Importing Users from Entra ID
Integrate Entra ID with Password Manager Pro and import users and user groups from Entra ID. Through this integration, users can login to Password Manager Pro using their Entra ID credentials, in both Windows and Linux platforms. After integration into Password Manager Pro, the user details and user group structure is maintained exactly as it is in the Entra ID platform.
Following are detailed steps to register Password Manager Pro in the Azure portal and import users into Password Manager Pro:
- Registering Password Manager Pro in Microsoft Azure Portal
- Steps to Import Users from Entra ID
2.1 Importing Users from Entra ID
1. Registering Password Manager Pro in Microsoft Azure Portal
To integrate Password Manager Pro with Entra ID and import users, Password Manager Pro should first be added as a native client application in your Microsoft Azure portal. Follow the steps given below to register Password Manager Pro as an application:
- Log in to the Microsoft Azure portal.
- Click App registrations from the main menu.
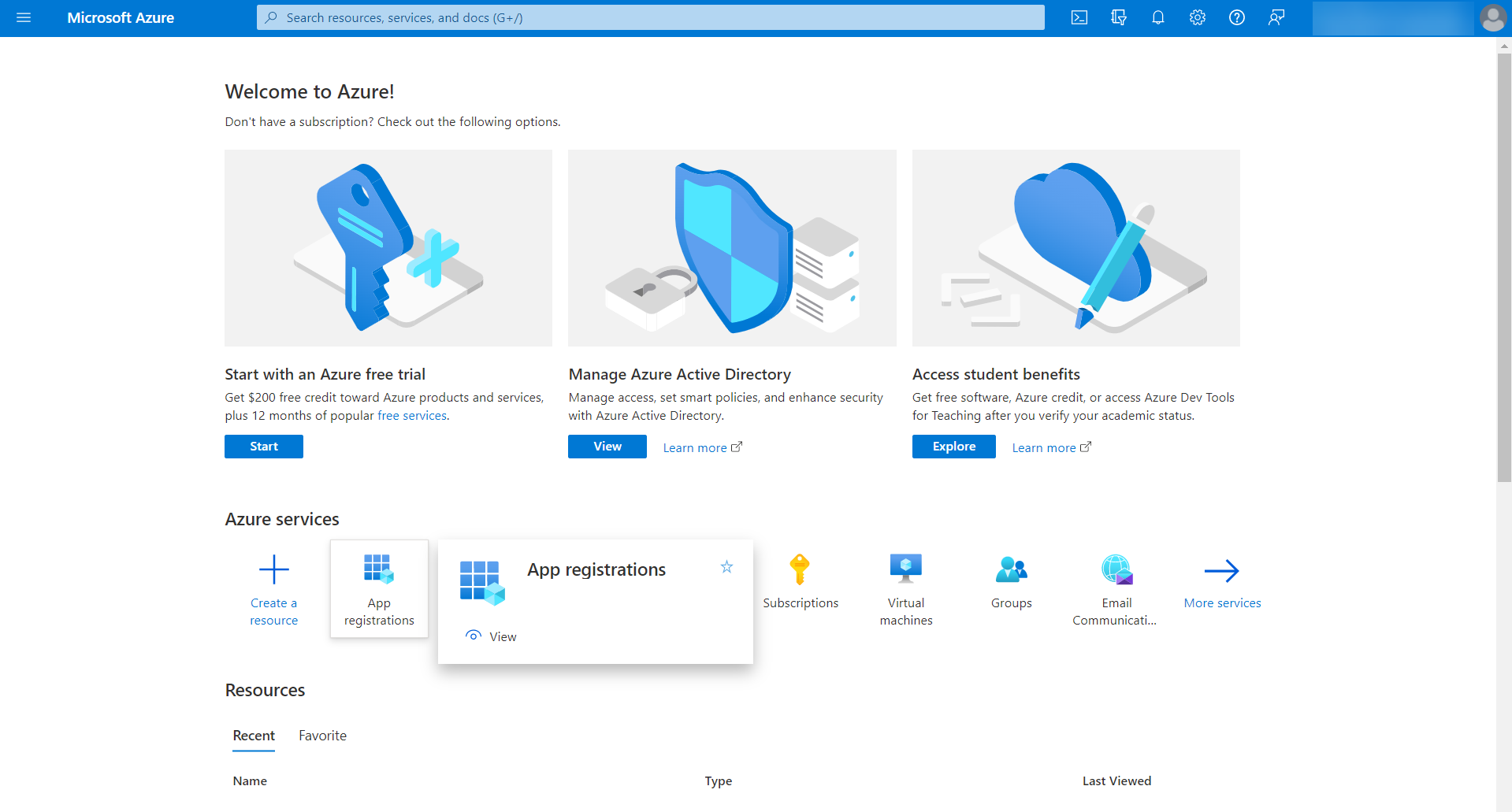
- Click + New registration from the top bar.
