The three Ps of compliance
The connections between people, processes, and products
“People perform processes to create products” accurately describes any business. Modeling this statement into a framework is where the key to effective governance, regulation, and control (GRC) lies. Below is a logical representation of this framework:
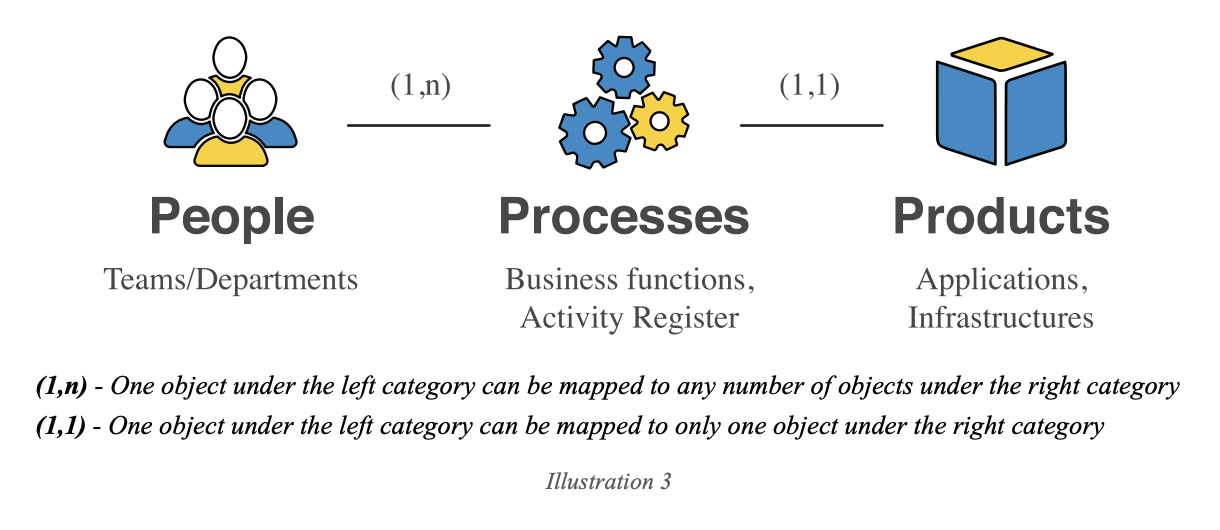
- People, Processes, and Products are entities. Each instance of an entity is an object. For example:
- Under People, an HR executive or a developer is an object.
- Under Processes, an activity (like hiring) or a business function (like product development) is an object.
- Under Products, an application or infrastructure that your company produces is an object.
- People (1,n) Processes: Each object under People can be mapped to any number of objects under Processes.
- One person or department can be involved in many processes. For example, an HR executive may be involved in hiring, onboarding, and grievance management. A marketer may be involved in lead generation as well as public relations.
- Why is it not “(n,1)”? Although it logically makes sense that more than one person or department may be involved in a process, that approach does not suit compliance. People always drive compliance by taking responsibility for the processes they are involved in. Every person in your organization must be mapped to a process. You may achieve this using the HR portal you use. Every user there must be able to see what processes they are mapped to.
- If an employee cannot be mapped to a process, they must receive more clarity on their role at the company.
- Processes (1,1) Products: Each object under Processes must be mapped to only one object under Products. Again, while it’s true that more than one process can be involved in making a product, the concept of a product is more inclusive when it comes to compliance:
- A product signifies any value that is created out of a process. It includes:
- The end product or service that customers pay you for.
- Components like software libraries, inventory of tools, asset registers, and even those crucial spreadsheets. These are products, too, because they are consumed by users within your organization.
- Every process produces some product that is either sold to customers or used internally in another process, eventually leading to the creation of the end product that your customers pay you for.
- If a process cannot be mapped to a product—in other words, it doesn’t produce any value—it should not exist.
The list of People, your HR portal, can be mapped to your list of Processes, which is your activity register. Also, your list of Products is the inventory of all value that your organization creates.
When you consolidate controls from certifications like ISO 27001 or a regulation like HIPAA, you can easily map which control corresponds to which entity. This clarity will help you decide how much effort you must put into each area to achieve the desired level of compliance.
