Note: YubiKey Authenticatior is an advanced authenticator available as part of the Professional edition of ADSelfService Plus.
ADSelfService Plus supports the YubiKey 5 series, YubiKey 5 FIPS series, and YubiKey 5 CSPN series as well as the Yubico OTP protocol for authentication.
Once YubiKey Authenticator is enabled, users are authenticated first through their AD domain credentials, and next through the one-time passcode (OTP) generated by the YubiKey Authenticator.
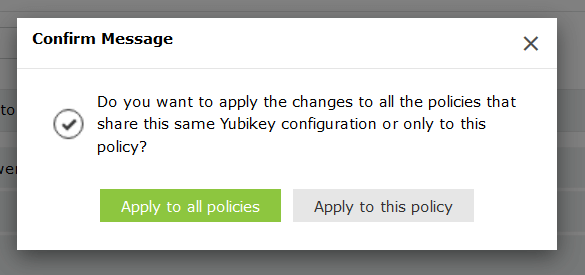
Note: You can choose to enforce multiple configurations for different users based on their domain, group, or OU membership, or simply apply one YubiKey Authenticator setting for all users.
Your request has been submitted to the ADSelfService Plus technical support team. Our technical support people will assist you at the earliest.
Copyright © 2026, ZOHO Corp. All Rights Reserved.