What is attack surface management?
Attack surface management is the continuous process of monitoring, discovering, and reducing risks across all assets that could be exploited by an attacker.
It has become a core part of modern security. Organizations today operate across cloud platforms, SaaS applications, remote endpoints, and identity systems. Assets are created and exposed faster than most teams can track. Some are forgotten, while others were never documented in the first place.
An attack surface includes everything an attacker can potentially interact with, such as:
Internet-facing applications and services
Internal systems and endpoints
Cloud resources
Identities, accounts, and permissions
Unlike traditional security approaches that rely on predefined asset inventories, attack surface management assumes that visibility is incomplete. Instead of working from what is already known, it continuously looks for gaps, uncovering assets and exposures that might otherwise go unnoticed.
Why attack surface management matters now
Attack surfaces are expanding faster than ever.
Recent industry findings consistently show that organizations manage hundreds, sometimes thousands, of unknown or unmanaged assets at any given time. Cloud adoption, decentralized teams, and rapid deployment cycles have made environments more dynamic but also more fragmented.
What this really means is that exposure is no longer an exception. It’s built into how modern infrastructure operates. A misconfigured cloud service, an exposed API, or an overlooked identity can all become entry points. And often, these aren’t the result of sophisticated attacks but simple visibility gaps.
Attack surface management shifts security from being reactive to continuous. It ensures that as environments evolve, visibility and control evolve with them.
Types of attack surface management
External attack surface management
External attack surface management focuses on assets exposed to the internet. This includes domains, subdomains, public-facing applications, open ports, and shadow IT.
Internal attack surface management
This deals with systems inside the organization, such as endpoints, servers, and internal applications. These become critical once an attacker gains initial access.
Cyber asset attack surface management
This type of management connects data across multiple systems to create a unified asset inventory. It pulls from cloud platforms, endpoint tools, and identity systems to eliminate blind spots.
Together, these layers provide a more complete view of an organization’s exposure.
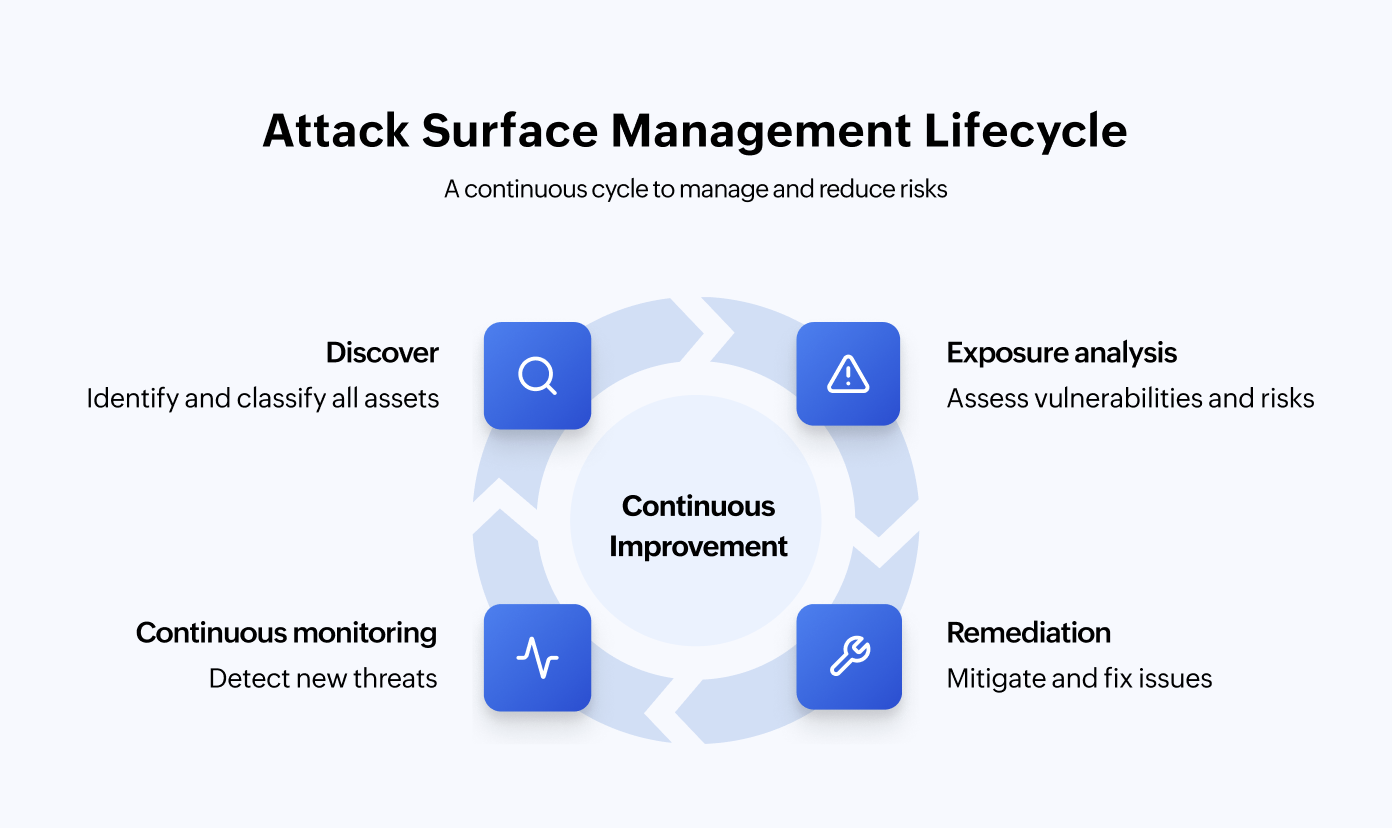
Attack surface management life cycle
Attack surface management is not a one-time activity. It works as a continuous cycle because environments are constantly changing.
