The increase in the number of dependencies in a supply chain has extended the attack surface for adversaries. Attackers have come up with various techniques to exploit different components of the supply chain.
I hope the first part of this blog series helped you understand the fundamentals of supply chain attacks. In this second part, we will discuss the various types of supply chain attacks with relevant use cases. We will be covering:
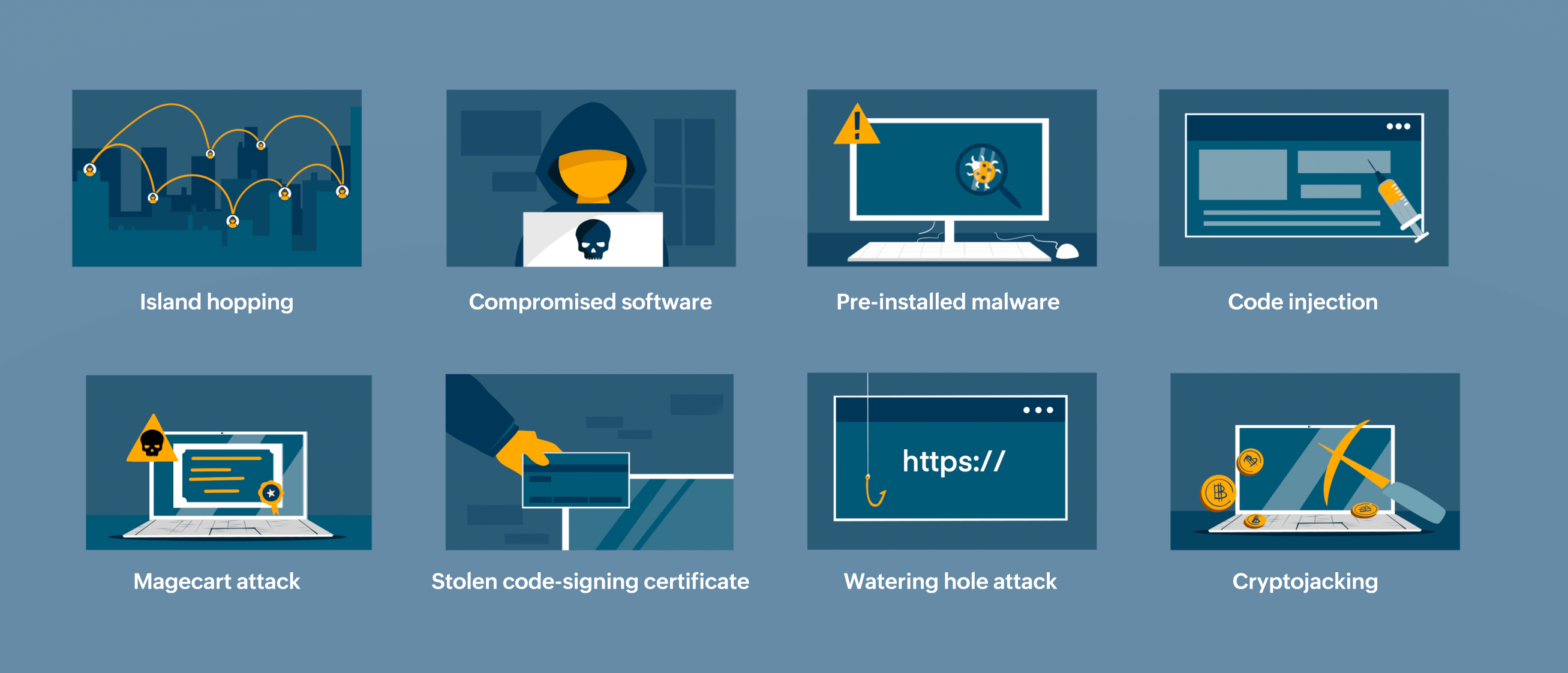 Fig 1: Types of supply chain attacks
Fig 1: Types of supply chain attacks
Island hopping, Compromised software, Pre-installed malware, Code injection, Stolen code-signing certificate, Magecart attack, Watering hole attack, Cryptojacking
Island hoping is a form of third-party attack, where an indirect route is pursued by adversaries to attack a high-end target with sophisticated network security. Since attackers cannot overcome the target's tight security defense, they exploit the weak links in its software supply chain. They victimize vulnerable vendors and third parties in the target's supply chain to gain initial access to the target's network and compromise resources. In a way, the adversaries hop from one organization to another, and so the attack is called an island hopping attack.
