- Home
- What is log management
What is log management?
Log management is a systematic process that includes collecting, log parsing, analyzing, and storing extensive log data generated within an organization's digital ecosystem. Logs are a comprehensive record of diverse events, such as user actions, error messages, system events, security events, etc. This information is critical when it comes to root cause log analysis or enhancing the organization's security posture.
What is a log file?
Log files are records of everything that happens within a system. These files contain information on any action taken by a user and play an important role in an organization's security posture. They help monitor IT environments and track every event that's happening on the enterprise network. Log files are an essential part of the enterprise security software stack, helping analysts trace the attack flow in order to prevent further attacks at the early stages.
A log file generally comprises of three components:
- 1. Timestamp
- 2. User information
- 3. Event or action taken
Here is an example of what a log will look like:
<190>date=2021-05-01 time=12:21:00 logid=0100032001 type=event subtype=system level=information vd="root" user="admin" ui=http(192.168.1.112) action=login status=success reason=none profile="super_admin" msg="Administrator admin logged in successfully from http(192.168.1.112)"
In addition, a log file also contains other event-related information such as the username and time for logon events, source IP and destination IP for allowed traffic, and more.
Logs are generated by nearly every source in the network, including devices, routers, switches, firewalls, servers, endpoints, applications such as IIS, Apache, SQL databases, SaaS applications, different cloud environment platforms such as AWS EC2 instances, S3 audit trails, and more.
Get started with log management
The log management process typically contains the following steps:
- Log collection
- Centralized log storage
- Log parsing
- Log analysis
Log collection:
Logs are generated and stored locally in devices, systems, and applications. Therefore, the first stage of the log management process is to collect these logs from the source and store them centrally for further analysis. Log management tools adopt different mechanisms to aggregate and centralize log data. Here are a few examples:
Agent-based log collection is when a specialized software, known as an agent, is installed. The source collects the locally generated log data, and securely transmits it to the centralized server for further log analysis and reporting. An agent-based log collection mechanism is usually adopted when there's a restriction (such as devices residing in demilitarized zones) in sending log data over the network to the centralized server.
Agentless log collection is when the logs are sent from the source to the centralized server. Agentless log collection is easier to configure and adopt, as the sources will take care of forwarding the log data without any additional agents involved. However, administrators must ensure that the log data gets transmitted to the central server or log management tool securely by adopting appropriate protocols.
API-based log collection is when APIs are utilized to collect log data. These APIs are configured to extract structured data from different systems. The types of log data that can be extracted via APIs include audit logs, transaction logs, configuration change logs, etc. This log data is then transmitted securely, often in a standardized format, to a central repository or a log management tool where it can be stored, analyzed, and monitored. API-based log collection is often used for cloud services and platforms, as traditional log collection methods aren't always effective. It is also utilized for custom application logging, or in dynamic environments where the infrastructure frequently changes. However, the granularity and format of the data accessible through APIs might also be limited, offering only what the API is designed to expose. This can result in a lack of detailed information or necessitate additional processing to align the data with the requirements of the log management system. This type of log collection is also more complex to set up since it requires custom integration and is more resource intensive.
Centralized log storage
The collected log data is stored centrally in a server or in the log management tool. In case of using a log management tool for storage, the tool stores the raw log data for a certain period, then archives it for future forensic log analysis. These tools also provide an option to retrieve a specific set of log data at any time for log analysis. Often, these tools come with a customization option to specify the period after which the raw log data can be archived.
Log Parsing:
This technique involves normalizing the unstructured log data and converting it into a common format for easy log analysis. Log management tools often come with built-in parsers to automatically extract fields from the log data for reporting, alerting, and log analysis. Also, they might include custom log parsers that can automatically generate regex patterns to parse and normalize the unsupported log formats. With this, the users get to extract common fields such as IP address, user name, time, destination host, etc., as soon as the log data is ingested, and then generate regex patterns to identify other fields of importance.
Log analysis:
Log management tools adopt and present the findings of log analysis in different formats. The log analysis process helps visually display the log data and offer actionable insights. Log management tools adopt different ways of presenting this information. They offer intuitive reports, dashboards, and real-time alerts to notify the administrators about the critical events. Further, they also come with a built-in correlation engine that offers better visibility on the events happening within the network.
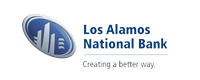
Log correlation: It is a crucial part of the log analysis process where information across different logs are stitched together to detect threat patterns, suspicious events, and other events of importance. Log correlation helps in getting complete visibility into related activities happening across different sources within the network.
