Key takeaways
- PKI is not a single tool or protocol. It is both a governing framework and an operational infrastructure, encompassing the policies, certificate authorities, encryption mechanisms, and trust hierarchies that organizations use to verify identities and secure digital communication.
- Certificates are the operational currency of PKI, and every certificate has a life cycle. Organizations that do not actively manage issuance, renewal, revocation, and expiry across their certificate estate are exposed to outages, compliance failures, and security blind spots.
- Implementing PKI is not a one-time project. It involves designing a CA hierarchy, establishing policies, deploying infrastructure, and then transitioning into the ongoing life cycle operations that keep the whole system functional as the environment evolves.
- At enterprise scale, manual PKI operations break down. As certificate volumes grow and validity periods shrink toward 47 days, automating life cycle management, centralizing visibility across CAs, and enforcing consistent policies become baseline operational requirements.
PKI vs. encryption vs. certificates
PKI, encryption, and digital certificates are often used interchangeably, but they refer to different layers of the same system. Encryption is the mechanism, certificates are the credentials, and PKI is the framework that ties them together. Here is how they compare:
| Attribute | Encryption | Digital certificates | PKI |
|---|---|---|---|
| What it is | A mathematical process that converts plaintext into ciphertext to prevent unauthorized access | Electronic documents that bind a public key to the identity of an entity (user, device, server, or application) | A comprehensive framework of policies, roles, hardware, software, and procedures for managing digital certificates and encryption keys |
| Primary function | Protects data confidentiality during transmission or storage | Verifies identity and establishes trust between communicating parties | Provides the framework to issue, manage, distribute, store, and revoke certificates at scale |
| Scope | A single operation applied to a specific data exchange or stored object | A credential tied to a specific entity, with a defined validity period and trust chain | An organization-wide (or cross-organization) system governing all certificates and keys |
| Works independently? | Yes. Encryption can function without certificates (e.g., symmetric key exchange between known parties) | Partially. Certificates require a CA and trust hierarchy, which are components of PKI | No. PKI depends on encryption and certificates to function. It is the orchestration layer. |
In short, encryption protects data, certificates prove identity, and PKI is the system that makes both of those things work reliably at scale. When organizations talk about "implementing PKI," they are talking about building the infrastructure that manages certificates and the encryption keys bound to them across their entire environment.
Key components of PKI
- 01.
Public and private keys
Public and private keys encrypt communications utilizing the PKI framework. The public key is visible to all, while the private key is used to decrypt the message and remains private to the entity.
Think of the public key in PKI as a lock, unique to users and entities and used for encryption. The lock, although unique to the entity, is publicly visible to anyone looking to access it. The private key is the specific key for that specific lock, used to decrypt messages. Unlike the public key, the private key isn't shared or visible to anyone and is known only to the user and entity that owns it.
When an encrypted message is sent to the entity, the message is encrypted using its public key. If the message is from an authorized source, the entity will then decrypt it using its own private key.
- 02.
Digital certificates
Digital certificates, or PKI certificates, are a pivotal component of PKI. Certificates are the digital world's passports and identity cards—they help verify if the digital entity is who they say they are. A certificate contains information about the user or device that the certificate belongs to along with the entity's public key. Certificates involve expiration dates and need to be renewed periodically. If not renewed in time, they become invalid.
- 03.
Certificate authorities
Certificate authorities (CAs) form the backbone of PKI. A CA is a trusted organization that validates the identities of digital entities and issues signed digital certificates to applicants once verification is complete. The certificate issued by the CA binds a public key and identity details to the subject of the certificate. This ensures that no one can claim to be the entity or replicate its public key, preventing manipulator-in-the-middle (MitM) attacks (also known as man-in-the-middle attacks). Some well known certificate authorities include Sectigo, DigiCert, GoDaddy, GlobalSign, and Let's Encrypt.
- 04.
Registration authorities
CAs use registration authorities (RAs) to help verify the identity of certificate applicants. RAs serve as intermediaries between the entity applying for a PKI certificate and the CA. RAs receive certificate signing requests (CSRs) for issuance and renewals, verify the identity details of the applicant, request proof of identity from the applicant, vet the documents, and pass the application to the CA. RAs include government agencies, banks, and other CAs.
- 05.
Certificate signing requests
A certificate signing request (CSR) is an encrypted message that contains information about the entity applying for the issuance or renewal of a digital certificate. Typically, a CSR is generated on the server that the certificate will be installed on. The CSR contains information about the applicant such as domain name, organization name, organizational unit, location, country, and email address. It will also contain the public key of the server, along with the key size and type.
Why is PKI important?
In a world where the threat landscape is growing and cyberattacks are becoming increasingly common, the need for secure, encrypted digital communications is paramount. Not only does PKI verify the identity of the client and server involved by binding their public keys to their respective digital certificates, it also ensures that the session is end-to-end encrypted, preventing snooping and possible MitM attacks, making PKI a necessity in any digital interaction.
