Scenario 1: Imagine a busy Monday morning at Zylker. In the Asia-Pacific region, the CRM system suddenly goes offline during a crucial sales window. The regional team feels the impact immediately, but since APAC contributes only a small fraction of Zylker’s global sales, the disruption—while inconvenient—poses no imminent threat to the company’s overall business continuity.
Scenario 2: Now, consider another scenario unfolding simultaneously: Zylker’s global endpoint protection platform (ERP) system begins lagging. It’s not a complete outage, yet the slowdown cascades across every department globally from sales and finance to logistics and delivery management, thus delaying shipments, invoicing, and business-critical workflows.
Which of these situations would qualify as a SEV‑1 incident? If you chose the second one, the ERP degradation, you are right. The key reason lies in impact. A SEV‑1 is not defined by whether a system is fully down, but by how deeply it harms critical business operations. A localized, complete outage might rank lower than a global slowdown if the latter halts critical operations that supports enterprise performance.
This difference makes it clear that definitions for incident severity need to focus on criticality and the scope of impact. They should not depend on subjective measures such as short-term revenue inputs or sales figures from specific regions. In times of high stress, IT teams can use such criteria based on impact, to resolve incidents quickly and contain the incident from affecting other enterprise operations and processes.
In this guide, we’ll discover how Zylker’s IT team structured its incident severity framework to triage complex disruptions efficiently. We’ll break down what severity levels mean, how can they be categorized, and what principles organizations should follow when tailoring severity definitions to align with their business priorities.
Key takeaways
This guide will equip readers with the knowledge to:
- Standardize triage: Master the art of categorizing disruptions through a structured severity framework to ensure the right resources hit the right problems.
- Prioritize with purpose: Understand how to define severity levels that reflect actual business impact, moving beyond technical metrics to operational reality.
- Align stakes with urgency: Connect incident response strategies directly to business priorities, ensuring high-stakes issues receive immediate attention.
- Build a scalable framework: Adopt a methodology for creating severity categories that grow and evolve alongside your organization’s IT infrastructure.
What is incident severity level?
Incident severity levels indicate and quantify the impact of an IT incident on the business, users, and operations, providing a clear, standard language that allows technicians and stakeholders to quickly understand the incident's criticality. Incident severity levels act as an input for determining the priority level of incidents, helping incident response teams (IRTs) triage and respond to the incident that matters the most.
Like the case with Zylker, where a sluggish application issue impacted its business revenue, clearly defining severity levels is essential. It is also crucial for the definitions to fit your specific business and team dynamics, ensuring that critical incidents receive immediate attention.
Now that we understand incident severity levels, let's see how these levels are defined and look at Zylker's examples for each of the severity levels.
Definition and classification of incident severity levels:
Before we dive into the different incident severity levels, it is worth noting that not every organization uses all five severity levels. The application of these severity levels can vary depending on different factors like team structure, the industry, and more. While some organizations might stick to the full scale, other organizations and IT teams might keep it to just a few levels that work best. With that in mind, let us take a look at the different severity levels and what each of them denotes.
| SEV type | Description | Example |
|---|
| SEV 1 | A SEV-1 incident signifies a critical outage of a core business system or service, resulting in a severe impact on day-to-day IT operations. | Complete outage of the primary ERP or the CRM system, a successful ransomware attack or major data breach that compromises sensitive company or customer data. |
| SEV 2 | A SEV-2 incident is usually major disruptions to a significant business service or system but isnt as devastating as a SEV-1 incident. | Partial outage of a key service that affects a major department like the inventory or ordering system, the VPN or remote access service being down for a large group of remote employees, the active directory service experiencing intermittent login failures for many users. |
| SEV 3 | A SEV-3 incident is defined as having a moderate effect on an organization's operations; usually affecting non-critical functionalities within core systems and significantly hinders business productivity. | A single shared network printer is offline in one department, a common application bug causes users to need a work-around to complete a minor, non-core function, internal Wi-Fi performance is degraded in a specific area, but a wired connection is available. |
| SEV 4 | A SEV‑4 incident represents a low‑priority issue that causes minimal or no disruption to normal service operations. | Performance issues with an internal analytics dashboard or a development/testing environment that is not customer-facing, a minor, non-critical firmware update failed on a small batch of workstations, performance degradation on a backup server that is currently running successfully but below optimal speed. |
| SEV 5 | A SEV-5 incident are issues which are purely informational, aesthetic, or administrative and don't affect system functionality. | A broken hyperlink on the internal self-service portal, a typo in the automated email signature of the service desk tool, minor cosmetic issues in a non-essential application's UI like an incorrect logo size or color scheme on a tool. |
1. SEV-1: Critical outage with high Business Impact
Definition: A SEV-1 incident signifies a critical outage of a core business system or service, resulting in a severe impact on day-to-day IT operations. Such an incident can cause potential financial and reputational damage to the organization. Swift actions to resolve such an incident is key to avoiding irreversible damage.
