Manage Chrome Extensions with Browser Security Plus' Extensions Manager
Chrome Extensions manager is a feature that IT admins can use to keep track of Chrome extensions used by employees in their organization Based on the insights they can remove Chrome extensions that are unnecessary. With Browser Security Plus' Chrome extensions manager feature, IT admins can take inventory of Chrome extensions present on users' browsers, detect the ones that are potentially harmful and remove extensions that aren't necessary. IT admins can also enforce mission-critical extensions needed for day-to-day tasks to employees browsers from a central console.
Need for Chrome extensions management.
Chrome extensions management is the process of keeping track of Chrome browser extensions present across an organization and subsequently remove those that are not required. Google Chrome stands tall with market share of 64.62%. Most people prefer using Chrome browser to browse through the web. To enhance their browsing experience, users depend on add-ons. Chrome hosts a store online from where users can install extensions on their browsers. Each of these extensions are aimed to fulfill a functionality that is not built-in within the browser. To render the intended functionality, these extensions require permissions to interact with the browser.
For example, an extension that is aimed at correcting grammar, would require "read and write" permission to read the contents present in the web page and to make changes when necessary. Cybercriminals can use extensions, to gain access to users' browsing patterns, account credentials and Personally Identifiable Information (PII) that users provide across websites. With businesses increasingly being carried out on the browsers, these extensions are being granted access to business data well. IT admins have no way of ensuring the security of sensitive enterprise data.
Need for Chrome extensions permission-management
Browser permissions when granted to the extension, are capable of causing data breaches for the organization. In order to protect employees' PII and their enterprise's