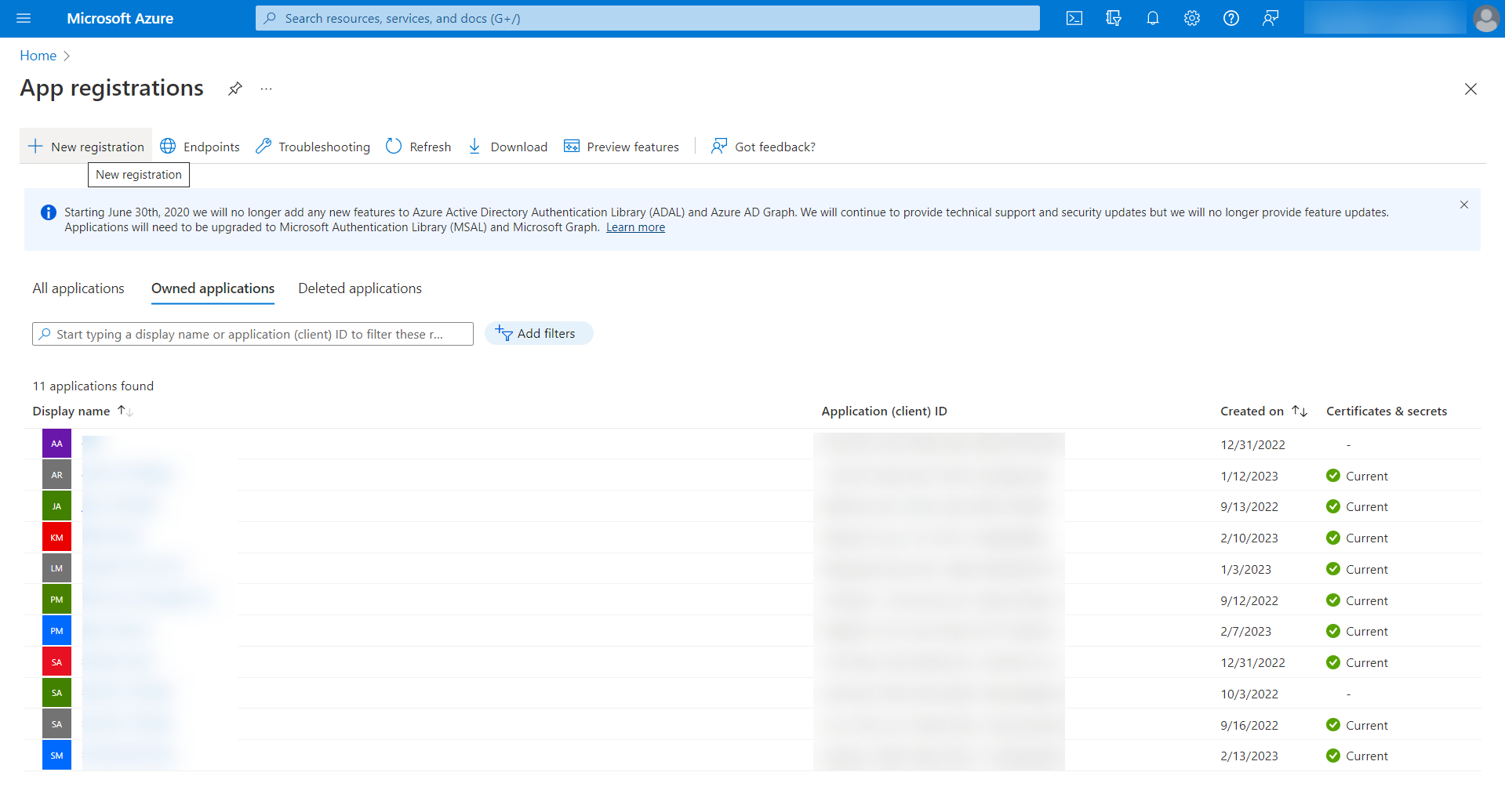
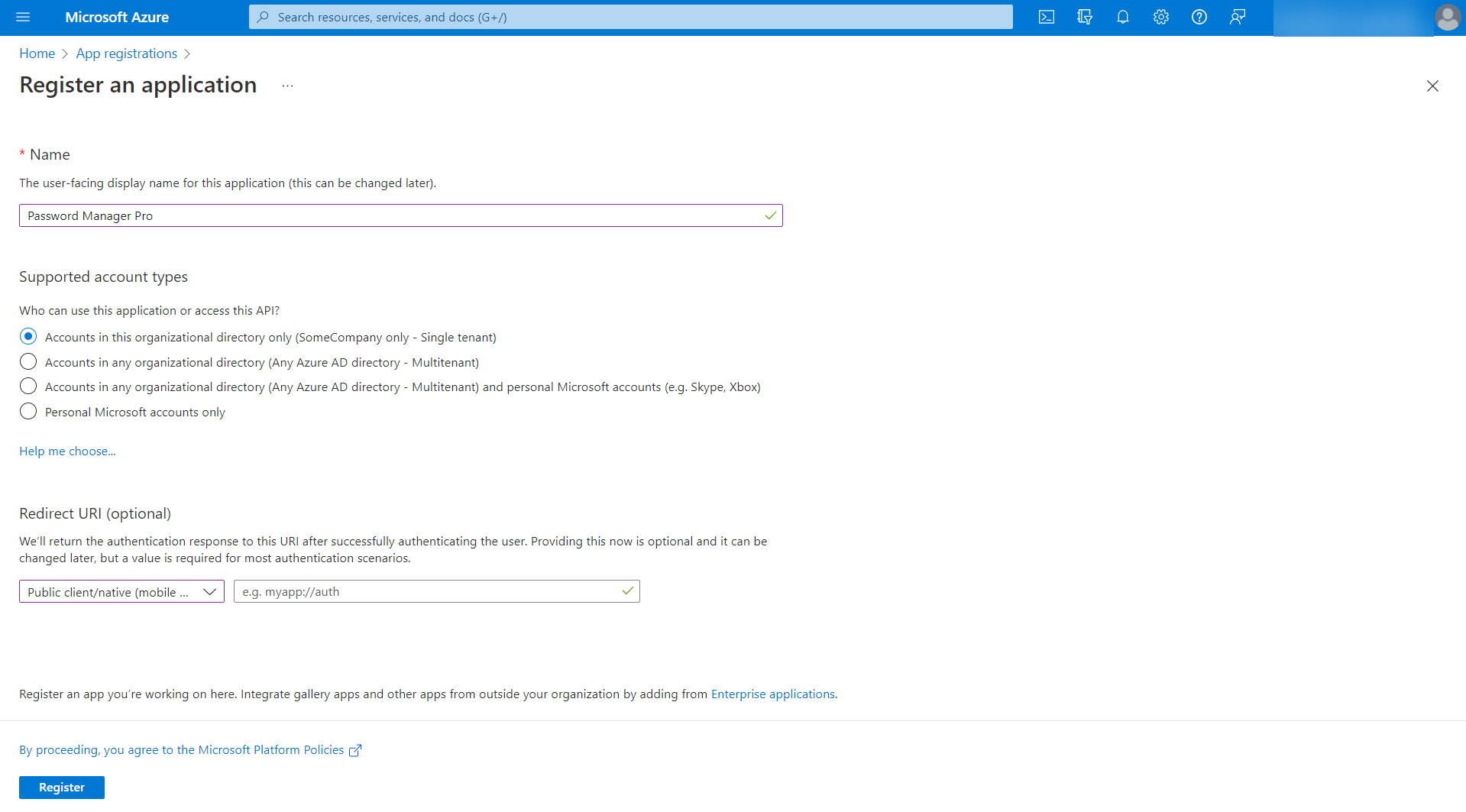
- In the Register an application page, enter the following attributes:
- Enter Name as Password Manager Pro or any name of your choice.