Zylker example: The complete and unexpected slowdown of Zylker's ERP system across major business units is categorized as a SEV-1. The incident sabotaged Zylker's sales, marketing, and customer support teams, preventing them from accessing crucial customer data, processing orders, and resolving customer issues. This directly impacted revenue and customer satisfaction. To restore operations to normalcy, the IT team should adopt an all-hands-on-deck approach and immediately initiate incident response.
2. SEV-2: A significant Incident with substantial Business Impact
Definition: A major disruption to a significant business service or system is referred to as a SEV-2 incident. Although not as devastating as a SEV-1, it nevertheless has a significant impact and might have an effect on several teams or important business operations. A prompt resolution is necessary to reduce additional disturbance.
Zylker example: A SEV-2 incident is a partial system outage and only impacts a division in the organization, such as the logistics application failing entirely or preventing access to lead management. Alhough parts of the service might continue to work, the impacted areas make it much more difficult for the sales or logistics teams to conduct their primary duties, which can result in delays and possibly unhappy customers. The IT team still needs to mobilize a significant part of its workforce to respond to SEV-2 incidents.
3. SEV-3: An incident with moderate impact
Definition: A SEV-3 incident has a moderate effect on Zylker's operations; it usually impacts non-critical functionalities within core systems and significantly hinders business productivity.
Zylker example: SEV-3 describes situations in which the CRM application has minor bugs, performance issues (such as slow loading times or inability to upload attachments greater than 5MB, or certain nonessential features that stop working). Users can still typically complete their primary CRM tasks, but these problems make them less productive and often more irritable.
4. SEV-4: A minor Incident with very low operational impact
Definition: A SEV‑4 incident is a low‑priority issue that causes minimal or no disruption to normal service operations. These incidents typically involve minor functionality degradation or configuration anomalies within non‑critical systems, features, or user interfaces. Core business processes, service continuity, and user productivity remain largely unaffected, and a stable workaround or alternate method is readily available.
Zylker example: Within Zylker's internal HRMS portal, the "Export to PDF" feature does not work for a subset of users. Alternative ways of exporting, like to CSV or DOCX files, run without any problems. This counts as a SEV-4 level issue because it affects a non-critical part of the system. In such SEV-4 scenarios, a solid workaround already exists, and business operations and targets stay pretty much unaffected.
5. SEV-5: Minimal to zero impact
Definition: A SEV-5 incident is the lowest impact level. These issues are purely informational, aesthetic, or administrative and don't affect system functionality. SEV-5 incidents are cosmetic flaws like UI misalignment or typographical errors. They require minimal intervention and can be fixed during routine maintenance.
Zylker example: A minor typographical error shows up in a lesser-used section of Zylker's internal knowledge base or a minor visual glitch inside an administrative dashboard that does not get in the way of how things run. All of it falls under a SEV-5 incident. Teams log these incidents for fixes down the line and handle them when time allows to ensure resources go towards mission critical incidents.
What’s the difference between incident severity, impact, and priority?
While closely related and often misused, severity, impact, and priority are distinct elements crucial for guiding your response. They are not the same and rather, are complementary metrics that guide the urgency and speed of resolution.
Severity and impact
Impact defines the extent and consequence of an issue, who and what services are affected. The incident severity level (often classified as SEV-1 through SEV-5) is the formal classification given to an incident based on that impact. It measures the degree of operational and business damage done to a service or IT component. Simply put, the severity level answers the question, "How bad is this incident for the organization?" A high severity (for example, SEV-1) signifies a critical incident with very high impact, such as a complete outage of a customer-facing service.
