Composable application architecture: Designing systems for sustained agility at scale

Summary
Composable application architecture moves organizations beyond assembling modular apps to engineering systems that can evolve safely at scale. The article explains how capability-centric design, loose coupling, resilience, and strong governance form the architectural backbone needed to avoid service sprawl and operational risk. It outlines how frameworks like MACH, zero-trust security, and compliance-ready design enable sustained agility, cost control, and innovation, while offering CXOs a practical roadmap for adopting composable architecture as a long-term operating model rather than a short-term modernization trend.
As digital initiatives scale across cloud, SaaS, and distributed teams, many organizations are discovering a hard truth: Delivering features faster is easy, sustaining that pace without breaking systems is not. What begins as modular innovation often turns into fragmented services, overlapping APIs, rising cloud costs, and growing operational risk. The issue is rarely composable applications themselves, but the absence of a clear architectural backbone to support them.
This is where composable application architecture becomes essential. It shifts the focus from assembling applications quickly to engineering systems that can grow, change, and self-correct over time. For CXOs and enterprise architects, composable architecture is not a development trend but a strategic operating model, one that enables scale without chaos and agility without constant rework.
What is composable application architecture?
Composable application architecture is an approach that structures enterprise systems as independently deployable, loosely coupled, and capability-aligned components that can be composed, recomposed, and governed dynamically over time.
At the heart of this architecture are packaged business capabilities (PBCs). A PBC is a software component representing a well-defined business function (e.g., Payment Processing, Inventory Lookup, or Claims Submission). Unlike a simple microservice, a PBC is a bounded, functional building block that includes its own data, logic, and standardized APIs.
For example, healthcare platforms often add services such as telemedicine, appointment scheduling, patient notifications, or analytics on top of existing clinical systems. With composable architecture, these services integrate through APIs and events without direct database access. This ensures compliance with data protection regulations while launching new digital capabilities without destabilizing critical systems.
Core principles behind composable application architecture
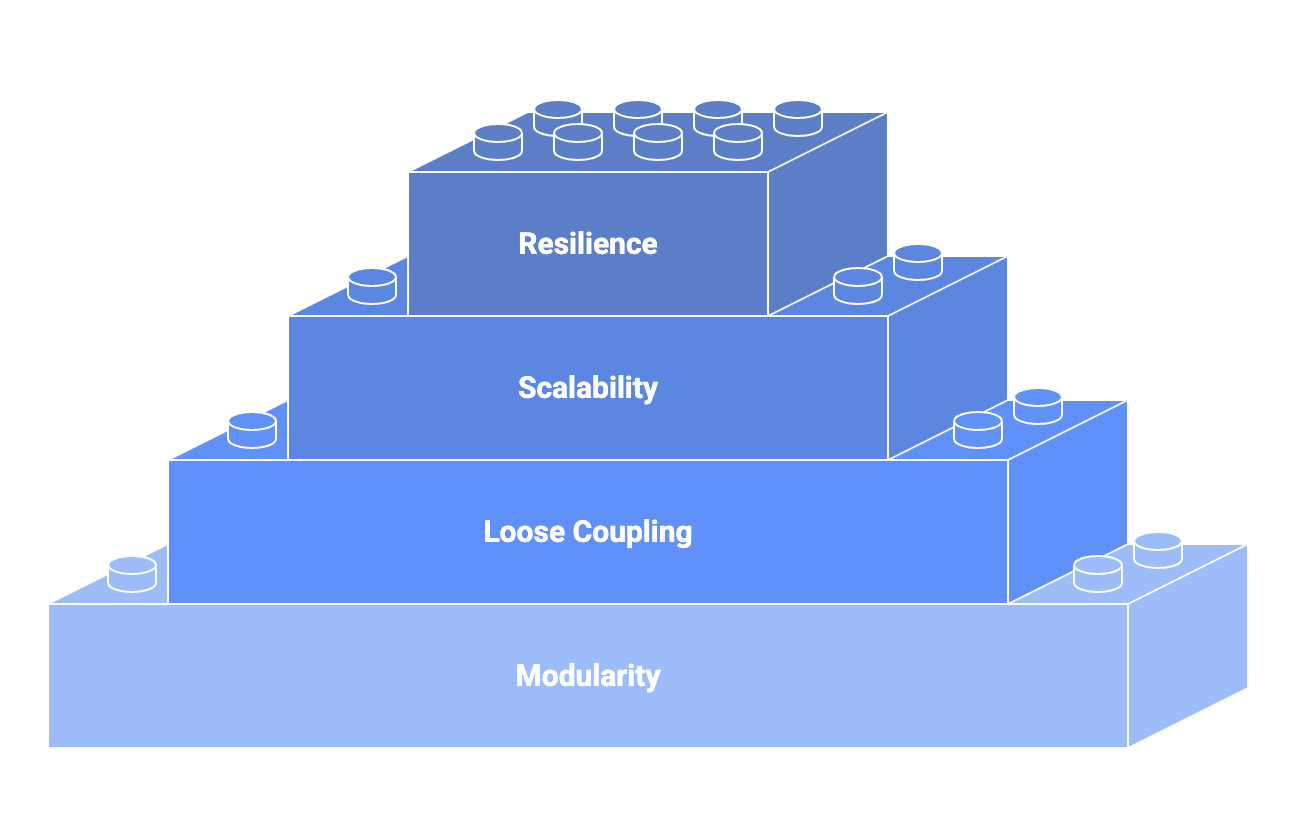
Composable architecture is defined less by tools and more by architectural discipline. The most effective implementations share several foundational principles:
Modularity
Composable architecture structures systems around discrete, reusable business capabilities rather than monolithic applications or organizational silos. Capabilities such as billing, identity, inventory, or onboarding encapsulate their own logic, data, and interfaces. This modularity reduces cross-team dependencies and allows capabilities to be reused, recomposed, or replaced without destabilizing the broader system.
Loose coupling
Components interact through well-defined APIs and event streams instead of shared databases or tightly bound runtime dependencies. This loose coupling allows each capability to evolve independently, minimizes cascading failures, and supports asynchronous, scalable workflows across distributed environments.
Scalability
Each component follows its own life cycle, from development and testing to deployment, scaling, and retirement. This independence enables organizations to scale only what is needed, deploy changes without system-wide coordination, and maintain high velocity without introducing systemic risk.
Resilience
