- Free Edition
- Quick Links
- MFA
- Self-Service Password Management
- Single Sign-On
- Password Synchronizer
- Password Policy Enforcer
- Employee Self-Service
- Reporting and auditing
- Integrations
- Related Products
- ADManager Plus Active Directory Management & Reporting
- ADAudit Plus Real-time Active Directory Auditing and UBA
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- EventLog Analyzer Real-time Log Analysis & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- DataSecurity Plus File server auditing & data discovery
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- AD Free Tools Active Directory FREE Tools
Challenges with Active Directory password auditing
Hackers exploit weak Active Directory passwords through brute-force and spraying attacks, compromising domain accounts. Manual Active Directory password audit processes are time-consuming, error-prone, and fail to provide real-time insights into expiration risks, lockouts, or authentication failures. Traditional Active Directory password audit methods leave admins reactive rather than proactive.
Your complete Active Directory password audit tool
ManageEngine ADSelfService Plus eliminates manual password audit for Active Directory with automated, out-of-the-box reports. As an ideal password audit tool, it delivers real-time reports on password status, weak passwords, login attempts, and verification failures to streamline password audits into daily operations.
Powerful password audit for Active Directory
ADSelfService Plus provides essential Active Directory password audit reports that simplifies Active Directory processes, and delivers real-time insights into password health and security risks:
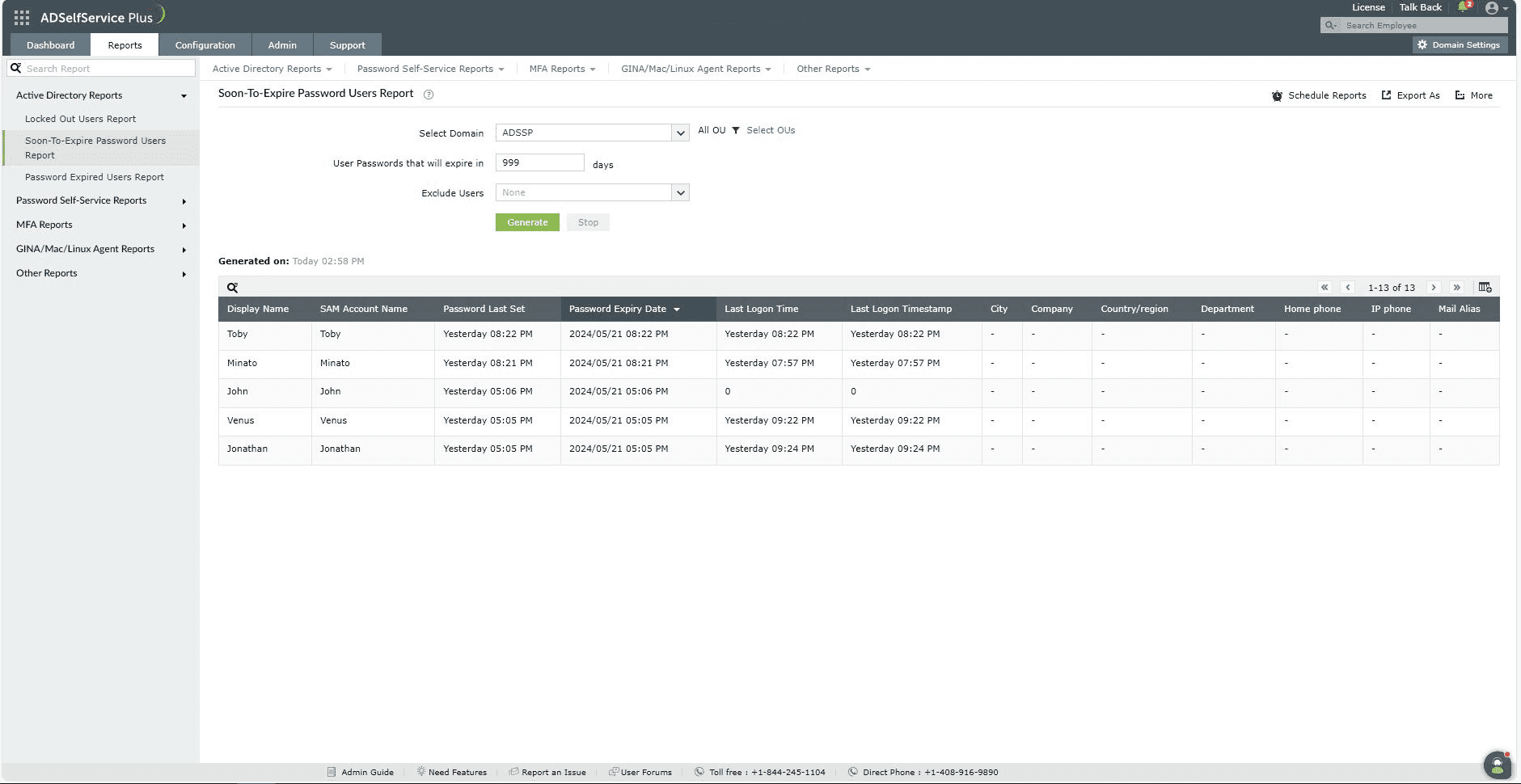
Soon-to-expire password users report
This Active Directory password audit report cites crucial details for proactive management, including:
- The display name and SAM Account Name of each Active Directory user with a soon-to-expire password.
