- Home
- SIEM use cases
- Password Spray Attack Detection
How to detect password spray attacks
In this page
Threat snapshot
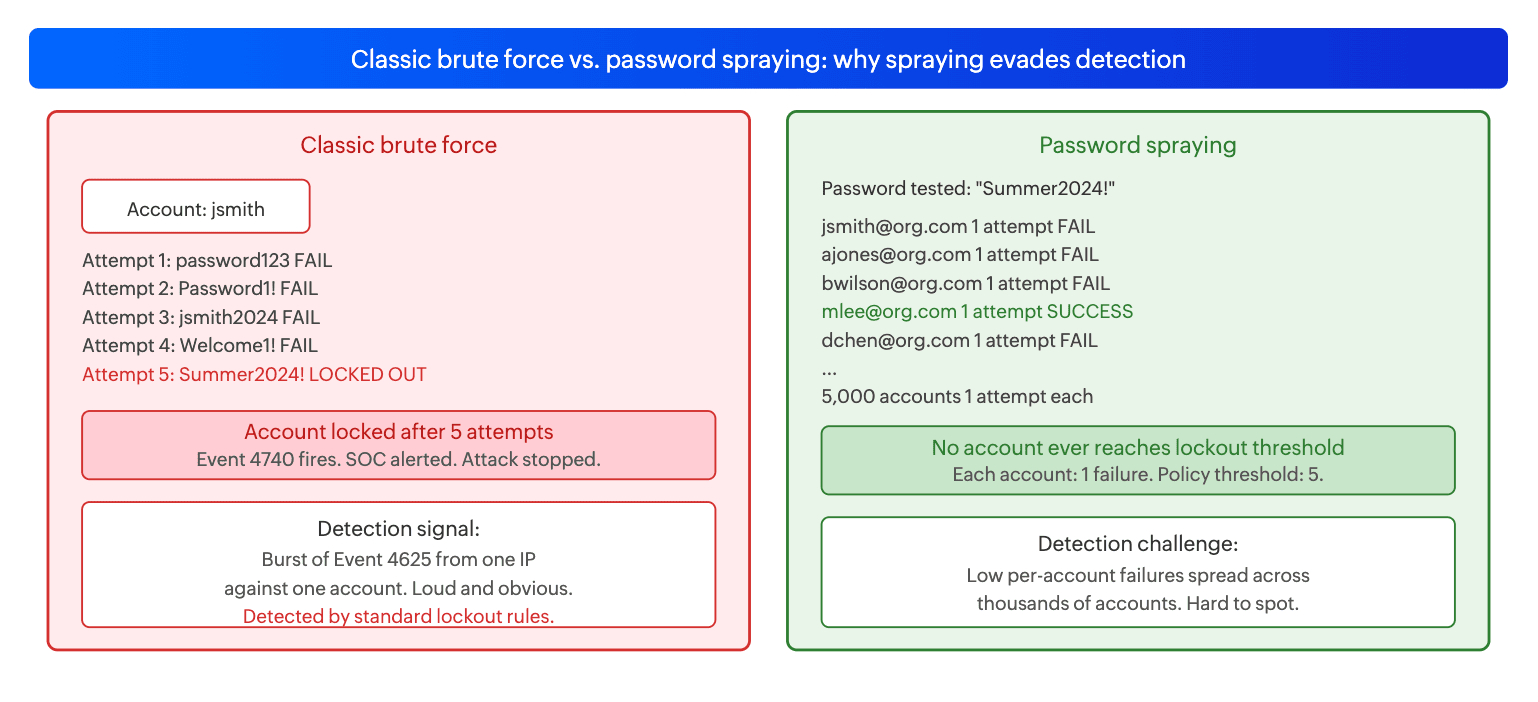
Password spraying is the art of staying invisible. Where a classic brute force attack hammers one account with hundreds of attempts and triggers lockout within minutes, a spray campaign does the opposite: it tests one or two passwords against every account in the directory, keeps the attempt rate well below the lockout threshold, and waits. An attacker targeting a 5,000-user organization with a lockout policy of five failures per 30 minutes needs only one attempt per account per hour to operate completely beneath the detection surface of standard lockout-based alerting.
