- Home
- Play books
- CrowdStrike - Concurrent user login containment
CrowdStrike - Concurrent user login containment
In this page
Playbook Description
This playbook detects concurrent logins on the same user account, analyzes login patterns and IP reputation, and if deemed malicious, it revokes sessions, enforces password reset, and blocks the source IP to prevent further unauthorized access.
MITRE ATT&CK mapping
| Tactics | Techniques | Sub-techniques |
|---|---|---|
| Credential Access(TA0006) | Brute Force(T1110) | Password Spraying(T1110.003) |
MITRE D3FEND mapping
| Tactics | Techniques | Sub-techniques |
|---|---|---|
| Evict(D3-Evict) | Credential Eviction(D3-CE) | Account Locking(D3-AL) |
Playbook input type
Alert
Prerequisites
- VirusTotal API - Need to connect with VirusTotal API and fetch access key to check the malware IP details.
- CrowdStrike configuration - Need to connect CrowdStrike using OAuth 2.0 connection with clientId and clientSecret, Authorize URL, Access Token URL, Refresh Token URL.
Playbook creation input
- connectionName - Provide the VirusTotal connection name for executing the VirusTotal APIs
Dependencies
Extensions - CrowdStrike
- crowdstrike_retrieveUserUuid
- crowdstrike_resetUserPassword
- crowdstrike_getUserRoleId
- crowdstrike_revokeUserRole
- virustotal_ipReputation
- virustotal_calculateRiskScore
Extensions - VirusTotal
- virustotal_ipReputation
- virustotal_calculateRiskScore
Utility functions:
- utility_getRequiredTime
- utility_extractFieldFromList
- utility_extractMaliciousEntitiesByRiskScore
- utility_convertToString
- utility_sendMail
Connections
CrowdStrike connection - OAuth2 connection with clientId and client secret along with region.
VirusTotal connection - Need to connect with VirusTotal API and fetch access key to check the malware IP/URL/File details.
Sub playbooks
- CrowdStrike Falcon - Block IP
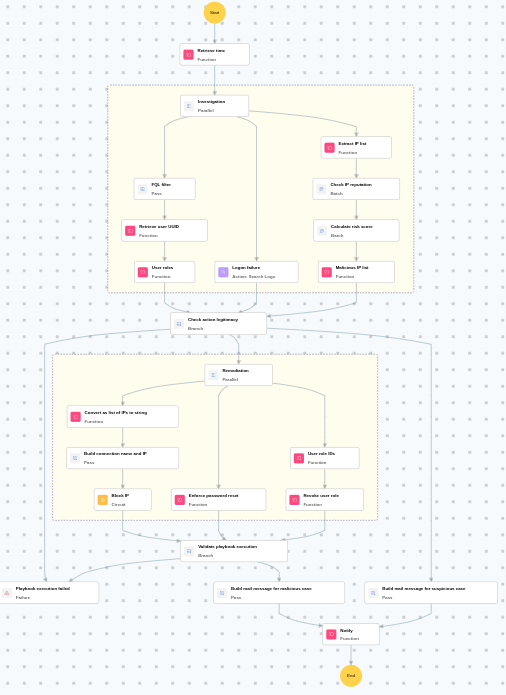
Execution workflow
Investigation:
- Retrieves the user UUID.
- Retrieves user roles.
- Retrieves logon failures.
- Extracts the IP list.
- Checks the IP reputation in batch.
- Calculates the risk score in batch.
- Identifies malicious entities based on their risk scores.
Decision logic:
- Proceeds to remediation based on the following conditions:
- Multiple logon failures were detected within the investigation period.
- If suspicious but not confirmed malicious, sends a notification for manual review and stops further actions.
- If no malicious indicators are confirmed, the playbook ends with no further actions.
Remediation:
- Executes the "CrowdStrike Falcon - Block IP" sub-playbook.
- Enforces the password reset.
- Fetches user role IDs.
- Revokes the user role.
- Validates if all remediation actions are completed successfully.
- Builds the notification email with remediation details and findings.
- Sends a notification email regarding the actions taken and required next steps.
Post execution procedure
- Review blocked IP addresses to ensure no legitimate traffic was affected.
- Investigate whether the compromised account was used to access sensitive resources.
- Audit other accounts for similar concurrent login patterns.


