Shadow IT management is the process of identifying, monitoring, and controlling unauthorized applications, tools, and services used within an organization without IT approval.
It involves discovering all SaaS applications in use, assessing their risks, governing their usage, and optimizing costs and compliance.
In simple terms, shadow IT management helps organizations answer three critical questions:
Shadow IT is no longer a small visibility problem. It has become a major operational and financial risk.
Recent data highlights the scale of the problem:
Without proper management, shadow IT leads to fragmented systems, security gaps, and uncontrolled spending.
Shadow IT introduces multiple layers of risk that extend beyond visibility. These risks impact security, compliance, operations, and overall business performance.
Unapproved applications often bypass security reviews, encryption standards, and access controls.
This creates blind spots where:
IBM reports that the average cost of a data breach exceeded $4 million globally, making unmanaged tools a serious financial risk.
Shadow IT can easily violate regulatory frameworks such as GDPR, HIPAA, or SOC 2.
Common issues include:
Even a single unauthorized tool handling customer data can lead to penalties and legal exposure.
SaaS sprawl refers to the uncontrolled growth of applications across teams.
This leads to:
Studies show that nearly 25%-30% of SaaS spend is wasted due to poor visibility and management.
Managing shadow IT is complex because it sits at the intersection of IT, security, finance, and employee behavior.
Many SaaS tools are adopted outside IT through personal logins or expense claims, making it difficult to maintain a single source of truth.
Teams often choose tools that help them move faster, and strict controls can lead to pushback or further hidden usage.
Overly rigid governance can slow teams down, creating a trade-off between compliance and efficiency.
IT, finance, procurement, and business teams all own parts of the SaaS life cycle, leading to misalignment and gaps.
Without continuous tracking, organizations struggle to detect new app usage, license changes, or emerging risks in time.
The goal is not to eliminate shadow IT entirely, but to control and govern it effectively.
Managing shadow IT effectively requires a structured approach. Instead of reacting to risks as they appear, organizations need a repeatable process to discover, assess, and control SaaS usage across the business.
Start with full visibility.
Use multiple discovery methods:
Not all shadow IT is equally risky.
Classify applications based on:
This helps prioritize which tools need immediate action.
Define clear policies for SaaS usage.
This includes:
Policies should enable productivity, not block it.
Shadow IT is dynamic. New tools appear constantly.
Continuously monitor:
Real-time monitoring helps detect anomalies early.
Manual tracking does not scale.
Automation helps:
This reduces operational overhead and improves consistency.
Once visibility is achieved, optimization becomes easier.
Focus on:
This step directly impacts ROI.
Beyond processes and tools, successful shadow IT management depends on how organizations approach governance at a cultural and operational level.
Encourage teams to disclose tools without fear, making governance collaborative rather than restrictive.
Regularly engage with departments to understand why tools are adopted and whether they solve critical needs.
Make it easy and fast to request and approve tools so employees don't bypass the system.
Awareness programs help users understand the implications of unapproved tools, improving voluntary compliance.
Periodic reviews help identify redundant apps, unused licenses, and potential security risks.
Combining technical and financial data enables more informed decisions around usage, risk, and spend optimization.
Organizations that treat shadow IT as a governance problem and not just a restriction problem will see better adoption and outcomes.