Composable architectures assume that partial failures are inevitable in distributed systems. Instead of optimizing for perfection, they prioritize fault isolation, graceful degradation, and automated recovery. This resilience ensures that failures are contained at the component level and do not cascade across critical business operations.
The MACH principle framework
To achieve true composability, industry leaders often adhere to the MACH framework, which provides the technical requirements for a modern stack:
Microservices: Individual pieces of business functionality that are independently developed and deployed.
API-first: All functionality is exposed through APIs, allowing different PBCs to talk to each other seamlessly.
Cloud-native: Leveraging the full capabilities of the cloud (SaaS, PaaS, elastic scaling) rather than just lift-and-shifting legacy code.
Headless: Decoupling the front-end user experience from the back-end logic, enabling the same PBC to serve mobile apps, websites, and IoT devices simultaneously.
How composable application architecture works in practice
Composable architecture operates across multiple architectural layers, working together as a cohesive system.
Domain-aligned components
At the core are domain-aligned services or modules that encapsulate business logic and data ownership. These components are intentionally small in scope but rich in responsibility.
API and event-driven integration
APIs enable synchronous composition, while event-driven patterns allow systems to react asynchronously. This hybrid approach supports both real-time interactions and scalable, decoupled workflows.
Platform and control layers
A composable architecture relies on shared platform services such as identity, security, observability, CI/CD, and policy enforcement. These provide consistency without reintroducing tight coupling.
Runtime intelligence and orchestration
Modern composable systems integrate observability, automation, and AIOps capabilities to manage complexity at runtime, enabling intelligent routing, scaling, and remediation decisions.
Composable architecture vs. traditional application design
| Aspect | Traditional monolithic architecture | Composable application architecture |
|---|---|---|
| Application structure | Single, tightly coupled codebase where components are interdependent | Modular system built from independent, reusable business capabilities |
| Change impact | Small changes often require redeploying the entire application | Changes are isolated to specific components without affecting the whole system |
| Scalability model | Scales as a whole, often leading to overprovisioning | Scales individual services based on demand, improving efficiency |
| Time to market | Slower due to long release cycles and coordination overhead | Faster experimentation and delivery through independent deployments |
| Resilience and fault isolation | Failures can cascade across the entire application | Failures are contained within individual components or services |
| Technology flexibility | Limited flexibility once the stack is chosen | Teams can use different technologies per component where appropriate |
| Operational complexity | Simpler initially but becomes rigid and fragile at scale | Higher upfront complexity, but far more manageable at enterprise scale |
| Cloud readiness | Often retrofitted for cloud, leading to inefficiencies | Designed for cloud-native, API-driven, and distributed environments |
| Business alignment | Business logic tightly bound to application structure | Business capabilities mapped directly to modular services |
| Long-term agility | Decreases over time as technical debt accumulates | Increases over time as components evolve independently |
Why composable application architecture matters for CXOs
As organizations scale, architectural decisions directly impact financial performance, operational resilience, and innovation velocity. Composable architecture delivers strategic advantages that extend well beyond IT.