Priority and urgency
Priority, on the other hand, indicates how fast an incident must be resolved—the level of urgency required to begin resolution. It dictates the order in which incidents should be addressed. Priority is often calculated by combining the incident’s Severity (Impact) with a secondary factor of time-sensitive Urgency.
While severity and priority often overlap, a SEV-1 outage that brings down a core CRM system would also be assigned High Priority. They can also diverge as, for example, when a minor typo or a broken image on your organization's primary marketing page might be of very low technical severity (for example, a SEV-4 or SEV-5) because no core functionality is lost. However, due to the high visibility and negative impact on brand perception, the fix must be deployed immediately, making it a high priority issue. Ultimately, clear incident severity levels provide the core data that feeds into your priority matrix, helping your team determine the necessary response speed and resolution order.
Why defining incident severity level is essential for effective incident management
Defining incident severity levels is fundamental to effective incident management because it establishes a uniform, organization‑wide understanding of how different types of incidents affect business operations and dictate response urgency. A well‑structured severity framework enables IT teams to assess impact and urgency objectively, ensuring incidents are categorized, escalated, and resolved according to their true business risk.
- Enable structured response planning: Defined severity tiers help the IRT and related stakeholders follow a consistent escalation path. Predefined playbooks can be activated based on severity, ensuring that diagnostic procedures, containment measures, and communication workflows are executed in the correct sequence for that category of impact.
- Facilitate optimal resource allocation: Severity‑based classification allows teams to allocate technical expertise, monitoring tools, and recovery efforts proportionate to the incident’s criticality. For instance, if Zylker’s ERP slowdown were classified as SEV‑1, the major incident response process would automatically engage senior engineers and service owners, preventing resource waste on lower‑impact events.
- Enhance communication and stakeholder alignment: Clearly defined severities streamline internal and external communications during disruptions. A SEV‑1 declaration triggers immediate, transparent updates to key stakeholders, improving situational awareness, accountability, and customer trust.
- Support trend analysis and continual improvement: Maintaining consistent severity data across incidents enables post‑incident reviews, root cause analysis, and service quality reporting. Over time, this data contributes to better risk forecasting and improved SLA/SLO adherence.
Conclusion
Zylker's journey from a chaotic CRM crash to a smooth-running incident management system is an excellent illustration of how important it is to set clear levels of incident severity. Zylker's IT team was able to work on future incidents more strategically by establishing the right criticality, no matter how they affected things right away.
Incidents involving IT are unavoidable. However, the mayhem they cause need not be. Organizations can change their IT operations from reactive firefighting to proactive, strategic problem-solving by comprehending, defining, and rigorously applying incident severity levels. In addition to protecting your systems and financial results, this increases customer trust and enables your IT staff to act as genuine business enablers.
Zylker's experience is a strong case study in the importance of clearly defining incident severity levels. After the CRM crash at Zylker, which caused enterprise-wide chaos, its IT team learned a valuable lesson that not all incidents should be handled equally. The team also discovered that a one-size-fits-all approach to incident resolution leads to resource misuse and prolonged downtime.
By establishing clear incident severity levels, Zylker's IT team now has a defined incident response plan for every severity level with the roles and responsibilities clearly delineated. Your approach to defining incident severity levels should start with defining the number of severity levels required to clearly classify incidents, differentiate between partial and complete outages, and ultimately keep it simple since overly complicated incident severity levels might confuse your team.
Frequently asked questions
Expand all
1. Why does your organization need incident severity levels?
Incident severity levels help classify incoming incident tickets based on their urgency and impact on the organization's everyday operations. This helps IT leaders prioritize the right tickets to minimize the impact on business operations.
