Setting up Two-Factor Authentication with RSA SecurID
You can set up Two-Factor Authentication (TFA) with RSA SecurID in Password Manager Pro if you have RSA Authentication Manager and RSA SecurID Appliance in your environment. This will help you leverage RSA SecurID's authentication factor as the second layer of security for your login.
Following are the steps to set up Two-Factor Authentication with RSA SecurID in Password Manager Pro:
- Configuring Two-Factor Authentication in Password Manager Pro
- Integrating RSA SecurID with Password Manager Pro
- Enforcing Two-Factor Authentication for Required Users
- Connecting to Password Manager Pro's Web Interface When TFA is Enabled
1. Configuring Two-Factor Authentication in Password Manager Pro
- Navigate to Admin >> Authentication >> Two-Factor Authentication.
- Choose the option RSA SecurID and click Save. Administrators can also enable RSA On-Demand authentication, by selecting the On-Demand authentication checkbox.
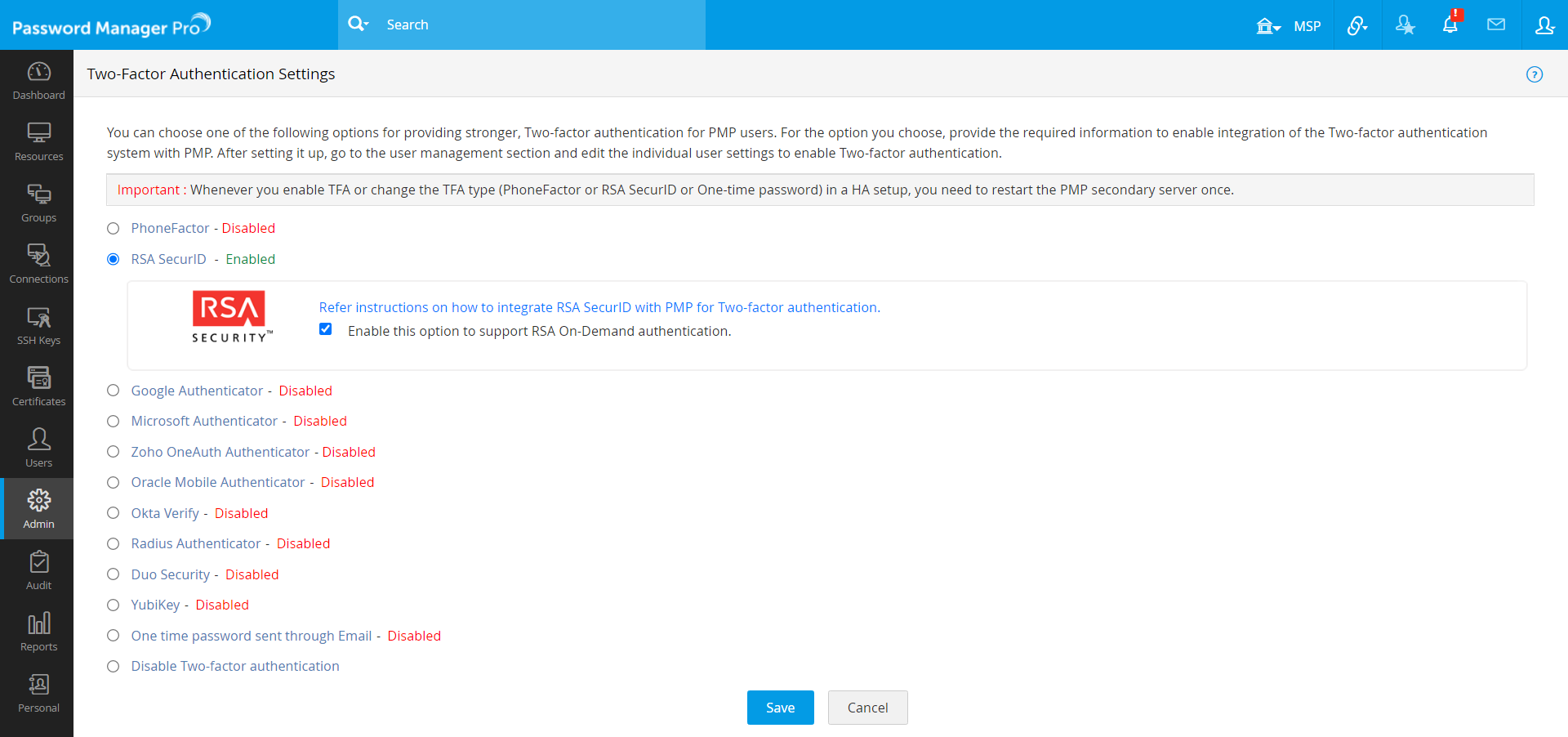
- Then, click Confirm to enforce RSA SecurID as the second factor of authentication.
