Configuring Port Address Translation (PAT) on Cisco devices
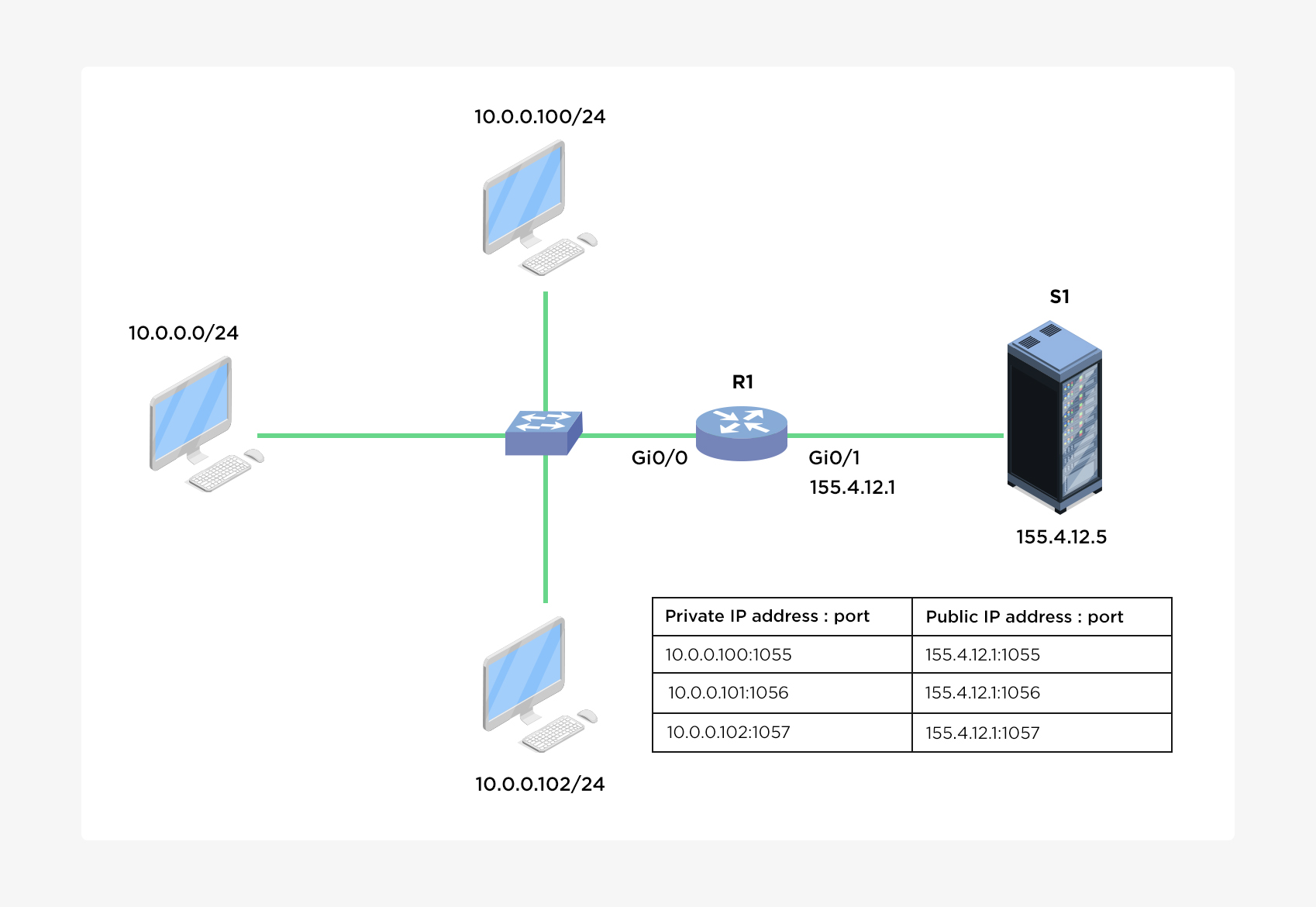
With Port Address Translation (PAT), a single public IP address is used for all internal private IP addresses, but a different port is assigned to each private IP address. This type of NAT is also known as NAT Overload and is the typical form of NAT used in today’s networks. It is even supported by most consumer-grade routers.
PAT allows you to support many hosts with only few public IP addresses. It works by creating dynamic NAT mapping, in which a global (public) IP address and a unique port number are selected. The router keeps a NAT table entry for every unique combination of the private IP address and port, with translation to the global address and a unique port number.