- The date the current password was set.
- The date the current password will expire.
Admins can use this report to schedule proactive notifications and that help prevent service disruptions due to expired passwords.
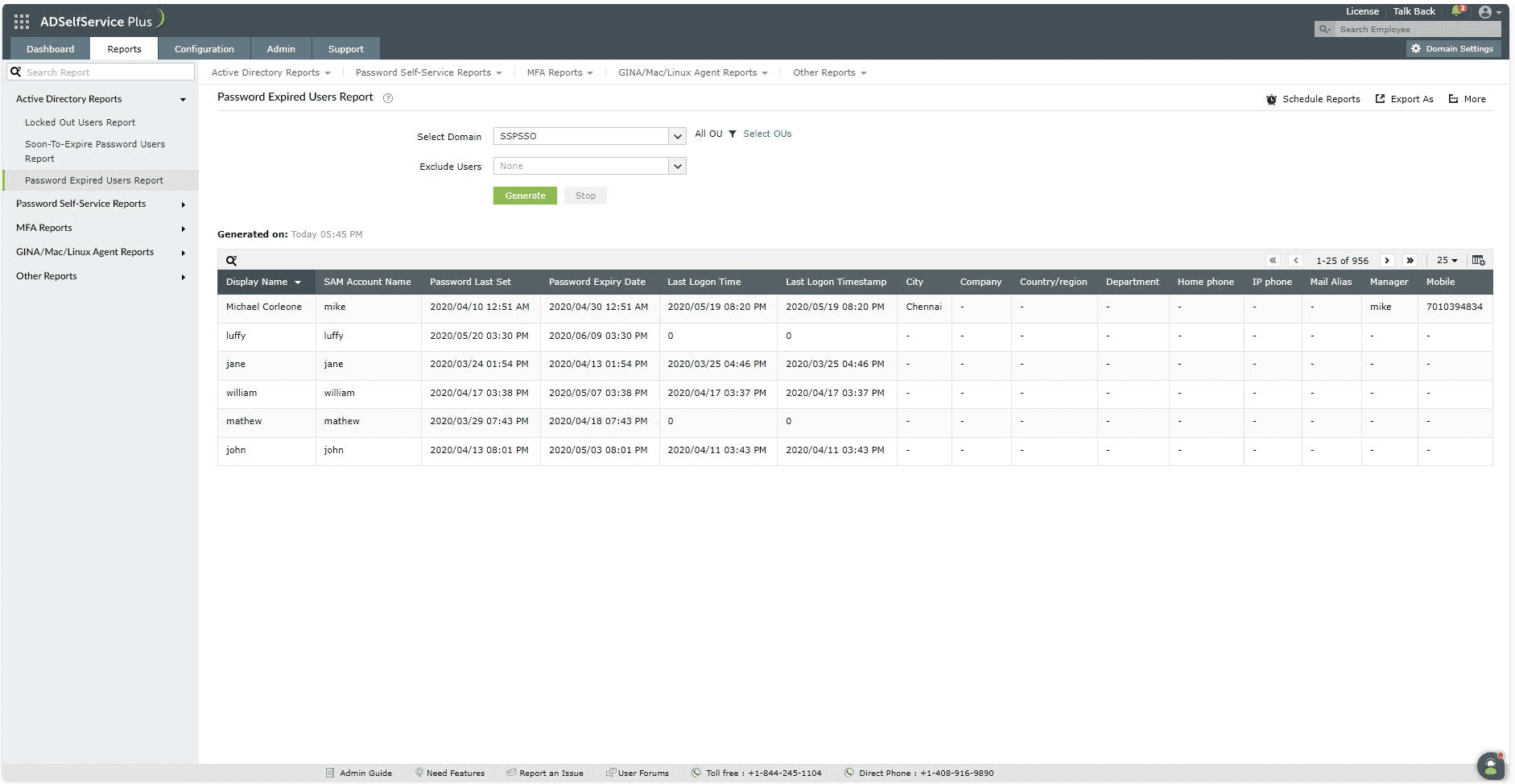
Password Expired Users Report
This password audit report for Active Directory identifies overdue accounts with:
- The display name and SAM Account Name of each Active Directory user with an expired password.