Digital signatures, issued by trusted CAs and in line with PKI chain of trust mechanisms, ensure that data isn't tampered with in transmission. This establishes trust and maintains the integrity of sensitive online activities, such as bank transactions, credential-based logins, and confidential data transfers. Additionally, compliance standards like the PCI DSS and HIPAA require organizations to utilize PKI for digital communication.
How does PKI work?
PKI is a framework that imposes mechanisms to verify the identity of digital entities by mapping and binding public keys to the certificate holder. Since communication in PKI is encrypted end-to-end and happens using asymmetric encryption, only a recipient with the right private key can decrypt information passed to it. Digital signatures in certificates ensure that data is not tampered with in transit and preserve the integrity of the communication.
- 01.
Asymmetric encryption utilized in PKI
PKI uses the asymmetric method of encryption to achieve secure digital communication. Asymmetric encryption utilizes a public-private key pair to establish secure communication. The sender and the receiver share their public keys with each other, and the sender encrypts the message based on the receiver's public key. The receiver then utilizes their private key to decrypt the message received. The key pairs are generated using a suitable algorithm like the RSA algorithm, Elliptic Curve Digital Signature Algorithm (ECDSA), or the Diffie-Hellman algorithm.
- 02.
PKI: A step-by-step process
- The first step in the PKI management process is for the applicant to generate a public-private key pair. Once the public-private key pair is generated for the server, the server creates a CSR based on the type of certificate needed.
- The CSR is then passed on to a CA to be vetted, and for the issuance of a signed digital certificate. The CA, either by utilizing a registration authority or independently, verifies if the information pertaining to the applicant as provided in the CSR is correct, and if the applicant is who they claim to be. Do note that the verification process varies depending on the type of certificate requested.
- Post verification, the CA creates and signs the certificate for the server and issues it to the applicant, while also storing a copy. The digital signature of the CA certifies that the information mentioned in the certificate and the public key belongs to the entity holding the certificate. The CA signs certificates using its private key, authenticating the signature and ensuring that it cannot be duplicated.
- When a user or client reaches out to the entity to establish communication, it verifies the digital signature in the certificate using the CA's public key and establishes secure, encrypted communication with the server. This is also known as an SSL/TLS handshake.
PKI certificates: The chain of trust
The chain of trust in PKI helps verify the authenticity of a certificate and the digital signature by tracing it back to the issuing or root CA. It is a sequential trust system, established from the root CA to the digital entity to whom the certificate belongs. Between the server or digital entity and the root CA, there are usually one or more intermediate certificates.
- 01.
Root certificate
The root certificate is a self-signed certificate of the issuing CA and is stored securely in a browser's trust store. The root certificate is an established token of trust and follows the X.509 certificate standard. Since the certificate is signed using the private key of the root CA, if the private key is compromised, all certificates signed by the root CA will have to be replaced.
To prevent this possibility and ensure the private key of the root is not exposed, the root does not sign the end-server certificates directly. Instead, there exist one or more intermediary certificates that link the server to the root.
- 02.
Intermediate certificates
Intermediate certificates serve as connecting links between the end-server and the root. In the hierarchical model of the chain of trust, the intermediary certificate that is directly under the root in the chain of trust hierarchy is signed by the root CA.
If there are more than one intermediary CAs between the root and the end-server, then the primary intermediate CA—that is the CA immediately under the root in the chain of trust hierarchy—signs the certificate of the second intermediary, and so on, until the end-server's certificate.
- 03.
End-entity certificates
The end-entity certificates are installed on the end-server and verify the identity of the certificate holder. This could be an SSL/TLS certificate, email certificate, EMV certificate, or code-signing certificate.
In the context of web communication where a web browser is trying to establish connection with a website or domain, the end-server certificate is the SSL/TLS certificate of the domain. The SSL/TLS certificate will contain information about the domain, organization, and public key of the webserver the certificate is stored in, along with the signature of an intermediate CA. This signature can be traced back hierarchically to the root CA, which serves as the trust anchor at the top of the chain.
The hierarchical trust method, although the most popular, isn't the only method of trust used in the PKI. Learn more about the different methods of trust used in PKI below.
Different models of trust in PKI
The certificate revocation landscape is evolving rapidly, and the change is driven by two major industry developments.
- 01.
