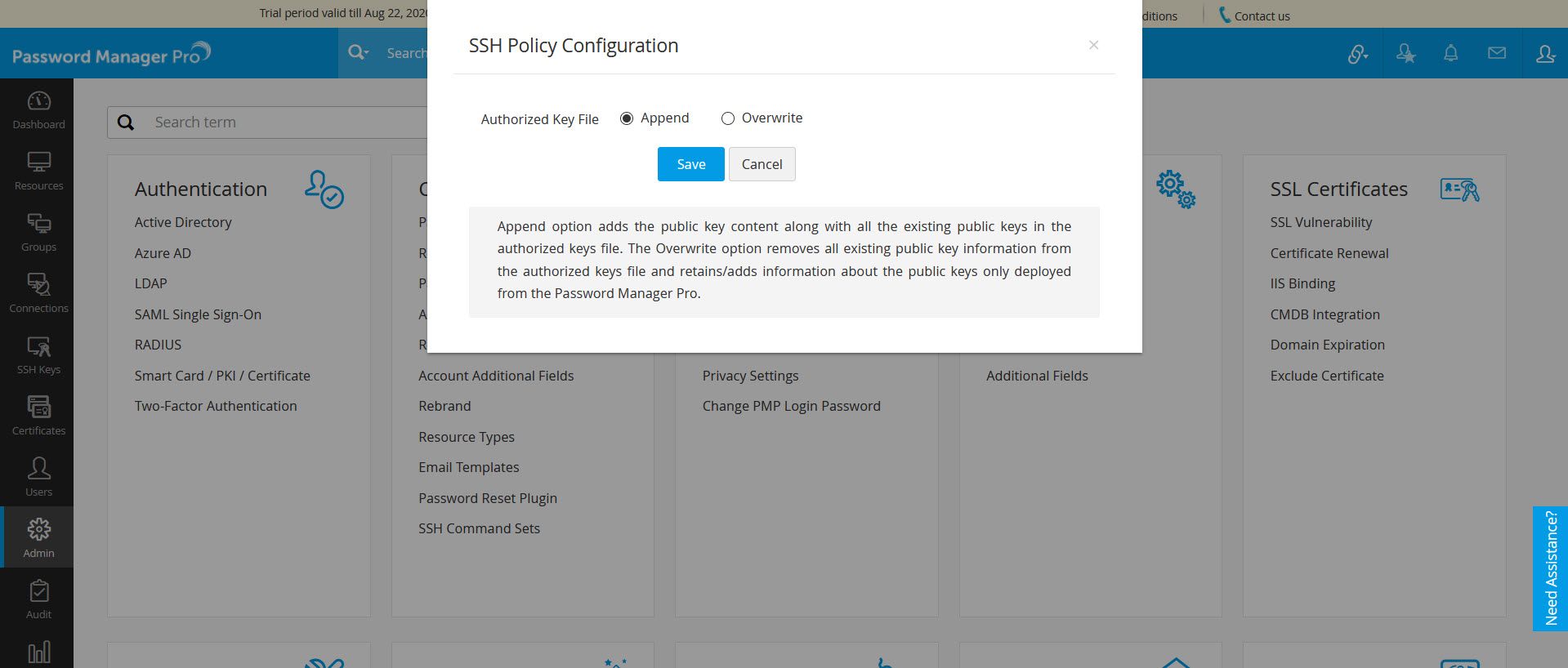
You will get a confirmation that the SSH policy settings have been updated.