For instance, in September 2017, CC Cleaner, a free cleanup tool, was compromised with a backdoor just before Avast, a security company, acquired it. Threat actors, instead of directly targeting Avast, indirectly infiltrated CC Cleaner to hop into Avast's network.
In this type of attack, threat actors directly target the victim organization by exploiting vulnerabilities in its software products. By introducing malware in the software's build cycle, adversaries open backdoors in the downstream supply chain, and all the customers of the target organization who download the product fall prey to the adversaries.
The infamous SolarWinds attack of 2020 was a compromised software attack where nation-state threat actors implanted a backdoor in a software update of a SolarWinds application. The malicious software spread across 18,000 customers who downloaded the update, including United States (US) government agencies.
This is also a type of third-party attack where the adversaries install malicious software on network devices or other electronic devices of third parties to cause distress to the target organization. The victimized third party as well as the target are unaware of such infiltration until the malware slowly and quietly takes over the target's network.
In 2013, Target, a US retailer, was subjected to this type of supply chain attack, where about 40 million customers' credit and debit card details were made public due to pre-installed malware on its point-of-sale (POS) system. Later investigations revealed that the POS system was infiltrated using credentials stolen from a third-party provider of heating, ventilation, and air-conditioning systems.
Code injection is a form of open-source attack targeting open-source code repositories and libraries. By injecting malicious code into code libraries and repositories, attackers target all legitimate users who access such repositories. JavaScript libraries that automatically execute code on user devices are one of the prime targets of attackers.
In 2021, Browserify, an open-source Javascript tool, was subjected to a code injection attack that targeted Linux and macOS operating systems. Attackers used a technique called brandjacking to persuade users to download software containing malicious code. It was a massive supply chain attack that affected 1.3 million users who downloaded Browserify. Luckily, the situation was proactively contained within a day.
A Magecart attack, also known as formjacking, is a type of code injection attack mostly directed towards third parties handling payment methods. In this attack, hackers inject malicious code into the JavaScript code to take over a website and skim sensitive financial details from the checkout forms filled out by users.
Code-signing certificates are used to assess the authenticity and integrity of a software product. Threat actors steal such certificates by compromising the private key of the legitimate owner. Then, the attackers distribute malware-infested software along with the stolen code-signing certificates to lure users into downloading the malware.
The Mimecast attack of 2021 is a good example of a stolen code-signing certificate attack. The code-signing certificate Mimecast used to authenticate its services on M365 Exchange services was compromised by hackers, affecting 10% of customers who used Mimecast's apps.
Websites with huge traffic are the main targets of this type of supply chain attack. Websites are the final windows of a supply chain, serving as media to install and download software products. By identifying loopholes in the website's architecture and embedding malicious links, attackers lure end users into opening a backdoor for malicious executions. This attack is named with reference to predators (attackers) that hide near watering holes (website vulnerabilities) to pounce on the prey (victims) at the right moment.
Cryptojacking is another form of supply chain attack in which adversaries use the computational resources of users to mine cryptocurrency. Most cryptojacking attacks are carried out using infected websites. Attackers compromise a website by injecting malicious commands in the HTML code of the website's architecture. Whenever users open such websites, the mining program gets automatically executed and the users' resources are exhausted without their knowledge.
A double supply chain attack scenario arises when one supply chain attack leads to another supply chain attack.
The 3CX breach was one such double supply chain attack. In March 2023, 3CX, a VoIP software provider, reported a breach in its desktop application that affected Windows and macOS operating systems. The application was infected with malicious code that automatically compromised all machines that ran the application. 3CX hired Madiant, a cybersecurity firm, to further investigate the attack. Madiant's reports revealed the following:
The 3CX breach started much earlier when 3CX had fallen prey to the Trading Technologies supply chain attack. In 2022, Trading Technologies, one of 3CX's vendors, was subjected to a supply chain attack. Attackers compromised an installer that was used to install X_TRADER, a software package from Trading Technologies. 3CX's compromise began when a 3CX employee downloaded the infected X_TRADER software package. In continuation of this earlier supply chain attack, 3CX opened a backdoor for another supply chain attack. Madiant also stated that it was the first time it had seen a software supply chain attack leading to another software supply chain attack.
Software supply chain attacks have seen an epic increase of 742% between 2019 and 2022. And this year, 2023, is expected to be no better than the previous years. So stay tuned for the final part of this series where we'll cover the various measures you can take to detect and prevent supply chain attacks.
You will receive regular updates on the latest news on cybersecurity.
© 2021 Zoho Corporation Pvt. Ltd. All rights reserved.