2. How does an incident severity matrix work?
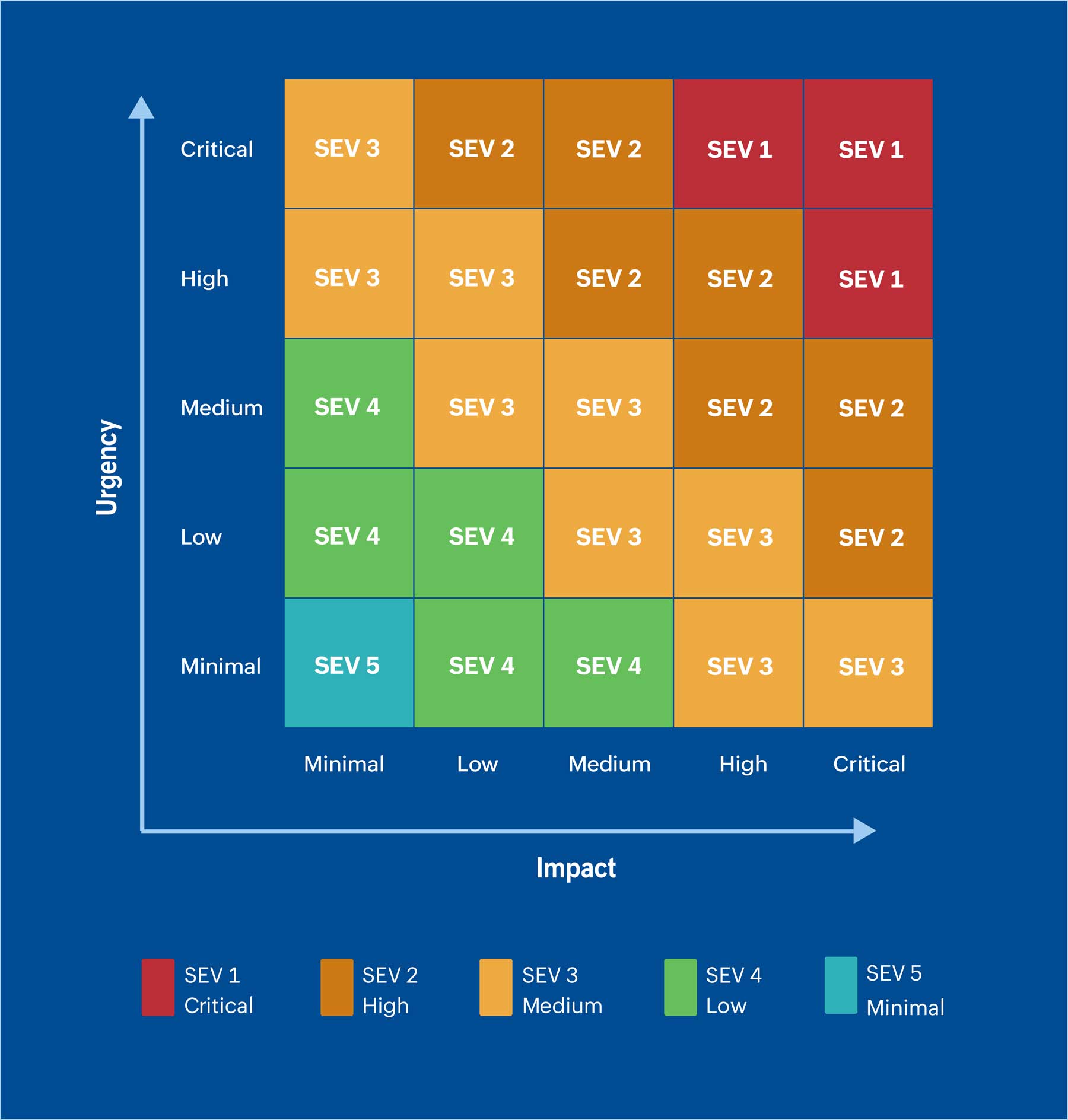
An incident severity matrix is used to classify an incident by referencing the impact of the incident against its urgency. When visualized as a graph, the horizontal axis represents the impact, while the vertical axis represents the urgency. The section where both the impact and urgency intersect determines the final severity level of the incident, removing the guesswork and helping teams expedite the resolution accordingly.
Incident severity matrix3. What is the difference between incident response and incident management?
In ITSM, incident response and management are related but distinct in their scope and focus.
Incident response: This a hands-on approach that involves detecting, triaging, and resolving incidents. For example, when a server stack goes down due to a memory overload, the incident response here would be the process of restoring the server to normal operation at the earliest.
Incident management: Incident management covers everything related to resolving an incident, from ticket creation, standard operating procedures, tasks undertaken by the incident response team, and defining the SLA, to conveying the resolution and documenting it in the knowledge base for future reference. For example, an end user reports that the e-commerce website's checkout page is down. The developer receives an alert, identifies a failed database connection as the root cause, restores the service within 20 minutes, and logs the resolution into the knowledge base for future reference.