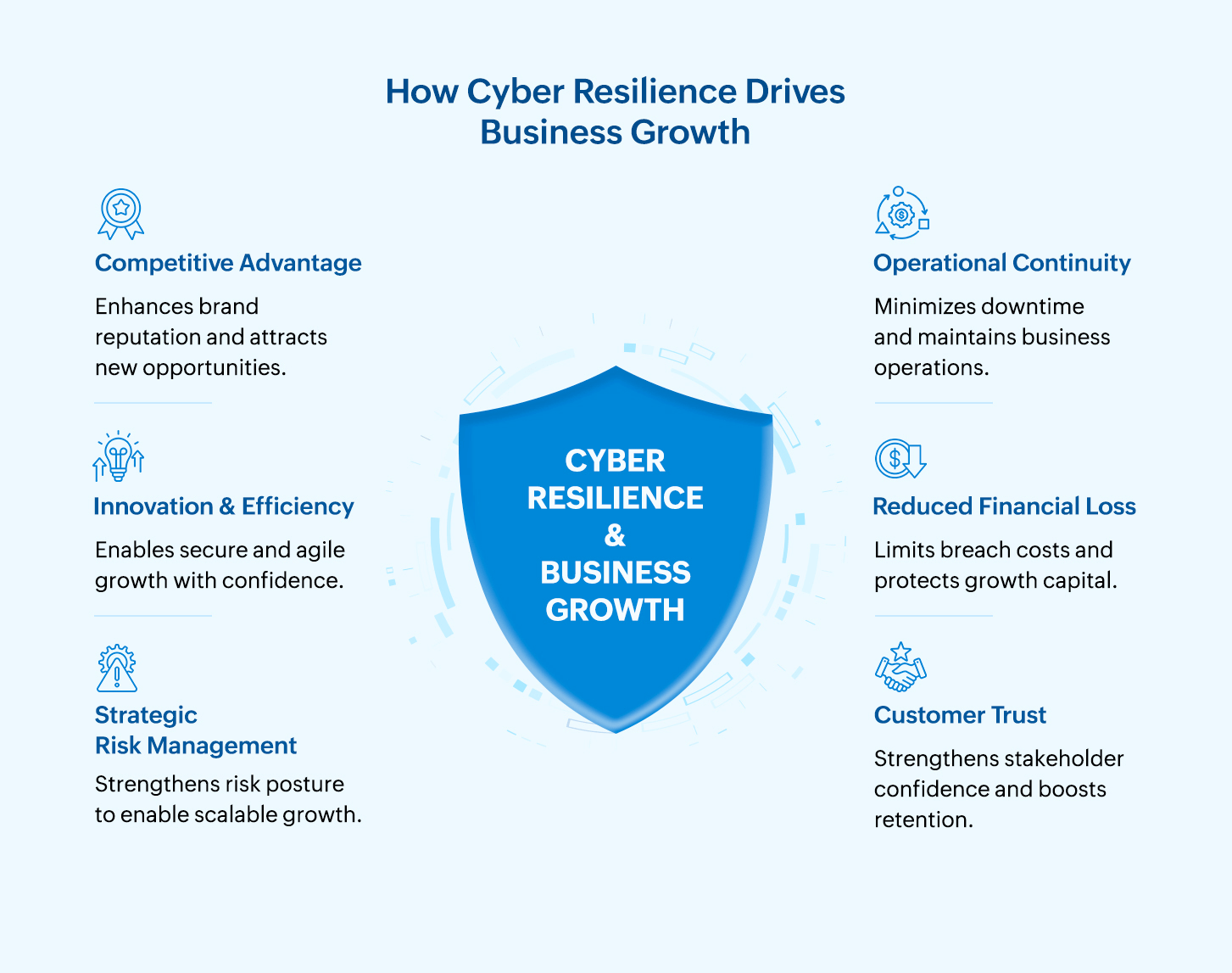
Cybersecurity enables revenue growth, protects a brand's reputation, strengthens customer trust, and ensures operational continuity. By reducing disruptions, accelerating secure innovation, and protecting digital assets, cybersecurity becomes a driver of business resilience and a competitive advantage rather than just an operational expense.
On this page
For years, cybersecurity was widely perceived as a cost center, one that was meant to satisfy compliance requirements and keep intruders out but was ultimately a non-revenue-generating function. Investment decisions were often justified defensively, framed around audit readiness and protecting network infrastructure rather than business growth. This perception no longer holds weight. In today's enterprise reality where the hybrid work model and cloud-driven ecosystems abound, cybersecurity directly influences business continuity, operational resilience, customer trust, and market competitiveness.
Incidents such as ransomware and supply chain attacks, along with healthcare data breaches, show how devastating the impact of cyberattacks can be on an organization’s profits, stock value, business continuity, and reputation. These events demonstrate how cybersecurity now underpins enterprise resilience.