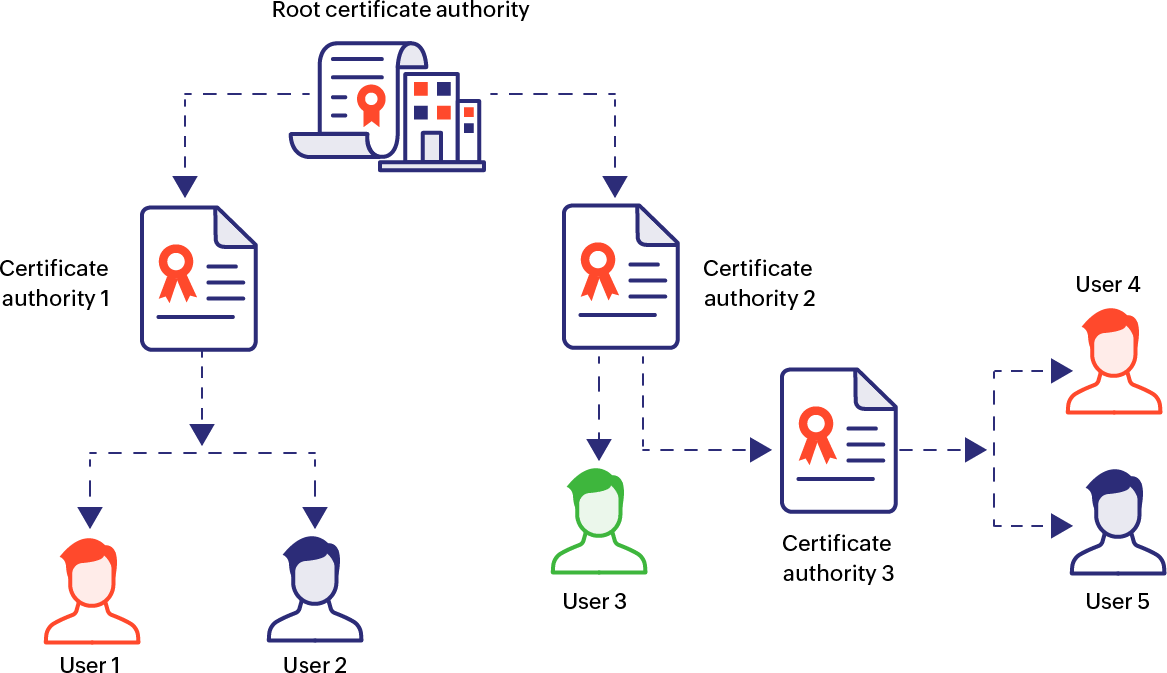
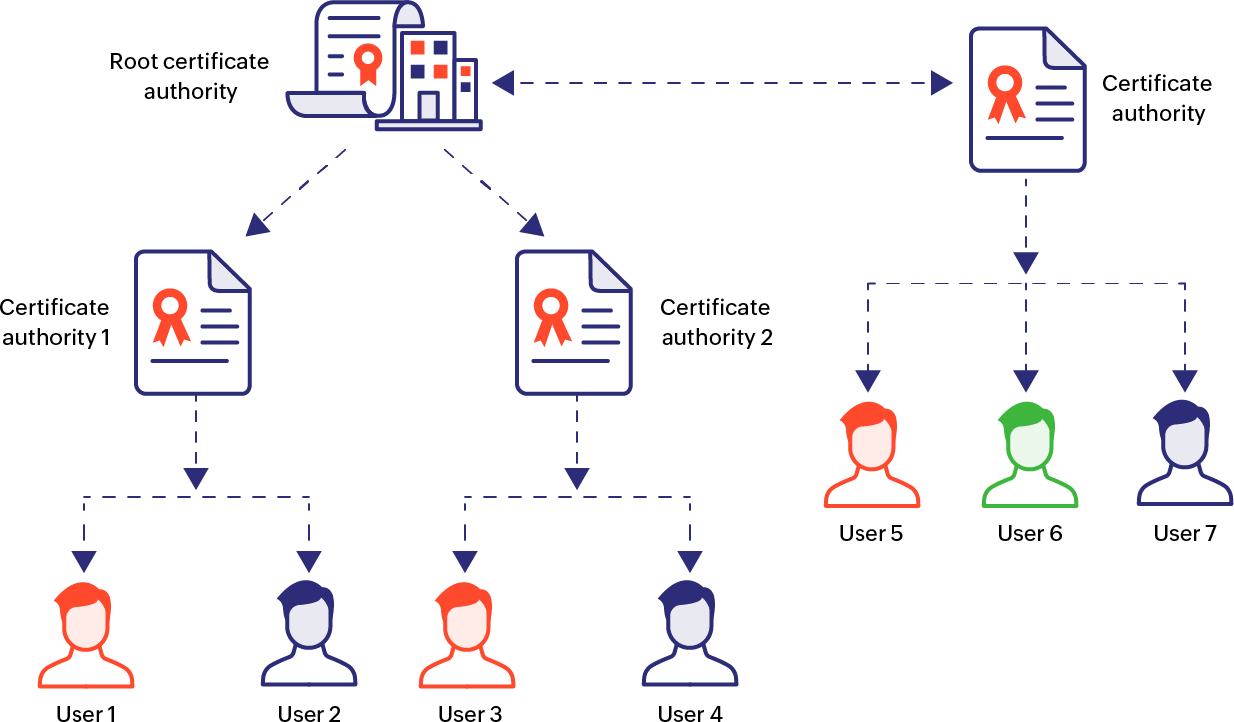
Hierarchical trust model
The hierarchical method is the method of trust to understand how root, intermediary, and end-entity certificates work. It is a top-down, unidirectional approach to trust, where the root certificate serves as the trust anchor and sits at the top of the chain. Between the end-entity certificate and the root certificate, there exist one or more intermediate certificates that eventually trace back to the root CA.
- 02.