sensitive information, IT admins need to keep track of the extensions used in their network to weed out the extensions that could be potentially malicious in nature. Browser Security Plus can be used to:
- Discover such potentially harmful extensions being used in your network.
- Remove unnecessary extensions.
- Block permissions directly, instead of extensions. This will ensure that all Chrome extensions that make use of the blocked permissions will in turn be removed.
Steps to manage Chrome extensions
IT admins can use Browser Security Plus to track the Chrome extensions present in their network, restrict access to specific extensions and distribute extensions from a single console. To manage Chrome extensions in enterprise network, follow the below steps:
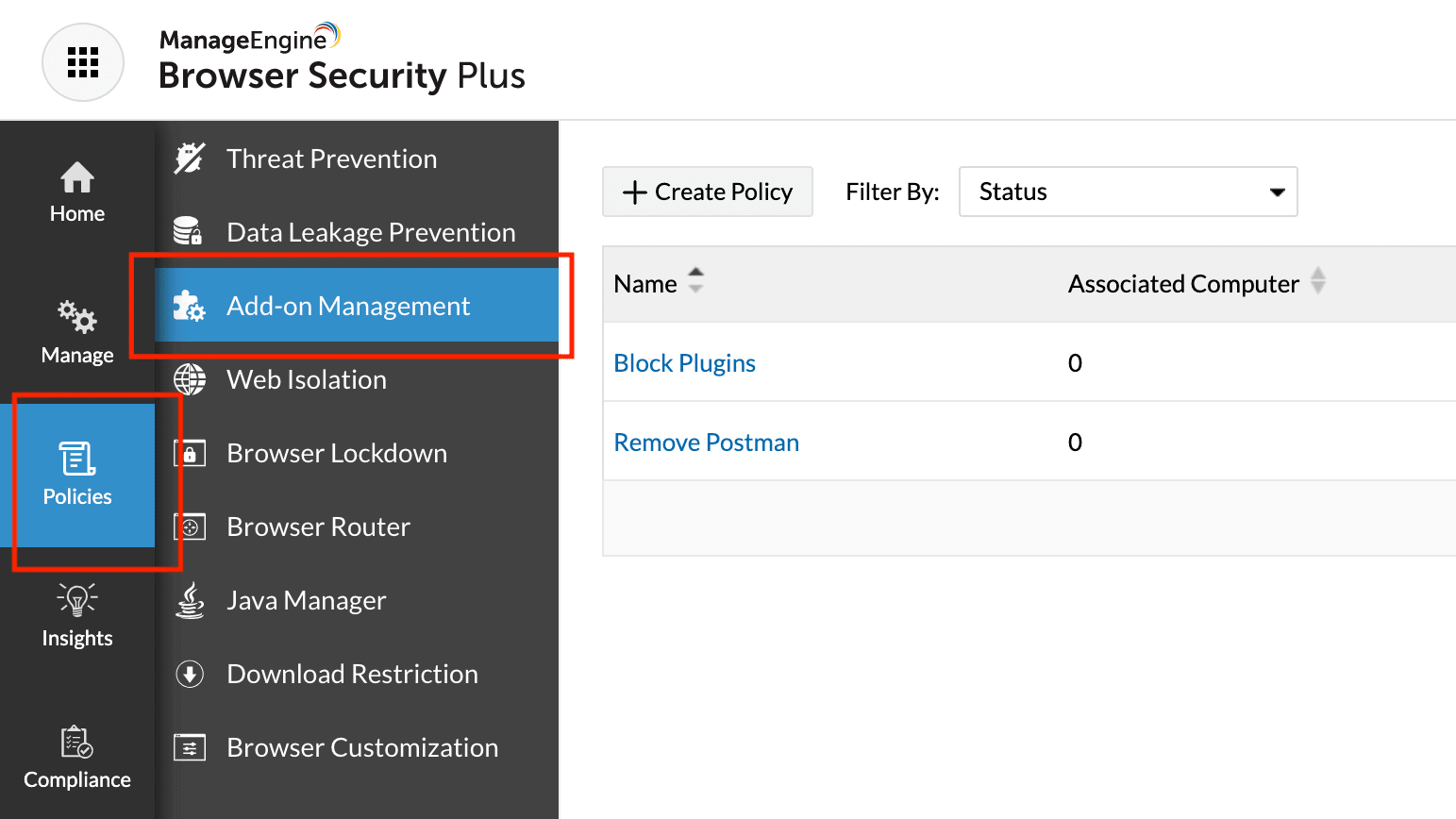
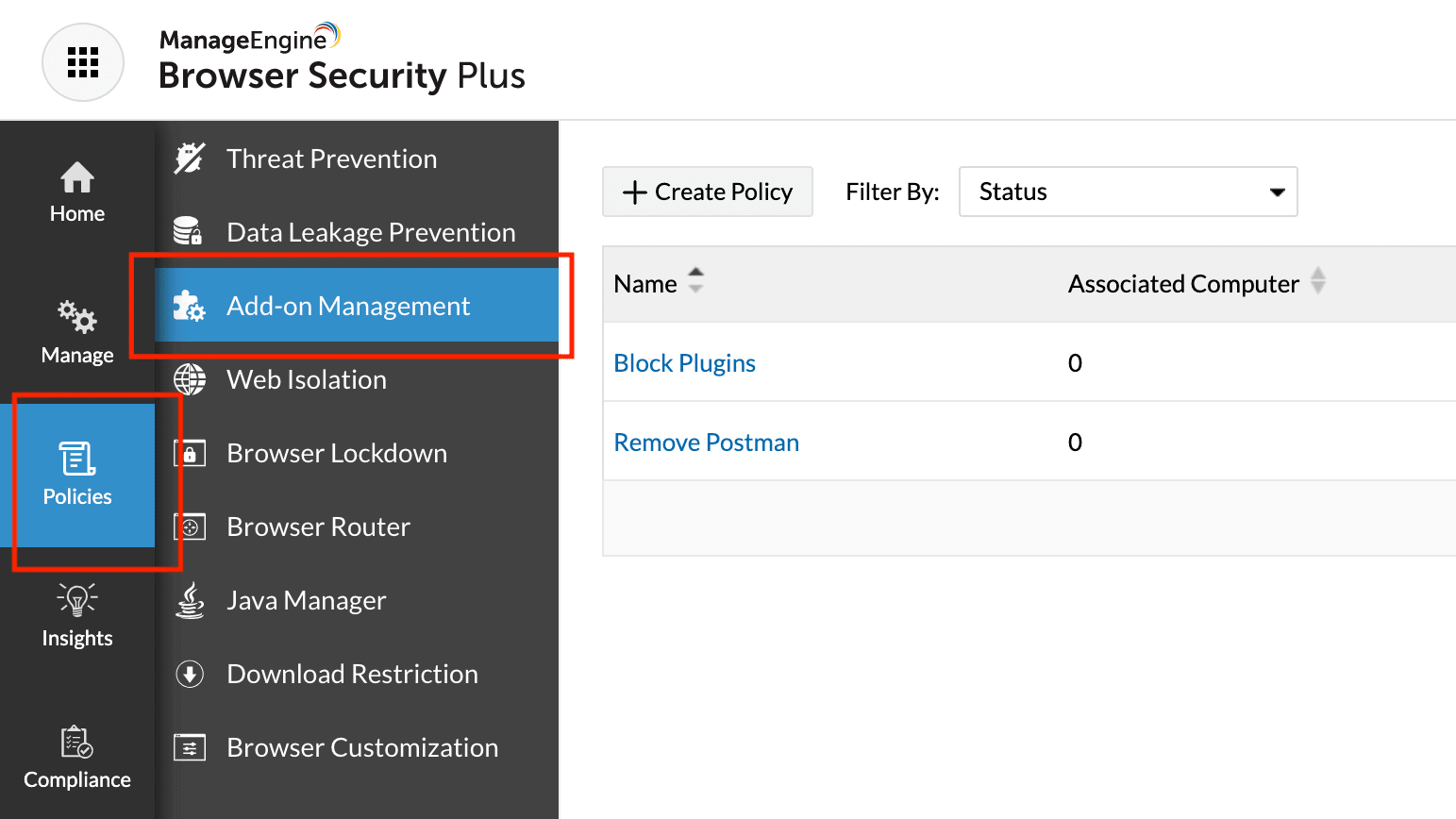
Step 1: Navigate to policies and click on Add-on Management in Browser Security Plus console.
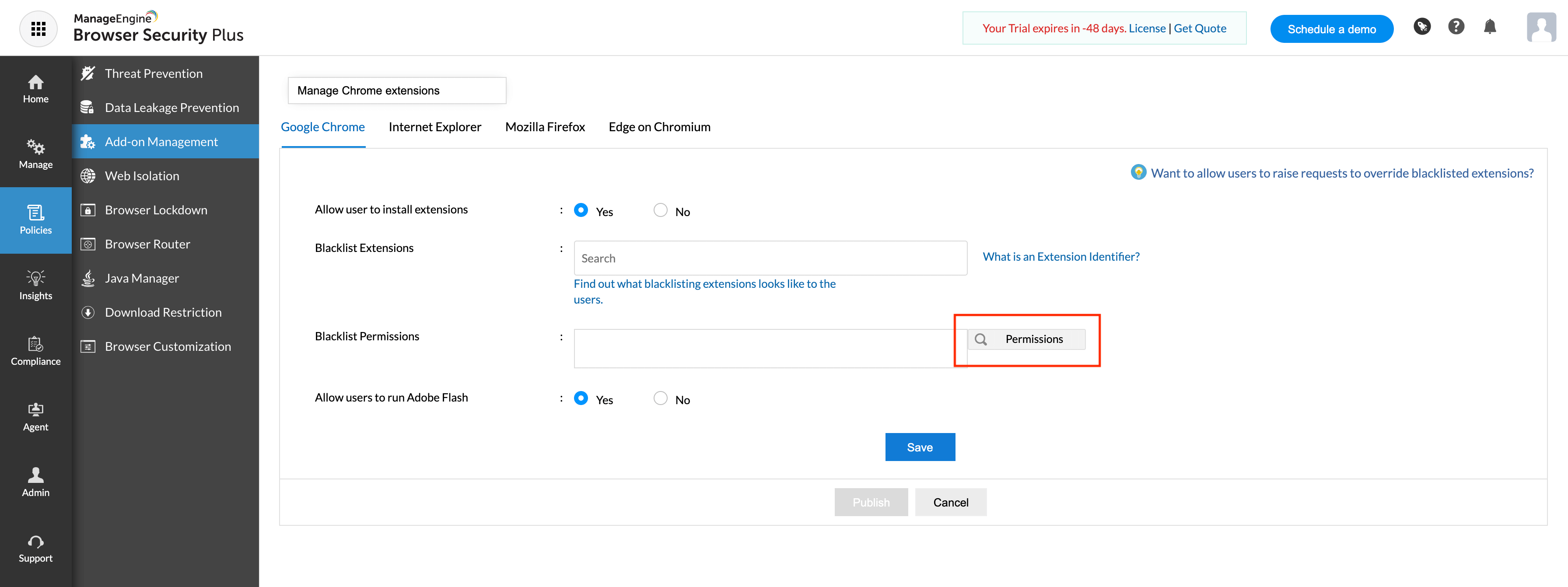
Step 2: Check No corresponding to Allow users to install extensions checkbox.
