Direct Inward Dialing: +1 408 916 9892
Once logon auditing is enabled, Active Directory Event Viewer records them as events with specific event IDs. To view the events, open Event Viewer, navigate to Windows Logs> Security. Look for event IDs 4624 (Account was logged on), 4634 (Account was logged off), 4647 (user initiated logoff) and 4672 (special logon), 4800 (the workstation was locked), 4801 (workstation was unlocked).
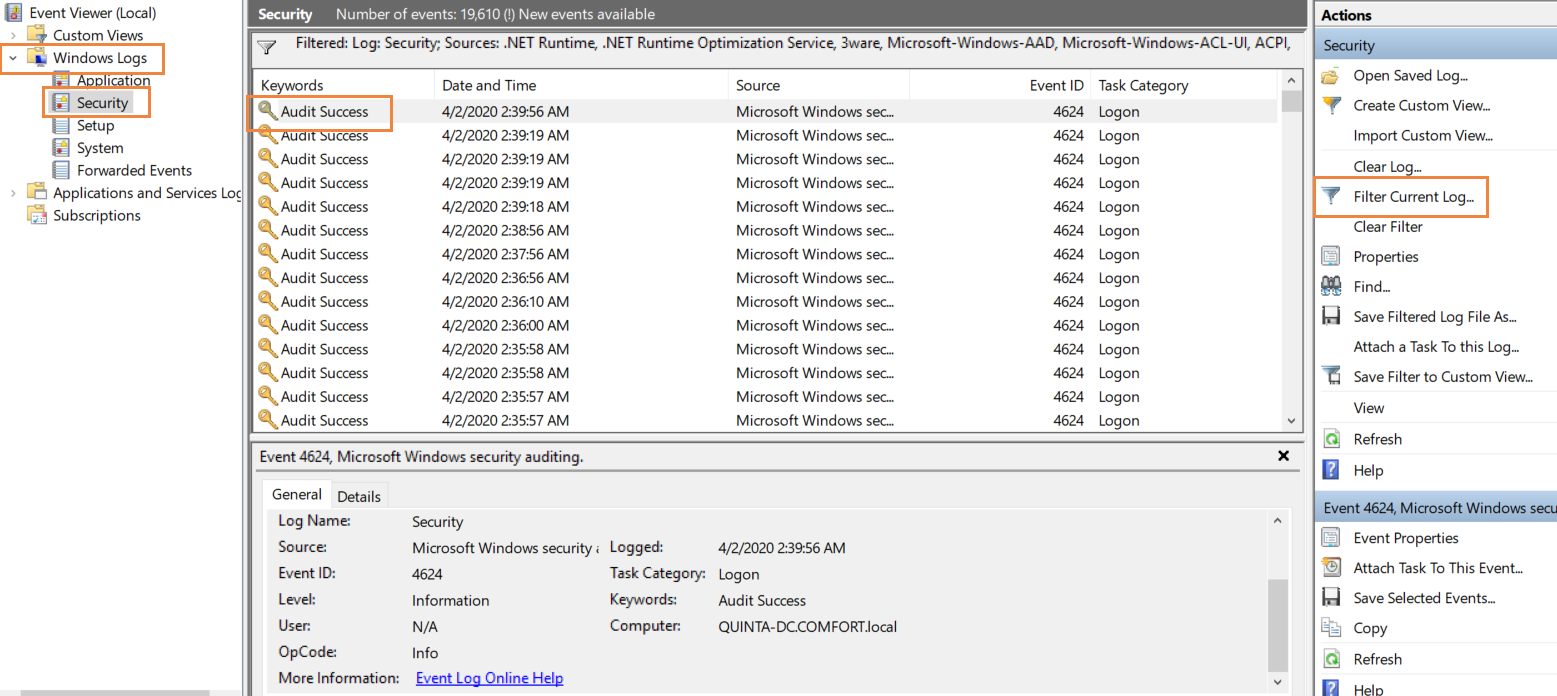
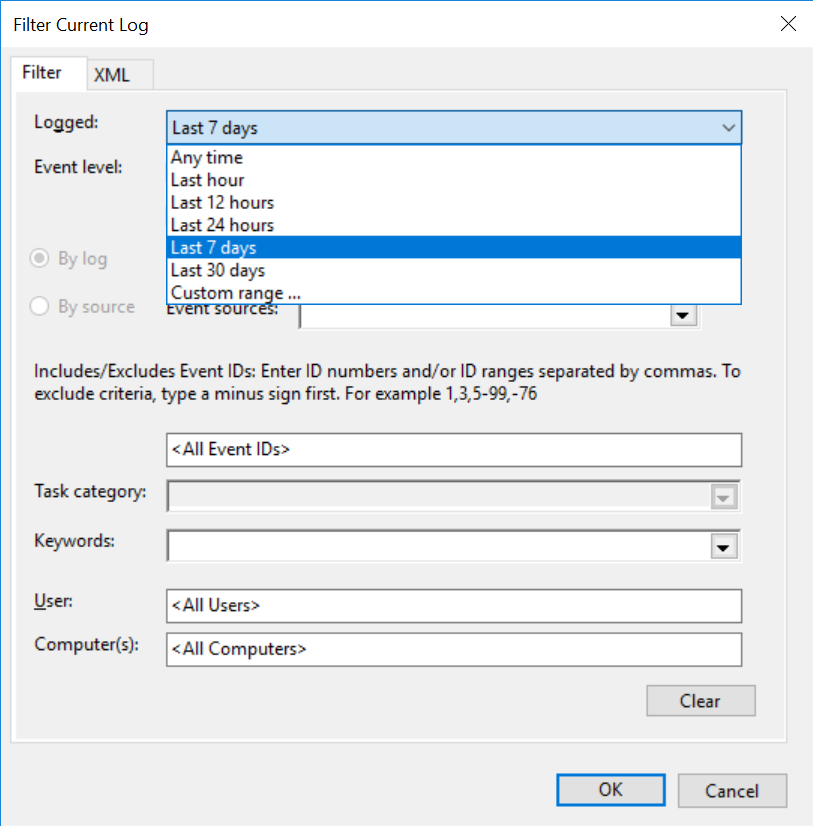
Click on 'Filter Current Log', on the right side to filter the logs based on event IDs or the time range for which you need the information.
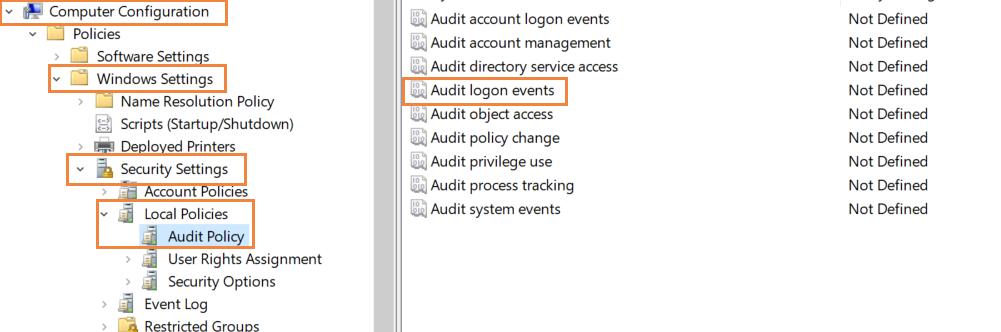
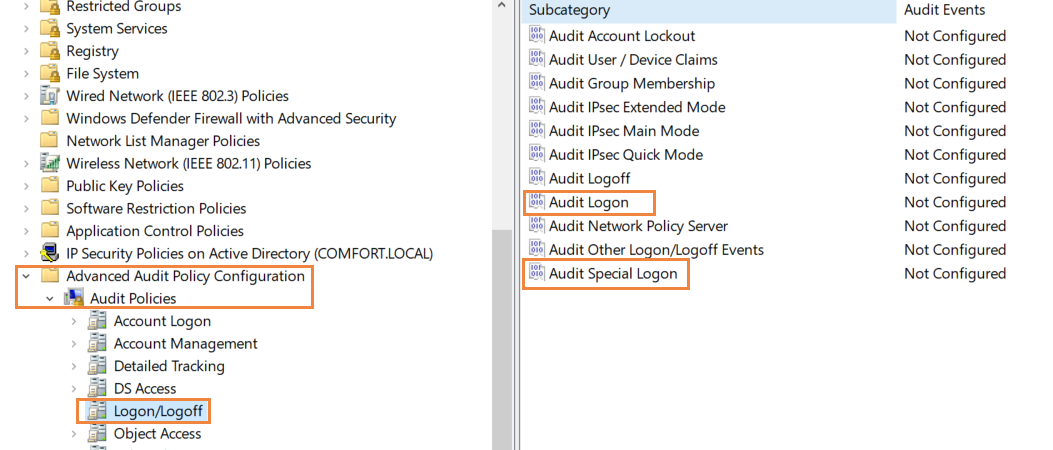
Turn on Audit Policy and enable logon/logoff auditing as detailed in steps 1 and 2 from the native AD auditing section.
