Direct Inward Dialing: +1 408 916 9892
Maintaining secure files and ensuring compliance requires effective file auditing. Organizations need to track who accesses their files, what changes are made, and when these activities occur. That provides the visibility and insights they need to spot security incidents. ADAudit Plus takes this further with centralized Windows and NAS file auditing and advanced behavior analytics to detect file security threats.
Download a free trial Fully functional 30 days
Track all file and folder changes in real time with detailed reports.
Stay on top of failed attempts to read, write, or delete critical files.
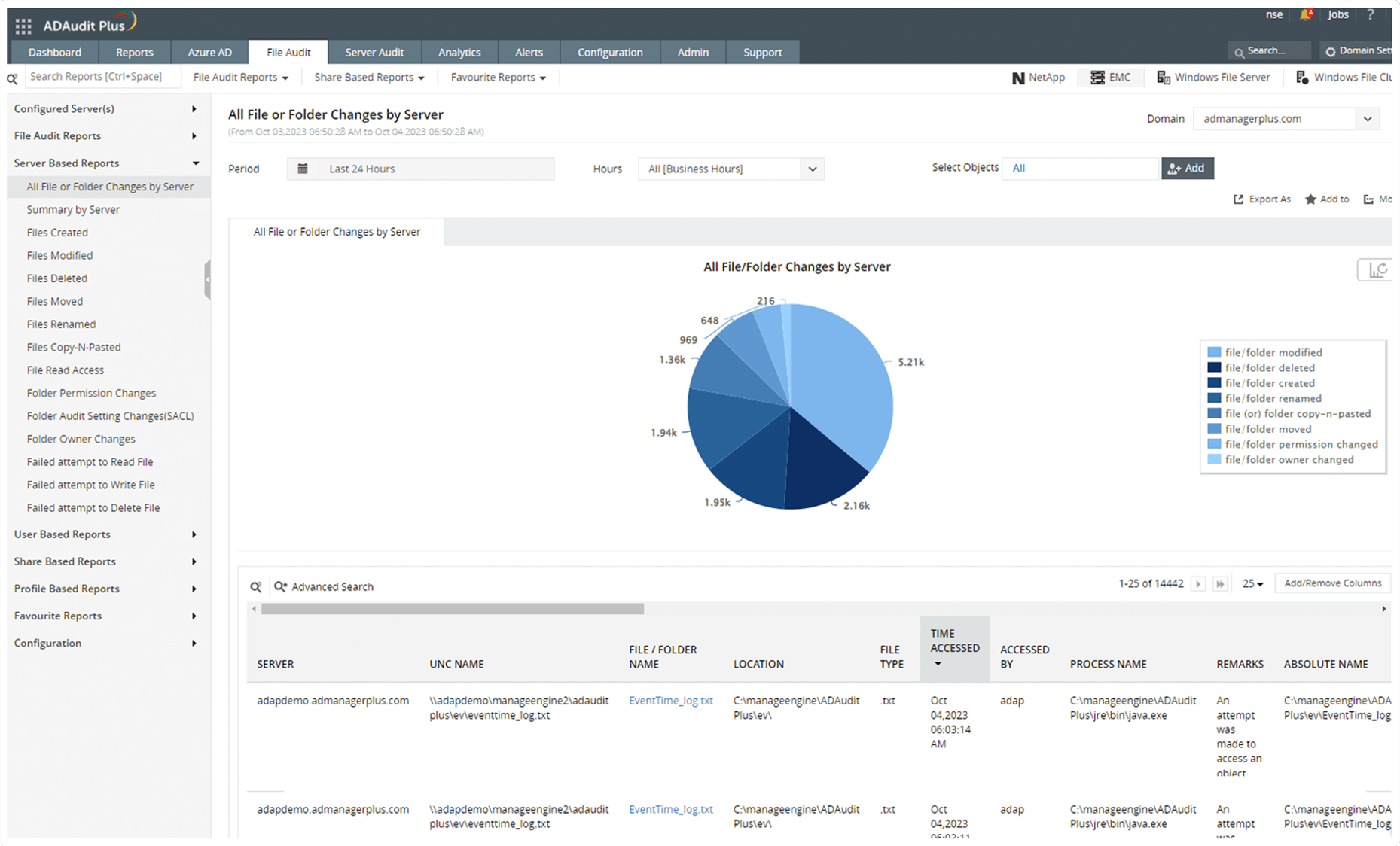
File change auditing:Track all file and folder changes in real time with detailed reports.
