- Home
- Play books
- Okta - Block IP or ASN
Okta - Block IP or ASN
In this page
Playbook Description
This playbook blocks malicious IP addresses or AS numbers in Okta. It triggers a response workflow that automatically applies active sign-on policies to enforce access denial across the network for the specific IP address.
MITRE D3FEND mapping
| Tactics | Techniques | Sub-techniques |
|---|---|---|
| Isolate (D3 - Isolate) | D3 - NI | Network Traffic Filtering (D3 - NTF) |
Playbook input type
Log
Prerequisites
API access with below scopes:
- okta.networkZones.read
- okta.networkZones.manage
- okta.policies.manage
Playbook creation input
- ipZoneName - Name of the IP network zone.
- asnZoneName - Name of the ASN network zone.
- pPolicyName - Name of the policy applied to the IP network zone.
- asnPolicyName - Name of the policy applied to the ASN network zone.
- ipPolicyRuleName - Name of the rule that enforces conditions within the IP policy.
- asnPolicyRuleName - Name of the rule that enforces conditions within the ASN policy.
Dependencies
Extensions - Okta
- okta_listNetworkZones
- okta_createNetworkZone
- okta_createPolicy
- okta_createPolicyRule
- okta_updateNetworkZone
Utility functions
- okta_buildNetworkZoneInfo
Connections
- Okta connection - Need to connect Okta using API Key.
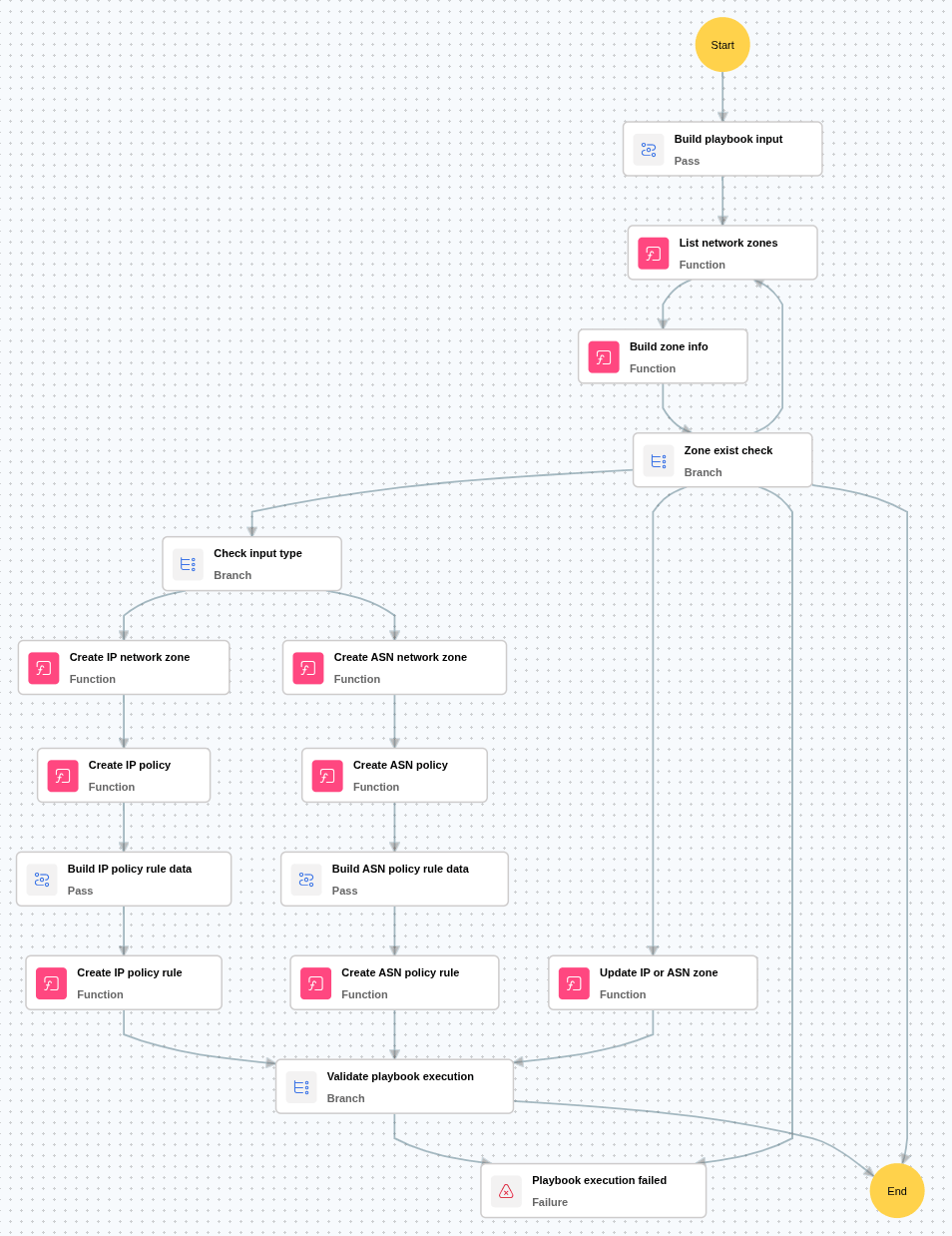
Execution workflow
- Lists existing network zones to verify whether the provided zone already exists.
- Builds the data required to create or update a network zone based on the input type (IP address or AS number).
- Creates a new network zone when the target zone is not found and adds the identified malicious IP addresses or AS numbers.
- Creates an policy and associates the newly created network zone.
- Creates a policy rule that applies sign-on access denial for the network zone.
- Updates the existing network zone when it already exists by adding the IP or AS number detail