- Home
- Play books
- Windows - File enrichment
Windows - File enrichment
In this page
Playbook Description
This playbook automates forensic analysis by retrieving hashes and querying VirusTotal for reputation data. It validates Authenticode signatures and identifies files in suspicious directories to determine origin. Based on these findings, it classifies the file risk level as high, medium, or low, streamlining the prioritization of potential security threats.
MITRE ATT&CK mapping
| Tactics | Techniques | Sub-techniques |
|---|---|---|
| Defense Evasion(TA0005) | Masquerading(T1036) | - |
| Defense Evasion(TA0005) | Subvert Trust Controls(T1553) | Code Signing(T1553.002) |
| Execution(TA0002) | User Execution(T1204) | Malicious File(T1204.002) |
MITRE D3FEND mapping
| Tactics | Techniques | Sub-techniques |
|---|---|---|
| (Detect) D3-Detect | (File Analysis) D3-FA | D3-FHA |
| (Detect) D3-Detect | (File Analysis) D3-FA | (File Content Analysis) D3-FCR |
| (Detect) D3-Detect | (Process Analysis) D3-PA | (Process Spawn Analysis) D3-PSA |
Playbook input type
Log
Prerequisites
- Windows Credentials - Go to Settings -> Devices -> Windows Devices.
- Provide/update the credentials of the respective Windows device with admin privileges.
Playbook creation input
- connectionName - Provide the VirusTotal connection name for executing the VirusTotal APIs.
Dependencies
Extensions:
- virustotal_fileReputation
- virustotal_calculateRiskScore
Utility:
- utility_extractMaliciousEntitiesByRiskScore
- utility_validateResponses
- utility_filterByStartsWith
- utility_filterByCriteria
- utility_convertToString
- utility_normalizeValue
Scripts
| Script Name | Description | Arguments |
|---|---|---|
| GetFileHash.ps1 | This script retrieves the hash of a specified file using the given algorithm. | FilePaths, Algorithm |
| GetAuthenticodeSignature.ps1 | Checks the Authenticode digital signature of one or more files. Returns whether each file is signable, whether its signature is valid, and signer certificate details (subject, issuer, thumbprint, validity dates) for validly signed files. | JsonPathList |
Connections
VirusTotal connection - Need to connect to VirusTotal API and fetch access key to check the malware IP/URL/file details.
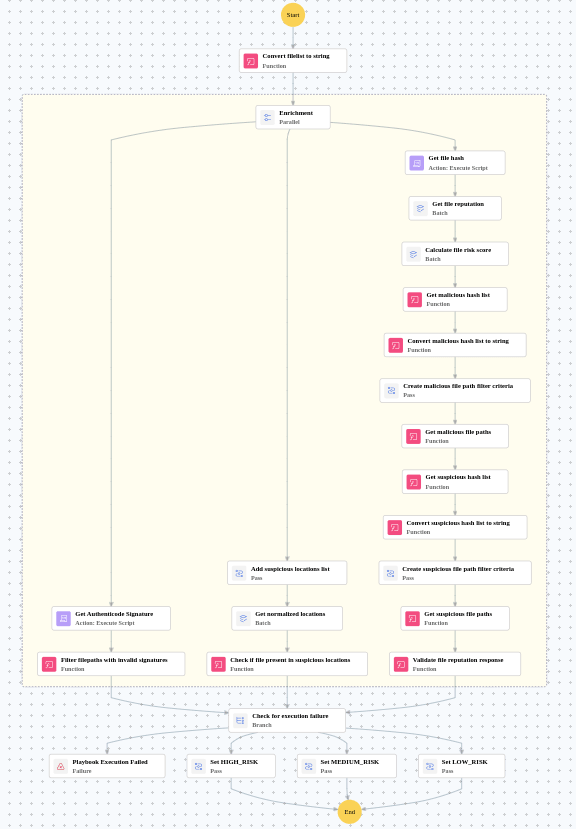
Execution workflow
- Converts file paths to string.
- Retrieves file hashes via PS script.
- Checks file reputation via VirusTotal and calculates risk scores.
- Classifies files as malicious (≥3) or suspicious (≥2).
- Maps hashes to file paths.
- Validates authenticode signatures.
- Normalizes paths and checks suspicious locations.
- Correlates signals to classify risk as HIGH, MEDIUM, or LOW.
Post execution procedure
If the file is confirmed to be malicious, block its execution and prevent access by non-admin users. Check and delete the file as required.