Failed file access attempt monitoring: Stay on top of failed attempts to read, write, or delete critical files.
Get an insightful overview of file changes in your domain across your hybrid storage environment.
Audit changes on not just Windows file servers and failover clusters but also NAS devices such as NetApp, EMC, Synology, Huawei, Hitachi, QNAP, and Amazon FSx systems.
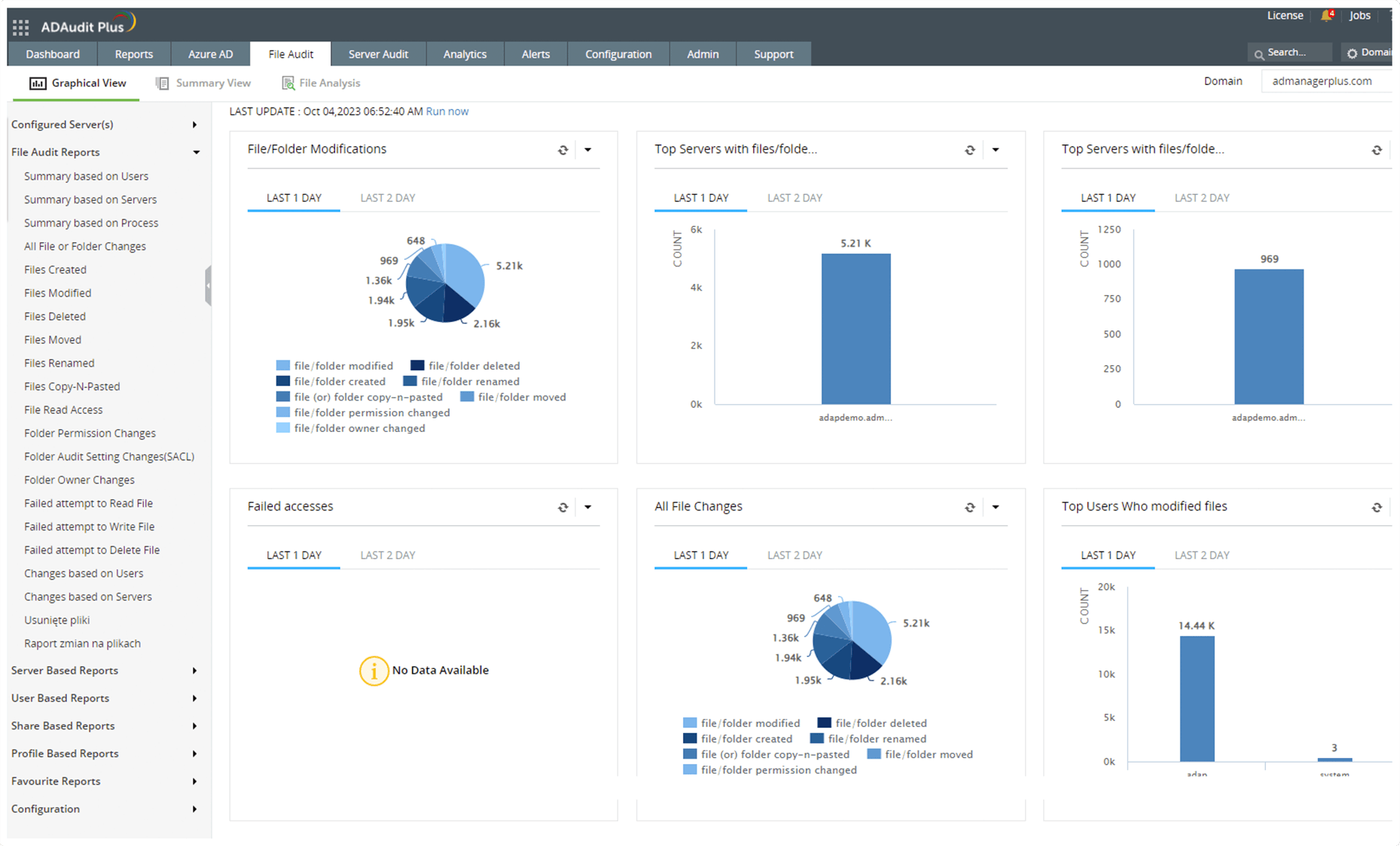
A bird's-eye view: Get an insightful overview of file changes in your domain across your hybrid storage environment.