Key takeaways for CISOs
- Shift from reactive defense to proactive resilience: Move beyond compliance-driven narratives and demonstrate how security directly supports revenue protection, operational resilience, and competitive differentiation.
- Align your security strategy with enterprise objectives: Develop multi-year roadmaps that support digital transformation, cloud adoption, M&A, and expansion initiatives while protecting critical revenue streams.
- Quantify cyber risk in financial terms: Translate technical vulnerabilities into measurable business impacts, such as the downtime cost, revenue disruption, regulatory penalties, and reputational damage, to strengthen executive decision-making.
- Embed cybersecurity into governance and enterprise risk management: Define your enterprise's risk appetite, assign business risk ownership, and align controls with recognized frameworks to ensure board-level visibility and accountability.
- Enable secure innovation without creating friction: Adopt security-by-design principles such as Zero Trust, DevSecOps, and third-party risk monitoring to support innovation while minimizing exposure.
- Drive maturity through culture and collaboration: Foster cross-functional engagement and shared accountability to ensure cybersecurity is treated as an enterprise-wide responsibility rather than a stand-alone function.
The growing strategic role of cybersecurity
Modern business environments depend on digital services, connected supply chains, and cloud-native platforms. In this context, cybersecurity is no longer just about preventing attacks; it determines enterprise stability, operational resilience, and revenue growth. Leading analyst firms like Gartner have emphasized the need for treating cybersecurity as a business investment that aligns protection goals with enterprise outcomes, rather than as an operational expense. If organizations persist with their outdated mindset that security investments can be made or utilized when an attack occurs (reactive security), or that cyber insurance will be the investment that protects them from the inevitable fallout of an attack, they will lose out to their competitors.
Frameworks like the NIST CSF support Gartner's view of cybersecurity as a business enabler since it's based on the premise that cybersecurity is integral to enterprise risk management. Introducing GOVERN as a core function of the framework further reinforces the importance of incorporating cybersecurity into the enterprise's risk management strategy.
A recent research article studied how security investments, when aligned with business goals, enhanced organizational impacts and resulted in benefits such as:
- Improved operational resilience and continuity.
- Stronger customer and stakeholder trust.
- Faster recovery from security incidents.
- Reduced overall incident costs.
- Enhanced competitive positioning.
Quantifying cyber risk in financial terms strengthens executive support and decision-making. Using business-focused metrics, such as the return on security investment (ROSI) and downtime cost reduction, demonstrates a higher perceived value from cybersecurity investments. The article also concluded that board engagement and CISO involvement in strategic planning accelerate alignment and improve investment outcomes. It emphasized that when cybersecurity is not treated as a stand-alone technical function but is instead integrated into enterprise strategy, it delivers measurable business value.
CISOs' role in aligning security with growth
CISOs serve as the bridge between technical teams and executive leadership. They play an instrumental role in securing executive buy-in by translating technical risk into strategic and financial impacts. While cybersecurity is a shared responsibility, it's undeniable that CISOs are critical in ensuring alignment between business and security goals.
CISOs are tasked with establishing strategies for enterprise security, governance and risk management, and ensuring alignment with the organization's business objectives. Here's how CISOs can redefine enterprise security as a business enabler:
1. Aligning cybersecurity with enterprise strategy
CISOs ensure that security initiatives directly support business objectives such as digital transformation, market expansion, M&A, and cloud adoption. Instead of implementing controls in isolation, they prioritize investments based on business risk exposure and strategic importance. This alignment ensures that cybersecurity protects revenue streams, safeguards innovation initiatives, and enables confident expansion.
Actionable insights for CISOs
- Develop a three-year or five-year roadmap of security objectives aligned with business goals.
- Adopt frameworks like the NIST CSF to track the progress of your organization's security maturity.
- Anticipate the attack and security trends and develop a plan to stay ahead of threats.
- Keep pace with AI governance and regulatory developments and adjust controls to remain compliant.
2. Translating cyber risks into business impacts
Boards and executive decision-makers understand financial and operational impacts better than technical security jargon. They tend to make their decisions based on the revenue impact, downtime costs, regulatory exposure, reputational risk, and insurance implications. By quantifying cyber risk in business language, CISOs can secure executive buy-in, improve capital allocation decisions, and demonstrate measurable business value.
Actionable insights for CISOs
- Quantify risk in terms of the financial impact using the Factor Analysis of Information Risk model or Monte Carlo simulation.
- Align cybersecurity KPIs with enterprise objectives such as uptime, customer trust, the compliance posture, and growth initiatives.
- Develop concise, industry-specific breach scenarios that clearly show how cyberattacks can disrupt operations, damage trust, and impact revenue and customer retention.
