BitLocker Encryption Pre-requisites
The successful deployment of BitLocker encryption depends on meeting specific system requirements and configurations. These conditions ensure that BitLocker can function optimally and provide the desired level of protection. BitLocker pre-requisites are criteria a computer must adhere to before deploying a BitLocker policy to initiate encryption. This article will delve into the essential criteria a computer must fulfill before implementing a BitLocker policy. Below are the various criteria:
- Operating System Compatibility
- BitLocker Availability
- TPM Ownership
- BIOS Mode Compatibility
- GPO Configuration
Operating System Compatibility
BitLocker encryption might not be available in all Windows versions used in your organization. Here's a list of Windows operating systems that support BitLocker:
- Windows 11 Pro, Enterprise, and Education editions
- Windows 10 Pro, Enterprise, and Education editions
- Windows 8.1 Pro and Enterprise editions
- Windows 8 Pro and Enterprise editions
- Windows 7 Ultimate and Enterprise editions
- Windows 7 Vista Ultimate and Enterprise editions
- Windows Server 2008 and above
BitLocker Availability
BitLocker is not automatically enabled on servers; however, you can manually enable it to start encryption. Below are common issues you might encounter when enabling BitLocker on a Windows Server machine.
BitLocker Status
BitLocker is disabled in Server OS computers by default. It can be enabled through the Server Manager and Command Prompt.
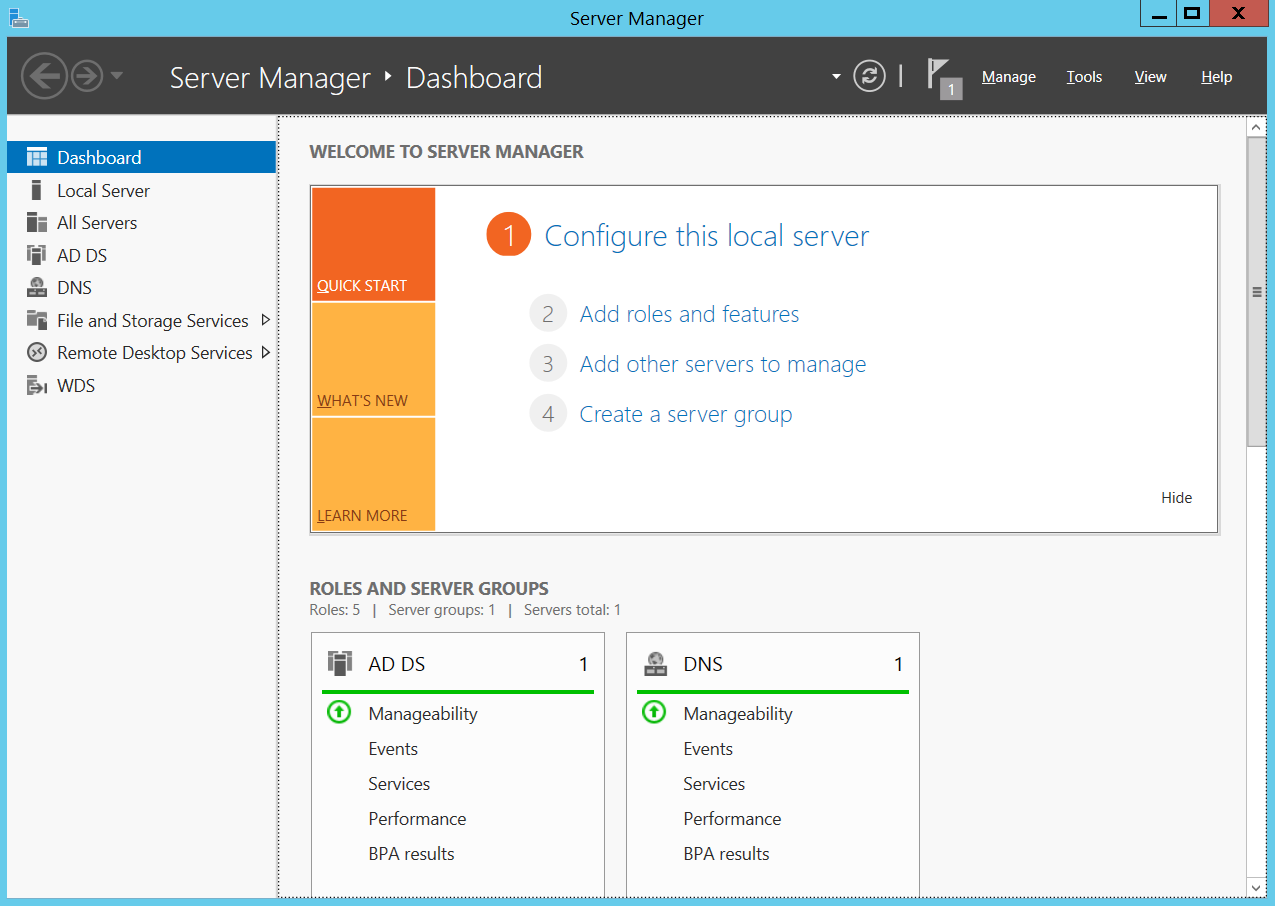
Through Server Manager
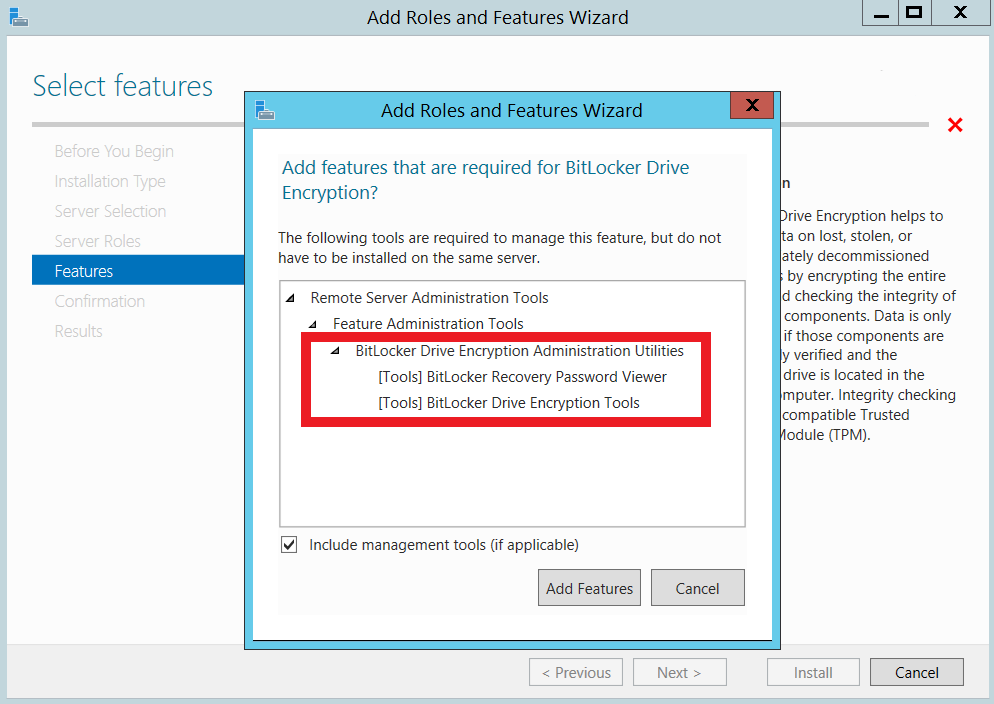
Perform these steps to enable the BitLocker feature through Server Manager and utilize the BitLocker Recovery Key storing feature:
- On the Windows taskbar, select Server Manager and choose Add Roles and Features to open the wizard.
- Follow the installation steps in the wizard. In the Features pane, select the BitLocker Drive Encryption Administration Utilities checkbox along with the associated checkboxes for BitLocker Drive Encryption Tools and BitLocker Recovery Password Viewer.