The password chosen is rarely random. Attackers select candidates based on common enterprise patterns: seasonal passwords ("Summer2024!"), company-name variants ("Acme@2024"), and passwords identified in prior breach datasets that match the target organization's known password policy requirements. In many organizations, a meaningful percentage of accounts will match at least one of these patterns at any given time.
What makes spraying particularly dangerous is not just that it evades lockout policies, but that a successful spray produces a successful logon that is nearly indistinguishable from a legitimate user authenticating for the first time that day. Without behavioral baseline context, the compromise event itself does not look like an attack at all.
Password spraying, at a glance
| Severity | Critical |
| Category | Identity & Access |
| MITRE ATT&CK tactic | TA0006 (Credential Access) |
| MITRE technique | T1110.003 (Password Spraying) |
| Platforms covered | Windows, Active Directory, Microsoft 365, Azure AD |
| Log360 detection rules | Hydra detection, Kerbrute detection, Notable account lockouts |
| SOC maturity level | Level 1 (triage) |
| Compliance mapping | NIST CSF PR.AC-7, PCI-DSS 8.3.4, HIPAA Section 164.312(d), ISO 27001 A.9.4.2 |
How password spraying works
Password spraying exploits a fundamental tension in enterprise security policy: lockout thresholds that are set high enough to tolerate legitimate user mistakes create a window wide enough for an attacker to attempt multiple passwords against every account without triggering lockout on any single target.
The mechanics of a spray campaign
A typical spray campaign operates in three phases. In the reconnaissance phase, the attacker enumerates valid account names from the target environment, either through LDAP queries if they have internal access, or through public sources such as LinkedIn, company websites, and prior breach databases that reveal email formats. Valid account enumeration is critical because spraying against invalid accounts wastes attempts and may trigger username-enumeration detection.
In the spray phase, the attacker tests their chosen password list against every valid account, observing the lockout policy timing. Most enterprise Active Directory policies use a 30-minute observation window. An attacker who observes this will attempt one password per account every 31 minutes, resetting the window counter before it ever reaches threshold. Tools like Kerbrute make this particularly dangerous because they operate at the Kerberos pre-authentication level: instead of generating Event 4625 (failed logon) which most SOCs monitor, Kerbrute generates Event 4768 with a result code of 0x18, a signal that many environments do not alert on at all.
In the exploitation phase, the attacker identifies successful authentications from the spray results, validates access to the compromised account, and begins post-compromise activity: directory enumeration, lateral movement planning, or data access, depending on the campaign objective.
The Kerberos blind spot: Kerbrute's deliberate avoidance of Event 4625 is the reason why detecting the tool itself via process creation logs (Sysmon Event 1) is more reliable than trying to detect the spray from authentication failure counts alone. A Kerbrute spray against 10,000 accounts leaves no Event 4625 entries, but leaves a clear Sysmon process creation record on the machine where Kerbrute ran.
Real-world campaigns
APT28 (Fancy Bear): sustained M365 and on-premises spray campaigns
APT28, the Russian GRU-affiliated threat group, has conducted sustained password spraying campaigns against government agencies, defense contractors, energy companies, and political organizations across the US and Europe. Their operational signature is patience: campaigns run for weeks at one to two attempts per account per day, targeting M365 and on-premises Exchange simultaneously. The group uses Tor exit nodes and compromised residential routers as spray infrastructure, making source IP blocking minimally effective. The passwords used are updated seasonally and reflect awareness of common enterprise password policy requirements, typically including an uppercase letter, a number, and a special character.
Iranian APT groups: Citrix and VPN gateway spraying
Multiple Iranian state-affiliated groups have been documented conducting password spraying campaigns specifically targeting VPN gateways, Citrix NetScaler appliances, and other remote access infrastructure. The objective is remote access to enterprise networks rather than cloud identity compromise. The technique is the same: low-volume attempts across a large account list, timed to avoid lockout. These campaigns have been particularly successful against organizations with inconsistent MFA enforcement on remote access infrastructure, where a valid username and password is sufficient for VPN authentication.