- Choose Supported account types - Accounts in this organizational directory only - Single tenant).
- Select the Redirect URI as Public client/native.
-
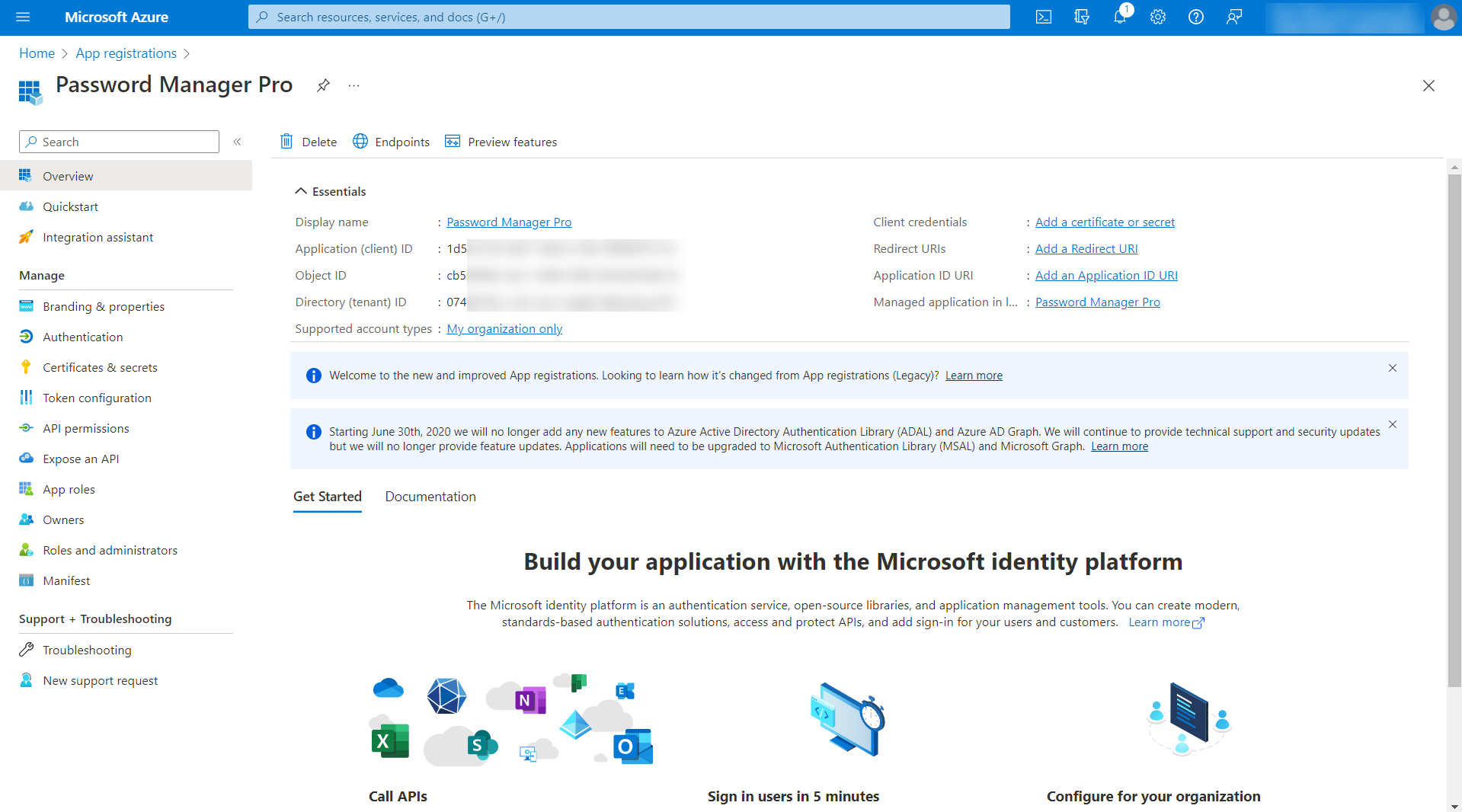
Click Register. Password Manager Pro will be added as an application in the Microsoft Azure portal.