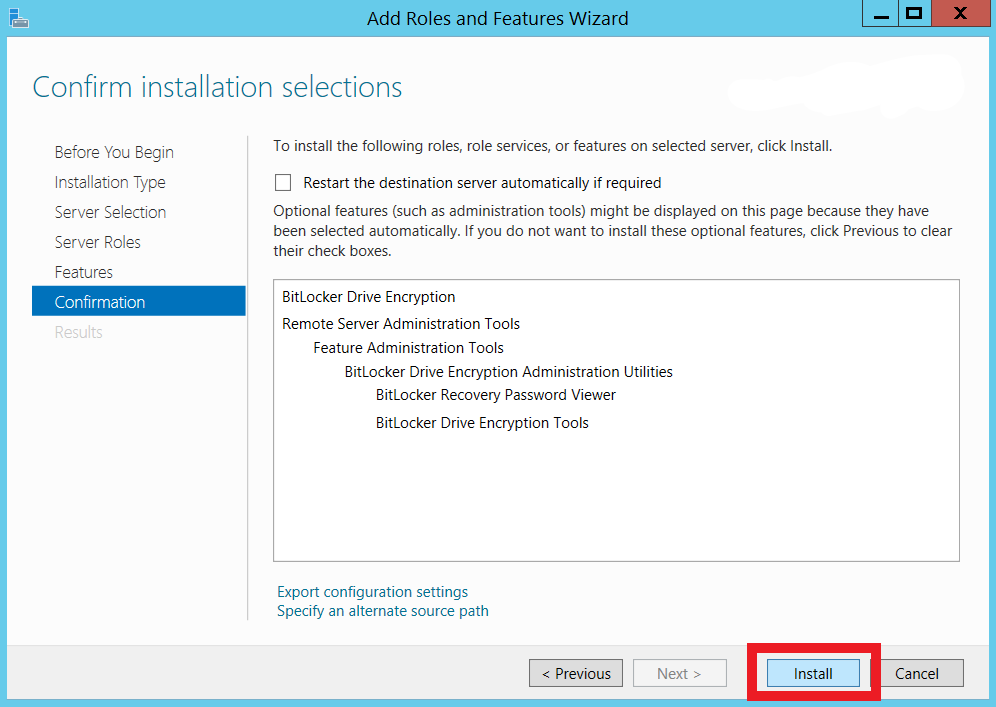
- Select Next to proceed in the installation wizard, then click Install on the Confirmation pane to start the BitLocker feature installation. Enabling BitLocker might require additional features, so follow the Confirmation pane to enable these features.
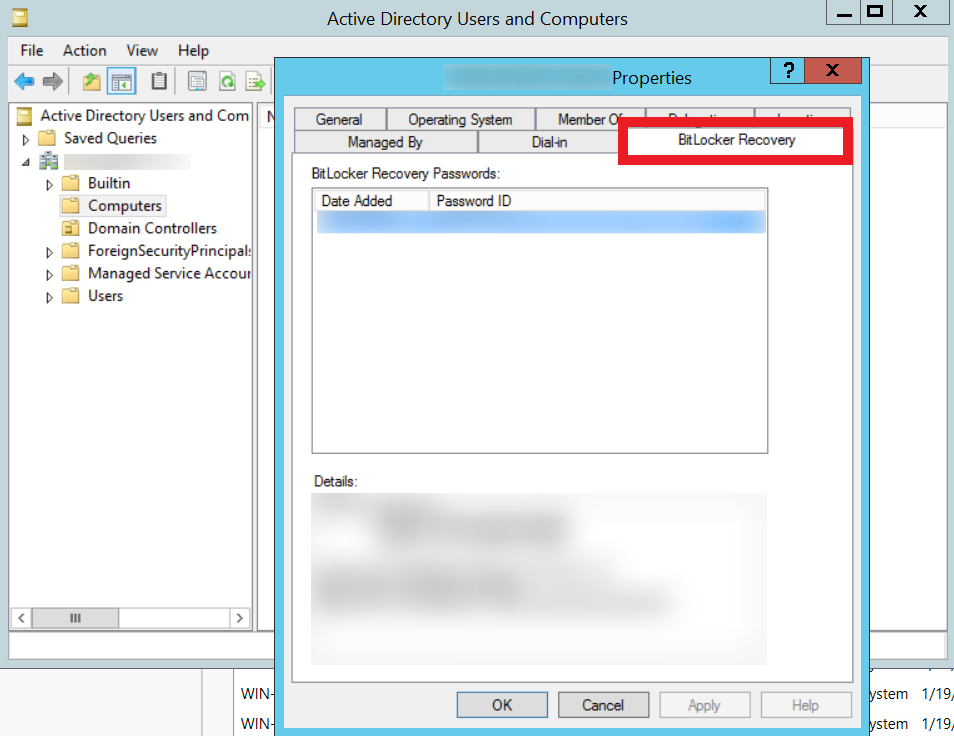
- Restart your computer to complete the BitLocker installation. To confirm installation, navigate to Active Directory Users and Computers; if the BitLocker Recovery tab is present, the installation is successful.
Through Command Prompt
Perform these steps to enable the BitLocker feature through the Command prompt:
- Open Command Prompt with Administrator rights and execute the following command.
dism /online /Enable-Feature /all /FeatureName:BitLocker /quiet /norestart - Restart your computer to complete the BitLocker installation process. To confirm the installation of the BitLocker feature, navigate to the Active Directory Users and Computers of computer objects; if the BitLocker Recovery tab is present, then installation has been successful.
WMI Functionality
Windows Management Instrumentation (WMI) is Microsoft's remote protocol for management tasks and information retrieval. To troubleshoot common errors while enabling BitLocker, perform the following steps:
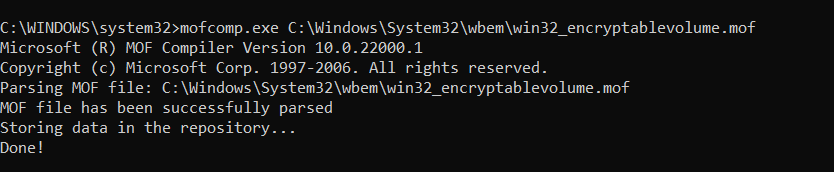
- Open the Command Prompt with Administrator rights and execute the command mofcomp.exe C:\Windows\System32\wbem\win32_encryptablevolume.mof