Sustained business agility
Composable architecture allows enterprises to respond to market changes, regulatory demands, or competitive pressure without large-scale rewrites. New capabilities can be introduced without disrupting existing operations.
Reduced systemic risk
Failure isolation ensures that issues in one component do not cascade across the enterprise. This is especially critical in distributed, cloud-native environments where partial outages are inevitable.
Improved cost governance
Independent scaling and life cycle management reduce overprovisioning. Teams can scale only what is needed, retire unused capabilities, and align infrastructure spend more closely with business value.
Faster, safer innovation
Teams can experiment, deploy, and iterate independently, while centralized architectural guardrails ensure security, compliance, and consistency are maintained.
Security and compliance by architectural design
Composable architectures expand the attack surface through APIs and distributed services, making security architecture foundational rather than optional.
Modern implementations embed protection through:
Zero Trust principles, where every service-to-service interaction is authenticated and authorized
API security controls, including rate limiting, schema validation, and abuse detection
Service isolation, limiting blast radius when a component is compromised
Continuous monitoring, enabling real-time threat detection across distributed systems
From a regulatory standpoint, composable architecture simplifies compliance in highly regulated industries such as healthcare, banking, insurance, and government. Capability-level isolation allows organizations to enforce data residency, access control, auditability, and policy enforcement aligned with standards like HIPAA, PCI DSS, GDPR, and SOX—without slowing innovation.
Architectural challenges to be aware of
While powerful, composable application architecture introduces new challenges that CXOs must anticipate.
Governance complexity: Without clear standards, service sprawl can undermine architectural integrity.
Data ownership boundaries: Decoupling logic is easier than decoupling data, and poor data design can reintroduce tight coupling.
Operational visibility: Distributed systems require advanced observability to maintain control and accountability.
Skill and maturity gaps: Teams must adopt new engineering, operational, and collaboration models.
Composable architecture succeeds not through tools alone, but through architectural intent and organizational alignment.
Roadmap to adopting composable application architecture
Adopting composable application architecture is less about a single transformation initiative and more about a phased evolution of how systems are designed, governed, and operated. Organizations that succeed treat it as an architectural journey rather than a one-time modernization effort.
Start with architectural intent, not tools
Begin by defining clear architectural principles around modularity, interoperability, and autonomy. Identify which business domains require agility and which systems are stable enough to remain unchanged. This prevents over-engineering and ensures composability is applied where it delivers real value.Decompose strategically, not universally
Rather than breaking everything into microservices at once, prioritize high-impact capabilities such as customer onboarding, pricing, fulfillment, or analytics. Incrementally decouple these areas into well-defined business capabilities with clear ownership and APIs.Establish strong governance early
Composable architectures fail when governance lags behind modularity. Put guardrails in place for API standards, versioning, service ownership, security, and life cycle management. Centralized visibility with decentralized execution is key to avoiding architectural sprawl.Modernize the platform layer
Invest in cloud-native platforms that support container orchestration, API management, service meshes, and event-driven integration. This platform layer becomes the foundation that enables teams to compose safely and consistently across environments.Align teams and operating models
Shift from project-based delivery to product- and capability-aligned teams. Each team should own its services end to end, from development to operations, with shared accountability for reliability, performance, and cost.Measure outcomes, not just velocity
Track success using metrics that matter at scale: deployment frequency without incidents, mean time to change, service reuse, cost efficiency, and resilience. These indicators signal whether composability is improving the enterprise or introducing hidden complexity.
For CXOs, the goal of this roadmap is clear: Build an architecture that allows the business to change continuously without increasing operational risk. Composable application architecture succeeds when agility, governance, and resilience evolve together.