Click on the 'Reports' tab and then select 'Local logon-Logoff'. Here, there are multiple reports that give you the logon information you need and more. Logon activity shows the logon attempts, with the username, logon time, name of the workstation, type of logon among other examples. Logon Duration gives you the logon time, the logoff time and the duration of each logged in session. User Work Hours gives the total amount of time the user spent logged in to the workstation.
Here is a sample Logon Activity report:
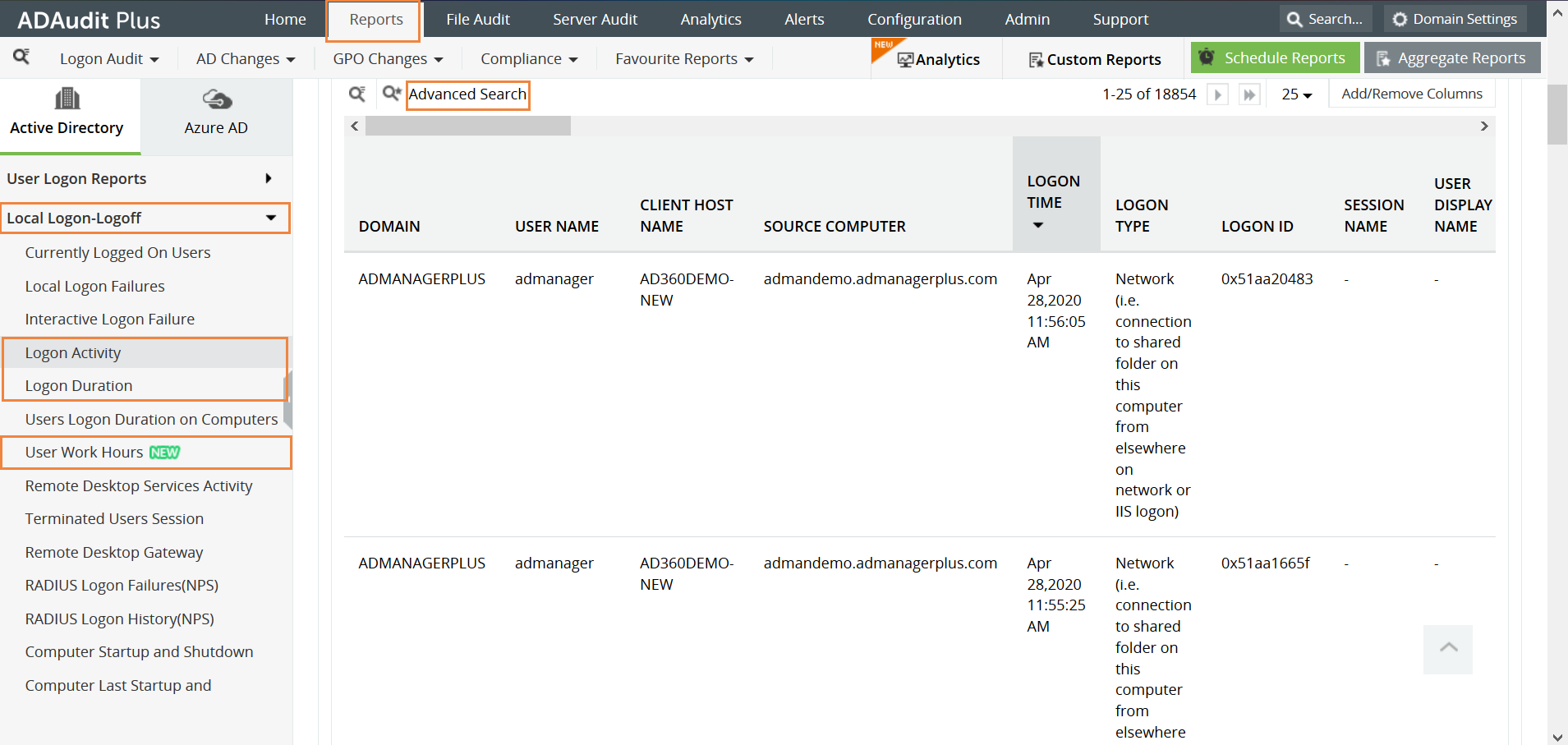
Click on 'Advanced Search' at the top to filter the report. A variety of parameters such as Username, Event ID, Domain can be used to filter the report.