NAS file auditing: Audit changes on not just Windows file servers and failover clusters but also NAS devices such as NetApp, EMC, Synology, Huawei, Hitachi, QNAP, and Amazon FSx systems.
Report on file and folder changes for regulations such as SOX, HIPAA, the PCI DSS, the GLBA, FISMA, the GDPR, and ISO/IEC 27001.
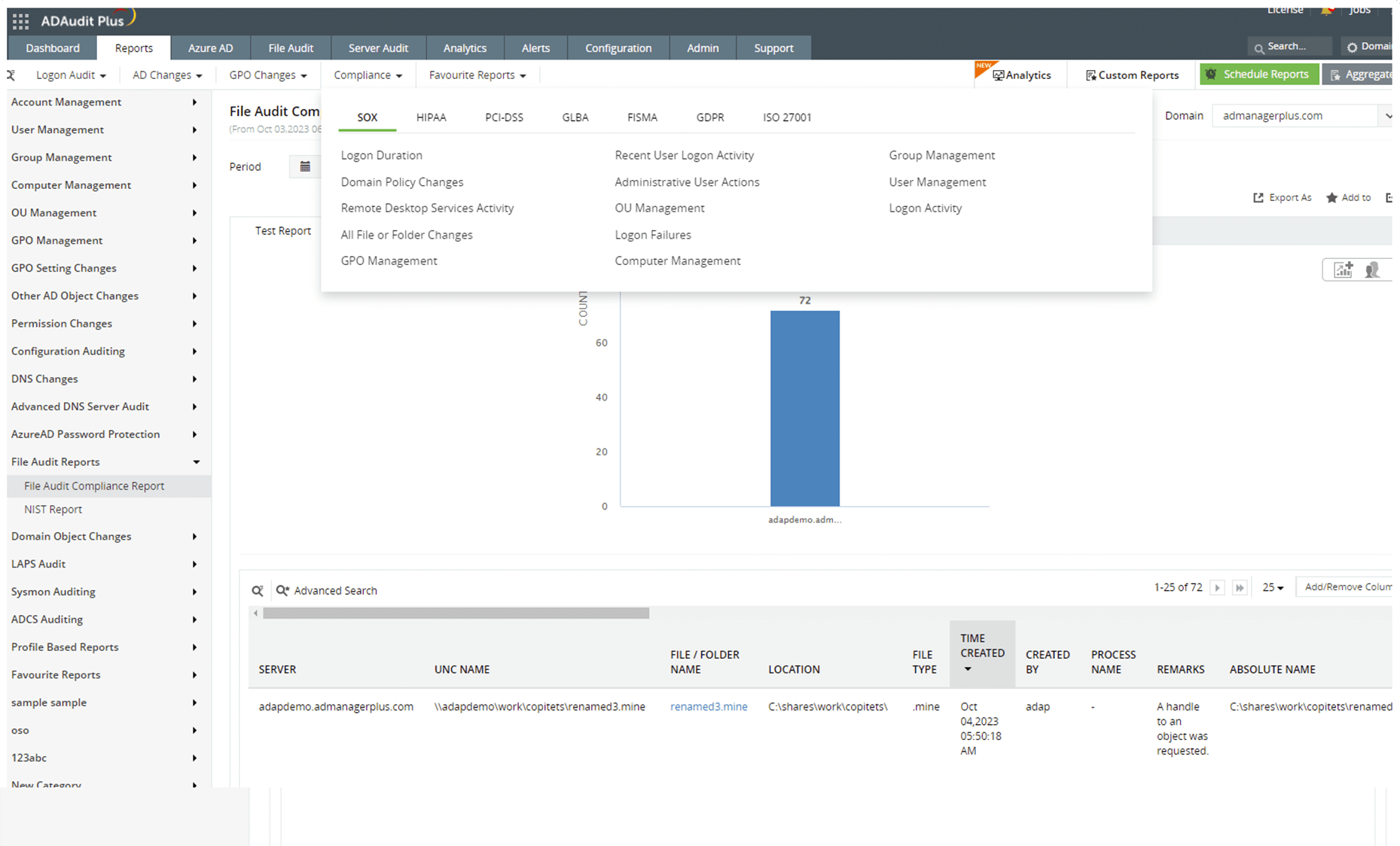
Built-in compliance reports: Report on file and folder changes for regulations such as SOX, HIPAA, the PCI DSS, the GLBA, FISMA, the GDPR, and ISO/IEC 27001.
Send instant alerts to designated security personnel or administrators when critical file or folder events are detected.
Create your own alerts for critical actions such as mass file deletions, which are unusual and must be investigated immediately.
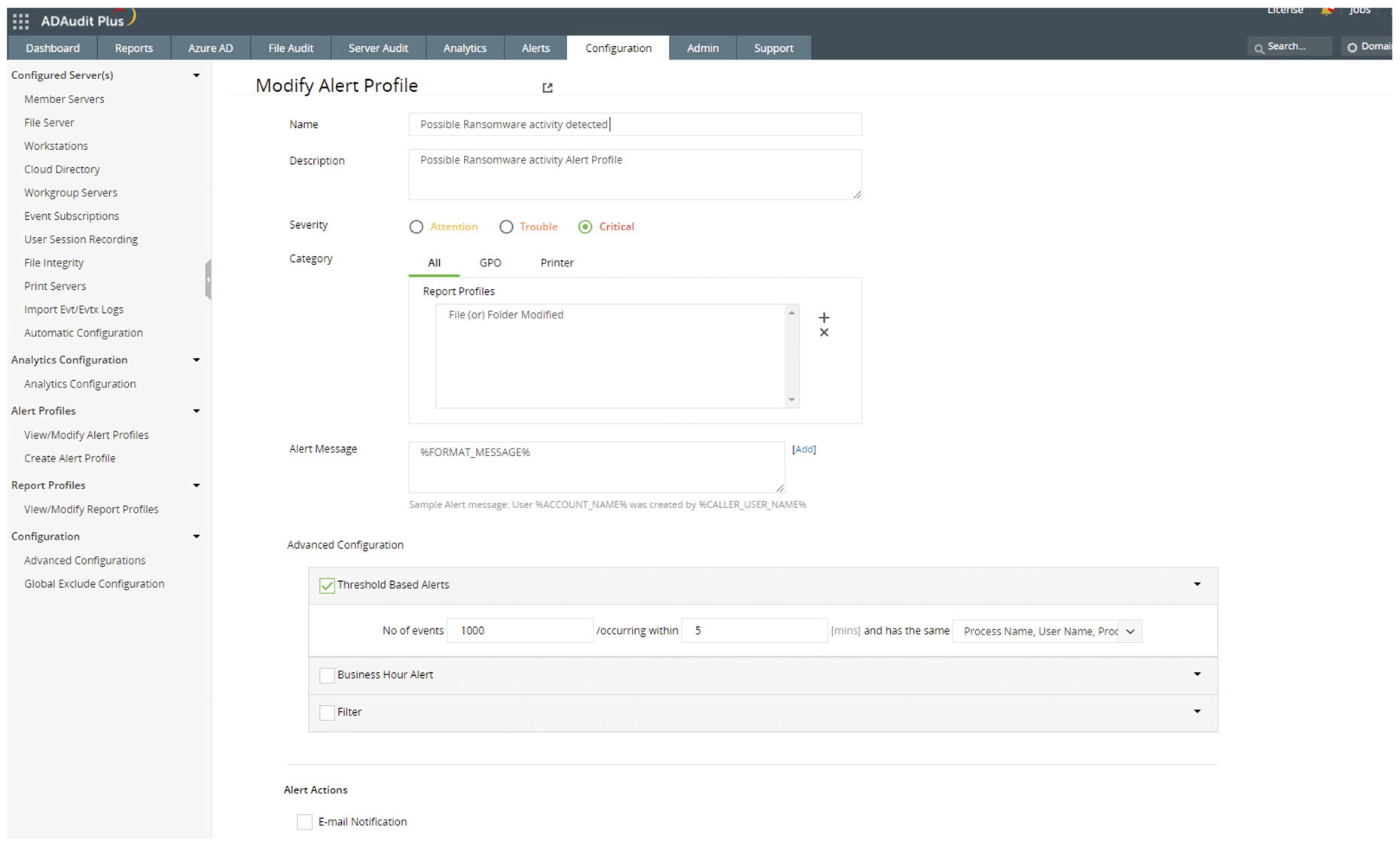
