- Free Edition
- Quick Links
- Active Directory Auditing
- Active Directory auditor
- Active Directory monitoring
- Account lockout analyzer
- Login monitoring software
- Active Directory change notifier
- User logon audit reports
- AD logon logoff tracker
- User logon failure auditing
- Login history tracking tool
- AD change auditor
- Insider threat detection software
- Permissions change auditing
- Entra ID reporting
- Privileged user monitoring
- User behavior analytics tool
- Active Directory security monitoring
- Group Policy auditing tool
- GPO change auditor
- Entra ID auditing
- Audit user account management
- OU change auditor
- Audit group membership changes
- Active Directory auditing and reporting tool
- GPO reporting tool
- Remote desktop monitoring software
- PowerShell logging and auditing
- Azure password protection auditing
- Azure sign-in risk detection
- File Server Auditing
- Windows Server Auditing
- Employee Tracking
- Workstations Auditing
- Compliance Auditing
- Other features
- SIEM Integration
- Windows DNS - Schema Auditing
- Windows security event log monitoring
- SIEM audit solution
- Schedule Active Directory change reports
- Reports from Archived Data
- Aggregated summary reports
- AD new/old attribute changes
- Audit trail
- Audit Active Directory LAPS
- Scheduled Reports & Alerts
- Account lockout examiner
- Industry
- Documents
- Success Stories
- Related Products
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- ADManager Plus Active Directory Management & Reporting
- EventLog Analyzer Real-time Log Analysis & Reporting
- ADSelfService Plus Identity security with MFA, SSO, and SSPR
- DataSecurity Plus File server auditing & data discovery
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- AD Free Tools Active Directory FREE Tools
Windows event ID 4740 - A user account was locked out.
Introduction
Windows lets you set an account lockout threshold to define the number of times a user can attempt to log on with an invalid password before their account is locked. You can also define the amount of time an account stays locked out with the account lockout duration setting. These account lockout policies help defend your network against password guessing attempts and potential brute-force attacks. However, strict policies could mean that users have fewer attempts to recall passwords, leading them to get locked out of their accounts more often.
Windows generates two types of events related to account lockouts. Event ID 4740 is generated on domain controllers, Windows servers, and workstations every time an account gets locked out. Event ID 4767 is generated every time an account is unlocked. In this guide, we're going to focus on event ID 4740.
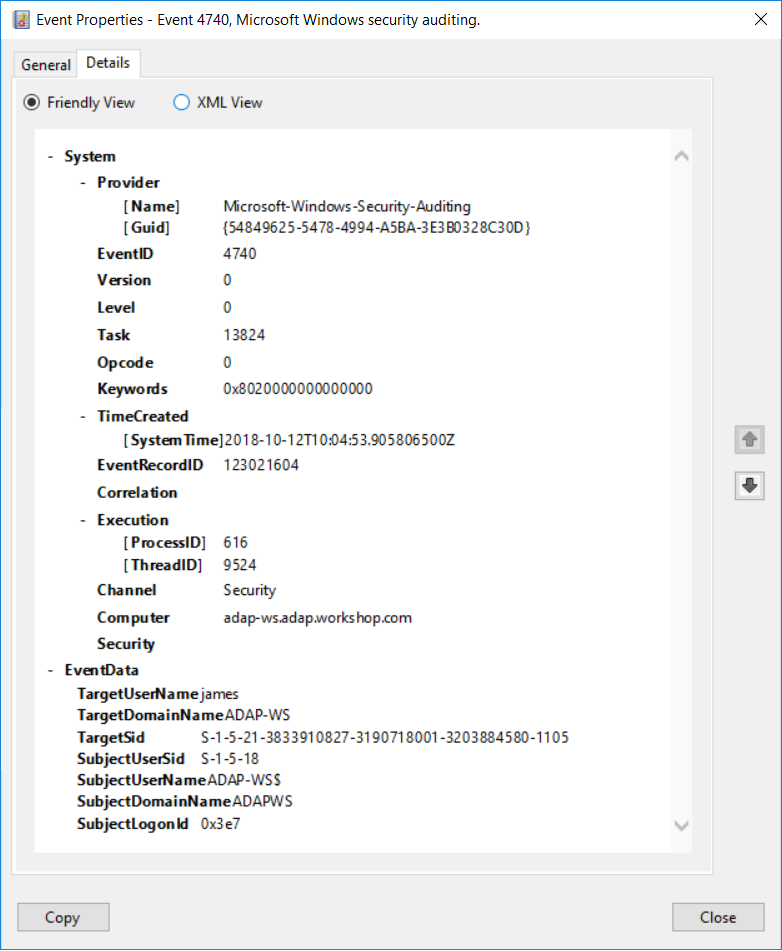
Event ID 4740 - Event properties
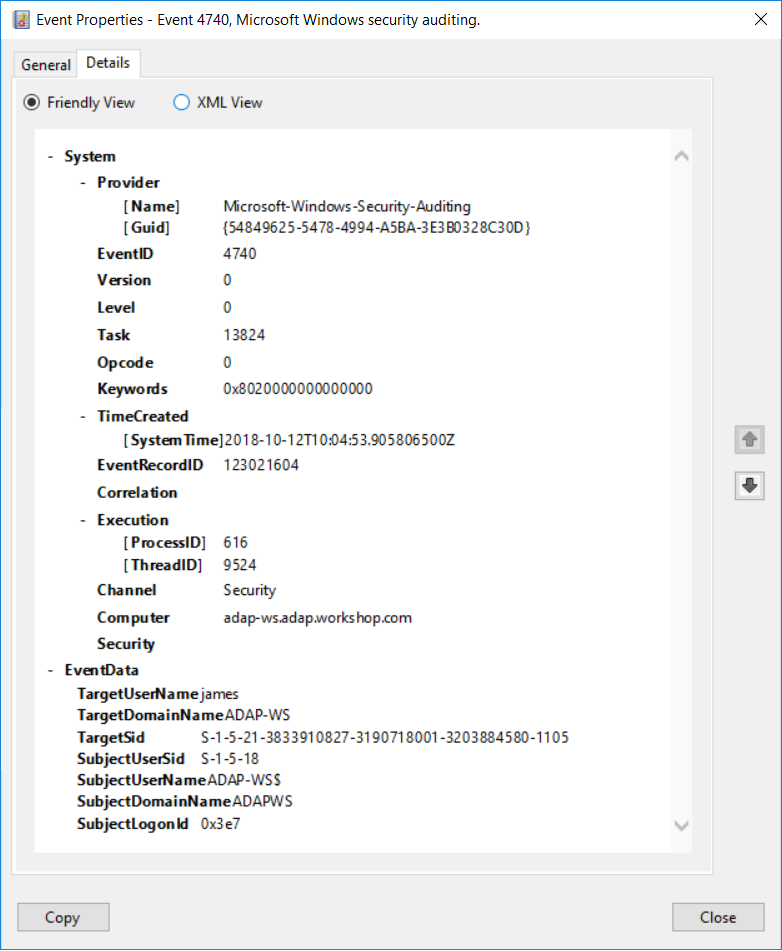
Event ID 4740 - Details tab
