Shadow IT is no longer a hidden side problem; it is now one of the biggest blind spots in SaaS-driven organizations. With teams adopting tools faster than IT teams can track, companies are losing visibility, control, and money.
This guide breaks down everything you need to discover, track, and eliminate shadow IT with practical workflows and actionable steps.
Shadow IT discovery is the process of identifying unauthorized or unapproved software, apps, and services used within an organization without IT team oversight.
Shadow IT includes:
Example
A marketing team subscribes to an email automation tool without informing the IT team. That tool now stores customer data outside of approved systems, creating compliance and security risks.
Shadow IT is not just an IT issue. It directly impacts security, compliance, costs, and operational efficiency.
Key statistics
What's at risk?
| Risk area | Impacts |
|---|---|
| Security | Data breaches and unauthorized access |
| Compliance | Violations of regulations such as the GDPR and SOC 2 |
| Financial | Duplicate tools and unused licenses |
| Operations | Data silos and inefficiency |
Shadow IT discovery tools combine multiple data sources to uncover hidden applications and provide a complete view of SaaS usage across an organization.
The core workflow
Continuously scans for and detects new applications without requiring manual input or audits
Aggregates financial data from multiple sources to provide a clear view of SaaS spending across departments
Connects users to licenses and applications, helping you identify unused or duplicated subscriptions
Evaluates each application against security standards and compliance requirements to prioritize risks
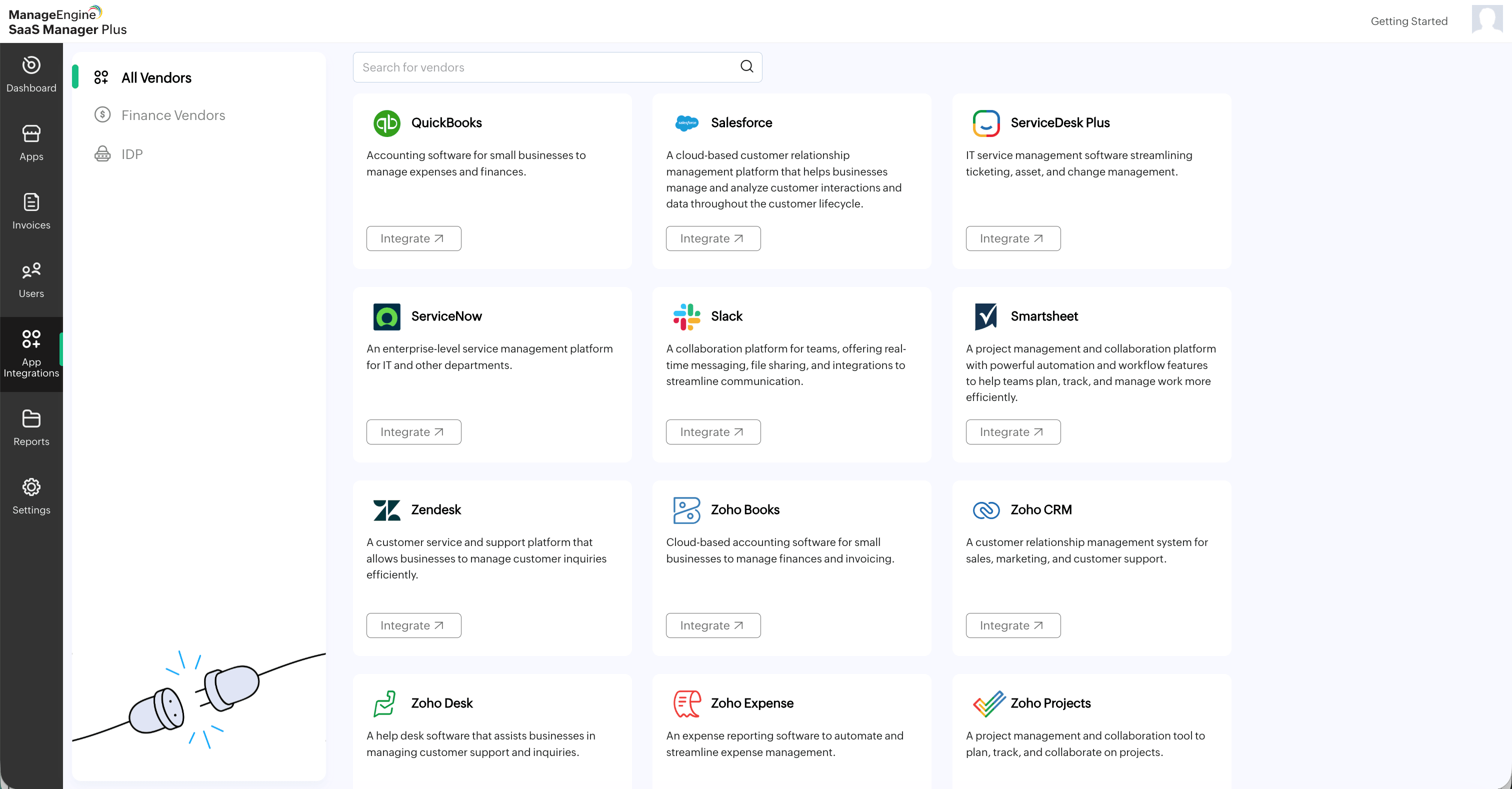
Integrates with identity providers like Okta and Entra ID to track verified user access and improve control
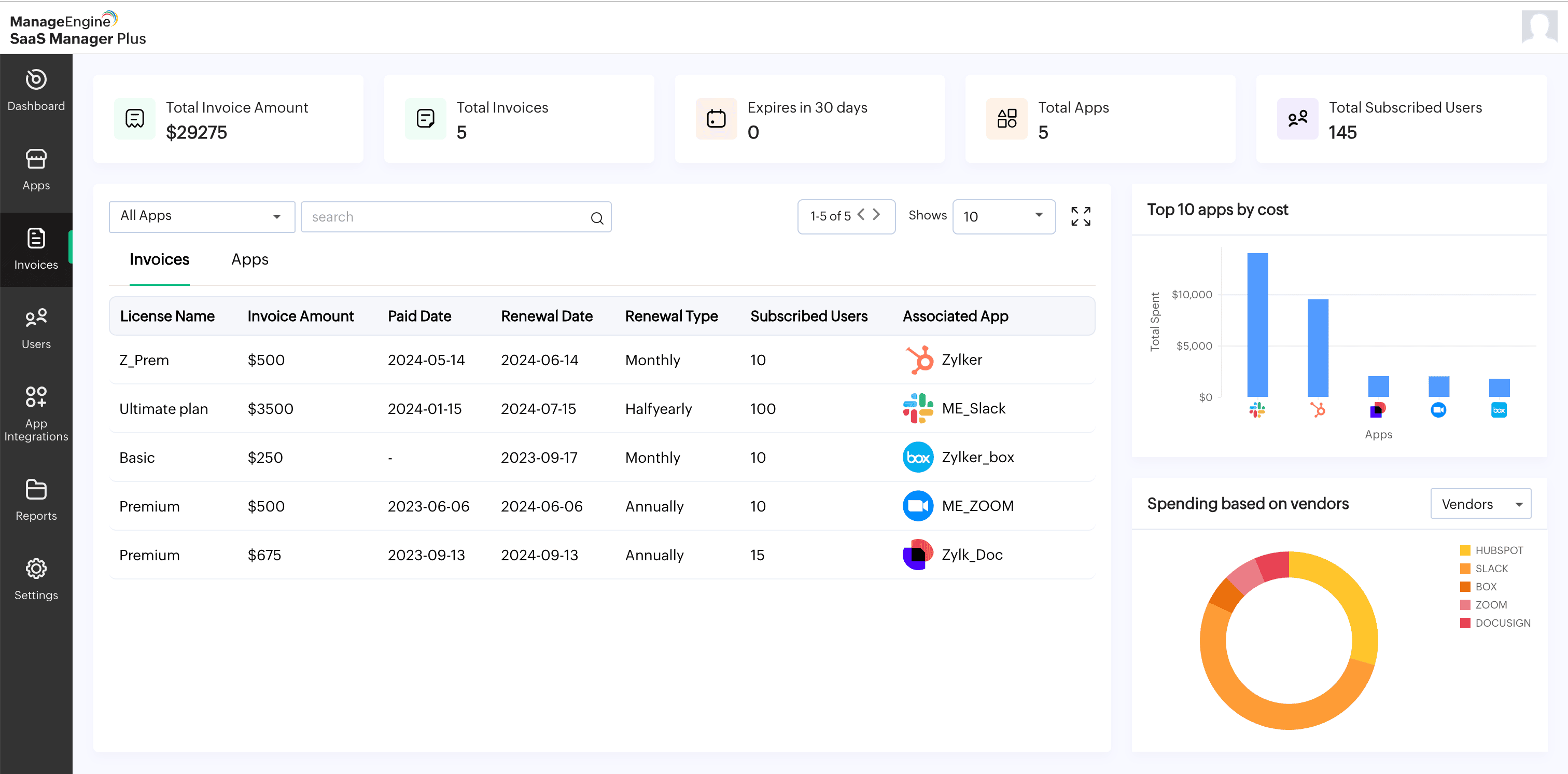
Monitors contract and subscription renewal dates to prevent unexpected charges and enable timely decisions
Analyzes engagement and activity levels to identify underutilized or redundant tools for optimization purposes
| Aspect | Shadow IT | Shadow AI |
|---|---|---|
| Definition | Unauthorized software usage | Unauthorized AI tool usage |
| Examples | CRM and project tools | AI copilots and content tools |
| Risks | Data leakage and compliance issues | Exposure of sensitive data to models |
| Growth | High | Extremely rapid |
Shadow AI adoption is accelerating faster due to easy access to GenAI tools without governance.