Discovery
It begins with discovery, where all assets, known and unknown, are identified across environments. Once discovered, assets are classified based on ownership, function, and business importance.
Exposure analysis
From there, organizations move into exposure analysis, identifying vulnerabilities, misconfigurations, and unintended access points. These findings are then evaluated through risk prioritization, where context such as exploitability and impact determines what needs immediate attention.
Remediation
Next comes remediation, which may involve patching systems, fixing configurations, or adjusting access controls.
Continuous monitoring
Finally, everything feeds into continuous monitoring, ensuring that new exposures are detected as soon as they appear.
This cycle repeats continuously—in modern environments, stability is temporary, but change is constant.
Attack surface management framework
While the life cycle explains how attack surface management operates over time, the framework explains how it is structured.
A strong attack surface management framework typically includes three interconnected layers.
Visibility layer
The visibility layer focuses on discovering and maintaining an accurate inventory of assets. Without this, everything else breaks down.
Analysis layer
The analysis layer evaluates exposures and provides context around risk. It connects vulnerabilities, configurations, and asset criticality to determine what actually matters.
Control layer
The control layer is where risk is reduced. This includes remediation, policy enforcement, and access governance.
In more mature environments, this framework integrates with identity systems, threat intelligence, and security operations, creating a more coordinated approach to risk management.
Where attack surface management falls short
Even with strong discovery and monitoring, attack surface management has limitations.
Most attack surface management approaches focus heavily on assets and external exposure. They are excellent at identifying what is visible, but they often lack deeper insight into how access works within the environment.
And that’s where a significant portion of risk exists, because every asset is ultimately accessed through identities.
Attack surface management vs. vulnerability management
Vulnerability management operates within a known environment. It scans identified assets for known weaknesses and helps teams remediate them. It is structured and effective, but it depends heavily on the accuracy of your asset inventory.
Attack surface management starts earlier. It assumes your inventory is incomplete and focuses on discovering what exists beyond your visibility. It identifies unknown assets, unintended exposures, and risks that traditional tools might miss.
In simple terms, vulnerability management helps you fix what you know about, while attack surface management helps you understand what you don’t.
Attack surface management vs. penetration testing
Penetration testing simulates real-world attacks, but it is time-bound. It provides valuable insights into how an attacker might exploit your environment at a specific moment.
Attack surface management, on the other hand, is continuous. It tracks changes, identifies new exposures, and ensures visibility is always up to date.
Penetration testing shows how far an attacker could go. Attack surface management ensures you always know where they could start.
Exposure management vs. attack surface management
Attack surface management gives you visibility into assets and their exposures. But visibility alone doesn’t solve the problem of prioritization.
This is where exposure management comes in.
Exposure management connects assets, vulnerabilities, identities, and threat context to determine which risks actually matter. Instead of treating all findings equally, it helps organizations focus on what is most likely to be exploited and what would have the highest impact.
In essence:
Attack surface management tells you what is exposed.
Exposure management tells you what is dangerous.
This distinction becomes critical as environments grow more complex and the volume of findings increases.
Bringing identity into attack surface management
To fully reduce risk, attack surface management needs to extend beyond assets into access.
This means understanding not just what is exposed but:
Who can access it
How that access is granted
Whether it is necessary
This is where risk exposure management becomes essential.