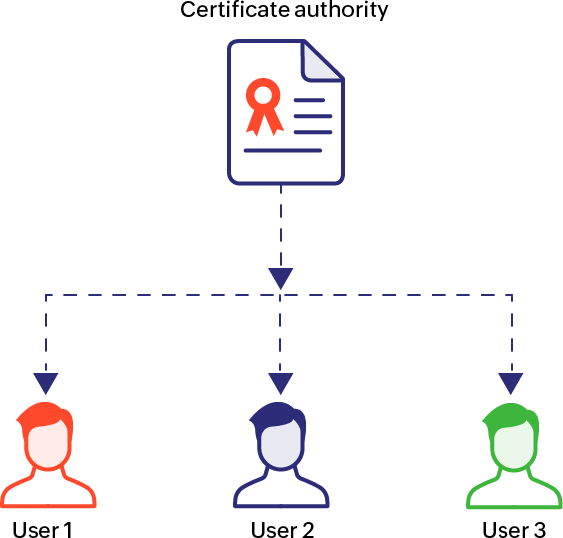
Single CA model
The single CA model, like the name suggests, involves only one CA. There is no intermediate CA or certificate between the issuing CA and the end-server. This model poses a risk of collapse—should the private key of the root certificate be altered, all certificates issued by the root CA must be replaced.
- 03.
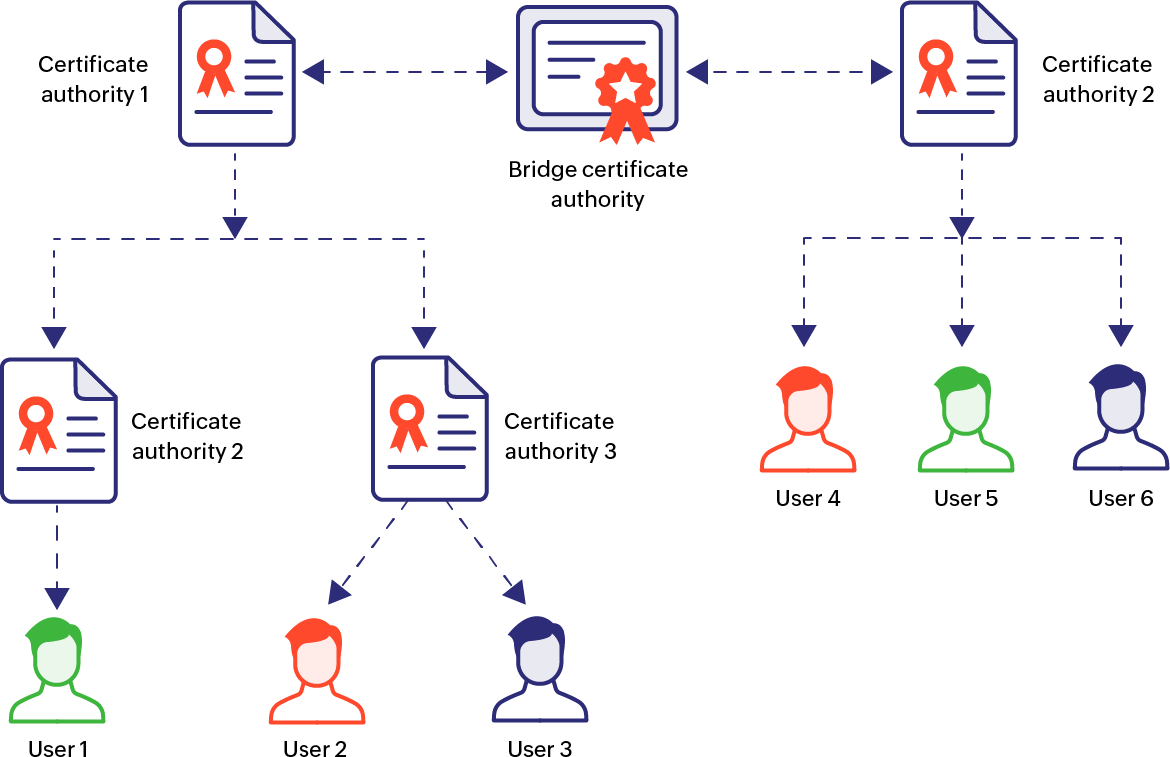
Bridge model
The bridge model involves the root CAs of multiple hierarchical PKI trees and domains connected to each other through one or more bridge CAs. The bridge CAs act as a bidirectional hub for peer-to-peer trust verification between different CAs and establishes trust between different PKI domains. This establishes trust between different PKI domains such that digital certificates of one PKI domain are trusted by entities in the other, enabling secure communication.
- 04.
