- Home
- Play books
- Cisco Duo – Authentication downgrade attempt detection and response
Cisco Duo – Authentication downgrade attempt detection and response
In this page
Playbook Description
This playbook investigates authentication downgrade attempts by analyzing user behavior, checking for attempts to bypass multi-factor authentication, and evaluating the risk associated with such attempts.
MITRE ATT&CK mapping
| Tactics | Techniques | Sub-techniques |
|---|---|---|
| Defense Evasion(TA0005) | System Binary Proxy Execution(T1218) | InstallUtil(T1218.004) |
MITRE D3FEND mapping
| Tactics | Techniques | Sub-techniques |
|---|---|---|
| Model(D3-Model) | Application Hardening(D3-AH) | Process Segment Execution Prevention(D3-PSEP) |
Playbook input type
Alert
Prerequisites
- VirusTotal connection - Need to connect with VirusTotal API to check URL and file hash reputation.
Playbook creation input
- connectionName - Provide the VirusTotal connection name for executing the VirusTotal APIs
Dependencies
Extensions - VirusTotal
- virustotal_ipReputation
- ciscoduo_createPolicy
- ciscoduo_retrieveEndpointById
- ciscoduo_modifyUser
- ciscoduo_retrieveUserById
- ciscoduo_retrievePolicies
Extensions - Cisco Duo
- ciscoduo_createPolicy
- ciscoduo_retrieveEndpointById
- ciscoduo_modifyUser
- ciscoduo_retrieveUserById
- ciscoduo_retrievePolicies
Utility functions:
- utility_analyseDeviceHealthResult
- utility_filterAndMatchEvents
- utility_convertTimeToUTC
- utility_sendMail
Connections
VirusTotal connection - Need to connect with VirusTotal API and fetch access key to check the malware IP/URL/File details.
Cisco Duo connection - Need to connect Cisco Duo using Integration Key, Secret Key and API Hostname.
Sub playbooks
- Cisco Duo - Block IP
- Cisco Duo - Add user to group
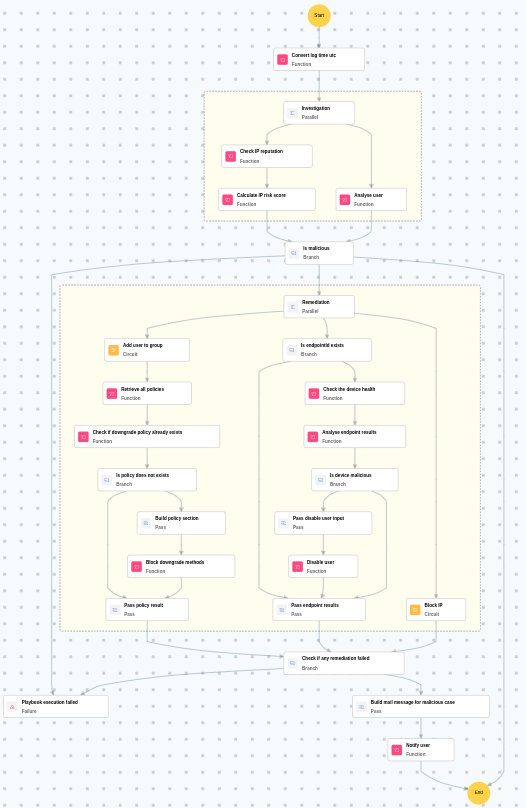
Execution workflow
Investigation:
- Checks the IP reputation.
- Calculates the IP risk score.
- Analyzes the user.
Decision logic:
- Proceeds to remediation based on the following conditions:
- The associated IP address has a high-risk score.
- If no malicious indicators are confirmed, the playbook ends with no further actions.
Remediation:
- Executes the "Cisco Duo - Add user to group" sub-playbook.
- Retrieves all policies.
- Checks if downgrade policy already exists.
- Checks whether policy does not exists.
- Passes policy result.
- Checks whether endpoint ID exists.
- Passes endpoint results.
- Executes the "Cisco Duo - Block IP" sub-playbook.
- Checks if any remediation failed.
- Builds the notification email with remediation details and findings.
- Sends a notification email regarding the actions taken and required next steps.
Post execution procedure
- Review the blocked IP address to ensure no legitimate traffic was affected.
- Investigate whether the attacker successfully downgraded the authentication before remediation.
- Review Cisco Duo authentication logs for any additional downgrade attempts across the organization.
- Consider enforcing stricter authentication policies to prevent future downgrade attacks.
- Audit all user accounts in Cisco Duo for similar authentication anomalies.