Log reporting: Once the data is analyzed and provided, you can generate reports to deliver insight into any anomalies, or possible security events within the network. You can also generate reports during security audits to show compliance with industry regulations.
- What are the features of a log management tool
- How does log management help enterprises?
- Best practices to effectively manage logs
What are the features of a log management tool:
A log management tool is preferred by organizations as it automates the log management processes and provides log analysis. Here's what to look for in your log management tool:
Log correlation: Look for a tool that provides built-in correlation rules to detect known threats and attacks. Correlation is a resource intensive process, so make sure to check the performance parameters of the correlation engine. Also, the options to build custom correlation rules and how easy it can be created should be noted while selecting a log management tool.
Here's how you can detect security attacks with log correlation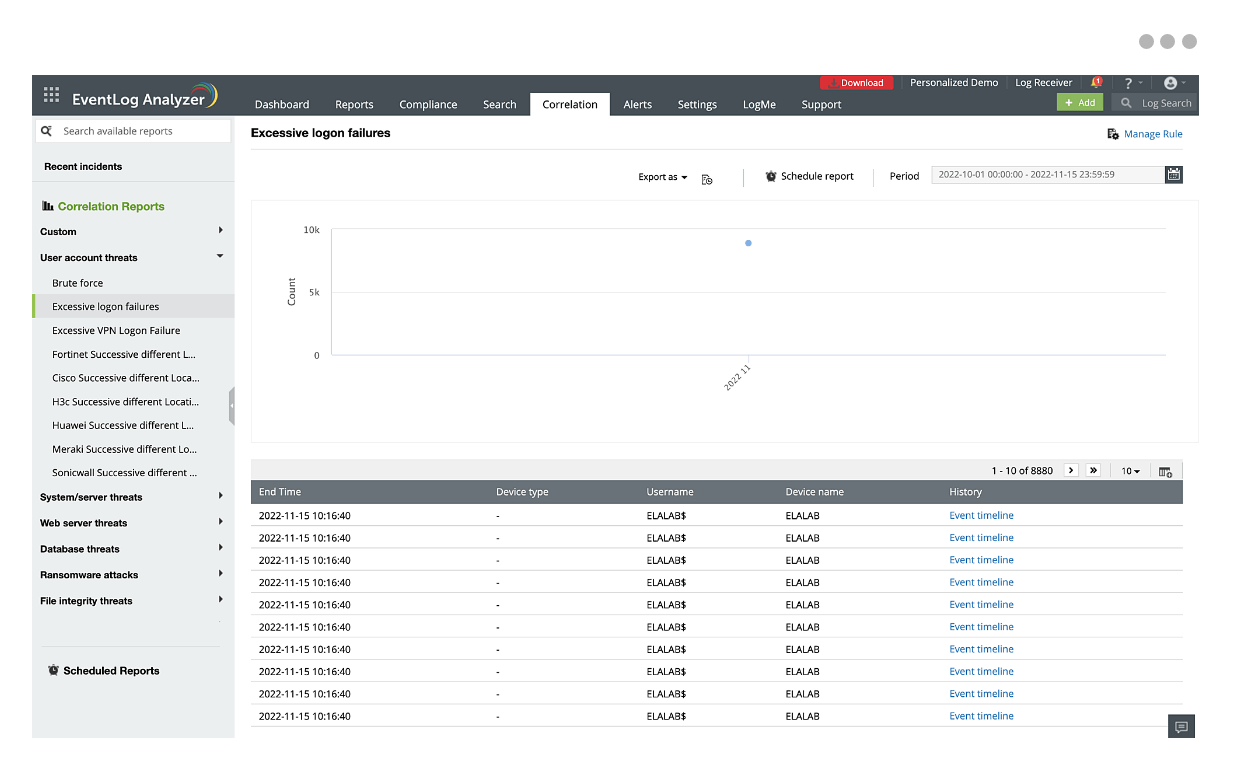
Log search: Log search is a feature in log management tools that helps swiftly and efficiently navigate through extensive volumes of log data to retrieve specific information. However, finding the threat in a haystack of log data can be difficult. Look for a log management solution that can use your search query and convert them into alert profiles so that you can get notified in real-time. EventLog Analyzer takes this one step further with the ability to build and group search queries, and processes log data at a speed of 25,000 logs per second.This will enable a quicker response to threats.