CVE reference table
| Technique / Tool | Target surface | Evasion approach | Log360 detection |
|---|---|---|---|
| T1110.003 via Kerbrute | Active Directory (Kerberos) | AS-REQ pre-auth spray generates Event 4768 (0x18) not Event 4625, bypassing standard failed logon detection | Kerbrute detection rule fires on process creation. Notable account lockouts fires if any accounts reach threshold. |
| T1110.003 via Hydra | Web portals, SSH, RDP, LDAP | Parallelized multi-protocol spray; attempt rate tunable to stay below per-account thresholds | Hydra detection rule fires on process creation signatures from Sysmon Event 1. |
| Low-and-slow spray (manual or scripted) | Active Directory, M365, Azure AD | One attempt per account per hour; no tool with detectable signature; relies on Windows built-in authentication | Notable account lockouts fires when spray volume is high enough to push some accounts to threshold across the observation window. |
| MSOLSpray / o365spray | Microsoft 365, Azure AD | Distributes attempts across Microsoft's authentication endpoints; uses user-agent rotation to blend with legitimate M365 traffic | UEBA anomaly detection on M365 sign-in volume deviations. Notable account lockouts for cloud account lockout events. |
Business impact
- Dwell time before detection. Because spraying does not trigger lockout or generate the high-volume failure bursts that standard SIEM rules look for, campaigns can operate for weeks before being detected, if they are detected at all. Each day of undetected access increases the probability that the attacker has established persistence, enumerated the domain, and identified high-value targets for the next phase.
- High value targets are the objective. Spray campaigns rarely care about the first account they compromise. They care about finding the account with the right access: a domain admin, a finance executive, an IT service account with broad permissions. A spray across 10,000 accounts is a systematic search for that one account with a weak password and high privilege.
- Initial access for ransomware and APT operations. Password spraying is documented as the initial access technique in a significant portion of ransomware incidents and many APT intrusions. It is preferred precisely because it produces valid credentials, which in most environments grant significantly more access than exploitation of a vulnerability in a single system.
- Compliance exposure. Organizations subject to PCI-DSS Requirement 8.3 must implement account lockout after a defined number of failed attempts. Password spraying by definition evades lockout controls. Evidence that a spray campaign succeeded while in-scope systems lacked adequate detection and response controls can constitute a compliance failure independent of whether data was accessed.
Detecting password spraying with Log360
Log360 ships three detection rules that target password spraying specifically. Two of them detect the tools most commonly used to execute sprays (Kerbrute and Hydra) via process creation logs, providing coverage even when the spray itself generates no authentication failure events. The third detects the aggregate lockout pattern that high-volume sprays produce across multiple accounts. For these rules to fire, Sysmon process creation logs (Event 1) must be forwarding to Log360 from domain-joined endpoints, and Windows Security event logs including Event 4740 must be collected from domain controllers.
| Rule name | Severity | Platform | MITRE technique | What it detects |
|---|---|---|---|---|
| Kerbrute detection | Critical | Windows | T1110.003 | Kerbrute binary execution detected via Sysmon process creation (Event 1). Kerbrute is specifically designed to spray Kerberos AS-REQ pre-authentication, bypassing Event 4625 generation entirely. Detection via process signature is the primary and most reliable method for catching Kerbrute-based sprays, since the authentication layer itself produces no standard failed logon events. Critical severity: there is no legitimate use for Kerbrute in a production environment outside of an authorized security assessment. |
| Hydra detection | Critical | Windows | T1110.003 | Hydra binary execution detected via Sysmon process creation (Event 1). Hydra is a parallelized network login brute force and spray tool supporting over 50 protocols including LDAP, HTTP, RDP, SSH, and SMTP. When configured with a single common password and a large account list it functions as a password spray tool. Process creation detection catches Hydra regardless of which protocol it is targeting or how its attempt rate is configured. |
| Notable account lockouts | Critical | Windows | T1110.003 | Multiple account lockout events (Windows Security Event 4740) occurring across distinct accounts within a short time window. A single lockout is almost always a user mistake. Lockouts across many accounts simultaneously, especially when the source IP or workstation field is consistent across events, is the observable downstream consequence of a spray campaign that ran at a volume high enough to push some accounts past threshold. This rule catches sprays that were too aggressive to stay fully below lockout, and it is the primary detection path for spray campaigns that do not use a named tool. |
Note that slow, disciplined spray campaigns operating precisely at one attempt per account per observation window will not trigger the Notable account lockouts rule. In those cases, detection depends on either catching the spray tool at execution time (Kerbrute, Hydra) or on UEBA behavioral anomaly detection identifying the pattern of distributed low-volume failures across accounts, which deviates from the normal failure baseline for the environment.