- You will be taken to the page with the details of the newly registered Password Manager Pro application.
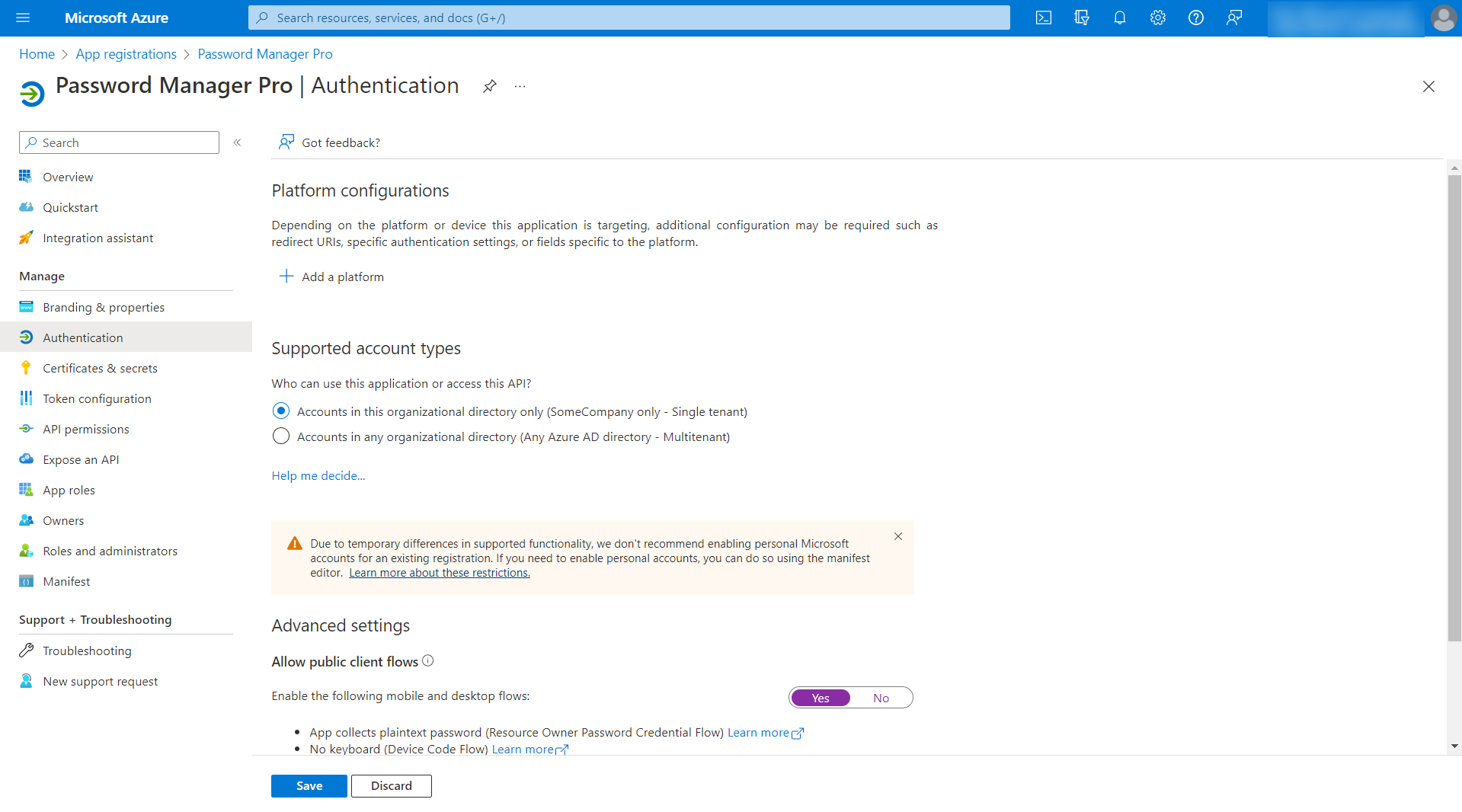
- Click Authentication under Manage in the left pane. In the Authentication page, under Advanced settings, enable Allow public client flows by clicking Yes and click Save.