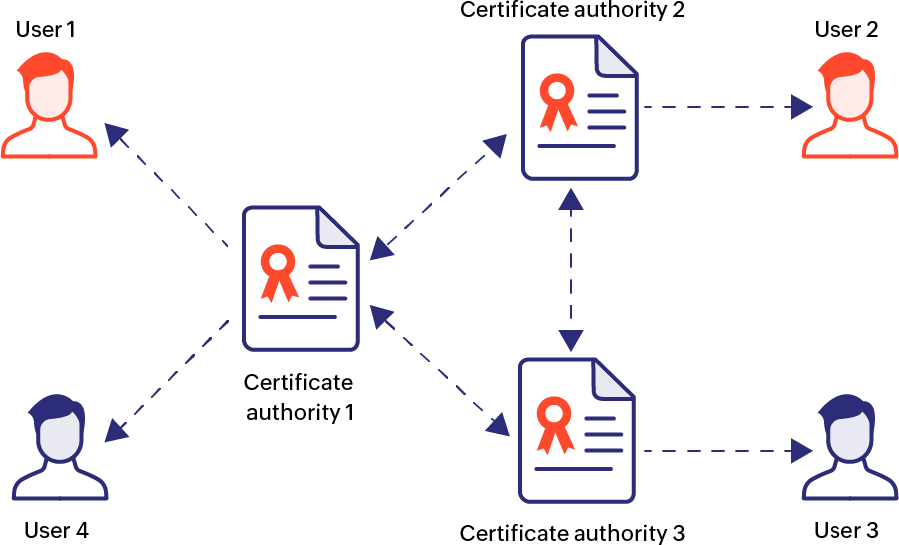
Mesh model
Unlike the hierarchical or bridge models, the mesh model has a decentralized trust system, where every local CA serves as a trust anchor in its own right. In the mesh model of PKI, different CAs are interconnected with each other, where they verify information in a bidirectional manner with other CAs connected to them. Since there is no root CA or a superior trust anchor based on hierarchy, the mesh model of PKI does not entail a single point of failure.
- 05.
Hybrid model
The hybrid model of PKI is a blend of the different models we have seen above. It utilizes characteristics of the hierarchical, bridge, and mesh models where suited in its architecture. The hybrid model is largely built to be flexible—depending on different organizational needs—making it agile and scalable.
What is the role of digital certificates in PKI?
SSL/TLS certificates are a fundamental component in ensuring secure web-based communication. They are typically used to establish encrypted communication between a web server and a web browser or client. They protect the integrity of the information that is transmitted and prevent data tampering.
SSL/TLS certificates can be broadly classified into three main subtypes:
- Domain validation (DV) certificates: These certificates are used to verify if the certificate holder has control over the domain. They are the most basic form of SSL/TLS certificates and are usually used for smaller blogs and websites.
- Organization validated (OV) certificates: Along with verifying the ownership of a domain and if the certificate holder has the rights to use the domain, OV certificates also verify organizational information.
- Extended validation (EV) certificates: These certificates are subjected to a stringent validation process. EV certificates verify organizational details of the certificate holder such as their legal status and physical existence.
Different ways in which certificates are used in PKI
- Code signing certificates: Code signing certificates are certificates that are signed by software developers to certify their code or application and verify their ownership. The purpose of code signing certificates is to ensure that the code hasn't been tampered with, verifying that it can be safely downloaded and used.
- Email signing and encryption certificates: Email signing certificates or secure/multipurpose internet mail extensions (S/MIME) certificates are signed to verify the authenticity of the sender and to protect against email spoofing. Meanwhile, email encryption certificates are used to encrypt email messages to maintain privacy of the contents of the email. They do this by using the recipient's public key, so that only the recipient's private key can decrypt it.
- Client authentication certificates: Client authentication certificates help authenticate a client—that is, a digital entity such as a user or device—and verify their identity. Client authentication certificates convey to the server that the client is trying to connect, that the client is who they say they are, and they can be trusted. Servers can implement access control restrictions based on the client certificate.
- Server authentication certificates: Server authentication certificates are SSL/TLS certificates used to verify the identity of servers when clients attempt to connect to it. Clients (e.g., web server) can verify that they are connecting to the right server (e.g., website) and not an imposter or malicious site.
How to implement PKI
Implementing PKI is not a one-time implementation project. It is a layered, continuous process that involves defining trust boundaries, building the certificate authority hierarchy, establishing policies, and then setting up end-to-end certificate life cycle management that keeps the whole thing running. The specifics will vary depending on whether you are building a private PKI, using a public CA, or working with a hybrid model, but the foundational steps are largely the same.
- 01.
Define the scope and objectives
Before anything else, you need to know what the PKI is responsible for securing. Web servers, internal APIs, email, device authentication, code signing, VPN access, IoT endpoints, or most likely some combination of all of these. Getting the scope right up front matters because it dictates everything down the line like how diverse the CA hierarchy needs to be, which certificate types you will be working with, and what policies need to govern them.
- 02.
Design the CA hierarchy
The CA hierarchy is the trust backbone of the entire PKI. Most enterprise implementations use a two-tier or three-tier model: an offline root CA at the top (kept air-gapped and powered down when not in use), one or more intermediate CAs that handle day-to-day certificate issuance, and optionally issuing CAs beneath them for specific use cases or business units. The root CA's private key is the single most sensitive asset in the hierarchy, and if it is compromised, every certificate in the chain must be replaced.
- 03.
Establish certificate policies and practice statements
A certificate policy defines the rules governing how certificates are issued, used, and managed. A certification practice statement describes the specific procedures the CA follows to implement those rules. Together, they set the ground rules for validation levels, key lengths, certificate lifetimes, revocation procedures, and acceptable use. These documents are not just internal governance tools, they are often required for compliance with standards like PCI DSS, HIPAA, and DORA.