Attack chain visibility
A password spray is rarely the end of the story. The sequences below show what the attack looks like in the logs from the first spray attempt through to post-compromise activity.
Sequence A: Kerbrute spray (no Event 4625 generated)
| Step | Log source and event | What it indicates | Time offset |
|---|---|---|---|
| 1 | Sysmon Event 1 (Process Creation) | Kerbrute binary executes with a username list file and a password argument
(e.g., kerbrute passwordspray users.txt Summer2024!). The Kerbrute
detection rule fires immediately. No authentication failure events are generated
at this stage. |
T+0 |
| 2 | Windows Security Event 4768 (DC Kerberos log) | AS-REQ requests with result code 0x18 (wrong password) appear in rapid succession across many different usernames from the same source IP. The pattern of many accounts receiving 0x18 errors from one source is the Kerberos-layer spray signature. No Event 4625 is generated. | T+0 to T+2h |
| 3 | Windows Security Event 4768 (success) + Event 4624 | A TGT is successfully issued for one of the sprayed accounts, followed by a successful network logon. The source IP from the Kerbrute execution matches the TGT requestor, linking the spray tool to the compromised account. | T+2h |
| 4 | LDAP query logs / Sysmon Event 1 | Post-compromise enumeration begins from the compromised account: net user, net group, LDAP queries for group memberships, or BloodHound collection. UEBA anomaly scores for the account spike as behavior deviates from its established baseline. | T+2h to T+6h |
Sequence B: Low-and-slow manual spray (no tool signature)
| Step | Log source and event | What it indicates | Time offset |
|---|---|---|---|
| 1 | Windows Security Event 4625 (multiple DCs) | One authentication failure per account, distributed across hundreds of accounts, from the same external source IP. The per-account failure count never exceeds one or two, so no individual lockout triggers. The Notable account lockouts rule does not yet fire at this volume. | T+0 to T+8h |
| 2 | Windows Security Event 4740 (multiple accounts) | If the spray increased pace or the attacker tried a second password on accounts that survived the first round, some accounts reach the lockout threshold. Multiple Event 4740 records from different accounts within the same 30-minute window triggers the Notable account lockouts rule. | T+8h (if spray accelerates) |
| 3 | Windows Security Event 4624 | One account produces a successful logon from the spray source IP. Logon type 3 (network) or type 10 (remote interactive) from an IP with no prior logon history for this account is the key forensic indicator of account compromise via spray. | T+8h to T+24h |
Investigation playbook
When a password spray detection rule fires in Log360, the core investigative question is identical to any brute force scenario: did any attempt succeed? A detected spray with no successful logon is a blocked attack. A detected spray with a successful logon from the same source is an account compromise that requires immediate response. The steps below structure that determination.