- If BitLocker WMI registration is successful, you will get the below notification.
TPM Ownership
The Trusted Platform Module (TPM) is a microchip that encrypts drives using cryptographic keys to mitigate dictionary attacks. If you have partial ownership of the TPM, BitLocker cannot use cryptographic keys; full ownership is required for TPM-based encryption.
To gain full ownership, clear the TPM as explained here. Clearing TPM will trigger the OS to automatically reinitialize and acquire full ownership.
NOTE - Clearing TPM can cause loss of stored cryptographic keys. Refer to this link for precautions before clearing TPM to safeguard your data.
BIOS Mode Compatibility
TPM-aided BitLocker encryption is supported only in Unified Extensible Firmware Interface (UEFI) mode. If you are using Legacy or Compatibility Support Mode (CSM), switch to UEFI mode to facilitate TPM-based encryption, as explained here.
GPO Configuration
Group Policy (GPO) settings can control Microsoft BitLocker's preliminary actions. Sometimes, the existing GPO settings of your computer can counteract
Endpoint Central's BitLocker policy. Remove all GPO configurations related to BitLocker and Encryption for seamless operation.
Details of BitLocker Group Policy Settings for your reference.
Now you can configure a BitLocker policy for successful encryption. Refer to this document for a detailed guide on creating and configuring BitLocker policies.
If you have any further questions, please refer to our Frequently Asked Questions section for more information.