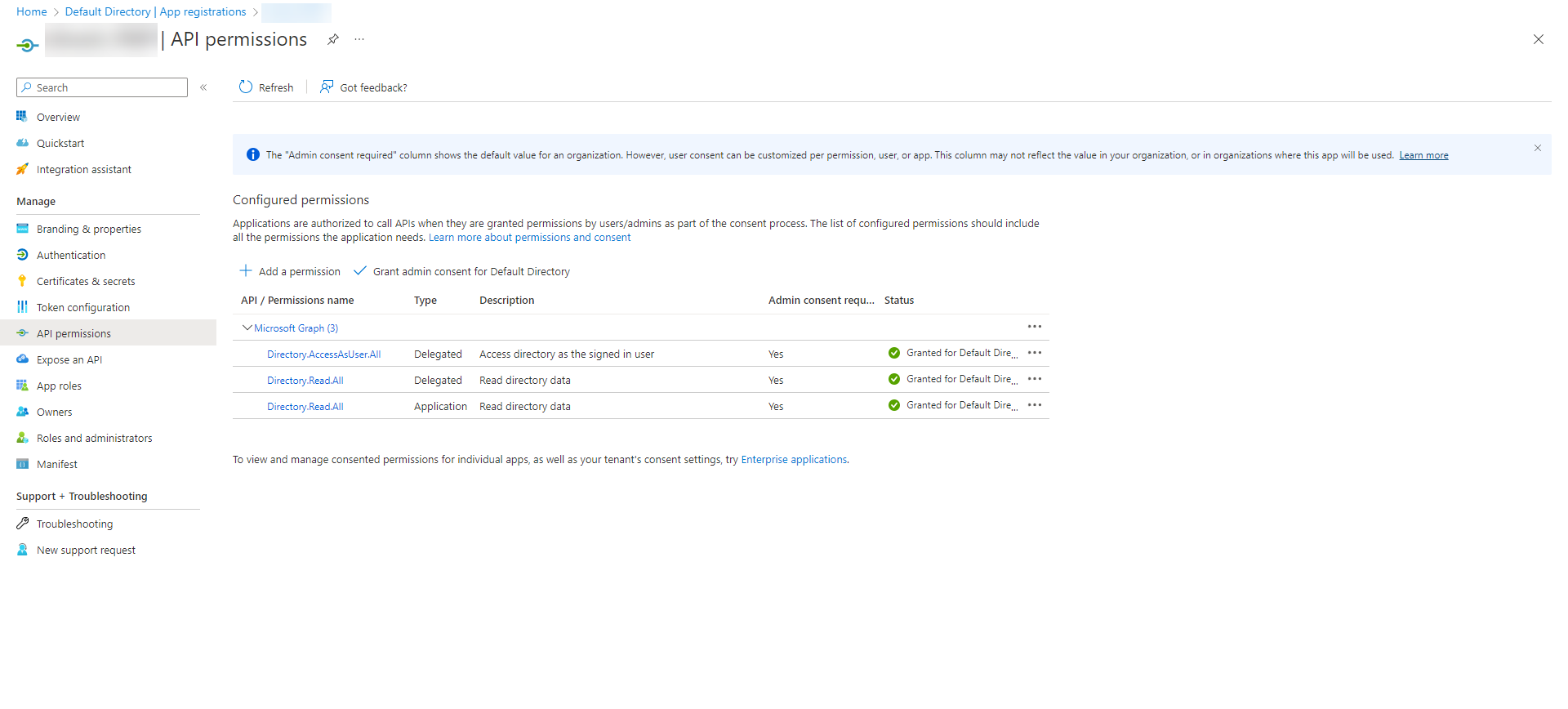
- Click API permissions under Manage in the left pane. In the API Permissions page, click +Add a permission.
- In the Request API Permissions page, choose Microsoft Graph.
- Click Delegated Permissions and search for "read" in the Select Permissions search bar to populate relevant permissions. Select the option Directory.Read.All and click Add Permissions.
- Click Application Permissions and search for "read" in the Select Permissions search bar to populate relevant permissions. Select the options Directory.Read.All and click Add Permissions.
- Click Delegated Permissions and search for "access" in the Select Permissions search bar to populate relevant permissions. Select the options Directory.AccessAsUser.All and click Add Permissions.
- In the Request API Permissions page, choose Microsoft Graph.
- Now, click the Grant admin consent under Configured Permissions.
- In the pop up that opens, click Accept to grant consent for the requested permissions.
Once you have registered Password Manager Pro with appropriate permissions, go to Password Manager Pro's web interface and start importing users using the steps detailed below.
