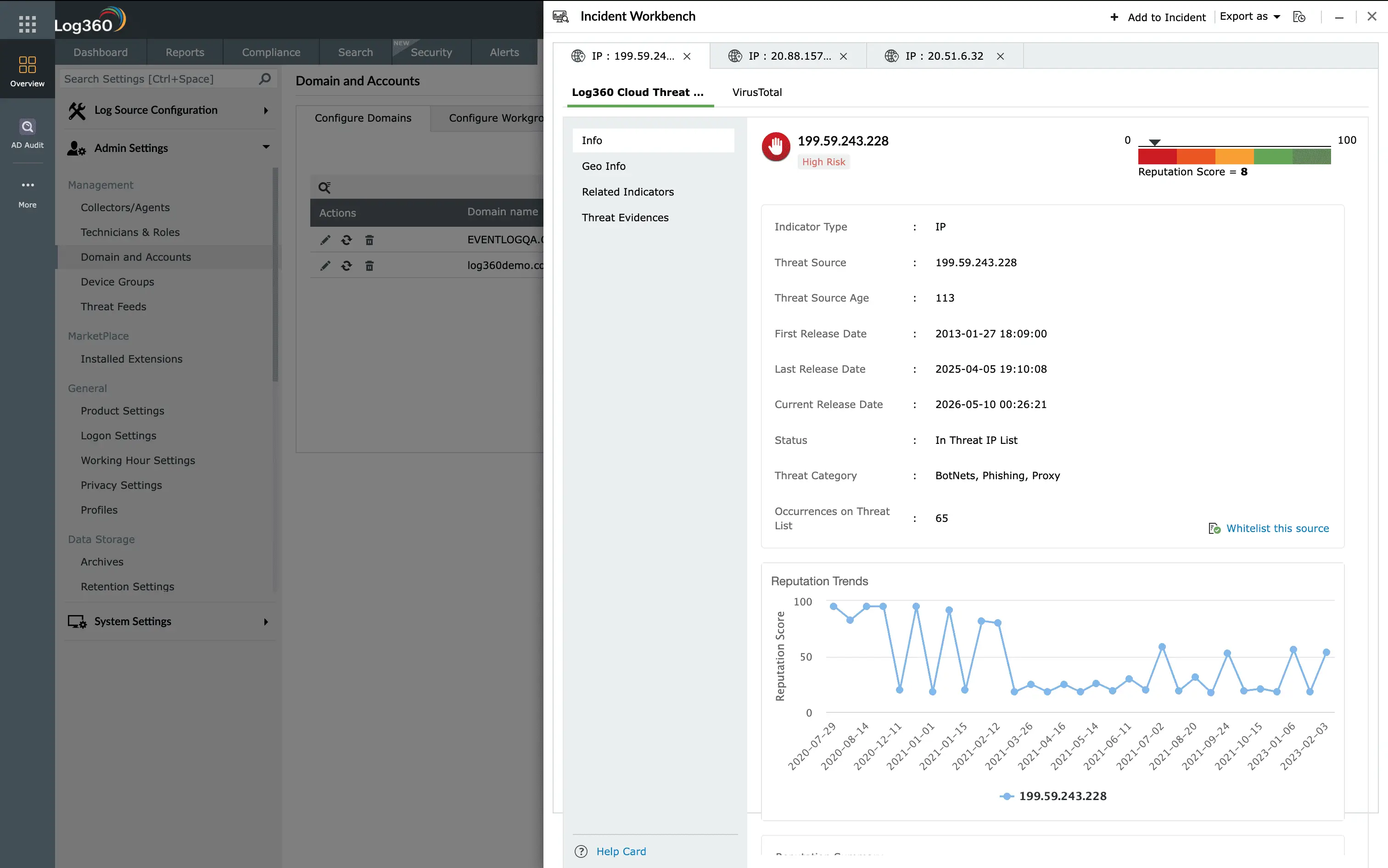
Threat intelligence
Enhance your automated workflows with actionable threat intelligence. Leverage global feeds from VirusTotal, AlienVault OTX, Webroot, FireEye, Symantec, and Malwarebytes to automatically strengthen SOAR playbooks with malicious IPs, domains, and file hashes.