- 04.
Select cryptographic standards
Choose the encryption algorithms and key lengths that the PKI will use. For most enterprise deployments today, this means RSA-2048 or higher, ECDSA with P-256 or P-384, and SHA-256 or SHA-384 for hashing. Organizations should also keep an eye on the post-quantum cryptography landscape, as NIST has finalized its first set of post-quantum standards and migration planning is already underway at many enterprises.
- 05.
Deploy
This involves setting up the root and intermediate CAs, configuring certificate templates, establishing the certificate revocation lists (CRLs) and OCSP responders for revocation checking, and integrating with directory services like Active Directory or LDAP for certificate distribution. Hardware security modules (HSMs) should be used to protect the private keys of at least the root CA, and ideally the intermediate CAs as well.
- 06.
Issue certificates and integrate with endpoints
With the infrastructure in place, begin issuing certificates to the endpoints, applications, and users identified in the scoping phase. Protocols like SCEP, EST, and ACME can streamline enrollment, particularly for device fleets and automated environments. Integration with web servers, email platforms, VPN gateways, and identity providers ensures that certificates are actually being used in the communication flows they were designed to protect.
- 07.
Operationalize life cycle management
This is where implementation becomes ongoing operations. Certificate life cycle management covers everything from tracking expiry dates and automating renewals to handling revocations and re-keying. As certificate volumes grow and validity periods shrink (with the industry moving toward 47-day certificates by 2029), manual life cycle management becomes increasingly untenable. Organizations should plan for automation from day one rather than treating it as a later optimization.
What are the challenges that PKI solves?
Strong cryptography and digital certificates play a vital role in securing modern enterprise infrastructure, but managing them efficiently across a large organization poses significant challenges. Without proper PKI management, organizations struggle with authenticating users and devices, securing communications, and maintaining compliance with security standards. The lack of a robust PKI solution can lead to unexpected certificate expirations, security breaches, and service disruptions.
As organizations increasingly rely on digital transactions and remote access, the need for reliable identity verification and encrypted communications is paramount. Traditional password-based systems are vulnerable to various attacks, while manual certificate management processes are error-prone and resource-intensive. The complexity multiplies when dealing with numerous endpoints, applications, and services spread across different networks and locations.
PKI addresses these challenges by providing a framework for managing digital certificates and encryption keys throughout their life cycle. It enables organizations to establish trust relationships, secure sensitive data transmission, and implement strong authentication mechanisms. A comprehensive PKI software helps automate many aspects of certificate management, reducing human error and ensuring timely certificate renewals. This systematic approach helps organizations maintain security standards while scaling their digital operations. But while PKI provides the framework, the operational reality of managing it at enterprise scale introduces a different set of challenges altogether.
PKI challenges in enterprises
The challenges above are amplified significantly in enterprise environments where certificate estates run into the tens of thousands, spread across multiple CAs, cloud platforms, and internal services. At that scale, the operational challenges become even more profound.
- 01.
Visibility gaps
Many organizations do not have a complete inventory of the certificates in their environment. Certificates get issued by different teams, across different CAs, for different use cases, and without a centralized discovery mechanism, it is entirely possible for certificates to exist in production that nobody is actively tracking. These blind spots are where outages and security incidents tend to originate.
- 02.
CA sprawl and fragmentation
Enterprises frequently work with multiple certificate authorities, both public and private, each with their own portals, renewal workflows, and policy configurations. Managing certificates across various public CAs, an internal Microsoft CA, and possibly others means there is no single place to view the entire certificate estate or enforce consistent policies.
- 03.
Manual processes that do not scale
Spreadsheets, calendar reminders, and ad-hoc scripts might work when an organization is managing a few hundred certificates. They do not hold up at enterprise scale. A single missed renewal can take down a customer-facing application or break an API integration, and the blast radius tends to grow as certificate estates get more distributed and interconnected.
- 04.
Shortening certificate lifetimes
The industry is actively moving toward shorter certificate validity periods, with the CA/Browser Forum's 47-day maximum set to take effect by 2029. For enterprises already struggling with annual renewals, this shift compresses the operational window dramatically and makes automation a prerequisite rather than a nice-to-have.
- 05.
Compliance and audit
Regulatory frameworks like PCI DSS, HIPAA, SOC 2, and ISO 27001 require organizations to demonstrate that their cryptographic assets are properly managed, that certificates are valid and up to date, and that access controls are in place. Without centralized reporting and audit trails, generating evidence for these requirements becomes a resource-intensive manual exercise.
- 06.
Key management risks
Private keys that are not stored securely, reused across environments, or not rotated on schedule are a significant attack surface. A compromised private key does not just affect a single certificate, depending on where it sits in the hierarchy, it can undermine trust across the entire PKI. Enterprises need clear policies and tooling for key generation, storage, rotation, and decommissioning.