2. Steps to Import Users from Entra ID
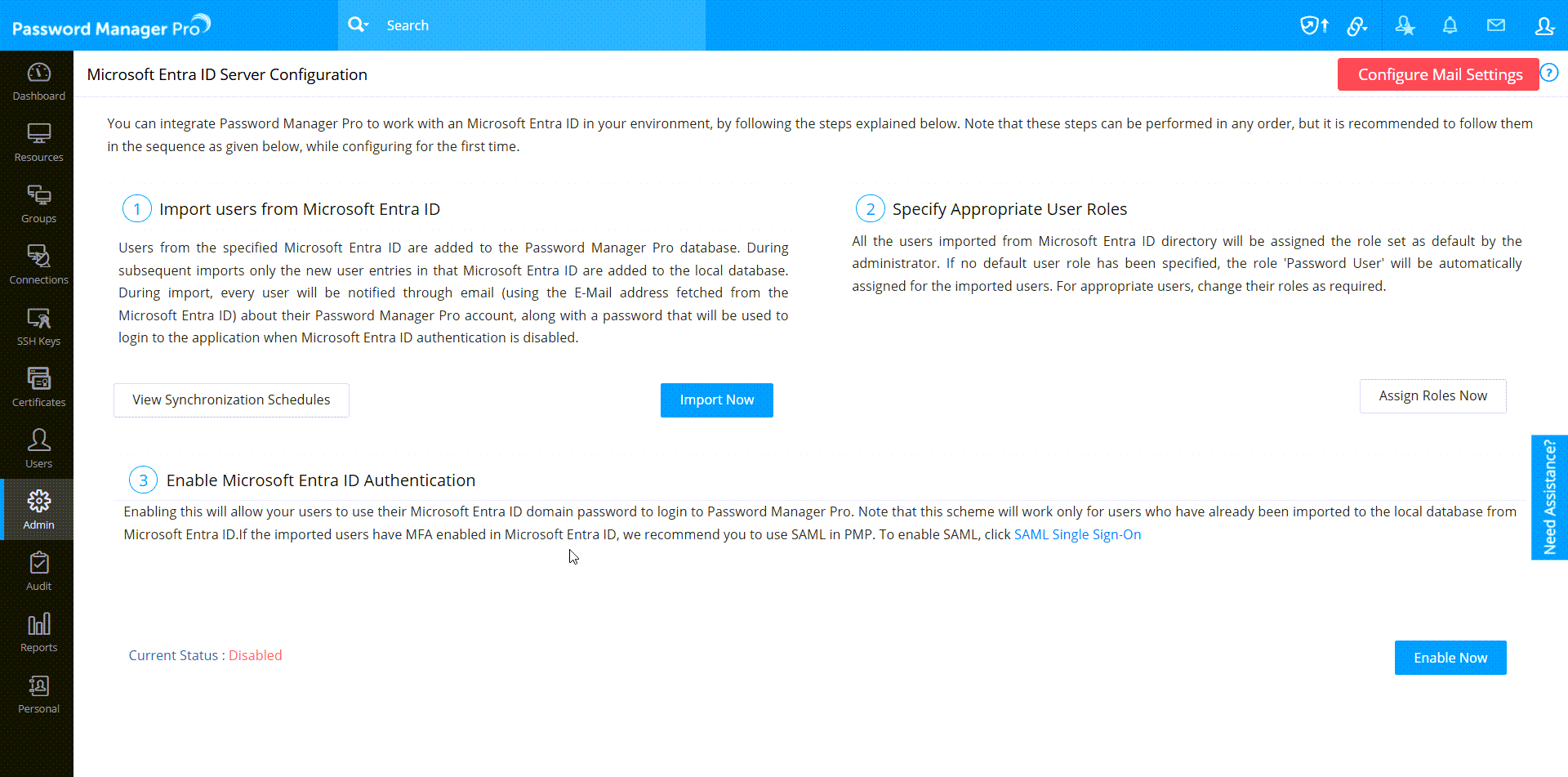
- Log in to Password Manager Pro and navigate to Admin >> Authentication >> Entra ID.
Note: You can also import users by navigating to Admin >> Users >> Add Users >> Import from Entra ID. However, Entra ID Authentication can be enabled only from Admin >> Authentication >> Entra ID.
- The Entra ID Server Configuration page will be displayed, from where you need to perform the below sequence of steps:
2.1 Importing Users from Entra ID
- Navigate to Users >> Add User >> Import From Entra ID.