Learn more
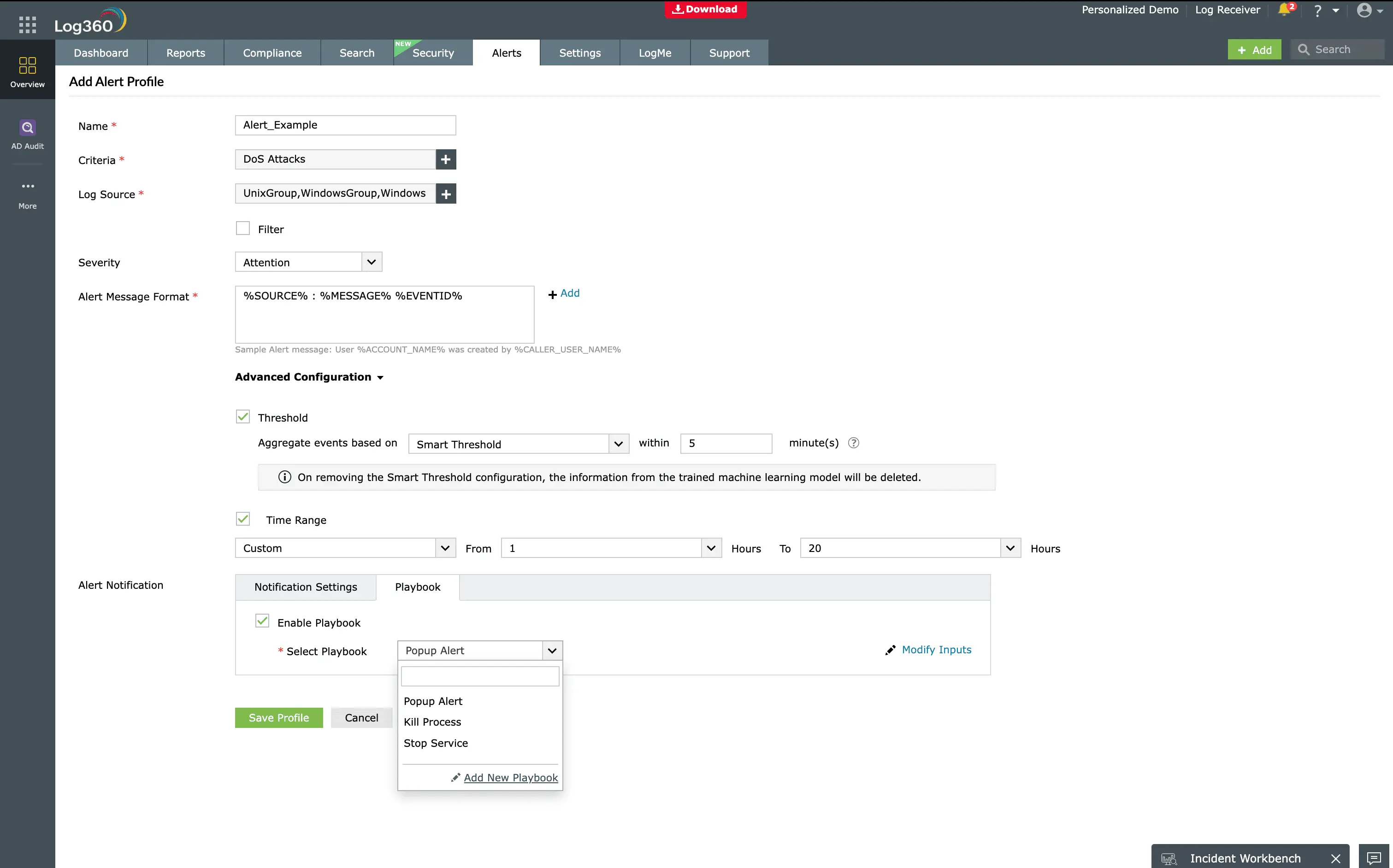
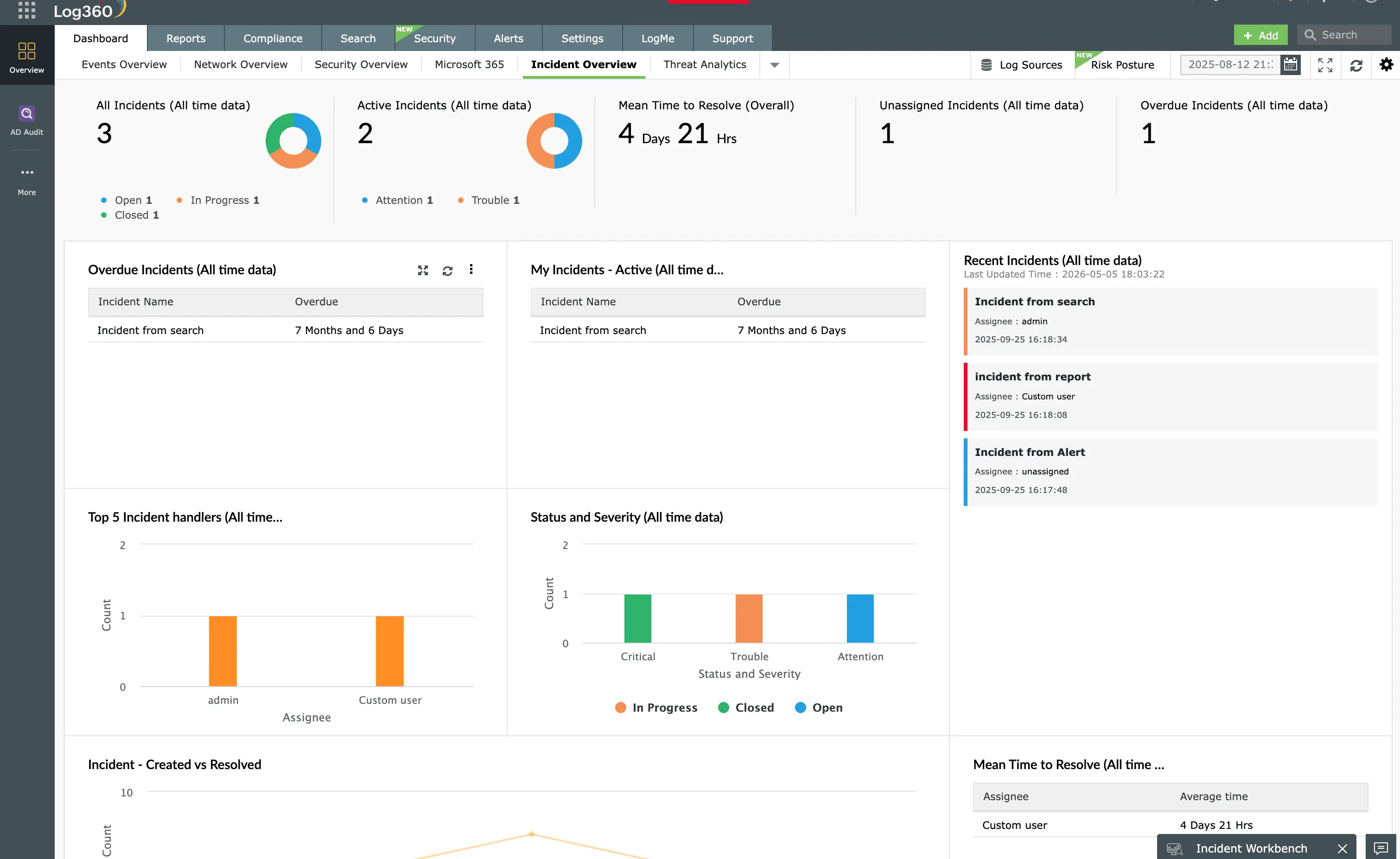
Automated incident response
Streamline incident response with SOAR-powered playbooks that orchestrate evidence collection, stakeholder notification, and remediation workflows while ensuring consistent, repeatable processes.
