Compliance Report
Ensuring compliance for every device is imperative for any network organization. Compliance entails adhering to a set of rules and standards established by international organizations to mitigate security vulnerabilities. Failing to comply can result in hefty fines, damage to reputation, and even legal consequences like imprisonment. Attempting to manually maintain compliance for numerous devices is impossible.
A compliance reporting tool or software proves invaluable by delivering real-time compliance reports, eliminating the need for manual management or auditing. Utilizing Network Configuration Manager as your compliance reporting software allows you to obtain real-time insights into the compliance status of devices through its compliance report feature, enabling you to stay proactive in addressing non-compliance violations.
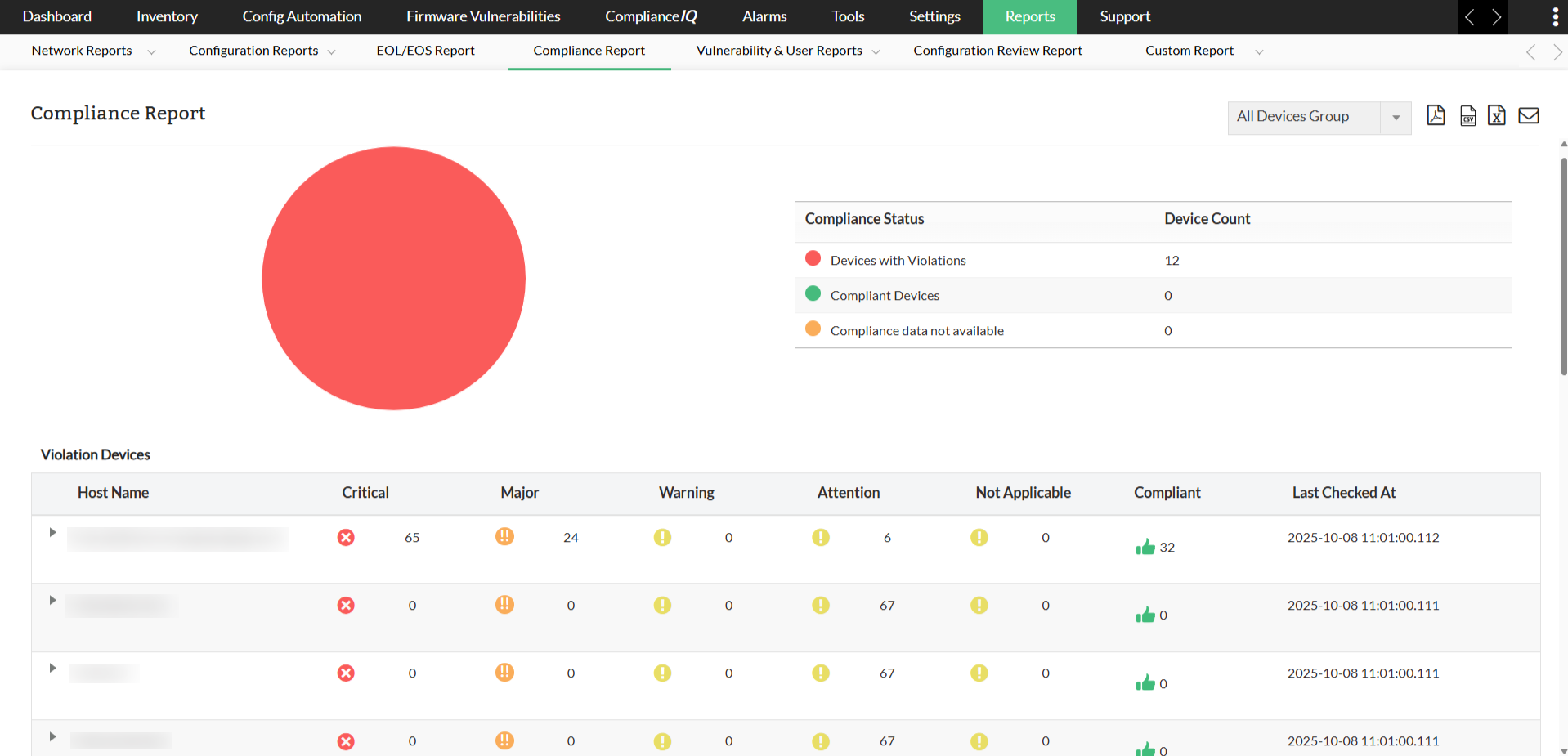
With this report, you can stay updated regarding the compliance status of devices within your network infrastructure. It furnishes details about policy violations and compliance adherence for associated policies.
This report is divided into three sections: Devices with Violations, Compliant Devices, and Compliance Data Not Available.
In the Devices with Violations report, you'll find the device's host name, severity levels (such as critical, major, and warning), the count of compliant devices, and the timestamp of the last check. You can further delve into individual devices to identify which specific policy is violated, along with severity levels (critical, major, and warning), the count of compliant devices, and the last check timestamp.
Clicking on a device will lead you to a detailed page specifying which rules of the policy are violated and which ones are compliant. From here, you have the capability to implement remediation configurations for the violated rules and rectify the non-compliance.
Moreover, you have the flexibility to export this report in both PDF and CSV formats, or send it via email if necessary. Additionally, if you have organized device groups, you can view the report for a specific group of devices.
To access this report, navigate to Reports -> Locate and click Compliance Report within the Other Reports section.
Download Network Configuration Manager now and enjoy this and various other kinds of reports and audits with a free, 30-day trial.
Want to see the reports in action? Request a free, personalized demo.
You can also get a price quote based on your usage and needs.
FAQs on Compliance reports
What is a compliance report?
+Why are compliance reports important?
+