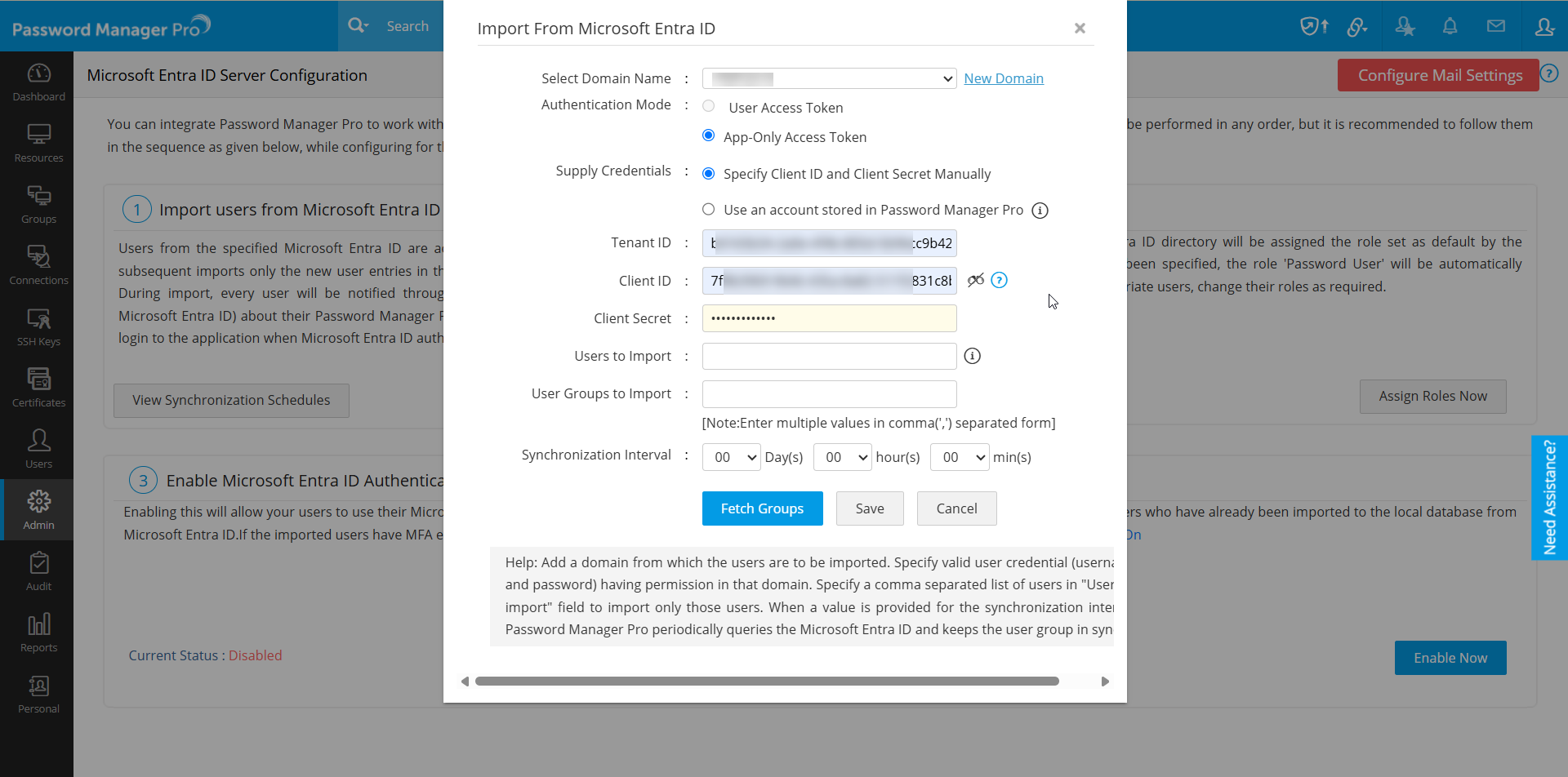
- In the pop-up that opens, perform the following operations:
- Click the New Domain and add the Entra ID domain from which users and groups are to be imported.
- Select the Authentication mode as App-Only Access Token. User Access Token will be no longer applicable from build 12230.
- Select the Supply Credentials as Specify Username and Password Manually. If you have stored the Azure Application of Microsoft Azure as a resource in Password Manager Pro, then select Use an account stored in Password manager Pro.
- If you have selected Specify Username and Password Manually in the supply credentials:
- Enter the Tenant ID and Client Secret.
- Enter the CLIENT ID generated in the Entra ID server while registering Password Manager Pro as a native client application in your Azure portal.
- If you have selected Use an account stored in Password Manager Pro, enter the Resource Name and Account Name stored in the Password Manager Pro.
- To import only particular users and user groups from the Entra ID, enter the required user name(s) in the comma-separated form in the field Users to Import and the required group name(s) in User Groups to Import.
- Add a synchronization schedule to keep the user database constantly in sync with your Entra ID. In the Synchronization Interval field, you can enter the time interval at which Password Manager Pro has to query Entra ID and keep the user database in sync with Entra ID.
- After entering the required details, click Fetch Groups. If you have specified users/user groups to import, then click Import. Password Manager Pro will list all the user groups available in your Entra ID domain. Select required groups using the check boxes beside them and import users.
- Once the import is complete, Import Summary will be displayed with the number of users imported successfully and the ones that failed. Once you click Close, you will be automatically taken to section 2.2: changing appropriate user roles.
Note: To view the synchronization schedules created for Entra ID user import, click View Synchronization Schedules in the Entra ID Server Configuration window.