You will be able to create the corresponding Configlet commands using Network Configuration Manager application. This will help you perform the same operation on multiple devices simultaneously.
If you don't have NCM installed, please click here to download and install the application.
To configure PAT, the following commands are required:
- Configure the router’s inside interface using the ip nat inside command.
- Configure the router’s outside interface using the ip nat outside command.
- Configure an access list that includes a list of the inside source addresses that should be translated.
- Enable PAT with the ip nat inside source list ACL_NUMBER interface TYPE overload global configuration command.
Steps to configure PAT for the network picture above using CLI.
- Login to the device using SSH / TELNET and go to enable mode.
- Go into the config mode.
- Configure the router's inside interface
- Configure the router's outside interface
- Define an access list that will include all private IP addresses you would like to translate within interface config mode
- Enable NAT and refer to the ACL created in the previous step and to the interface whose IP address will be used for translations
- Exit config mode
- Execute show ip nat translations command to view the NAT configuration.
- Copy the running configuration into startup configuration using below command
Router#configure terminal
Enter configuration commands, one per line. End with CNTL/Z.
Router(config)#
Router(config)#interface Gi0/0
Router(config-if)#ip nat inside
Router(config-if)#exit
Router(config)#interface Gi0/1
Router(config-if)#ip nat outside
Router(config-if)#access-list 1 permit 10.0.0.0 0.0.0.255
Router(config-if)#exit
Router(config)#ip nat inside source list 1 interface Gi0/1 overload
Router(config)#exit
Router#
Notice that the same IP address (155.4.12.1) has been used to translate three private IP addresses (10.0.0.100, 10.0.0.101, and 10.0.0.102). The port number of the public IP address is unique for each connection. So when S1 responds to 155.4.12.1:1026, R1 look into its NAT translations table and forward the response to 10.0.0.102:1025
Router#write memory
Building configuration... [OK]
Router#
The corresponding configlet can be created in NCM application as shown in below screenshot.
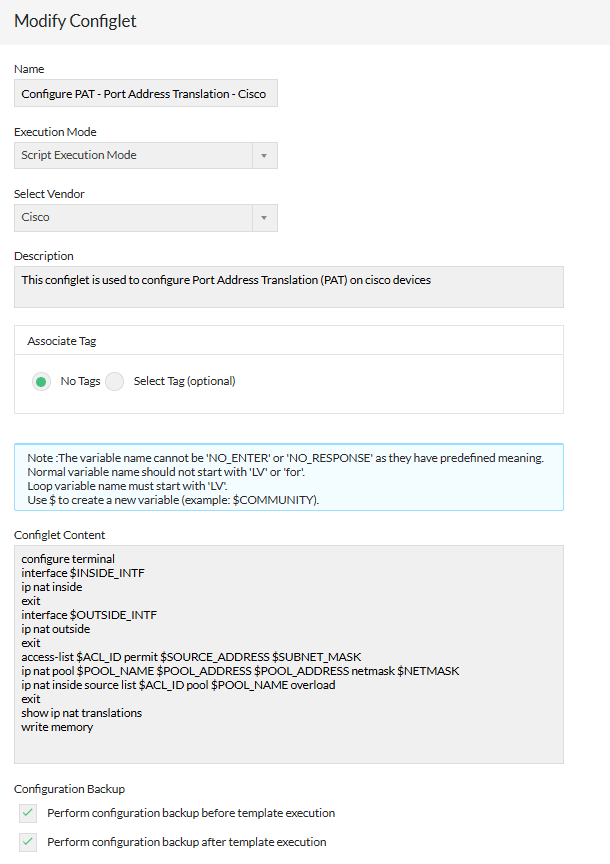
Also you can click the below button to download the Configlet as XML and import it into NCM application using file import option.
| Configlet Name | Configure PAT - Port Address Translation - Cisco |
|---|---|
| Description | This configlet is used to configure Port Address Translation PAT on cisco devices |
| Execution Mode | Script Execution Mode |
| Configlet Content | configure terminal interface $INSIDE_INTF ip nat inside exit interface $OUTSIDE_INTF ip nat outside exit access-list $ACL_ID permit $SOURCE_ADDRESS $SUBNET_MASK ip nat pool $POOL_NAME $POOL_ADDRESS $POOL_ADDRESS netmask $NETMASK ip nat inside source list $ACL_ID pool $POOL_NAME overload exit show ip nat translations write memory |