- The date on which their expired password was set.
- The date on which their password expired.
Admins can use this report to prioritize high-risk accounts, initiate bulk resets, and restore access quickly.
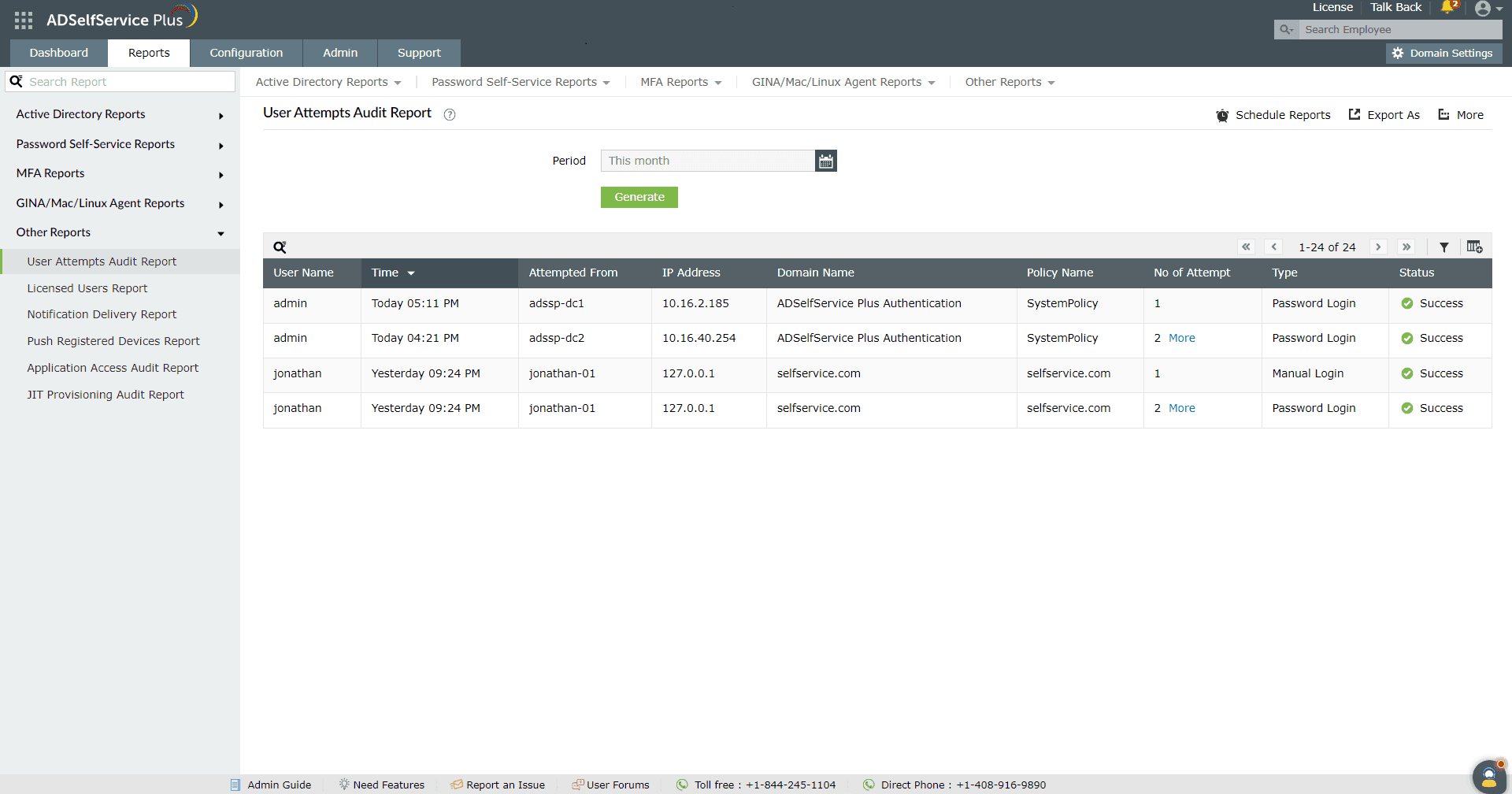
User Attempts Audit Report
This powerful Active Directory password audit report determines why a user's account was locked out by providing details on:
- The number of attempts a user makes to log in to the ADSelfService Plus self-service portal using their Active Directory password.