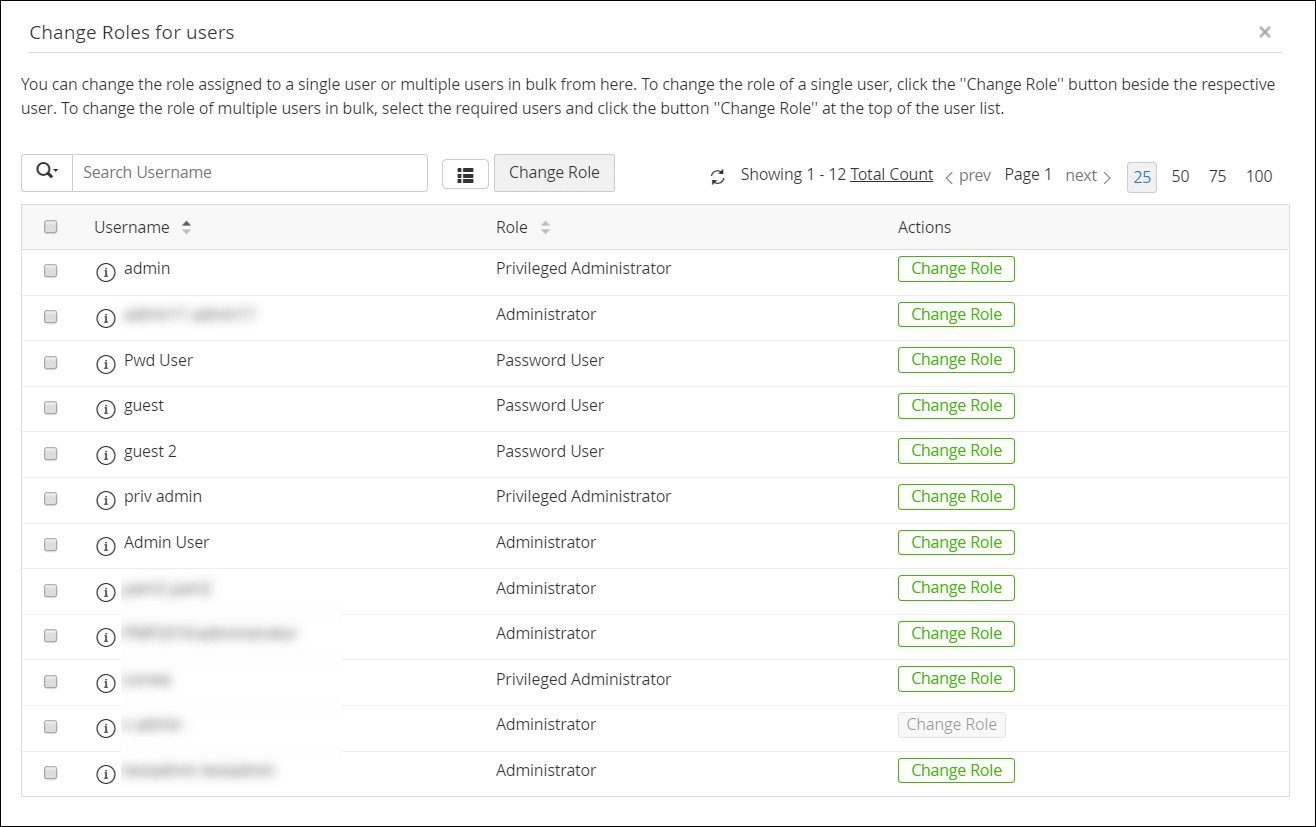
2.2 Specifying Appropriate User Roles
After import, all the users imported from Entra ID will be assigned the Password User role as shown in the Change Roles for users dialog box.
- Click Change Role button against the users for whom you wish to change the role and choose an appropriate role from the drop-down.
- To change roles for users in bulk, select the users using the check boxes and click Change Role at the top and choose an appropriate role from the drop-down. The changes will be saved as and when the roles are assigned.
Notes:
- You can change the assigned roles anytime in the future by clicking Assign Roles Now in the Entra ID Server Configuration page.
- Assign Administrator role to at least one user from the list of users imported from Entra ID as administrator privileges are required to carry out user management and other system operations in Password Manager Pro.
2.3 Enabling Entra ID Authentication
The third step is to enable Entra ID authentication—enabling this will allow your users to login to Password Manager Pro using their Entra ID domain password. Note that this feature will work only for users who have already been imported to the local database from Entra ID. Before enabling Entra ID authentication, ensure that AD authentication is disabled.
- Navigate to Admin >> Authentication >> Entra ID and click Enable Now under Enable Entra ID Authentication as shown in this image.
- Once Entra ID authentication is enabled, you can disable local authentication under Admin >> Settings >> General Settings >> User Management. Click here to learn more about that.
3. Troubleshooting Tips
In Password Manager Pro, Entra ID authentication will not work under two circumstances, which are explained below with possible solutions:
- Users in the Microsoft Azure portal have Conditional Access enabled, which prevents sending of auth token to Password Manager Pro, leading to authentication failure.
Solution: Bypass this by disabling Conditional Access at both app-level and user level in the Microsoft Azure portal before enabling Entra ID authentication in Password Manager Pro. - The Microsoft Azure portal has Multi-Factor Authentication (MFA) enabled.
Solution: Bypass this by disabling MFA in the Microsoft Azure portal.
In the place of Conditional Access and MFA, you can enable SAML Single sign-on in the Microsoft Azure portal. Click here to learn how to set up SAML authentication.