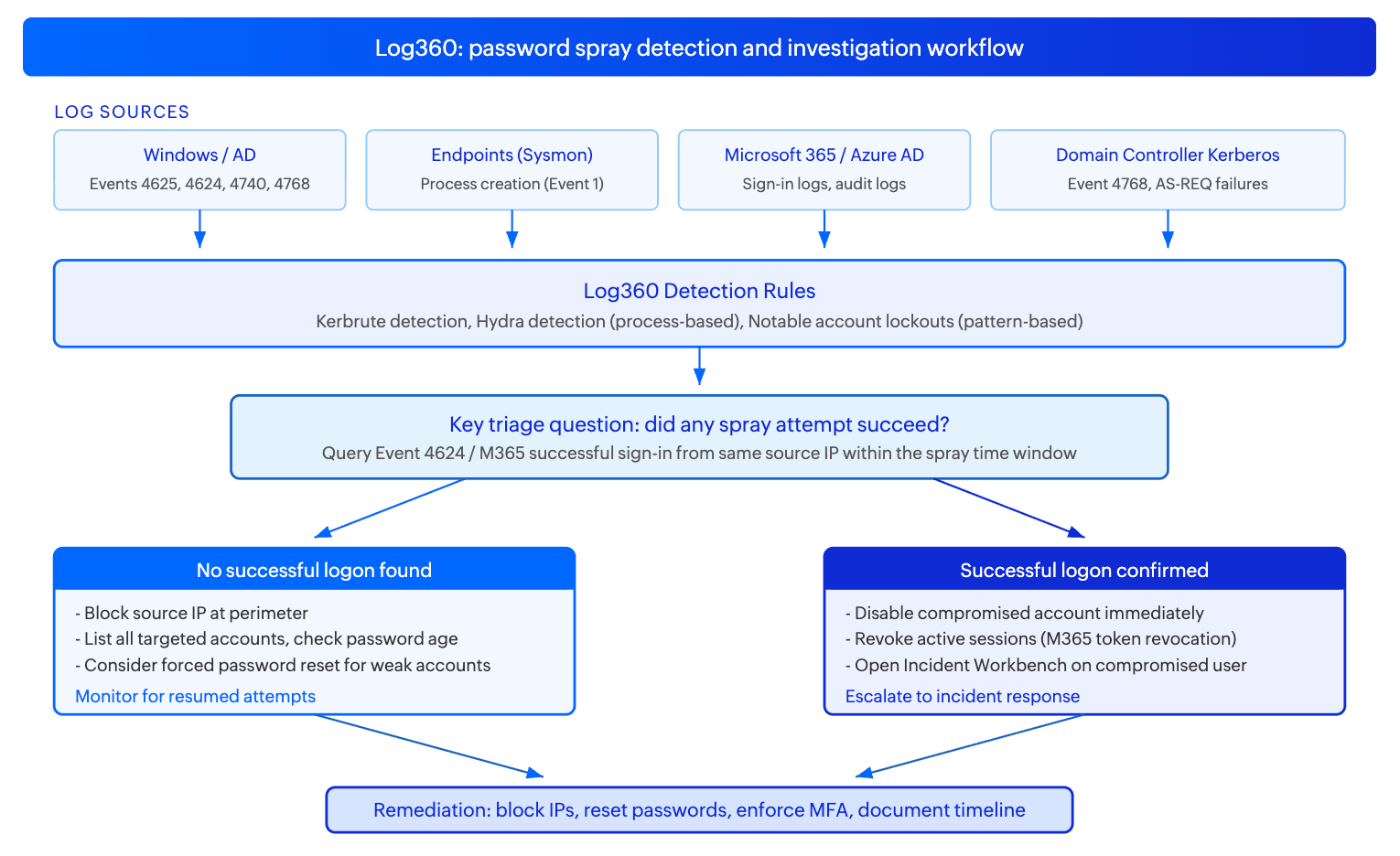
Step 1: Triage - identify which rule fired and what it means
| Rule that fired | What it means | First action |
|---|---|---|
| Kerbrute detection | A Kerberos-based spray tool ran on an internal or external host. No Event 4625 will be present. The spray may have already completed by the time this alert fires. | Identify the host where Kerbrute ran. Check Event 4768 logs on domain controllers for AS-REQ failures (result code 0x18) from that host's IP in the same time window. Then check for any successful TGT issuances (result code 0x0) from the same IP. |
| Hydra detection | Hydra executed on an internal host, suggesting a post-compromise scenario where the attacker is using a compromised machine to spray internal or external targets. | Identify the host and account. Treat the host running Hydra as compromised. Determine what credential list and target protocol Hydra was configured to attack from the Sysmon Event 1 command-line field. |
| Notable account lockouts | Multiple accounts reached the lockout threshold within the same observation window, indicating a spray that either ran too aggressively or attempted multiple passwords per account. | List all locked accounts. Identify the common source IP or workstation name across the Event 4740 records. Check if that source IP has any successful authentications (Event 4624) for any account in the same window. |
Step 2: Determine if any attempt succeeded
- Using Log360's log search, query for Event 4624 (successful logon, logon type 3 or 10) from the same source IP as the spray alert, within the spray time window and the 24 hours following it. A successful logon from the spray source is the most critical finding in the investigation.