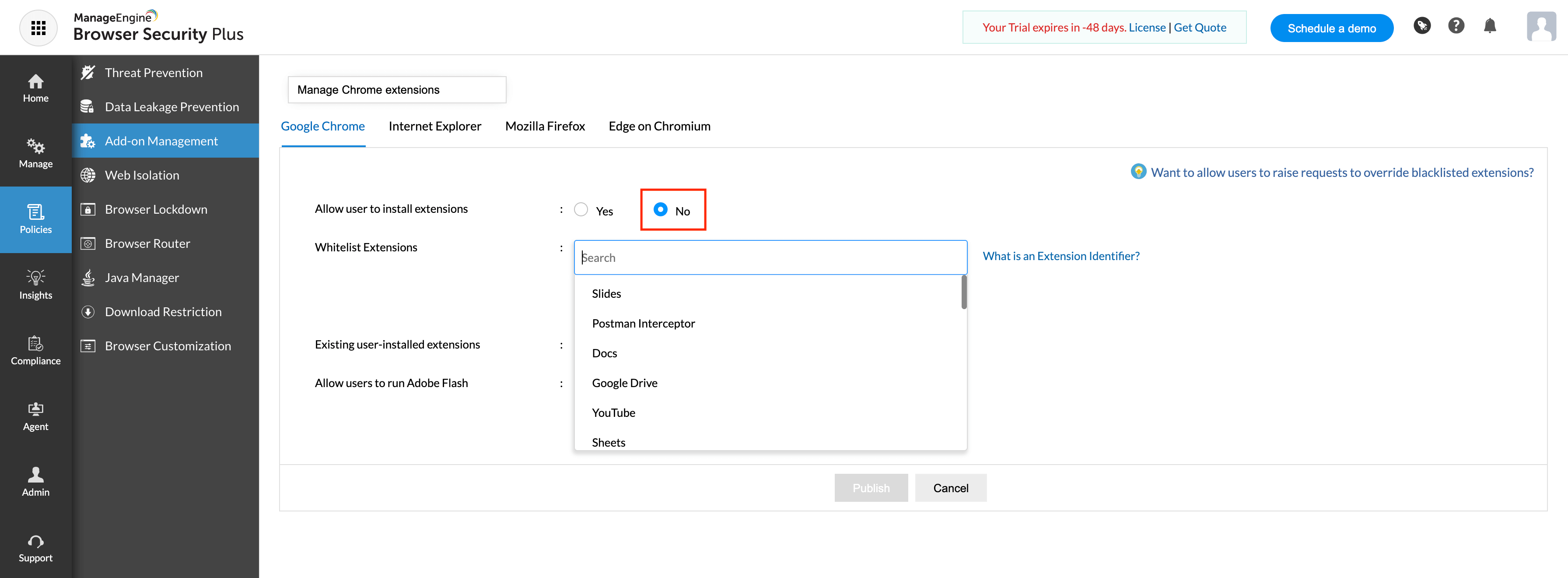
Step 3: Select the extensions that you want to whitelist from the Whitelist extensions drop down list.