3. Strengthening governance and accountability
Governance involves incorporating organization-wide security policies, controls, and procedures. These policies have to align with business objectives for them to be implemented successfully with board-level support. CISOs help establish governance frameworks that integrate cybersecurity into enterprise risk management and ensure that cybersecurity is not siloed within the IT department but embedded into decision-making processes across the organization.
Actionable insights for CISOs
- Define your organization's risk appetite and tolerance in alignment with its strategic business objectives.
- Establish clear risk ownership across business units.
- Conduct qualitative and quantitative risk assessments periodically.
- Embed security into procurement, product development, and vendor management.
- Align controls with recognized frameworks like the NIST CSF.
- Automate compliance monitoring to detect policy violations and control drift in real time.
4. Enabling secure innovation and information security
Digital transformation initiatives, such as cloud migration, AI adoption, IoT integration, and ecosystem partnerships, require security by design. However, these introduce security challenges, of which employees may not always be aware. Shadow IT and the unapproved use of applications also complicate visibility, leading to breaches and friction with the security team. CISOs perform the balancing act of enabling secure innovation while reducing friction.
Actionable insights for CISOs
- Implement Zero Trust architecture, the principle of least privilege, and strong administrative and technical controls to ensure secure cloud adoption.
- Adopt DevSecOps, threat modeling, and secure coding policies to ensure application security.
- Ensure secure third-party collaboration by conducting due diligence, enforcing contractual security requirements, requiring compliance certifications, and enabling continuous monitoring.
5. Building organizational resilience
Cyber resilience is essential for maintaining operational continuity in the face of insider and supply chain threats and ransomware attacks. By bolstering resilience, CISOs can help protect revenue and customer trust and enable long-term growth.
Actionable insights for CISOs
- Invest in SIEM solutions with robust detection and response capabilities.
- Enforce validated security programs for incident response, business continuity planning, disaster recovery, and supply chain risk mitigation.
- Build a security-driven culture by implementing role-based security training, continuous microlearning, and phishing and social engineering simulations.
6. Fostering cross-functional collaboration
Cybersecurity is a collective responsibility, which means the organization's cyber maturity is dependent on security being embedded across business functions rather than operating as a siloed control function. CISOs must work closely with different business functions to ensure that cybersecurity supports enterprise-wide objectives.
Actionable insights for CISOs
- Form a recurring governance forum including finance, IT, legal, compliance, risk, HR, and operations teams to understand their priorities and get their buy-in.
- Collaborate with legal and compliance teams to ensure regulatory readiness.
- Develop scenario-based financial models for ransomware attacks, data breaches, and third-party compromise.
- Present risk heat maps in business impact terms and simplify reporting in terms of risk, cost, and compliance outcomes.
- Conduct joint tabletop exercises, such as cyberwar games, to increase the effectiveness of cross-functional team collaboration and to enhance cyberdefense.
Frequently asked questions
Effective cybersecurity reduces downtime, prevents data breaches and regulatory fines, and minimizes recovery costs. It also supports secure digital services and customer confidence, directly influencing revenue retention and long-term profitability.
Cybersecurity risks are business risks. Board involvement ensures that security priorities align with enterprise strategy, capital allocation decisions are informed by risk exposure, and accountability for cyber resilience extends beyond the IT team.
By translating technical risks into financial impacts, such as the projected loss scenarios, downtime costs, regulatory exposure, and ROSI, CISOs can align cybersecurity metrics with business KPIs and strategic objectives.
Cloud migration, AI adoption, IoT integration, and supply chain partnerships increase the attack surface. Embedding security by design ensures that these initiatives scale safely, preventing innovation from introducing unmanaged risks.
Yes. Organizations with mature security postures recover faster from incidents, maintain stakeholder confidence, meet regulatory expectations efficiently, and differentiate themselves as trusted digital partners in the market.
Cyber resilience ensures the organization can detect, respond to, and recover from attacks quickly. This minimizes operational disruption, protects revenue streams, and preserves customer and investor trust.
Supply chain risk can materially affect enterprise valuation because a significant vendor breach can trigger stock volatility, erode investor confidence, and increase the perceived enterprise risk.
Related solutions
ManageEngine AD360 is a unified IAM solution that provides SSO, adaptive MFA, UBA-driven analytics, and RBAC. Manage employees' digital identities and implement the principle of least privilege with AD360.
To learn more,
Sign up for a personalized demoManageEngine Log360 is a unified SIEM solution with UEBA, DLP, CASB, and dark web monitoring capabilities. Detect compromised credentials, reduce breach impacts, and lower compliance risk exposure with Log360.
To learn more,
Sign up for a personalized demoThis content has been reviewed and approved by Ram Vaidyanathan, IT security and technology consultant at ManageEngine.