2. Integrating RSA SecurID with Password Manager Pro
You can integrate RSA SecurID with Password Manager Pro by following the below steps:
- Register the Password Manager Pro server as an Agent Host in the RSA Authentication Manager.
- Generate RSA Authentication Manager configuration file, or sdconf.rec in RSA manager. Copy and paste the sdconf.rec to the <PMP_SERVER_HOME>\bin directory. In addition, if a node secret file (securid) exists, copy and paste that as well.
- In the RSA Authentication API configuration file (rsa_api.properties), edit the "RSA_AGENT_HOST" property value as Password Manager Pro's server hostname or IP address. This file will be located in the default application directory (<PMP_SERVER_HOME>\bin).
Note: If you are using Password Manager Pro's high availability feature, you need to carry out the above steps in the secondary server installation as well.
Mapping Password Manager Pro users to RSA Authentication Manager:
Before the second factor authentication can take place, use the RSA Security Console to enter all desired Password Manager Pro users into RSA Authentication Manager, assign tokens to them and activate them on the appropriate Agent Host.
Ensure that the user name in RSA Authentication Manager and the corresponding user name in Password Manager Pro are the same. For an already existing RSA user, in case there is a user name mismatch between Password Manager Pro and RSA Authentication Manager, you can map the correct user name in Password Manager Pro by editing the user properties in Password Manager Pro.
For example, if you have imported a user by the name 'ZYLKER\rob' from Active Directory into Password Manager Pro and in RSA Authentication Manager, the username is recorded as 'rob', there will be a mismatch. To avoid that, you can edit the user name in Password Manager Pro and get the name 'ZYLKER\rob' mapped to 'rob')
The following sequence describes the authentication process between Password Manager Pro and RSA SecurID:
- When user first tries to access Password Manager Pro, authentication is done through Active Directory or LDAP or locally.
- Password Manager Pro prompts the user for a username and the RSA SecurID passcode, both of which are sent to the RSA Authentication Manager through the RSA Runtime API.
- RSA Authentication Manager then authenticates the user and returns a message to Password Manager Pro.
- Password Manager Pro grants the user access to the requested resource.
3. Enforcing Two-Factor Authentication for Required Users
- Once you confirm RSA SecurID as the second factor of authentication, in a new pop-up window, you will be prompted to select users for whom TFA should be enforced.
- You can enable or disable TFA for a single user or multiple users in bulk from here. To enable TFA for a single user, click Enable beside the respective username. For multiple users, select the required usernames and click Enable at the top of the user list. Similarly, you can also Disable TFA from here.
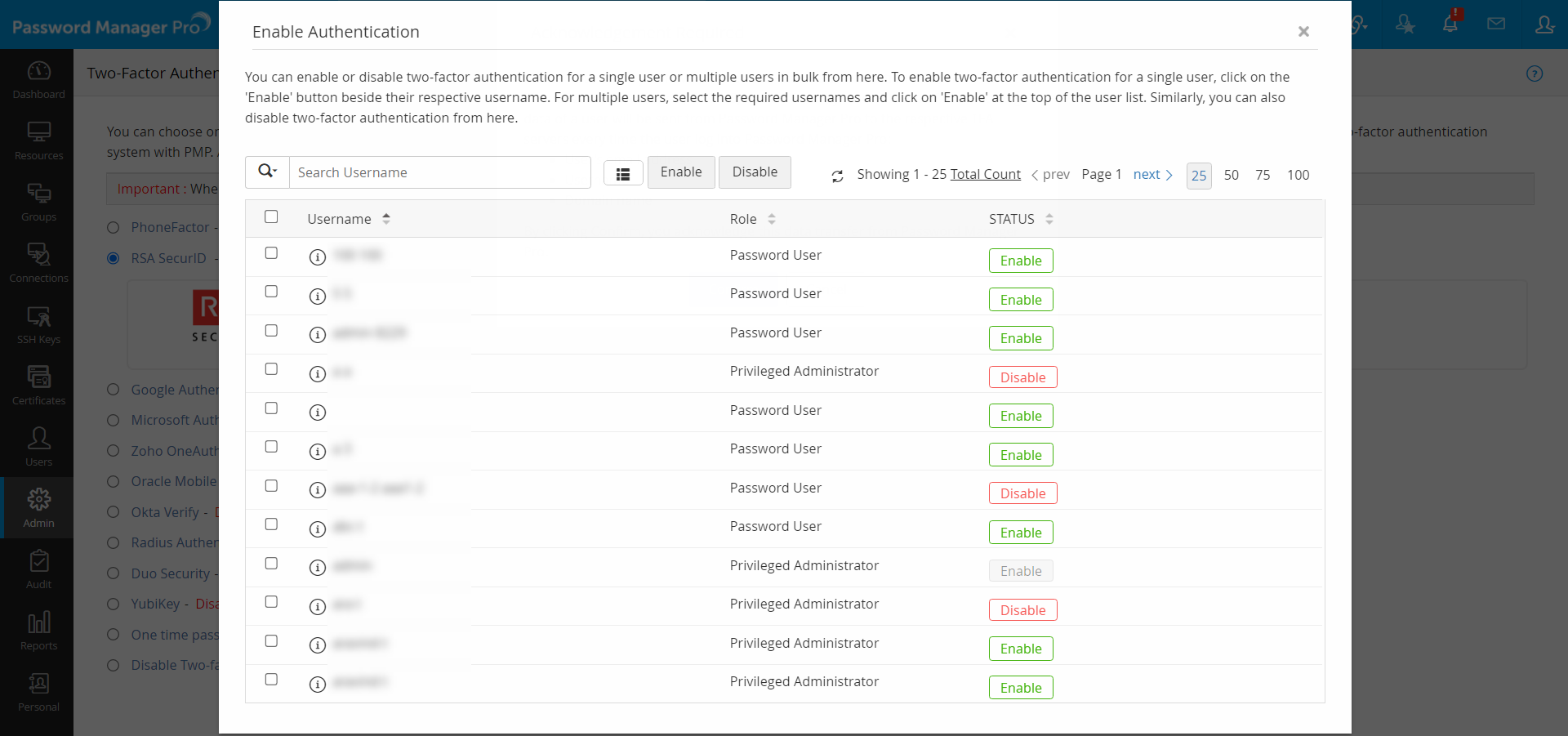
- You can also select the users later by navigating to Users >> More Actions >> Two-Factor Authentication.
4. Connecting to Password Manager Pro Web Interface When TFA is Enabled