By combining visibility into assets with insight into identities and permissions, organizations can move from detection to control. Instead of just identifying exposure, they can evaluate whether access aligns with least-privilege principles and security policies.
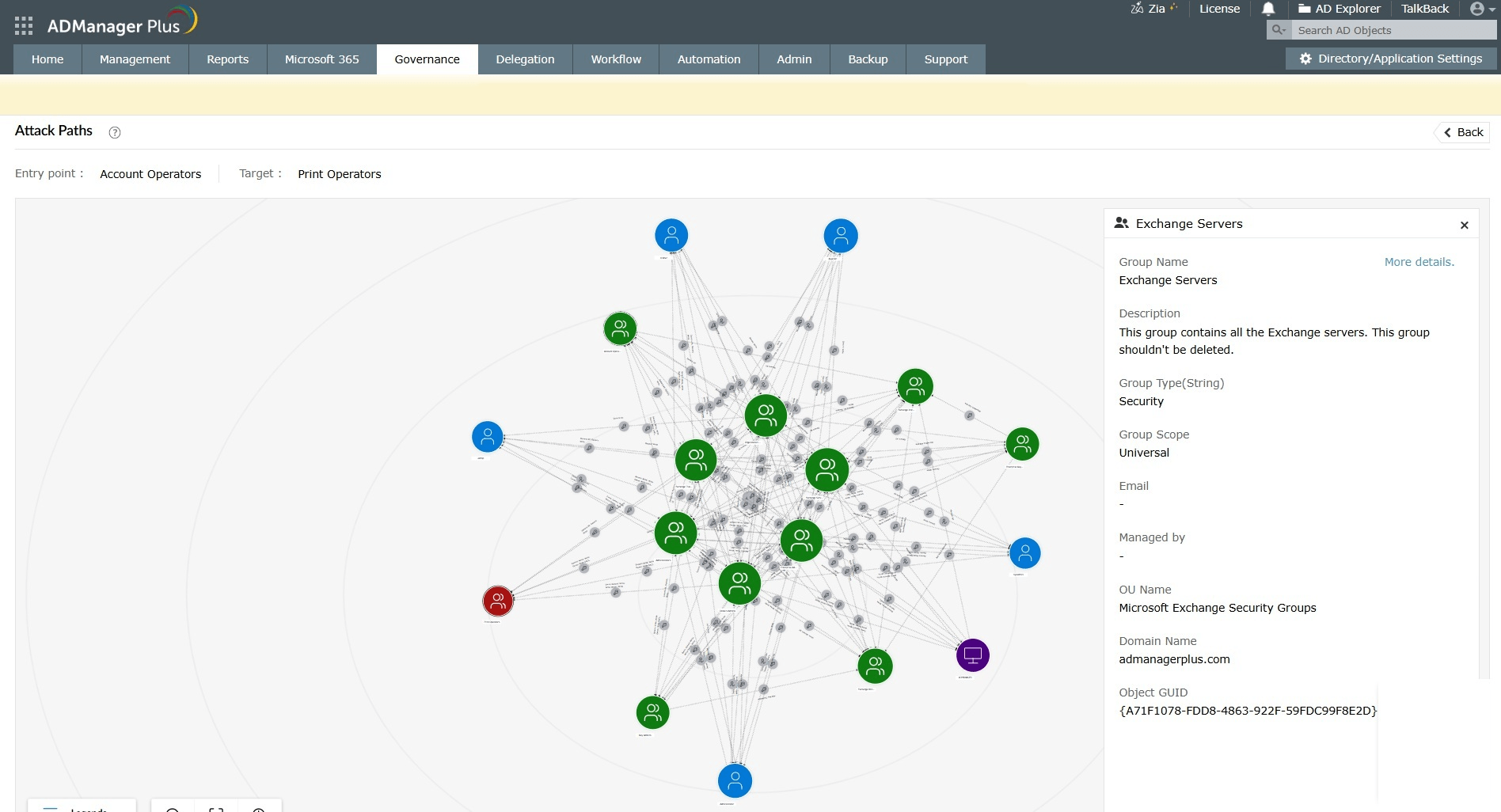
In Active Directory environments, this becomes especially important. Privileged groups, nested memberships, and delegation models can create hidden access paths that are difficult to track manually.