How to manage PKI at scale
Managing a handful of certificates is straightforward, but managing thousands, across multiple CAs, cloud environments, and internal services, requires a fundamentally different approach. PKI management at scale is less about individual certificate operations and more about building systems that give security teams visibility, control, and confidence that nothing is falling through the cracks.
- 01.
Centralized discovery and inventory
The first step in managing PKI at scale is knowing what you have. Automated discovery scans the network, cloud environments, certificate stores, and CA databases to build a complete, continuously updated inventory of every certificate in the environment. This includes certificates that were issued outside of standard workflows, certificates on devices that may have been forgotten, and certificates across all CAs, whether public, private, or cloud-hosted. Without this foundational central visibility, every other management activity is working from an incomplete picture.
- 02.
Automated life cycle management
Once an organization has visibility into its certificate estate, the next priority is automating the repetitive, time-sensitive operations that make up the certificate life cycle. This means automated renewal workflows that trigger before expiry, automated provisioning for new endpoints through protocols like ACME and SCEP, and automated revocation when certificates are compromised or no longer needed.
- 03.
Policy enforcement and governance
PKI management should include the ability to define roles, directly responsible individuals (DRIs), and enforce policies around minimum key lengths, approved algorithms, maximum certificate lifetimes, naming conventions, and which CAs are authorized for specific use cases. Policy enforcement ensures that the certificates being issued across the organization meet a baseline standard, regardless of which team or CA is doing the issuing. Equally important is having a defined DRI, whether an individual or a team, for every certificate or certificate group, coupled with a responsibility matrix that provides clarity on who is managing what across the estate. Without that ownership layer, policy exists on paper but nobody is accountable for it in practice, and that is usually where things start to slip.
- 04.
Multi-CA management
Most enterprises do not operate with a single CA. They work with a mix of public CAs for external-facing certificates, private CAs for internal use, and possibly cloud-native certificate services. Managing PKI at scale requires the ability to work across all of these from a centralized interface, normalizing the differences in how each CA handles issuance, renewal, and revocation into a consistent operational workflow.
- 05.
Monitoring, alerting, and reporting
Continuous monitoring provides real-time awareness of impending expiries, certificate health, renewal completion and failure, weak key strengths, algorithm deprecations, and trust chain issues. Alerting should be configurable and escalation-aware, ensuring the right people are notified at the right time.
Manual PKI operations vs. life cycle automation
The gap between manual certificate management and automated life cycle management is not just about efficiency. It affects security posture, compliance readiness, operational reliability, and how well an organization can adapt to an environment where certificate volumes are growing and validity periods are shrinking. Here is how the two approaches compare across the attributes that matter most:
| PKI function | Manual PKI operations | Life cycle automation |
|---|---|---|
| Certificate discovery | Periodic, typically ad-hoc. Relies on teams self-reporting certificates or running occasional scans. Certificates issued outside standard workflows often go untracked. | Continuous and automated. Network-wide scans, CA database syncs, and cloud integrations maintain a real-time inventory with minimal manual effort. Centralized inventory through a CLM tool. |
| Renewal management | Driven by spreadsheets, calendar alerts, or email reminders. Susceptible to missed renewals when staff turnover occurs, reminders are misconfigured, or certificate ownership is unclear. | Automated renewal workflows trigger based on configurable lead times. Renewals are initiated, approved, and deployed without manual intervention for standard certificates. |
| Provisioning and enrollment | Manual CSR generation, submission to the CA, certificate retrieval, and installation. Each step introduces potential delays and configuration errors. | Protocol-driven enrollment (ACME, SCEP, EST) automates the end-to-end provisioning process, reducing deployment time from hours or days to minutes. |
| Revocation | Requires identifying the compromised certificate, locating it in the environment, contacting the issuing CA, and manually triggering revocation. Response time depends on how quickly the certificate can be found. | Centralized revocation from a single interface across all CAs. Compromised certificates can be identified, revoked, and replaced in a coordinated workflow. |
| Visibility | Fragmented. Different teams manage different subsets of certificates, often in different systems. No single source of truth for the full certificate estate. | Centralized dashboard provides a unified view of all certificates across all CAs, environments, and endpoints, with real-time status and key information. |
| Policy enforcement | Relies on documentation and manual review. Policies around key lengths, algorithms, and lifetimes are defined but not systematically enforced at the point of issuance. | Policies are codified and enforced automatically. Non-compliant certificate requests are flagged or blocked before issuance. |
| Compliance reporting | Manual data collection across multiple sources. Generating audit evidence is time-intensive and often reactive, triggered by an upcoming audit rather than maintained continuously. | On-demand reports with full audit trails. Compliance evidence is generated from live data, reducing preparation time and improving accuracy. |
| Error rate | Higher. Manual processes introduce human error at every stage, from CSR generation to certificate installation to renewal tracking. | Significantly lower. Automated workflows reduce the surface area for human error and enforce consistency across operations. |
| Scalability | Does not scale. The operational burden grows linearly (or worse) with certificate volume. Each additional certificate adds to the tracking, renewal, and management workload. | Scales efficiently. Automated systems handle growing certificate volumes without proportional increases in operational effort or staffing. |
| Readiness for shorter validity periods | Poorly positioned. The move toward 47-day certificate lifetimes will multiply renewal frequency roughly 8x compared to annual certificates, overwhelming manual workflows. | Well positioned. Automated renewal cycles absorb increased frequency without additional operational load, making shorter lifetimes operationally transparent. |
Common PKI use cases
- 01.