- For Kerbrute specifically: query Event 4768 on domain controllers for TGT issuances (result code 0x0) from the same source IP as the Kerbrute execution. A successful TGT is equivalent to a successful logon for the purposes of determining compromise.
- For M365 spray indicators: query Microsoft 365 sign-in logs for successful authentications from the spray source IPs. Pay attention to whether MFA was completed or bypassed, as a successful password authentication without MFA completion on an MFA-enrolled account indicates MFA was not enforced at the relevant authentication endpoint.
Step 3: Investigate using the Incident Workbench
- If a successful logon is confirmed, click on the compromised username in the alert or log search results to open the Incident Workbench. Use the User analytics tab to pull the account's full activity overview: recent logon history, resources accessed, and UEBA risk score. A compromised spray victim will often show a sudden change in logon source geography or an immediate access to resources the account has never previously touched.
- Use the Process analytics tab if the spray originated from an internal host (indicating Kerbrute or Hydra running on a machine already inside the network). The process tree will show what spawned the spray tool, which helps determine how the attacker got onto that machine in the first place.
- Use Advanced Threat Analytics on the source IP to pull threat feed risk scores. IPs used for spray campaigns frequently appear in threat intelligence feeds as known attack infrastructure, Tor exit nodes, or compromised hosts in prior campaigns.
- Save the Incident Workbench session directly to an incident for tracking. The user activity timeline and process tree captured at this stage become the evidence record for the incident.
Step 4: Scope the exposure
- List every account that received an authentication failure from the spray source. This is the full targeted population, not just the accounts that were locked out or compromised.
- For each compromised account (successful logon from spray source), check downstream activity: LDAP queries, file server access, email access, Group Policy reads. Each of these indicates how far post-compromise activity has progressed and what data may have been accessed or exfiltrated.
- Determine whether the spray originated externally or from an internal host. An internal spray source indicates the attacker already has a foothold and is using a compromised machine for lateral expansion, which changes the scope significantly.
- Check whether multiple source IPs targeted the same account list. Distributed sprays from many IPs are a sign of an infrastructure-backed campaign rather than an opportunistic single-host attack, and typically indicate a more determined threat actor.
Step 5: Collect evidence and build the timeline
- Export the Event 4625, 4768, 4740, and 4624 records for all affected accounts from Log360's log search. This is the primary forensic record showing the spray window, accounts targeted, and the moment of compromise if one occurred.
- If Kerbrute or Hydra was detected, preserve the Sysmon Event 1 log with the full command-line field. The command line shows the password tested, the account list used, and the target, which may identify additional compromise vectors not visible in the authentication logs.
- Record all source IPs, their geographic location, ASN, and any threat intelligence context gathered from the Incident Workbench Advanced Threat Analytics tab.
- Export the investigation timeline from Log360 as the compliance artifact for NIST CSF DE.AE-5 (incident analysis) and PCI-DSS Requirement 10.7 (detecting failures of critical security controls).
Response and remediation
Immediate containment
- Disable compromised accounts immediately. If a successful logon from the spray source is confirmed for any account, disable it in Active Directory or suspend it in M365 before any further investigation. An active compromised account can be used for lateral movement while the investigation continues.
