Network Audit
Organizations depend on their network infrastructures to perform everyday operations seamlessly, and this is increasingly important today in our remote workplace environments. This requires IT administrators to be vigilant to ensure that network systems operate efficiently.
With networks expanding exponentially, the number of vulnerabilities and loopholes increases as well. A network outage, or even a minor glitch can result in loss of revenue and reputation of the company. There are several ways in which networks can become susceptible to cyberattacks, or breakdown on their own.
What is network audit?
With network audits, IT admins can understand the status of their networks, and take appropriate actions to fix faults. Network auditing is a process of collating data of different network parameters, and analyzing it for meaningful insights. These insights can be used to understand the health and general status of the network when compared to existing benchmarks and industry compliance standards.
Why is network auditing important?
Activities like changing hardware, adding new devices, changing configurations, or installing or modifying firewalls, are all imperative for optimum network performance and security. Maintaining a record of all these operations is equally important. Whenever the network malfunctions, IT admins can use these records to identify and troubleshoot the issue quickly.
In our current remote work era, bring your own devices (BYODs) are increasingly being adopted by organizations. With this work culture shift comes increased bandwidth usage and security risks. In organizations where BYOD has been implemented, IT admins must be aware of the risks, and enforce policies to manage these devices and minimize risks.
Even when employees connect to the corporate network with company devices, the networks are undergoing continuous changes. It's important that network administrators monitor changes, and perform audits on a regular basis to ensure that the network security and performance aspects are faultless.
How to do a network audit?
Although tools automate the network auditing and reporting process, IT admins can perform these actions manually as well. The touchpoints remain the same for both types of auditing. Some of them are:
1. Network device inventory
It is crucial to audit your network device inventory at regular intervals. Devices have to be scanned to confirm if they're still receiving firmware and security updates from the vendors. If devices are not being updated regularly, your organization should determine if they are obsolete and should be replaced. The IT admins should be aware of the firmware versions and operating systems these devices are running on, and troubleshoot whenever necessary.
2. Bandwidth consumption
Avoiding bandwidth bottlenecks is crucial for providing a seamless end-user experience. To do that, IT admins should carefully analyze their network to identify trends in bandwidth usage. Detailed analysis will enable IT admins to understand which service or application in their network consumes more bandwidth, and make the appropriate changes.
3. Users and access levels
The number of network users increase as the infrastructure grows in size; it's a good practice to implement a restricted access policy for all users. IT admins, while auditing changes in the network, can check if there were any unauthorized changes made to the network, and revert them promptly.
4. Network configurations and firewall rules
Network configuration changes are made regularly to improve the performance of the network. Firewall rules are also updated regularly to tighten network security. But both of these changes have to be documented and audited because even the slightest error can wreak havoc in the network.
5. Network availability and health
A thorough audit of availability and health parameters can help IT admins learn which devices are troublesome, and what kind of changes regularly cause network outages. They can use this information to avoid issues, or to immediately troubleshoot them when they occur.
Benefits of network auditing
Network audits offer several crucial advantages for organizations, including:
- Strengthened security: By identifying vulnerabilities such as outdated software, weak passwords, or incorrectly set up firewalls, audits significantly mitigate the risk of cyber threats and data breaches.
- Enhanced network efficiency: Identifying network inefficiencies, like overtaxed devices or traffic bottlenecks, allows for precise enhancements, boosting network performance and reliability.
- Compliance verification: Audits ensure that network operations comply with relevant industry standards and internal policies, helping to avoid legal issues and fines related to non-compliance.
- Proactive issue resolution: Regular network reviews facilitate the early identification of security risks and operational problems, enabling timely interventions that avert larger issues and potential data loss.
- Strategic decision support: Providing a clear overview of network health and functionality, audit results support strategic planning for network expansions, resource distribution, and IT budgeting.
Can network auditing be automated?
This brings up the question of whether network auditing processes can be automated, as manual management may not achieve these benefits smoothly. Numerous automation tools are available for this purpose. However, when selecting a network auditing tool, IT administrators should ensure that the tool not only identifies issues but also assesses their impact and provides guidance on resolving them.
ManageEngine Network Configuration Manager - your network audit tool
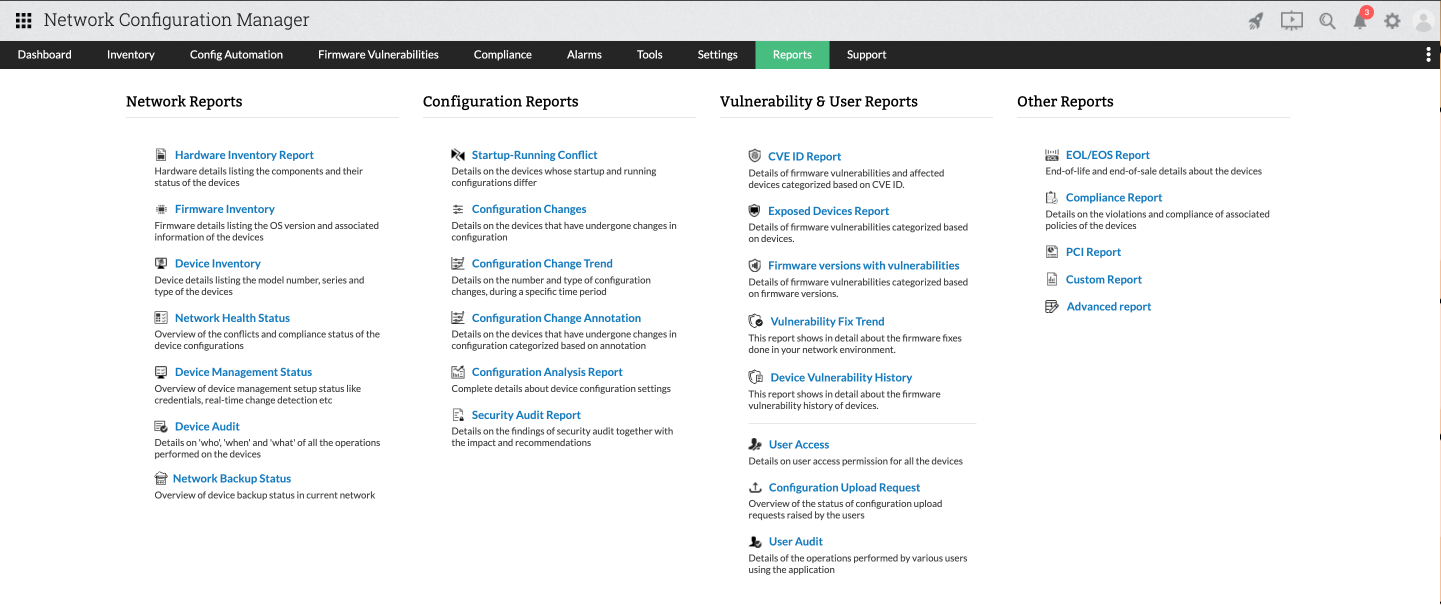
ManageEngine Network Configuration Manager comes with intuitive reporting capabilities that help IT admins to easily analyze network changes, and correlate them with issues. Some of the reports provided include compliance report, vulnerability reports, etc. The built-in reporting capabilities capture all data, and reduce the need for manual documentation. IT admins can easily schedule these reports to be generated at regular intervals, ensuring routine network audits are performed on time, every time.
FAQs about network audit
What are the general best practices in network auditing?
+How frequent should the network audits be conducted?
+How does ManageEngine's Network Configuration Manager helps with audit?
+Can I access ManageEngine's Network Configuration Manager for free?
+Want to streamline your network audit process? Download our 30-day free trial now!