Secure email communication
Email PKI enables users to digitally sign and encrypt their email messages, ensuring confidentiality and authenticity in business communications. Using protocols like S/MIME, recipients can verify the sender's identity and be confident that the message hasn't been tampered with during transmission.
- 02.
Digital certificates for websites
Website certificates form the backbone of secure internet browsing by enabling HTTPS connections that encrypt data between browsers and servers. When users visit a website with a valid certificate, they see the padlock icon indicating a secure connection for protecting sensitive information like passwords and credit card details.
- 03.
Code signing
Code signing certificates allow software developers to sign their applications digitally, proving their identity as the legitimate publisher. This helps ensure code integrity. When users download or install signed software, their OS can verify the signature and warn them if the code has been modified since it was signed. This protection is essential in preventing malware distribution and maintaining trust in software distribution channels. PKI software helps in discovering and managing code-signing certificates.
- 04.
Document signing
Digital document signing enables paperless workflows by providing legally binding electronic signatures that are impossible to forge. Each signature is uniquely tied to both the signer and the document content, creating a tamper-evident seal that maintains the document's integrity. This technology has revolutionized contract management, legal proceedings, and government services by reducing processing time from days to minutes while maintaining security and authenticity.
- 05.
Internet of things
In the internet of things (IoT) ecosystem, PKI provides a scalable way to authenticate and secure millions of connected devices. Each device receives a unique identity certificate, enabling secure communication with other devices and central management systems. This infrastructure is crucial for protecting smart homes, industrial IoT deployments, and critical infrastructure from unauthorized access and tampering.
- 06.
Internal IT infrastructure
Organizations utilize PKI management to secure their internal networks by issuing certificates to servers, workstations, and network devices. These certificates enable secure authentication and encrypted communication between different components of the IT infrastructure, protecting sensitive data and services. Comprehensive PKI software helps provide centralized control over security policies and certificate life cycle management.
PKI best practices
If you are implementing or overhauling your organization's PKI, here is a quick checklist of the practices that matter most. Several of these are covered in more detail in the sections above.
- 01.
Secure private keys with hardware security modules (HSMs)
As mentioned in the above sections, private keys are the cornerstone of PKI, so protecting them is critical. Private keys, especially those belonging to root and intermediate CAs, should be stored in hardware security modules rather than in keystores. HSMs provide physical and logical isolation that significantly reduces the risk of key compromise. This is particularly critical for the root CA, which should be kept offline and air-gapped when not actively signing.
- 02.
Use strong, current cryptographic standards
RSA-2048 or higher, ECDSA with P-256 or P-384, and SHA-256 for hashing are the baseline today. But cryptographic standards evolve, and organizations should be building for crypto-agility so that algorithm transitions, including the eventual move to post-quantum cryptography, do not require a ground-up rebuild.
- 03.
Automate certificate life cycle management
Manual tracking breaks down at scale, and it will break down faster as the industry moves toward shorter certificate validity periods. Automating discovery, renewal, provisioning, and revocation is the single highest-leverage operational improvement most organizations can make to their PKI.
- 04.
Define certificate ownership and accountability
Every certificate or certificate group should have a defined, directly responsible individual or team, documented in a responsibility matrix. Without clear ownership, renewals get missed, policy enforcement becomes inconsistent, and incident response slows down because nobody knows who is responsible for what.
- 05.
Enforce access controls and maintain audit trails
Limit who can request, approve, and revoke certificates. Log every action. This is not just good security hygiene; it is a compliance requirement under PCI DSS, HIPAA, SOC 2, and ISO 27001, and having continuous audit trails in place is significantly easier than reconstructing them before an audit.
- 06.
Disaster recovery and business continuity
A key compromise, CA failure, or infrastructure outage can cascade across the entire PKI. Organizations should maintain secure offline backups of root and intermediate CA keys, document clear recovery procedures, and test those procedures regularly. The time to find out your recovery plan has gaps is not during an actual incident.
Importance of using a PKI management tool
If there is one thread that runs through everything above, it is that PKI gets harder to manage the more it grows, and it is growing faster than most organizations are equipped to handle. More certificates, more CAs, more endpoints, shorter validity periods, and the operational surface area just keeps expanding. At a certain point, the question stops being whether you need a dedicated management tool and becomes how quickly you can get one in place before something slips through.
How Key Manager Plus helps manage PKI at scale
ManageEngine Key Manager Plus is built for exactly this problem. It gives security teams a single pane of glass across their entire certificate and key estate, regardless of how many CAs are in the mix or where the certificates live. Discovery runs continuously across your network, cloud environments, and CA databases so you are not relying on teams to self-report what they have issued. From there, the entire certificate life cycle, issuance, expiry tracking, renewal, deployment, and monitoring is managed from one place, with the kind of automation that keeps things running even as certificate volumes scale and renewal windows shrink.