- Block the source IP at the perimeter. For external spray sources, add the IP and its associated subnet or ASN to the deny list on the perimeter firewall or VPN gateway. For distributed campaigns using many IPs, consider blocking authentication attempts from the geographic regions or ASNs the spray originated from, if those regions have no legitimate user base.
- Revoke active M365 sessions for any compromised cloud accounts. Password reset alone does not invalidate existing session tokens in M365. Use the Revoke-MgUserSignInSession PowerShell cmdlet or the equivalent admin portal action to force re-authentication.
- Force a password reset for all accounts included in the spray target list. Any account that received a spray attempt may have been compromised using a credential that did not appear in the local authentication logs, particularly if the spray operated across a longer time window than the log retention period covers.
Response actions by trigger
| Trigger | Immediate action | Owner |
|---|---|---|
| Kerbrute detection, no successful TGT found | Isolate the host running Kerbrute. Identify how the attacker accessed that host. Block the spray source IP. Review all sprayed accounts for password strength. | SOC L2 |
| Kerbrute detection with confirmed successful TGT issuance | Disable compromised account, force password reset, check all activity from the TGT in Kerberos logs, open incident. | SOC L2 + Incident Response |
| Hydra detection | Isolate the host running Hydra immediately. Treat as post-compromise. Determine what the attacker was targeting and what credentials may now be compromised. | SOC L3 + Incident Response |
| Notable account lockouts, no successful logon found | Identify spray source IP, block at perimeter, unlock affected accounts, notify account owners, review password age for all targeted accounts. | SOC L1 |
| Notable account lockouts with confirmed successful logon | Disable compromised accounts, revoke sessions, block source IP, force password reset for all targeted accounts, open incident, begin scope investigation. | SOC L2 + Incident Response |
Hardening
- Enforce MFA on all authentication paths. Password spraying succeeds when a correct password is sufficient for access. Enforcing MFA on Active Directory (via Azure AD joined devices and Conditional Access), M365, VPN, and all remote access portals breaks the attack at the point of successful credential validation. An attacker who correctly guesses a password but cannot complete MFA cannot proceed.
- Enable Microsoft Entra ID Smart Lockout for M365 environments. Smart Lockout applies lower lockout thresholds for authentication attempts from unfamiliar locations while maintaining higher thresholds for trusted locations, reducing the effectiveness of distributed sprays without increasing false positives for legitimate users.
- Deploy Azure AD Password Protection on-premises (for hybrid environments) to block common passwords and custom banned password lists at the domain controller level. This eliminates the category of seasonal common passwords that spray campaigns depend on, such as "Summer2024!" or "Company@123".
- Enable Kerberos pre-authentication logging on domain controllers to ensure Event 4768 is captured and forwarded to Log360. Without this, Kerbrute sprays are invisible at the authentication layer and detection depends entirely on the Sysmon process creation rule.
False positive tuning
| False positive source | Rules affected | Tuning strategy |
|---|---|---|
| Mass password reset during a password policy change rollout | Notable account lockouts | Organizationwide password policy changes that force resets can generate many simultaneous lockout events as users encounter the new requirements on cached credentials. Correlate Notable account lockouts alerts with change management records for scheduled policy rollouts. Create a time-bounded exception during the rollout window. The key distinguishing factor from a real spray is that policy-rollout lockouts have diverse source IPs (users authenticating from their own devices) whereas spray lockouts share a common source IP or a narrow IP range. |
| Authorized penetration testing or red team exercises | Kerbrute detection, Hydra detection, Notable account lockouts | Create a time-bounded exception scoped to the authorized assessment IP range and tied to the approved change ticket. Remove the exception immediately when the assessment window closes. Kerbrute and Hydra detection rules should never have permanent exclusions in production environments. |
| Service accounts with cached expired credentials on multiple systems | Notable account lockouts | A service account with an expired password that is cached on many systems will generate simultaneous lockout events from many different source machines when all systems attempt to re-authenticate at the same time. Distinguish from spray by checking whether the Event 4740 records share a common Source Workstation value (spray pattern) or have diverse Source Workstation values (service account credential expiry). Service account lockouts will have diverse sources; spray lockouts will have a consistent source. |