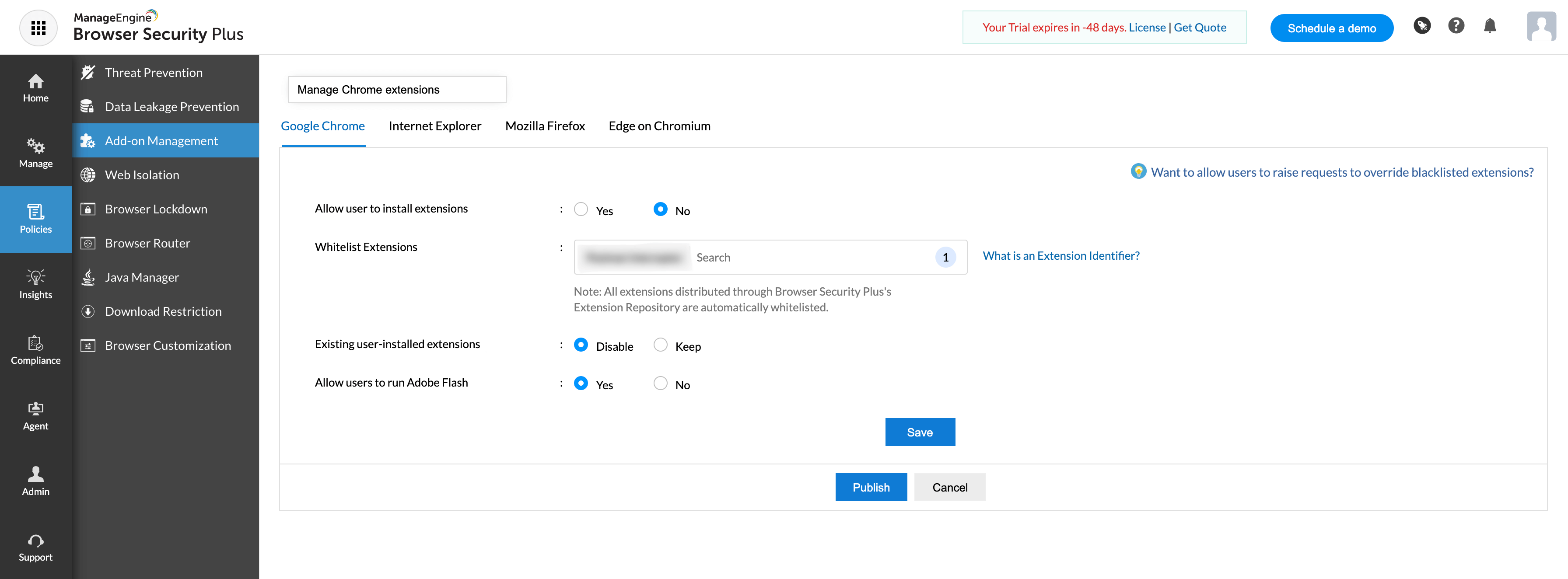
Step 4: Save and publish the policy.
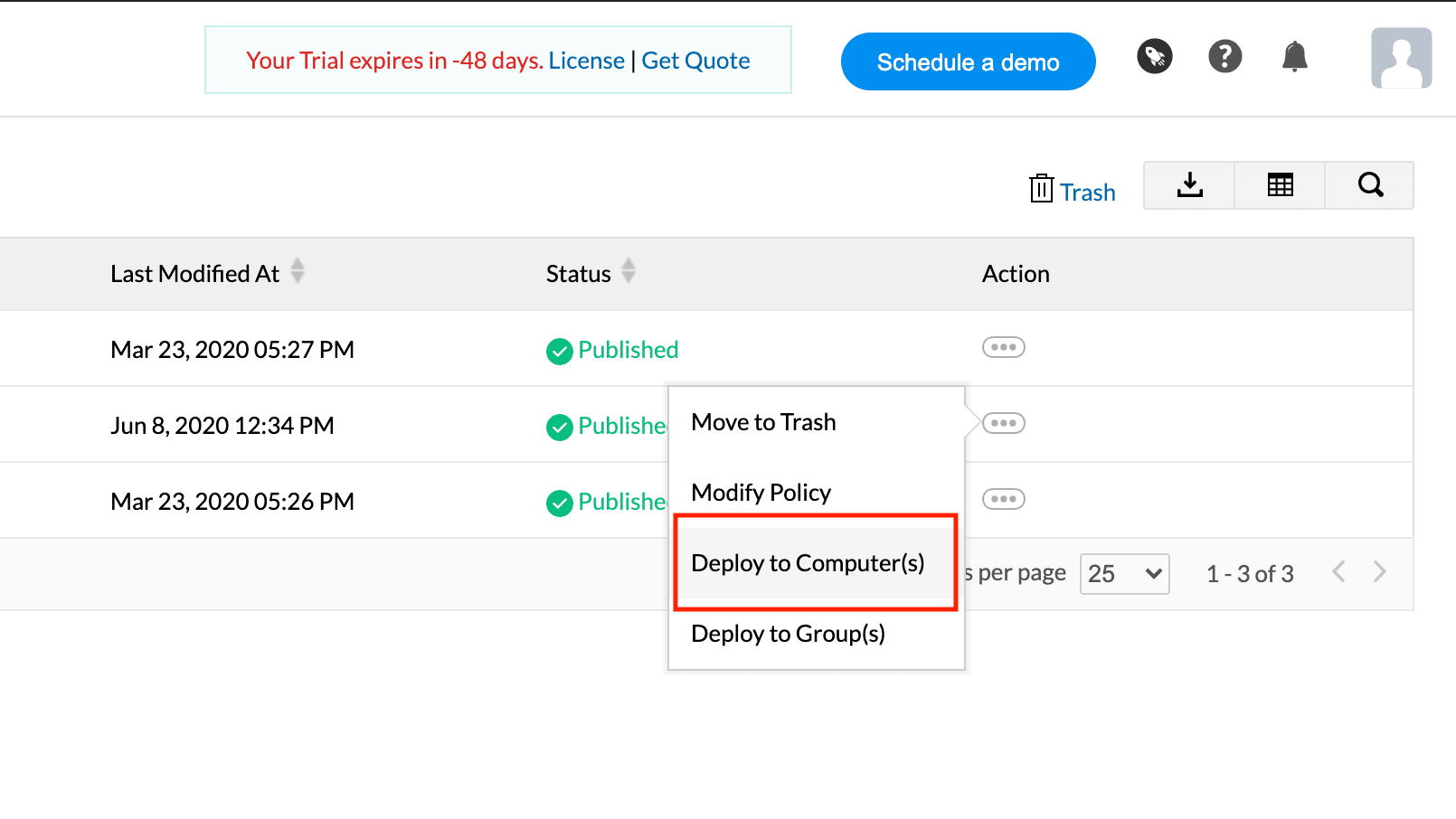
Step 5: Deploy the policy to computers that you want to apply the changes to.
Chrome extensions management based on the permissions they use:
Step 1: Open Browser Security Plus console.
Step 2: Navigate to policies and click on Add-on Management.
Step 3: Click on Search Permissions corresponding to Blacklist Permissions.
