- Home
- Play books
- Windows Defender quick scan
Windows Defender quick scan
In this page
Playbook Description
This playbook triggers an immediate scan on a target endpoint to identify active threats. This automation enables security teams to rapidly assess device health and accelerate incident response. By isolating malicious artifacts in real-time, the playbook ensures a proactive defense posture and minimizes the window of opportunity for potential attackers.
MITRE D3FEND mapping
| Tactics | Techniques | Sub-techniques |
|---|---|---|
| (Detect) D3-Detect | (File Analysis) D3-FA |
Playbook input type
Log
Prerequisites
- Microsoft defender should be enabled.
- Windows Credentials - Go to Settings -> Devices -> Windows Devices. Provide/update the credentials of the respective Windows device with admin privileges.
Dependencies
Utility-Functions:
- utility_dateTimetoFilter
Scripts
| Script Name | Description | Arguments |
|---|---|---|
| StartDefenderScan.ps1 | Starts a Microsoft Defender Quick Scan as a background job and returns the scan start time | - |
| MonitorsForScanCompletion.ps1 | Polls Windows Defender Operational event log (Event ID 1001) to detect when a scan completes after a given start time | ScanStartTime |
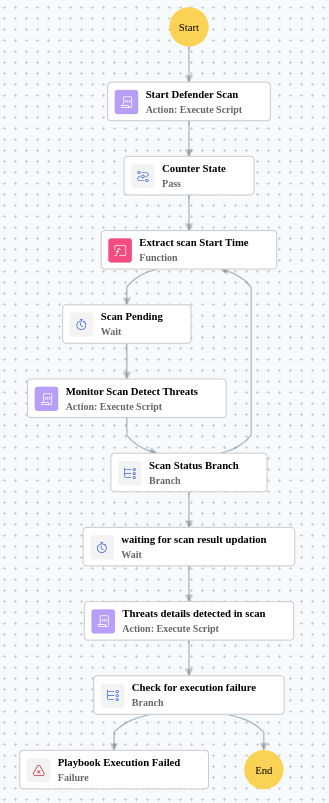
Execution workflow
- Starts Defender offline scan on target host.
- Initializes scan time counter.
- Extracts scan start time.
- Waits for scan to begin.
- Monitors scan and detects threats.
- If no threats found and max time not exceeded, retries the scan.
- Waits for results.
- Retrieves threat details.
Post execution procedure
Review the Windows Defender quick scan report.
Manually delete or move any confirmed malicious files if not automatically handled.