Law
The GDPR, HIPAA, and the CCPA are laws that dictate how companies should process personal data. Any regulation stands on top of four pillars:
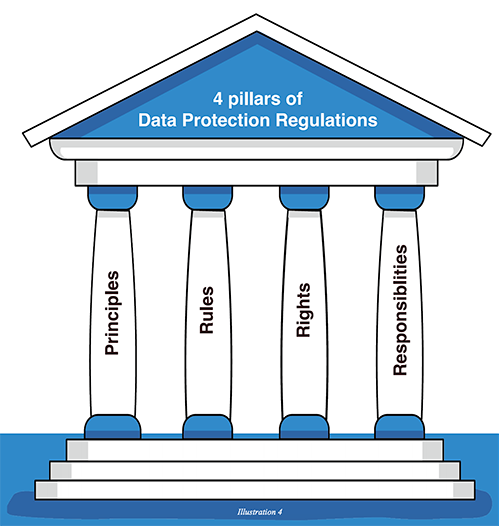
Principles: These are the values that the governing bodies want you to keep in mind and apply throughout your processes. In the GDPR, Chapter 2 (Art. 5-11) is entirely dedicated to the principles that must be followed while processing personal data.
- Lawfulness, fairness, and transparency: The GDPR gives you six lawful bases, and any processing (collection, usage, disclosure, and storage) must fall under one of those laws.
- Purpose limitation: You must collect and use the data for the stated purpose alone and only collect data for as long as necessary to complete that purpose.
- Data minimization: You must ensure that the personal data you process is adequate and relevant to what is necessary concerning your processing purpose.
- Accuracy: You must take every reasonable step to update or remove data that is inaccurate or incomplete.
- Storage limitation: You must delete personal data when you no longer need it.
- Integrity and confidentiality: You must keep personal data safe and protected against unauthorized or unlawful processing, as well as accidental loss, destruction, or damage, using appropriate technical or organizational measures.
Likewise, Brazil’s Lei Geral de Proteção de Dados (LGPD) lists 10 principles that should be taken into account when processing personal data, such as purpose limitation, necessity, transparency, security, non-discrimination, and accountability.
Principles come into play when you draft policies to govern your processes.
Rules: These usually describe what happens when you do not comply with the law, or they are the standing instructions when you comply with it. For example, Art. 83 of the GDPR describes how much organizations will be fined based on the kind and severity of the breach they face. Rules also describe the actions that you need to take to ensure that principles are implemented.
Likewise, Section 1798.155(a) of Title 1.81.5 in the CCPA describes the penalty for violating the act. Other rules describe how to respond to breaches and how to inform data subjects.
Rules come into play when you draft and standardize procedures for your processes.
Rights and responsibilities: Chapter 3 of the GDPR lays down the rights that data subjects have, and Chapter 4 describes the responsibilities organizations have when they assume the role of controller or processor.
Both rights and responsibilities affect your organization’s processing activities.
For example, the “right to be forgotten” in the GDPR will change the way you process data. You will realize that you can no longer send multiple support emails distributed in multiple inboxes. A consolidated help desk system can ensure that all data corresponding to a support ticket is in one spot so when the right to be forgotten is invoked, all you have to do is focus on the help desk rather than multiple individual inboxes.
Standards
Standards are what help a customer in the US buy a meter of cloth from a vendor in Asia. Thanks to one such standard, the International System of Units, people around the world can understand each other's expectations without complications.