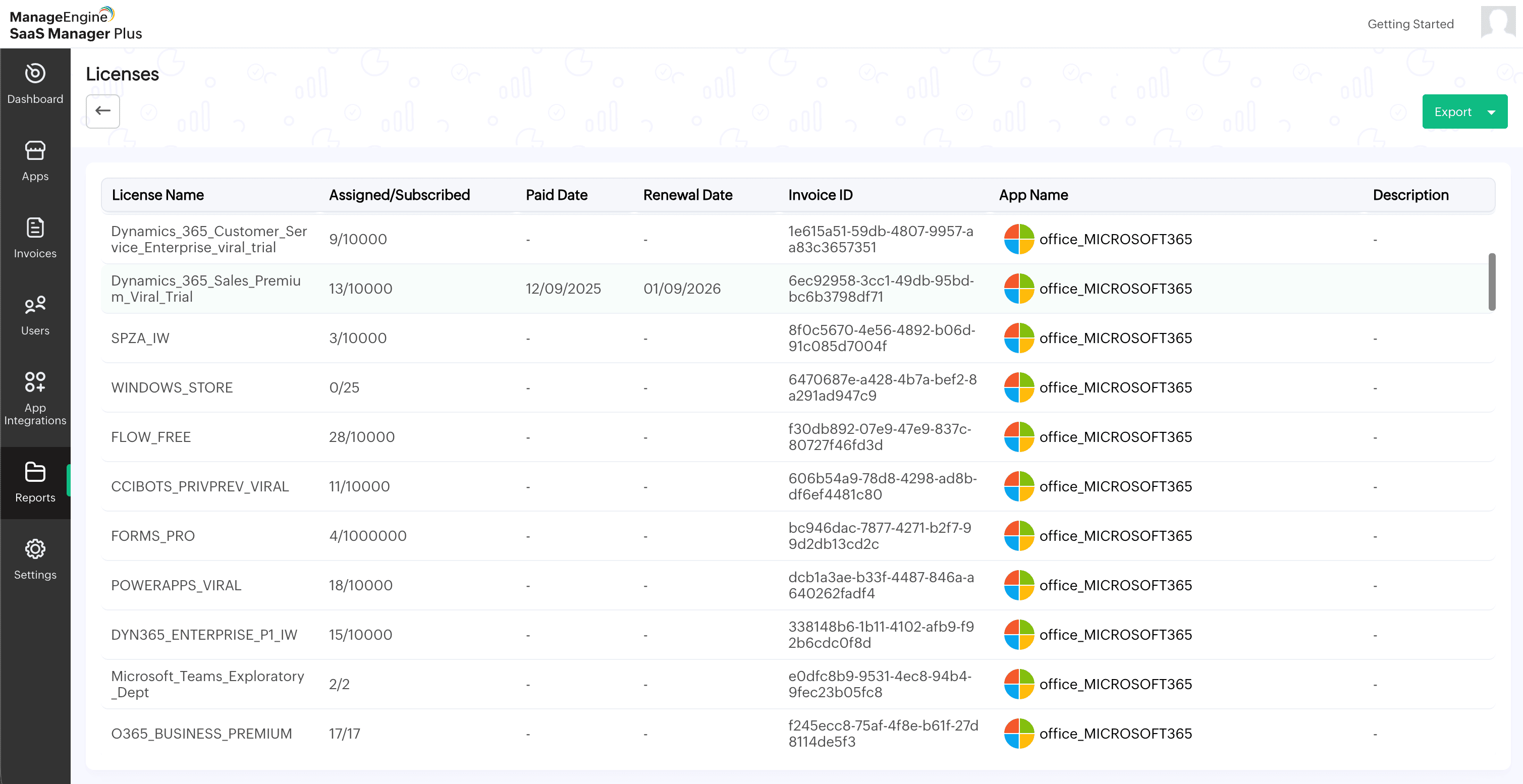
ManageEngine SaaS Manager Plus provides a centralized platform to discover, manage, and optimize SaaS applications.
Identifies applications through multiple sources like network logs and expense data to uncover hidden or unmanaged tools.