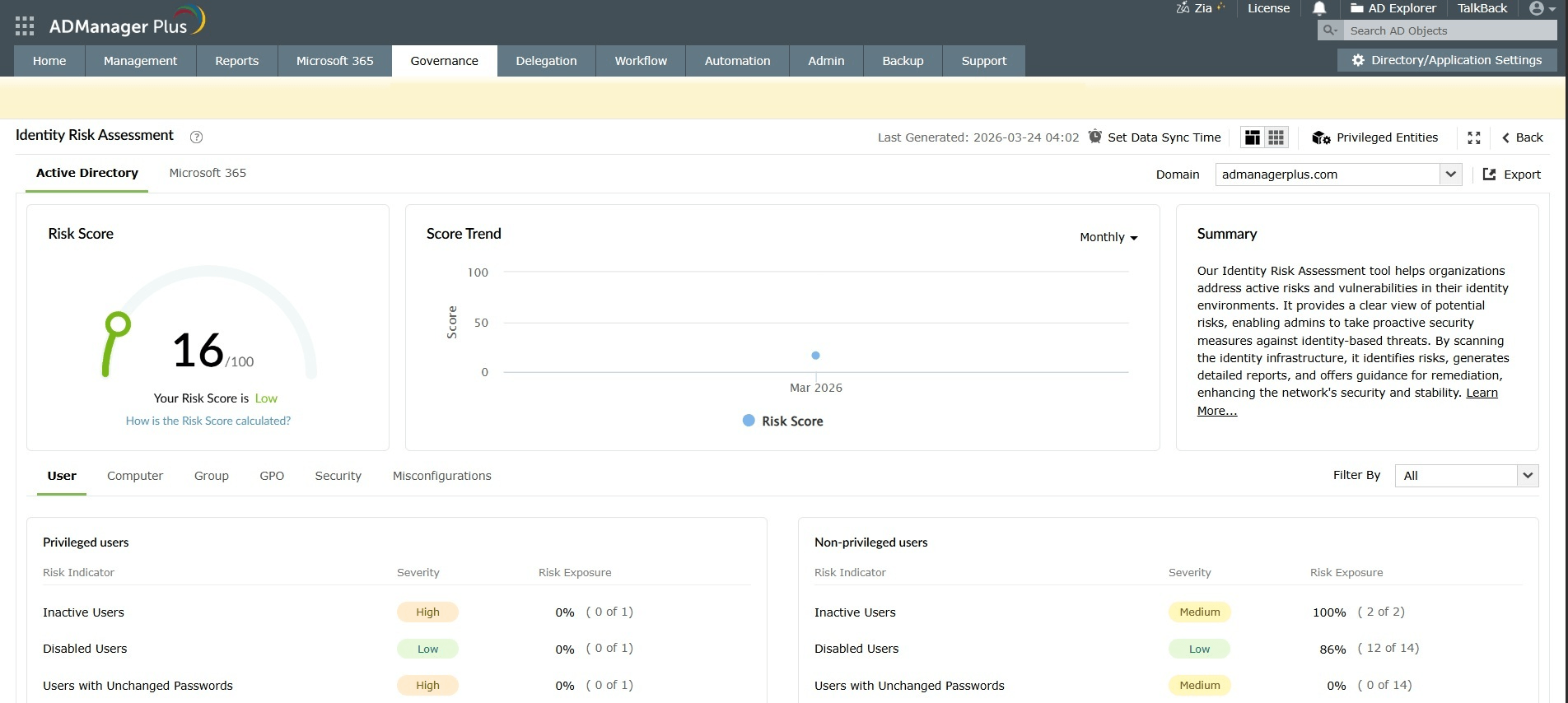
Solutions like ADManager Plus help address this by providing centralized visibility into identity-based risks. They enable organizations to analyze permissions, detect privilege sprawl, identify inactive but high-impact accounts, and ensure that access is properly governed.
This brings a critical missing layer into attack surface management—one that connects exposure to actual risk.
Attack surface management use cases
Use case 1: Identifying unknown and shadow assets
In many organizations, not every asset is tracked through official processes. A developer might spin up a test server, a team might use an unsanctioned SaaS tool, or an old subdomain might still be active long after its purpose is gone.
These unknown assets often sit outside visibility but remain accessible from the internet.
Attack surface management continuously scans and discovers these assets, bringing them into the light before attackers find them. Instead of relying on manual inventorying, this ensures that even forgotten or unmanaged resources are identified and assessed.
Use case 2: Detecting exposed services and misconfigurations early
A single misconfiguration, like an open port, a publicly accessible database, or an exposed API, can become an entry point for attackers.
In fast-moving environments, these exposures can appear unintentionally during deployments or updates. Without continuous monitoring, they may go unnoticed for long periods.
Attack surface management helps detect these issues as they arise. It provides real-time visibility into what is exposed and flags risks early, allowing teams to fix them before they are exploited.
Use case 3: Reducing identity-based risk and privilege exposure
Not all risks come from exposed systems. Many originate from excessive or poorly managed access.