The users who have Two-Factor Authentication enabled for their accounts will have to authenticate twice successively during login. As mentioned above, the first level of authentication will be through Password Manager Pro's local authentication or AD/LDAP authentication. Depending on the type of TFA chosen by the administrator, the second level of authentication will differ as explained below:
- Upon launching the Password Manager Pro web interface, the user has to enter the username and local authentication or AD/LDAP password to login to Password Manager Pro and click Login.
- Against the text field RSA Passcode, enter the RSA SecurID passcode. The passcode could be a combination of PIN and Tokencode or just the Tokencode alone or the On-Demand PIN depending on the configuration done in RSA Authentication Manager.
- If you want to leverage the RSA On-Demand authenticator, select RSA On-Demand and proceed. In this case, you need to provide the On-Demand Tokencode as specified in case 3 below.
4.1 Three different scenarios possible while logging into Password Manager Pro using RSA SecurID
Case 1: Entering user generated / system created PIN
As mentioned above, the RSA passcode could be a combination of PIN and tokencode or just tokencode alone or a password depending on the configuration done in RSA Authentication Manager. If the settings in RSA Security Console demands the users to create a PIN on their own or use a system generated PIN, the following options would be shown to the users after step 2 (that is, after entering the first password and RSA tokencode to log in to Password Manager Pro).
User Created PIN:
In the case of user created PIN, users will get the option to enter the PIN on their own. The PIN should contain numeric characters - minimum of 4 and a maximum of 8 characters. After entering the PIN, the user will have to wait for a while until the RSA tokencode changes to a new value. Then, in the next screen, enter the new PIN and the RSA tokencode to authenticate.
System Created PIN:
In the case of system created PIN, Password Manager Pro itself will randomly generate a PIN and it will be shown on the screen. Users will have to note down the new PIN and wait for a while until the RSA tokencode changes to a new value. Then, in the next screen, the users will have to enter the new PIN as generated by the system and the RSA tokencode to authenticate.
Case 2: New Tokencode Mode
If a user attempts to log in to Password Manager Pro using a random RSA passcode or by guesswork for a specified number of times, the RSA Authentication Manager will turn the screen to the New Tokencode mode to verify whether the user possesses the token. In that case, Password Manager Pro prompts for next tokencode during the login. That means, the user will have to wait until the RSA device shows a new tokencode and the new code to proceed with logging into Password Manager Pro.
Note: If the new tokencode entered by the user is wrong, Password Manager Pro will revert to the initial login screen. Users will have to start again by entering the username.
Case 3: Tokencode Mode
When RSA On-Demand authenticator is configured, you need to supply the Tokencode to log in to Password Manager Pro. Tokencode will be sent to the registered email id or mobile number as configured in the RSA On-Demand authentication system.
If you have configured High Availability
Whenever you enable TFA or when you change the TFA service type, you need to restart the Password Manager Pro secondary server once for it to take effect.