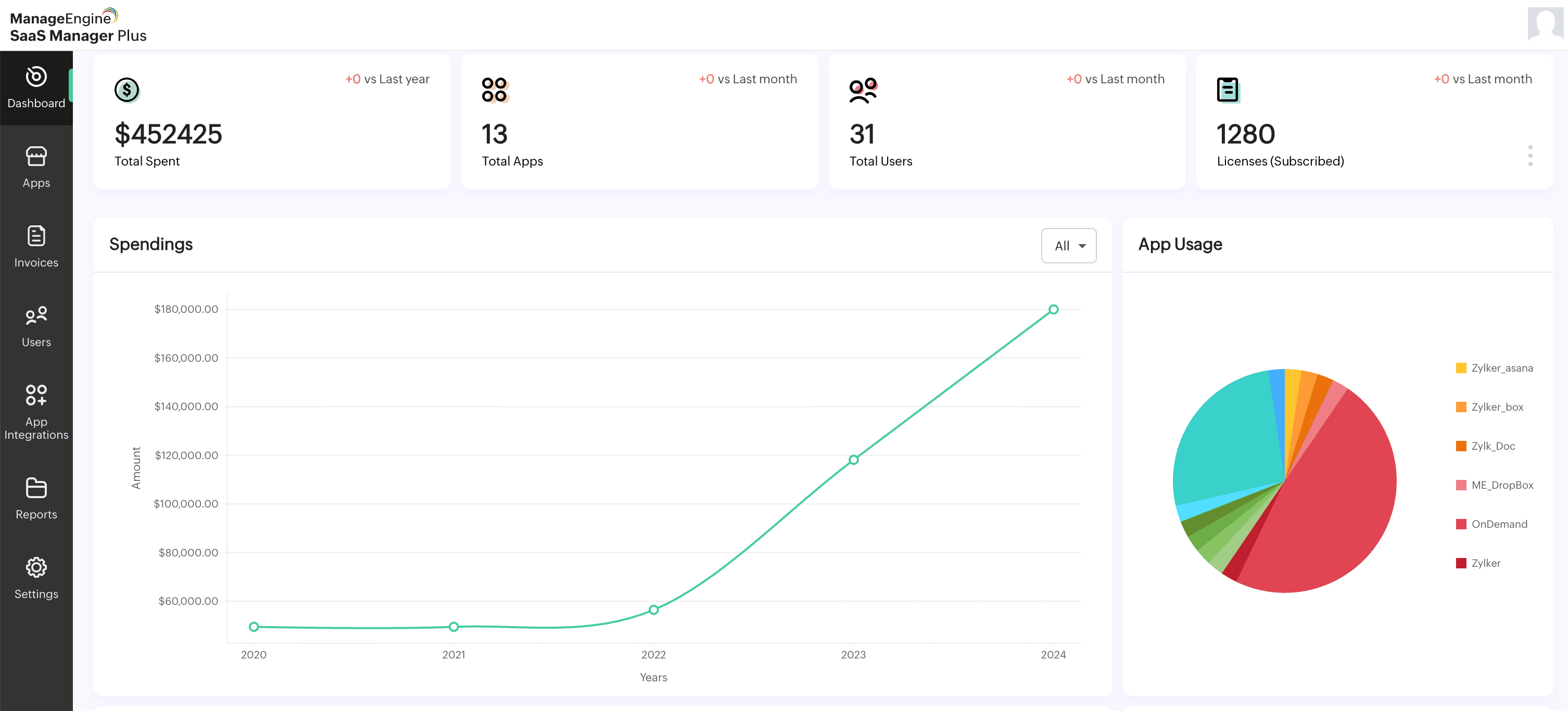
Tracks actual usage patterns to highlight waste and opportunities for license optimization.
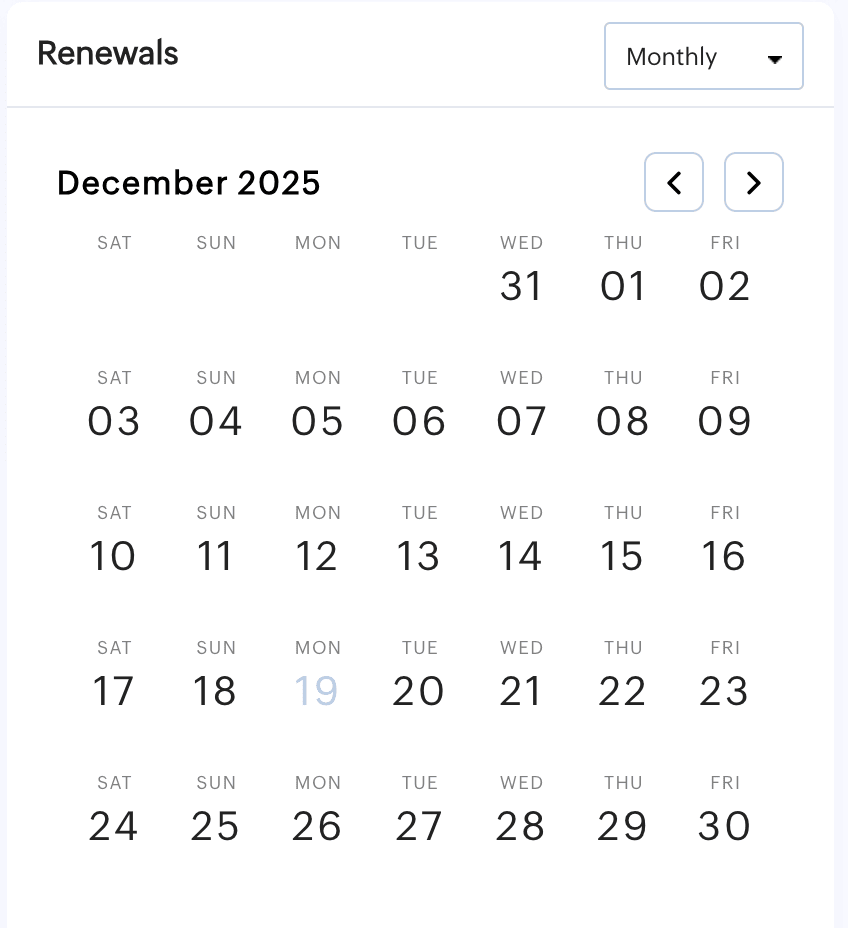
Provides visibility into contract timelines, helping teams act before auto-renewals lock in unnecessary spend.