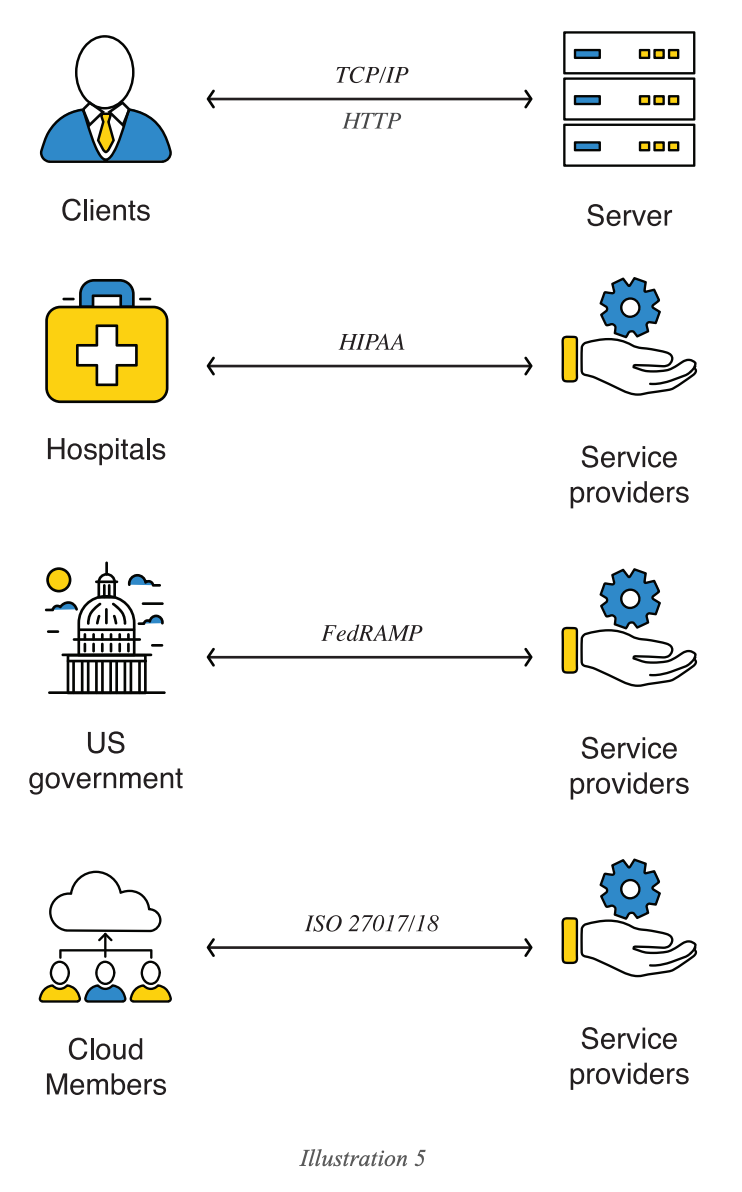
All communication needs a standard to be effective. A server understands a client through Transfer Control Protocol (TCP). Likewise, the US government understands service providers through FedRAMP. When a service provider gets certified with standards, users will know what to expect of the service provider and will not have to personally test the provider’s processes to ensure consistency.
Standards have a set of definitions, controls, and requirements that need to be fulfilled so that consistency is established among all parties.
Complying with standards is a matter of understanding the definitions and mapping a standard’s controls to your processes. Controls, here, are measures or certain activities that standards expect you to carry out. There are two cases:
- If the standard requires a control that isn't part of your process, you can either try to include it in your process or provide sufficient justification that the absence of such a control does not affect the expectations of customers.
- If the standard requires a control that is part of your process, you must gather sufficient evidence that the control is executed effectively and efficiently.
Audits
Audits determine what you lack with regards to a particular standard. In that sense, internal and external audits are the same. However, the need to focus more on internal audits arises from the problem of scaling. Consider an example:
Zylker, after great efforts, gets its first ISO 27001 certification. However, it wants to expand further to SOC, PCI, and other ISO standards like 27017 and 27018. External audits will be happening throughout the year if Zylker is to receive that many certifications.
Is it practical for Zylker to conduct internal audits for every standard they choose to comply with that is about to happen? Each product and operations team must dedicate many man-hours for both internal and external audits, and this may become a hindrance to productivity, which defeats the whole point of process control. So, what is the solution?
Consolidate the audit requirements into a list of controls. List every expectation you have of teams with regards to these standards, and create a consolidated list of controls.
