Configuration and change management for Fortinet environments
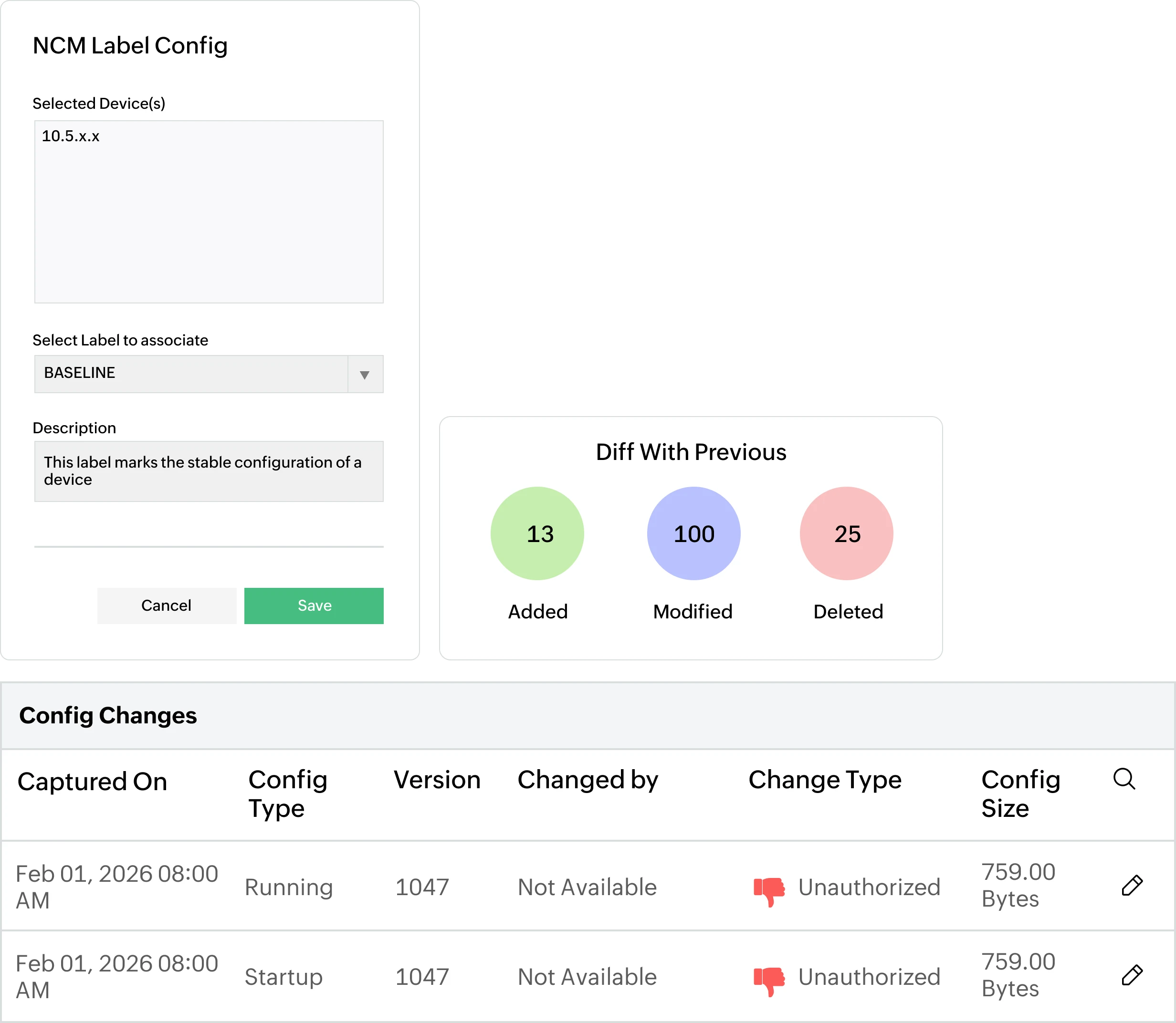
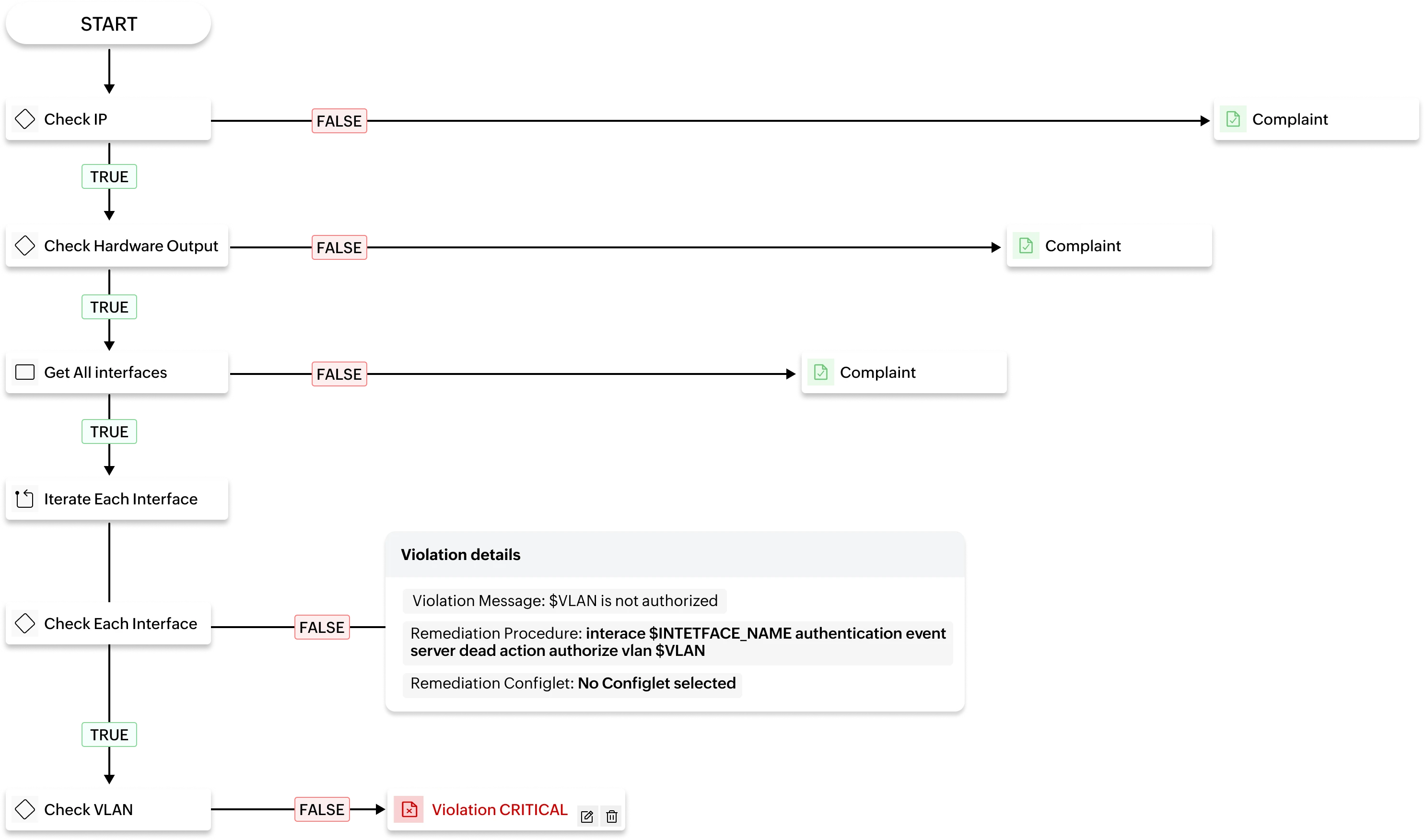
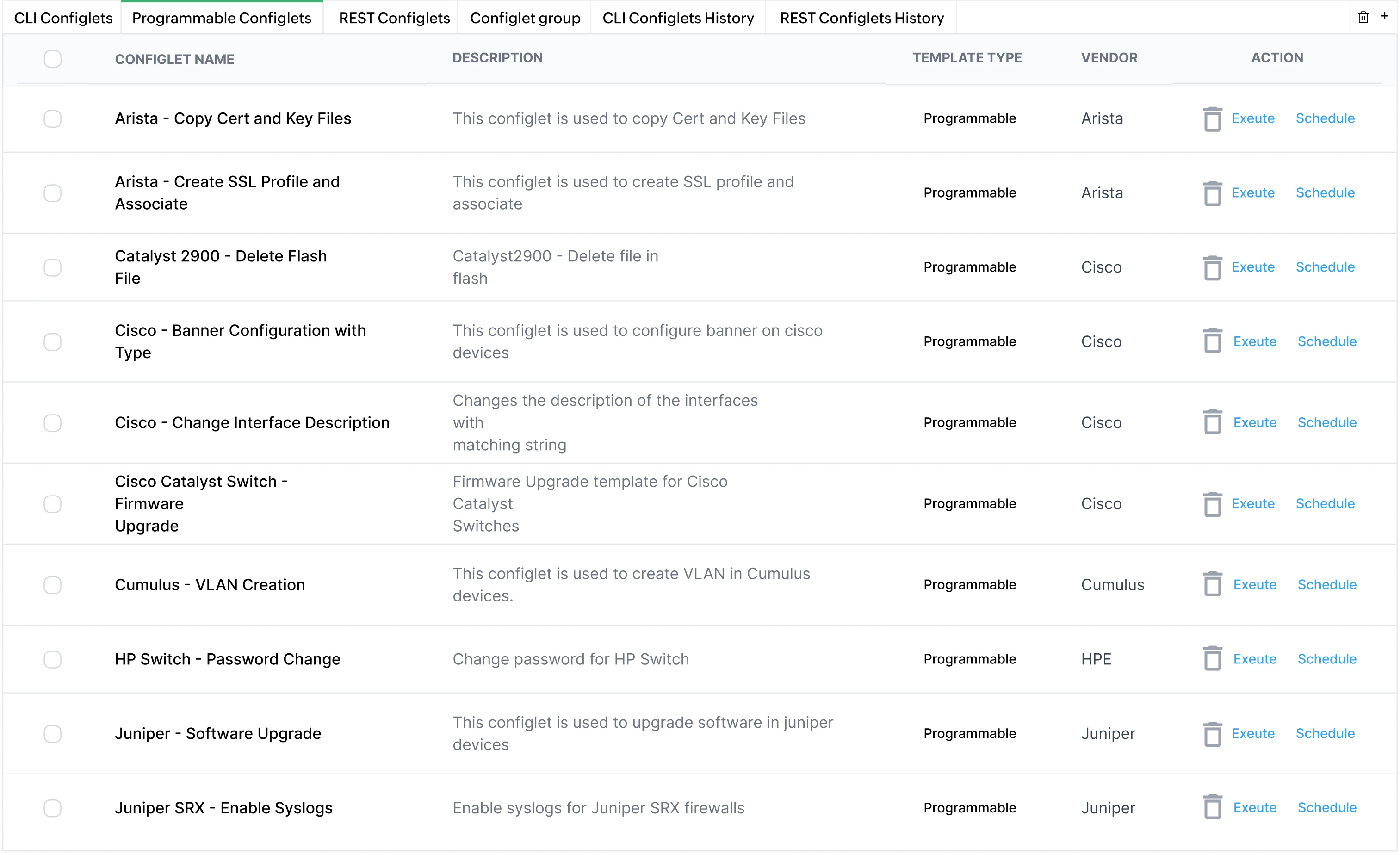
Frequent configuration changes across Fortinet environments make it difficult to trace outages without structured tracking. Network Configuration Manager establishes baselines and maintains version-controlled configuration history across FortiGate, FortiSwitch, and FortiAP devices.
- Establish baseline configurations for Fortinet devices
- Automatically back up running and startup configurations
- Maintain detailed, time-stamped configuration history
- Compare configurations using side-by-side diff views
- Restore previously approved versions to recover from misconfigurations