Learn how to use log search effectivelyReal-time event monitoring: Real-time event monitoring helps in the immediate detection of errors or threats as they occur. A log management tool automatically monitors and analyzes all the events that occur within the network in real-time and helps you visualize this data for easy log analysis and swift incident detection. Look for a solution that comes with predefined reports and allows you to set up custom alerts so that you are notified of suspicious events instantly.
Learn more about event monitoring
Instant alerts and notifications: A log management tool can provide instant alerts when a particular attack flow or any anomalous activity is detected. This would help you take immediate remedial action through automated incident workflows and helps speed up your incident response. When it comes to choosing a log management tool, look for a solution that allows you to categorize the alerts based on their priority for effective incident management.
Learn more about log alerting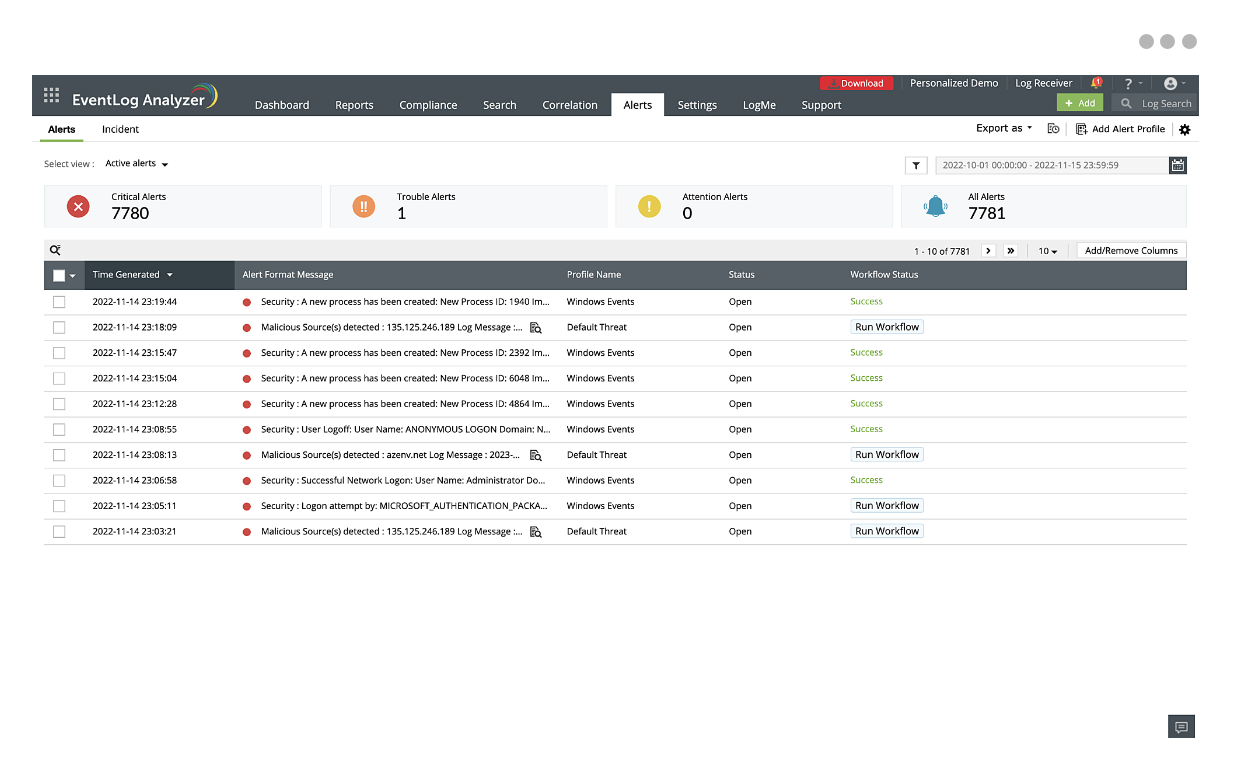
Log retention and archival: A log management tool helps in setting policies for log retention, and archiving older logs to optimize storage while also ensuring the accessibility of the logs. The log archival period may differ based on your industry requirements. When considering a log management tool, look for a solution that helps you customize the log archival process to suit your organization's needs.