Email and SMS notifications: Send instant alerts to designated security personnel or administrators when critical file or folder events are detected.
Threshold-based alerts: Create your own alerts for critical actions such as mass file deletions, which are unusual and must be investigated immediately.
Mitigate attacks quickly with predefined alert responses, such as isolating servers and ending user sessions.
Integrate with popular service management platforms to ensure that security incidents are promptly documented, assigned, and tracked until resolution.
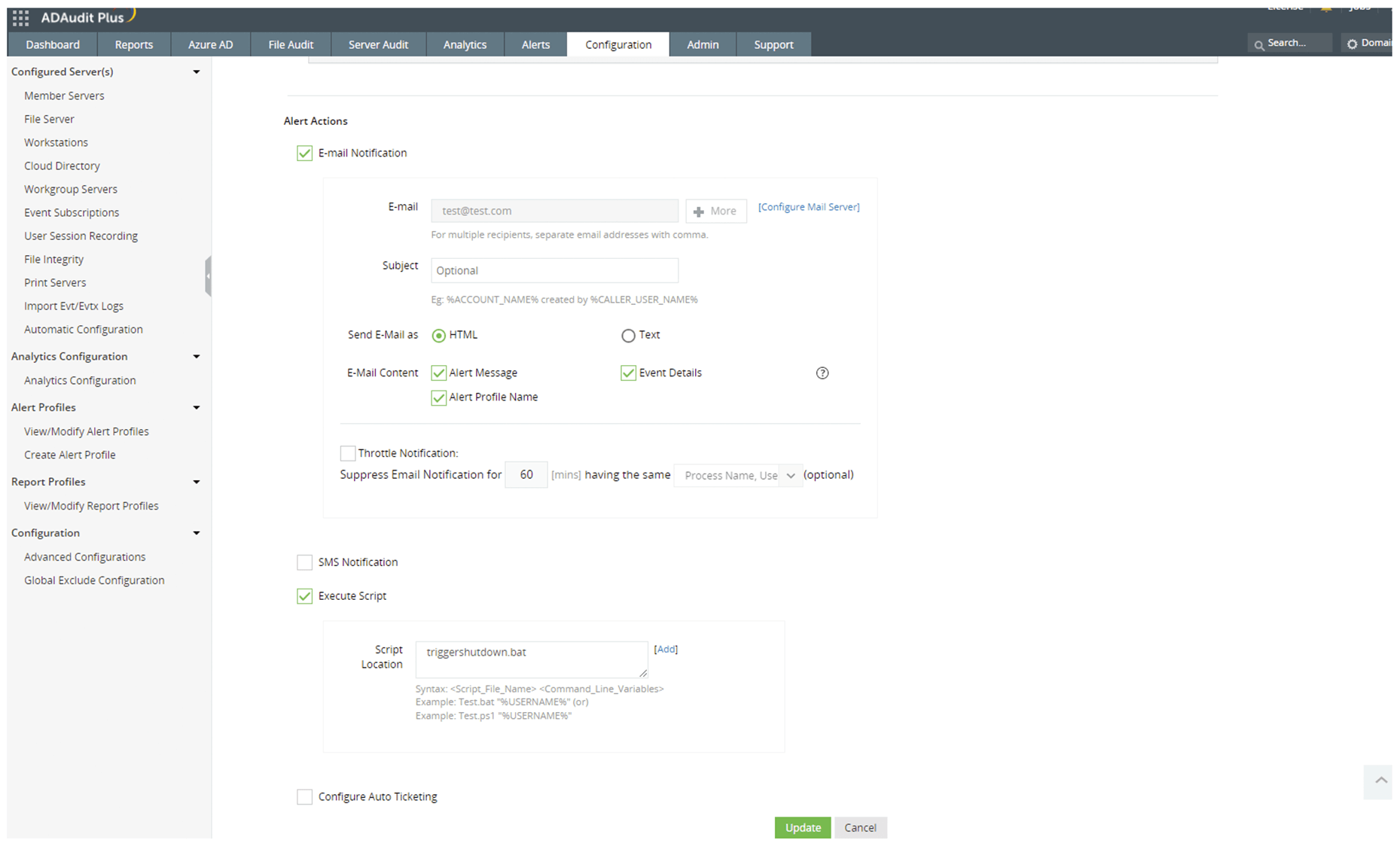
Automated security incident responses: Mitigate attacks quickly with predefined alert responses, such as isolating servers and ending user sessions.
Documented administration: Integrate with popular service management platforms to ensure that security incidents are promptly documented, assigned, and tracked until resolution.