A combination of reports enables you to eliminate redundancies and align spend with actual usage.
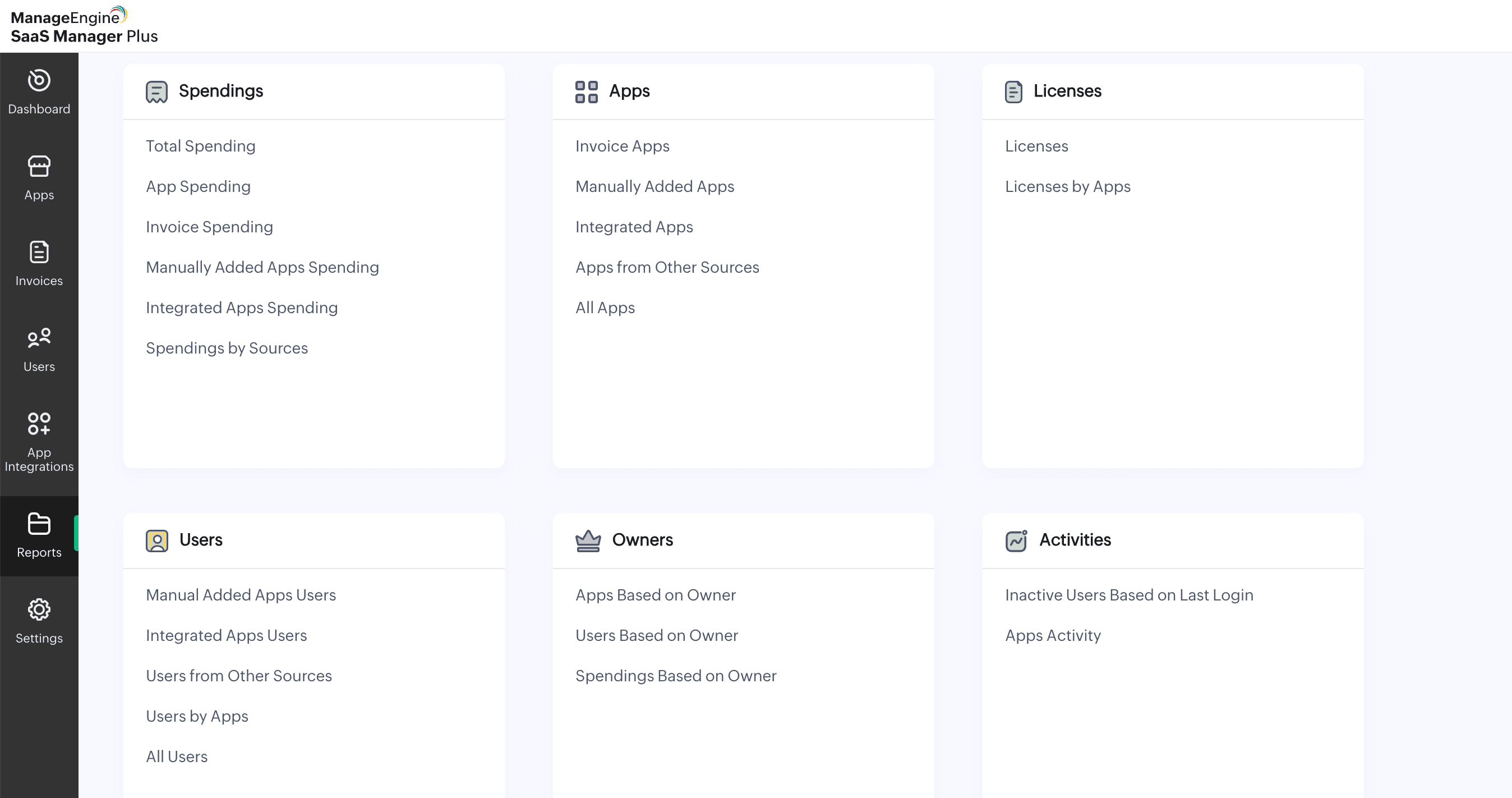
By combining visibility and tracking, it helps organizations reduce risk, control costs, and streamline SaaS operations.
A practical outcome many organizations see:
Managing shadow IT in 2026 is not about restricting employees; it is about enabling them with the right tools, safely and efficiently.