Learn more about log archiving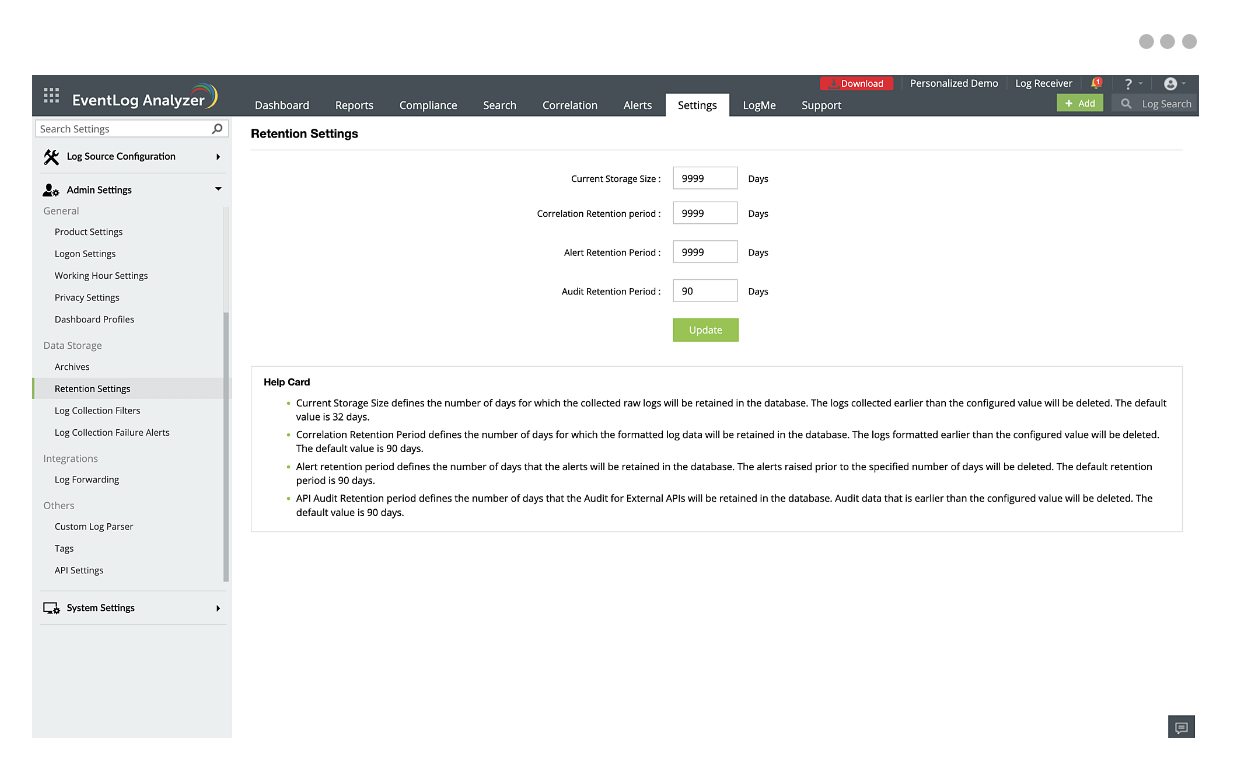
Compliance support: With a log management tool, you can maintain an audit trail and generate reports to stay compliant with regulations such as GDPR, HIPAA, FISMA, etc. In addition to these, you need a tool that will help comply with the new regulations. Look for a log management solution that can help you create new compliance reports that match the requirements of the new mandate so that you can always stay compliant.