For example, an inactive employee account may still have privileged access, or nested group memberships might grant unintended administrative control. These issues don’t appear as vulnerabilities, but they create pathways for attackers once access is gained.
By extending visibility into identities and permissions, attack surface management helps organizations identify and reduce these risks. When combined with identity-focused controls, it becomes much harder for attackers to escalate privileges or move laterally.
Best practices for attack surface management
Leverage continuous visibility, not periodic scans
Attack surfaces are constantly changing. New assets are created, configurations shift, and access evolves. Relying on periodic scans creates gaps where exposures can exist undetected. Continuous discovery and monitoring ensure that changes are tracked in real time and risks are identified as they emerge.
Prioritize risk based on impact
Effective attack surface management focuses on prioritization. By considering factors like exploitability, business impact, and access level, teams can focus on what truly matters instead of trying to fix everything at once.
Attack surfaces span multiple environments, including cloud platforms, endpoints, and identity systems. When data is siloed, it creates blind spots. Bringing together insights from different tools helps create a unified view of risk. It allows organizations to connect assets, vulnerabilities, and access, making it easier to understand the full context of exposure.
Treat identity as part of the attack surface
One of the most common gaps in security is treating identity separately from infrastructure.
In reality, access defines risk. Even a well-secured system can become vulnerable if permissions are excessive or misconfigured. Including identities, privileges, and access paths as part of the attack surface ensures a more complete approach to risk reduction.
How ADManager Plus enhances attack surface management
Solutions like ADManager Plus strengthen attack surface management through risk exposure management by:
Continuously analyzing identities, permissions, and access paths across Active Directory environments.
Visualizing real-world attack paths instead of just listing users or groups.
Identifying hidden risks, such as excessive permissions and nested group access.
Prioritizing exposures based on actual risk and impact.
Enabling continuous monitoring to detect changes in access and emerging risks.
Automating remediation actions to reduce manual effort and response time.
This helps organizations move beyond visibility and take proactive steps to reduce identity-based risks, making attack surface management more complete and actionable.
Take control of your identity attack surface with ADManager Plus
Explore now
FAQs
1. What types of assets are included in an organization’s attack surface?
An organization’s attack surface includes any system, device, or human element that an attacker can potentially exploit.
This typically spans several categories:
Digital assets, such as websites, web applications, APIs, SaaS platforms, cloud instances, databases, and internal applications
Network and infrastructure components, like routers, firewalls, VPN gateways, DNS records, IP ranges, and exposed services
Endpoint devices, including laptops, desktops, servers, mobile devices, and IoT or OT devices such as cameras and sensors
Cloud infrastructure, like storage buckets, containers, serverless functions, and third-party integrations
Human and third-party elements, including employees, contractors, and partners whose credentials or access could be misused
Physical assets, such as servers, workstations, USB drives, and access badges
In simple terms, the attack surface includes anything that can accept input, expose data, or be misconfigured in a way that creates an entry point.
2. How does continuous monitoring aid in attack surface management?
Continuous monitoring ensures that your view of the attack surface stays accurate as your environment evolves.
It plays a key role by automatically discovering new assets such as cloud instances, domains, or services as they are created, including those that may not be officially tracked. It also detects vulnerabilities and misconfigurations in real time, reducing the gap between when a risk appears and when it is identified.
By shortening the time to detect issues, organizations can significantly reduce the window in which attackers can exploit them. Many modern attack surface management solutions also enrich findings with threat intelligence, helping teams understand which risks are most urgent.
In essence, continuous monitoring transforms attack surface management from a static snapshot into a constantly updated view of risk.
3. What are the benefits of implementing effective attack surface management?
Proactive risk reduction
Identify and prioritize exposures before attackers can exploit them.Reduced attack surface
Discover and secure unused, misconfigured, or forgotten assets.Faster incident response
Gain clear visibility into affected assets and their relationships for quicker containment.Improved compliance posture
Maintain accurate asset inventory and configurations for audits and regulations.Better third-party risk visibility
Identify external dependencies and potential vulnerabilities in vendor integrations.
4. What is the purpose of attack surface management?
Continuous discovery of assets
Identify all known and unknown assets across the environment.Attacker’s perspective visibility
Understand what is exposed, accessible, and potentially exploitable.Risk-based prioritization
Focus on issues based on real-world impact and likelihood of exploitation.Controlled expansion of environments
Ensure new systems, cloud workloads, and integrations do not introduce unmanaged risk.Reduction of exploitable entry points
Minimize opportunities for attackers by securing and managing exposure continuously.