Then, you can schedule two or three internal audits per year to evaluate the teams' current process against the desired set of controls, as follows:
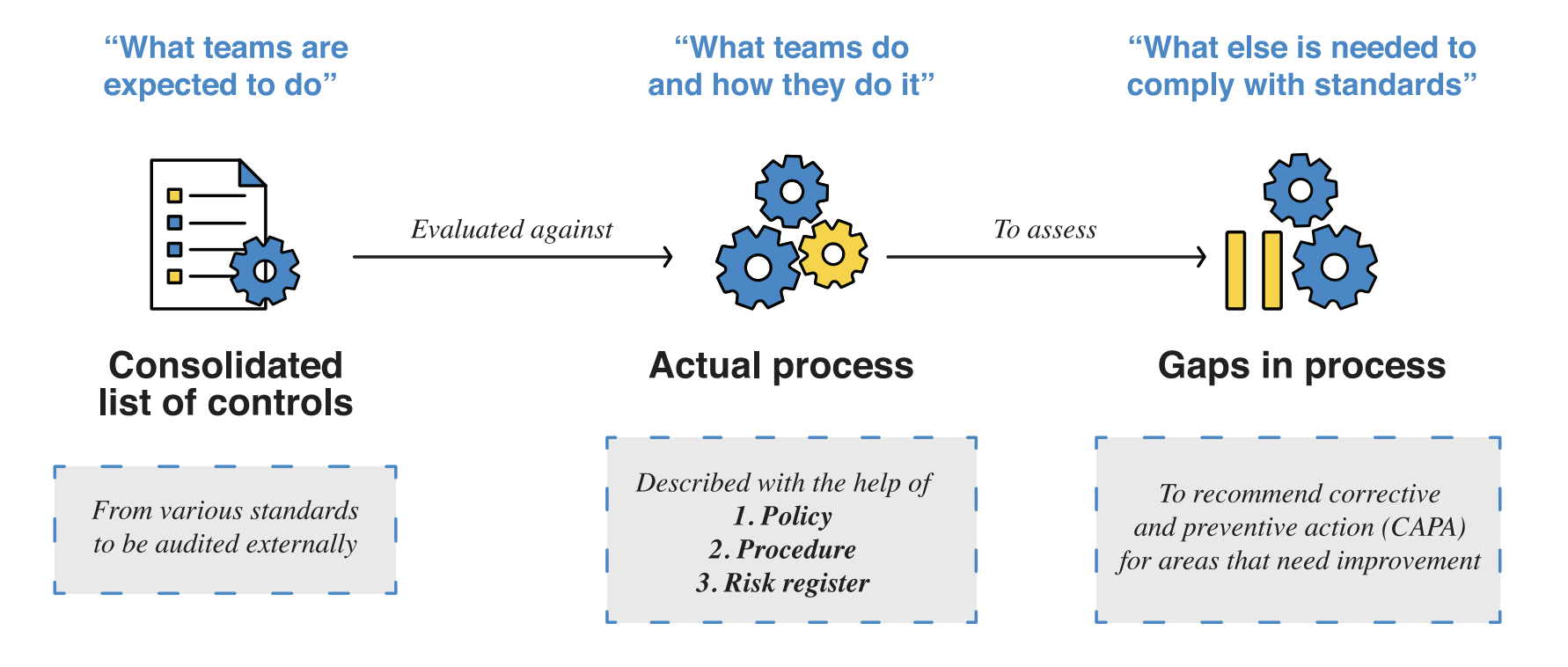
The internal audit then goes on to collect evidence for the gap assessments and the implementation of CAPA. This evidence must include everything, including email communications, screenshots of processes, and audit logs, to prove the actual process’s compliance with standard controls.
ZOHO STORY
Zoho and audits: As we expand our compliance portfolio, there is always another audit around the corner. Although the initial audits were challenging, we were able to include an “audit readiness” section in teams' processes to keep them in the loop and set them up for external audits.
The initial struggles also helped teach us how different each standard is. ISO audits like ISO 27001 focus heavily on the organization's information security management system (ISMS), while SOC 2 focuses on system-level controls with special attention to data protection. From an audit perspective, these standards seem to be miles apart; but from a process perspective, one can consolidate them into a system of controls. In fact, if an organization’s process control is efficient and effective, compliance with any standard could merely become a matter of extrapolating on existing processes.
To face multiple external audits throughout the year, an organization’s internal audit framework needs to be robust. That is why a framework-based approach is the best way to sustain compliance.