Event fields and reasons to monitor them
Let's break this event's properties down by Subject, Account That Was Locked Out, and Additional Information, as shown on the General tab (Fig. 1).
Subject:
Security ID: The SID of the account that performed the lockout operation.
Because event ID 4740 is usually triggered by the SYSTEM account, we recommend that you monitor this event and report it whenever Subject\Security ID is not "SYSTEM."
Account Name: The name of the account that performed the lockout operation.
Account Domain: The domain or computer name. Formats could vary to include the NETBIOS name, the lowercase full domain name, or the uppercase full domain name.
For well-known security principals this field is "NT AUTHORITY," and for local user accounts this field will contain the computer name that this account belongs to.
Logon ID: The logon ID helps you correlate this event with recent events that might contain the same logon ID (e.g. event ID 4625).
Account That Was Locked Out:
Security ID: The SID of the account that was locked out. Windows tries to resolve SIDs and show the account name. If the SID cannot be resolved, you will see the source data in the event.
Account Name: The name of the account that was locked out.
Monitor for all 4740 events where Account Name corresponds to a specific list of high-value accounts like CXOs and IT admins. Also audit this event for accounts that are monitored for every change.
Additional Information:
Caller Computer Name: The name of the computer account (e.g. JOHN-WS12R2) from which the logon attempt was generated.
Monitor Caller Computer Name for authentication attempts from user accounts that should not be used from specific endpoints, as well as computers that don't belong to your network.
The need for a third-party tool
1. 24/7, real-time monitoring:
Although you can attach a task to the security log and ask Windows to send you an email, you are limited to getting an email when event ID 4740 is generated, and Windows lacks the ability to apply more granular filters.
For example, Windows can send you an email when event ID 4740 is generated, but it will not be able to only notify you when high-value accounts get locked out, or if a logon request comes from an unauthorized endpoint. Getting specific alerts reduces the chance of you missing out on critical notifications amongst a heap of false-positive alerts.
With a tool like ADAudit Plus, not only can you apply granular filters to focus on real threats, you can get notified in real time via SMS, too.
2. User and entity behavior analytics (UEBA):
Leverage advanced statistical analysis and machine learning techniques to detect anomalous behavior within your network.
3. Compliance-ready reports:
Meet various compliance standards, such as SOX, HIPAA, PCI, FISMA, GLBA, and the GDPR, with out-of-the-box compliance reports.