Learn more
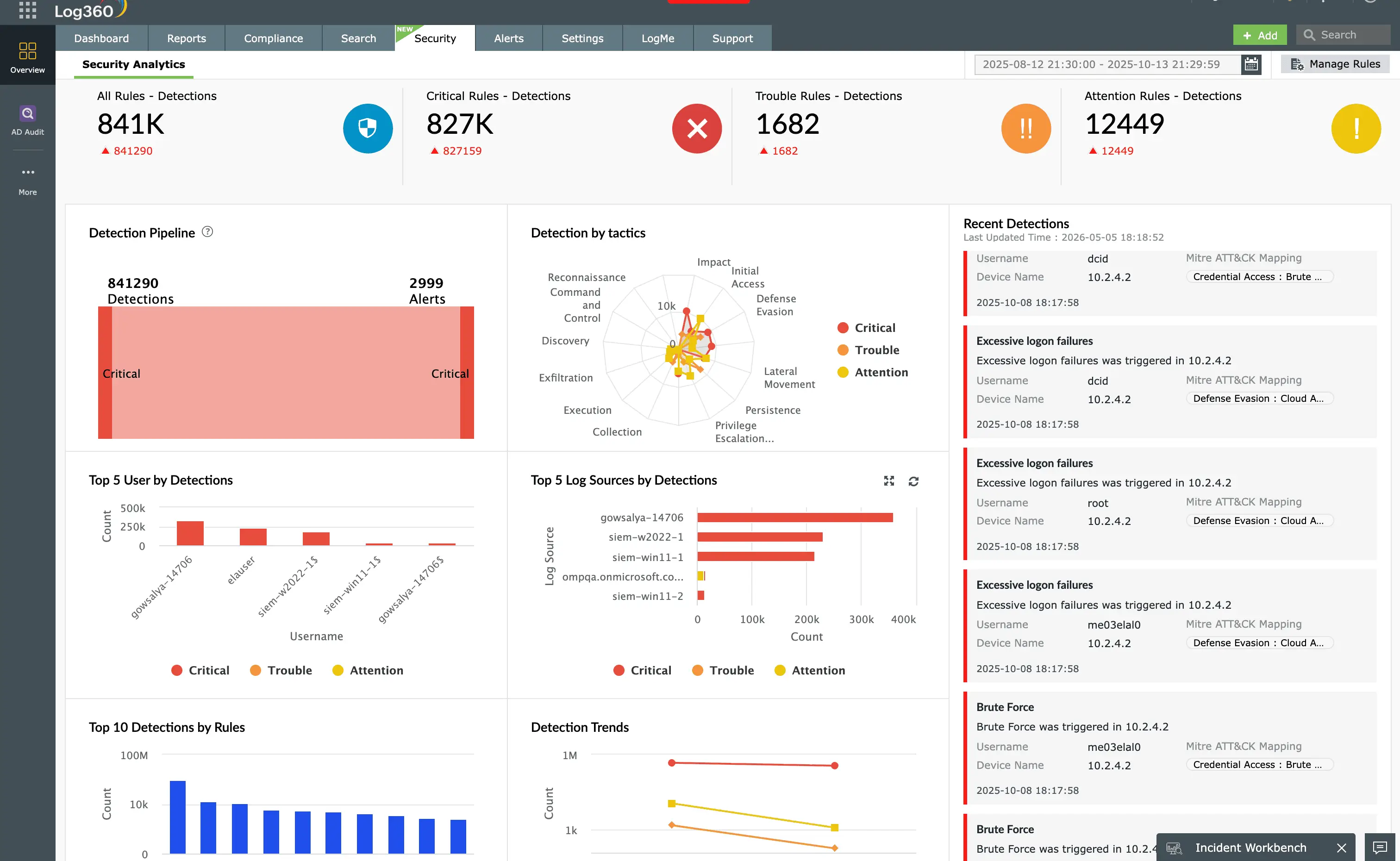
Advanced threat detection
Combine behavioral analytics, MITRE ATT&CK mapping, and correlation rules to identify sophisticated attacks and automatically triggers SOAR playbook when threats are confirmed for immediate orchestrated response.
Learn more
Integrated compliance management
Automate compliance workflows with playbooks that enforce policy controls, document remediation actions, and generate audit reports for PCI DSS, HIPAA, GDPR, SOC 2, and ISO 27001.
Learn more