Organizations often lack a single source of truth, making it difficult to track all SaaS applications across departments.
Teams adopt tools independently to move faster, unintentionally creating blind spots for IT and security teams.
Freemium and trial-based tools do not appear in expense data, making them harder to detect through traditional methods.
Different teams often use multiple tools for the same function, increasing costs and operational complexity.
Employees may resist restrictions if policies slow them down or limit access to their preferred tools.
Define clear ownership, approval workflows, and usage policies to ensure all tools are vetted before adoption.
Train teams on the risks of shadow IT and guide them toward approved tools that meet their needs.
Route all SaaS purchases through IT or finance teams to maintain visibility and control over the tech stack.
Implement tools that automate the discovery, tracking, and management of all SaaS applications in use.
Identify overlapping applications and standardize on a smaller approved set to reduce redundancy and costs.
Use SSO and role-based access to control who can access which tools and prevent unauthorized usage.
Reduces SaaS waste by identifying unused licenses and eliminating duplicate tools, often saving up to 30% of spending
Minimizes the attack surface by identifying and removing unauthorized and high-risk applications
Ensures all tools meet regulatory standards like the GDPR and SOC 2, helping you maintain audit readiness
Streamlines workflows by reducing tool sprawl and standardizing on a common set of approved tools, ensuring teams work on the same platforms, share data seamlessly, and avoid fragmentation caused by multiple disconnected apps
Centralizes application usage and data flows, giving IT teams full control and insight into the SaaS ecosystem
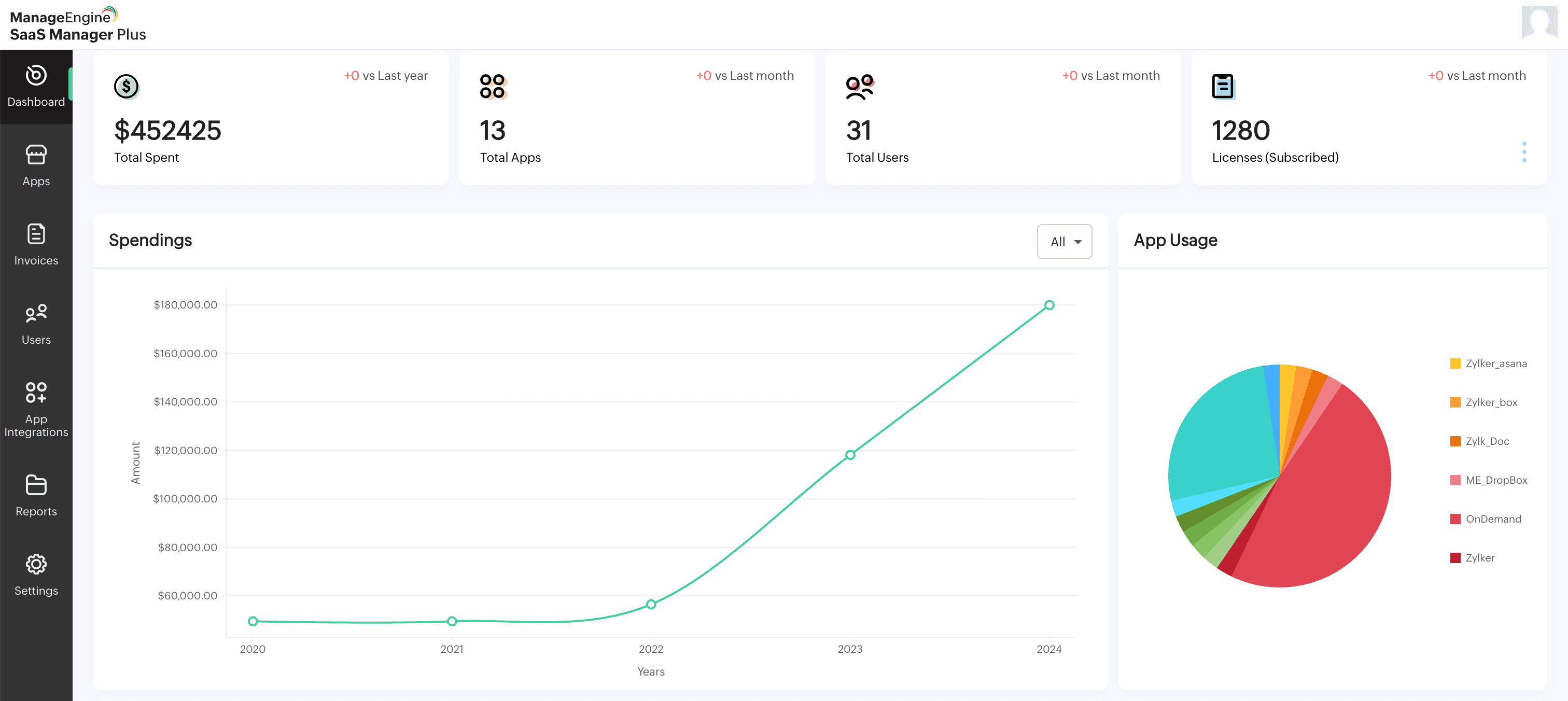
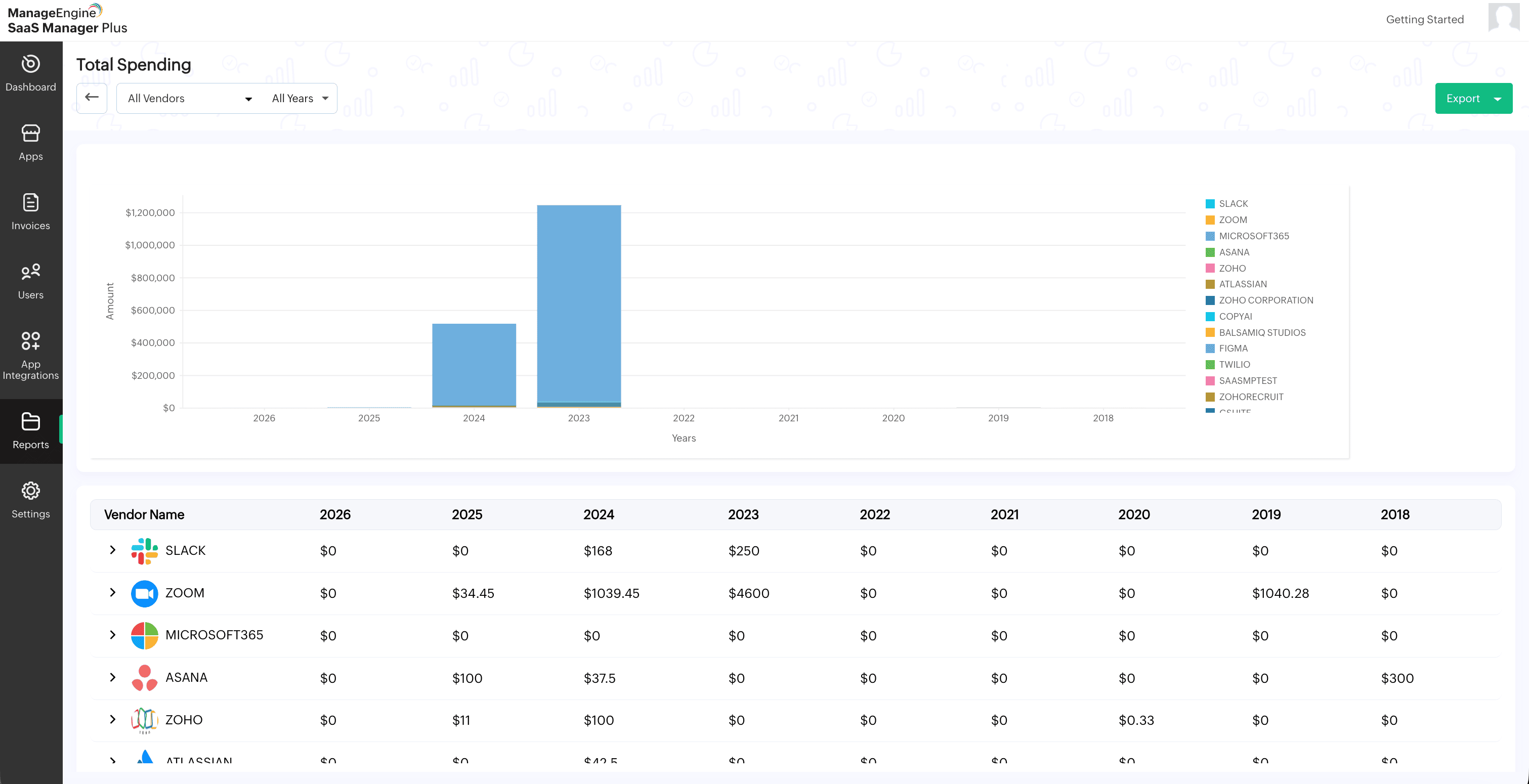
SaaS Manager Plus provides a strong discovery capability along with cost optimization and contract visibility, making it suitable for IT teams that want both control and financial insights. It integrates well with existing IT ecosystems and offers continuous monitoring of SaaS usage.
Zylo focuses heavily on SaaS spending visibility and optimization, helping enterprises track licenses, reduce waste, and manage renewals effectively. It integrates with financial systems, SSO systems, and HR tools to build a complete SaaS inventory.
Torii offers strong automation and workflow capabilities, enabling teams to manage SaaS life cycle processes like onboarding, offboarding, and license allocation. It provides centralized visibility into SaaS usage and helps uncover shadow IT across departments.
BetterCloud focuses on SaaS operations and governance, with powerful automation for enforcing security policies and managing user access. It also enables IT teams to take immediate action on shadow IT through automated remediation workflows.
Productiv specializes in advanced usage analytics, enabling enterprises to understand how applications are used at a granular level. It combines usage data with contract insights to help enterprises optimize SaaS investments and improve decision-making.
SaaS Manager Plus helps organizations identify, manage, and eliminate shadow IT by combining discovery, spending tracking, and governance into a single platform.
Shadow IT often emerges from a simple problem: Teams want speed, but processes slow them down. The solution is not strict control; it is visibility combined with enablement.
Organizations that succeed:
If you do not know how many SaaS apps your teams are using today, you already have a shadow IT problem. Start by auditing your stack or use a SaaS management platform to automate discovery and take control before costs and risks escalate.