Here's how you can stay compliant using a log management solution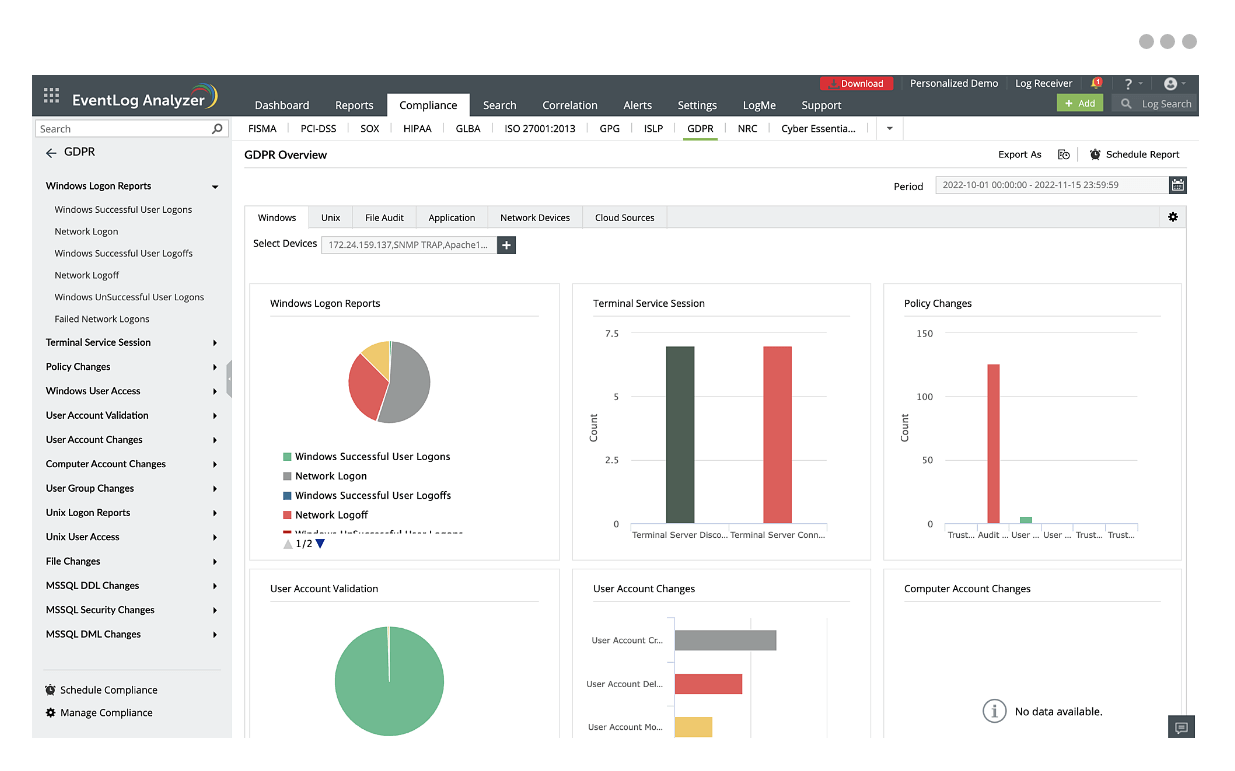
How does log management help enterprises?
A comprehensive log management tool offers various benefits to enterprises from troubleshooting IT issues, to ensuring security, to meeting compliance needs. Here are some of the benefits of deploying a log management tool:
Visibility
Logs can provide insights into threats and anomalous behavior. A log management tool automatically collects and analyzes these logs in real-time to give you an understanding of what is happening within your environment. This information is presented with a dashboard, which makes it easier to understand the data and spot trends or issues at a glance.
Security
Effective log management is imperative to ensure your organization's security. Log management tools can correlate logs from different sources to identify unusual patterns or behaviors that may indicate a security incident like a breach or attack. After an incident, log management tools are also instrumental in conducting forensic log analysis through log searches to understand the incident's nature, scope, and impact.
Compliance and auditing
Organizations are required to archive logs in a secure, tamper-evident environment, ensuring data integrity and availability, which a log management tool can help with. The solution assures that logs are readily available for review, ensuring transparency, accountability, and adherence to compliance standards. This mitigates the risks associated with non-compliance, including financial penalties and reputational damage.
Troubleshooting
When issues arise, log management tools enable rapid troubleshooting by allowing teams to access relevant log data quickly, understand the context of the problem, and diagnose the root cause by providing detailed historical data.
Performance log analysis and optimization
Log monitoring and log analysis can provide you with insights into the functionality of applications and devices using system logs and performance metrics such as response times. They also help you identify any factors that are affecting system performance, such as high CPU usage, network connectivity issues, or security threats, which can diminish the user experience.
Best practices to effectively manage logs
There are countless number of logs generated at any given moment. Managing and analyzing all these logs manually is impossible for one IT professional. Here are some log management best practices that can help organize and analyze these logs effectively.
Centralized log management
A centralized log management console is a cornerstone for enhancing the security and efficiency of an organization's IT infrastructure. By bringing diverse data into one platform, it facilitates advanced analytics. Furthermore, it reduces the workload on individual systems and enhances the efficiency of security personnel.
Log retention policies
It's essential to implement a log retention policy to manage costs and resources efficiently. Certain logs, like security logs, should be retained for longer than firewall and auditing logs as they contain necessary information in the event of an attack or breach. You need to have a log retention strategy that allows you to retain the logs required by your industry regulations.
Integration with a SIEM
Integrating a log management tool with a SIEM solution gives you enhanced security with additional features such as attack detection and User Entity Behavior Analytics (UEBA).