Easily identify a dynamic baseline for normal activity in your files and folders with ADAudit Plus' UBA.
Detect deviations from the normal file activity baseline, such as spikes in file modifications or file actions at unusual times.
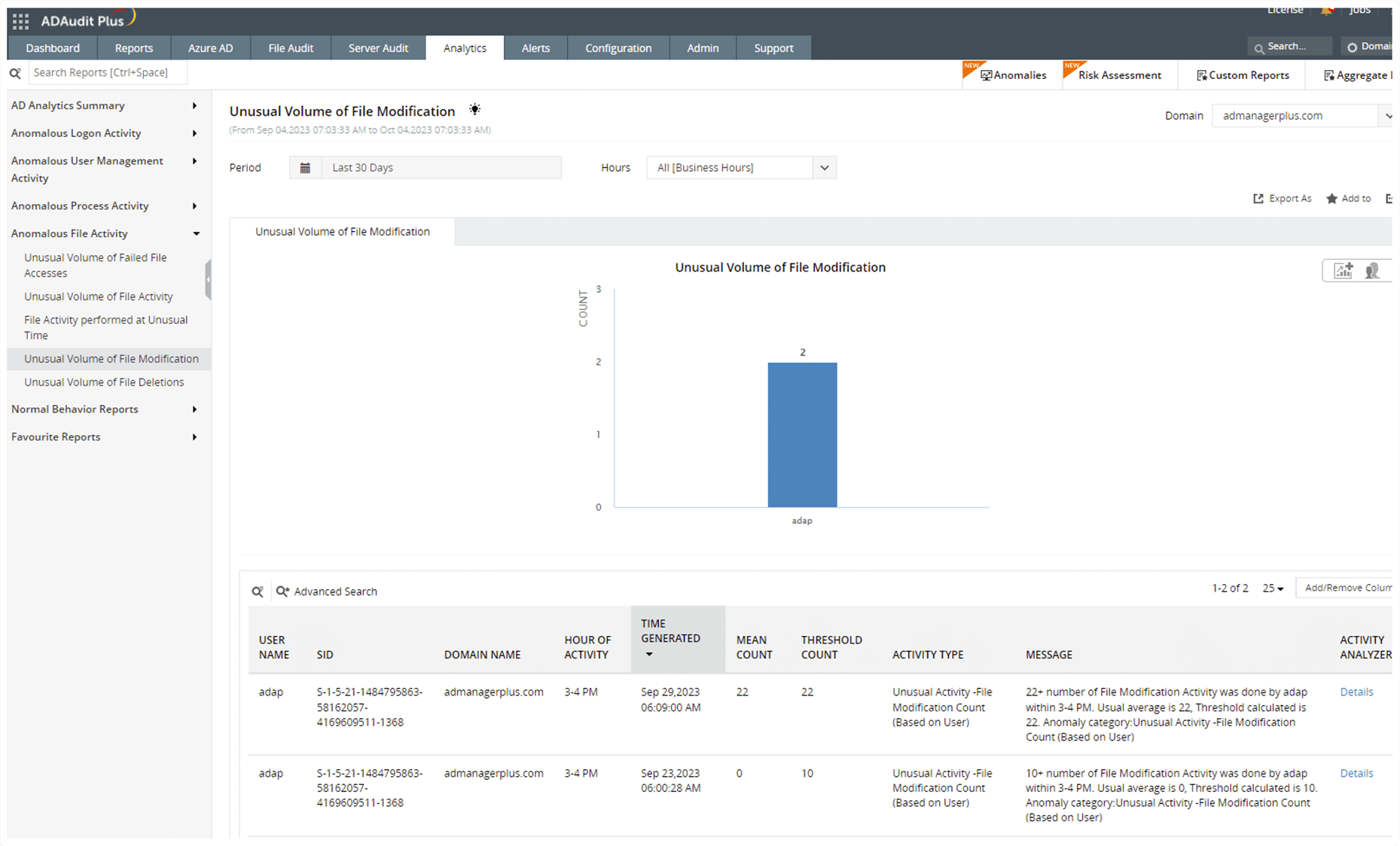
Dynamic baselining: Easily identify a dynamic baseline for normal activity in your files and folders with ADAudit Plus' UBA.
File activity anomaly detection: Detect deviations from the normal file activity baseline, such as spikes in file modifications or file actions at unusual times.
Thank you for your interest in ManageEngine ADAudit Plus. We have received your request for a price quote and will contact you shortly.
File server auditing plays a critical role in maintaining security and compliance in an IT environment. It helps organizations:
Most file servers include built-in audit policies that allow administrators to define which events, such as file reads, writes, or deletions, should be logged. Once these audit policies are configured, the system records the relevant events, which can then be centralized for monitoring.
For example, in Windows file servers, administrators must configure a set of advanced audit policies within a Group Policy Object (GPO). This GPO is then applied to all file servers that require auditing. Object-level auditing settings, also called System Access Control Lists (SACLs) must be configured for all files that require auditing. The logged events can be accessed via Windows Event Viewer and centralized using Windows Event Forwarding (WEF) for streamlined monitoring.
To strengthen file server security, organizations should follow these best practices:
While native file server auditing tools provide basic monitoring capabilities, they do have a few limitations:
An effective file auditor should offer:
Organizations can enhance security, improve compliance, and gain visibility into file activities by choosing a robust auditing tool with all these features like ADAudit Plus.
Review the datasheet to learn how ADAudit Plus helps audit AD changes, mitigate security threats, demonstrate compliance, and more.
Access the datasheetAccess in-depth reports that track every change made to your AD objects, including users, computers, groups, and GPOs.
Monitor and track all Azure Active Directory sign-ins and events across cloud and hybrid environments.
Track file changes across Windows, NetApp, EMC, Synology, Hitachi, Huawei, Amazon FSx for Windows, QNAP, and Azure file servers.
Gauge employee productivity by analyzing their clock-in and clock-out times, and maintain accurate timesheets to calculate billable hours.