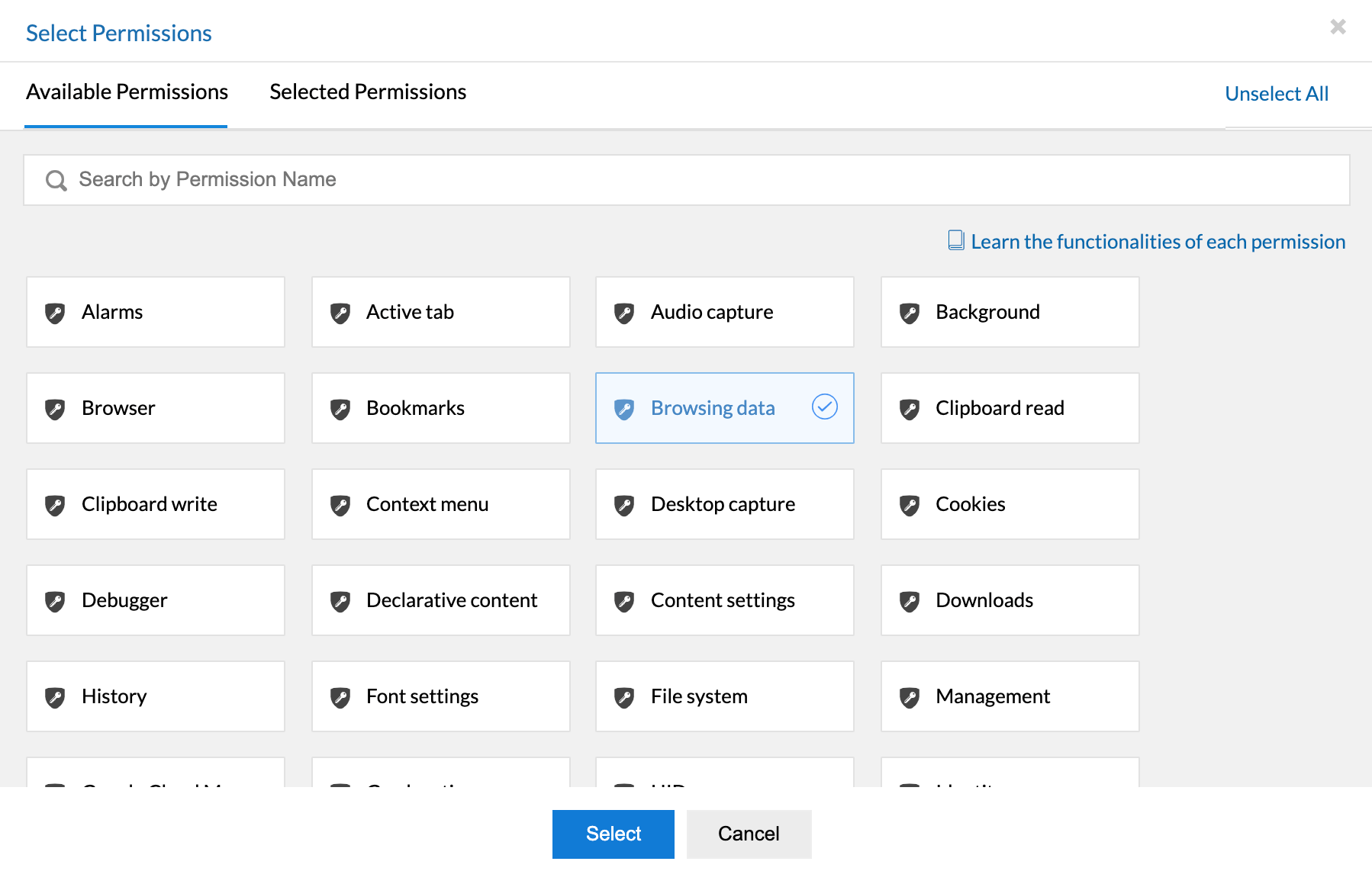
Step 4: Select the permissions you want to blacklist.
Step 5: Save and publish the policy.
Step 6: Deploy the policy to computers that you want to apply the changes to.
Need for Chrome extension management
While some Chrome extensions are installed by users merely to enhance their browsing experience, some are mission critical for users to get their work done. So IT admins have to manage Chrome extensions effectively, making sure only trusted extensions are present in their network. Equip yourself with the below tools to efficiently manage Chrome extensions:
- Proper visibility into what extensions are present in the network. Based on the insights, IT admins can scrutinize their reliability and take a call on which extensions can be trusted and which cannot.
- The next step in managing Chrome extensions would be to remove these unnecessary extensions from the network.
Currently, IT admins have no visibility of what extensions are present in their network. They have no way of knowing what permissions have been granted to these extensions and hence no clarity over which extensions are privy to which sensitive data. This makes it imperative for IT admins to manage Chrome extensions. IT admins can use Browser Security Plus to manage and remove Chrome extensions present in their network. It's Chrome extensions manager provides a clear view into all extensions present on employees' browsers, and it also provides simple and effective way to disable Chrome extensions from a central console.
To manage Chrome extensions and secure your network from data breaches, download a free, 30-day trial of Browser Security Plus and try out these features for yourself.