- The date and time of the login attempts.
- The status of the login attempts.
- The machine and IP address where the attempts originated.
Admins can use this report to quickly identify suspicious login patterns, trace attack sources by IP/machine, and unlock legitimate users.
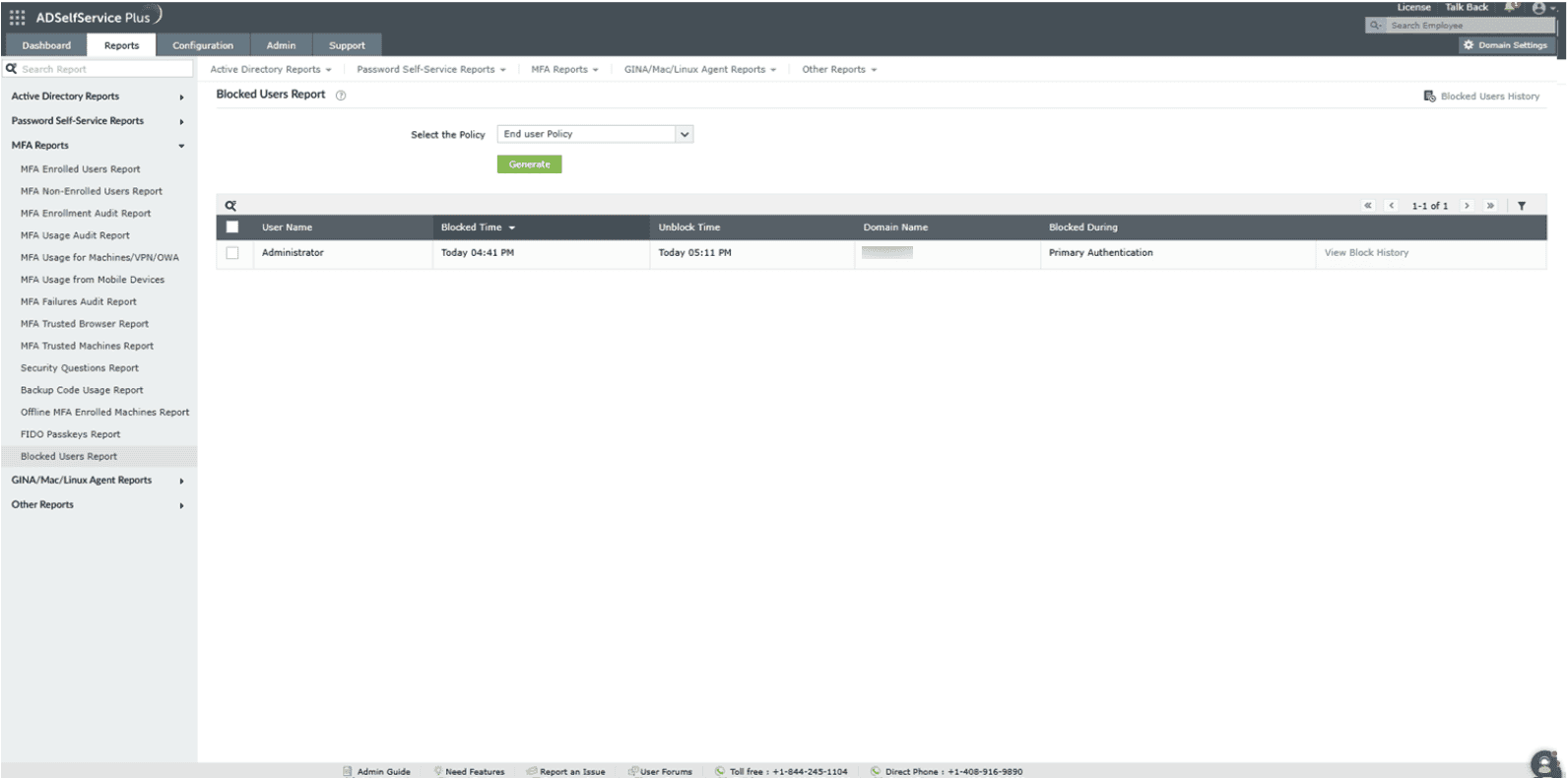
Blocked Users Report
This Active Directory password audit report generates the list of users who failed MFA verification during password resets or account unlocks, and have been blocked from accessing ADSelfService Plus. The report provides:
- Time of blocking and when the user will be unblocked.
- Domain name of the blocked accounts.
Admins can monitor MFA security effectiveness, manage block durations, and unblock users directly from this password audit Active Directory report.
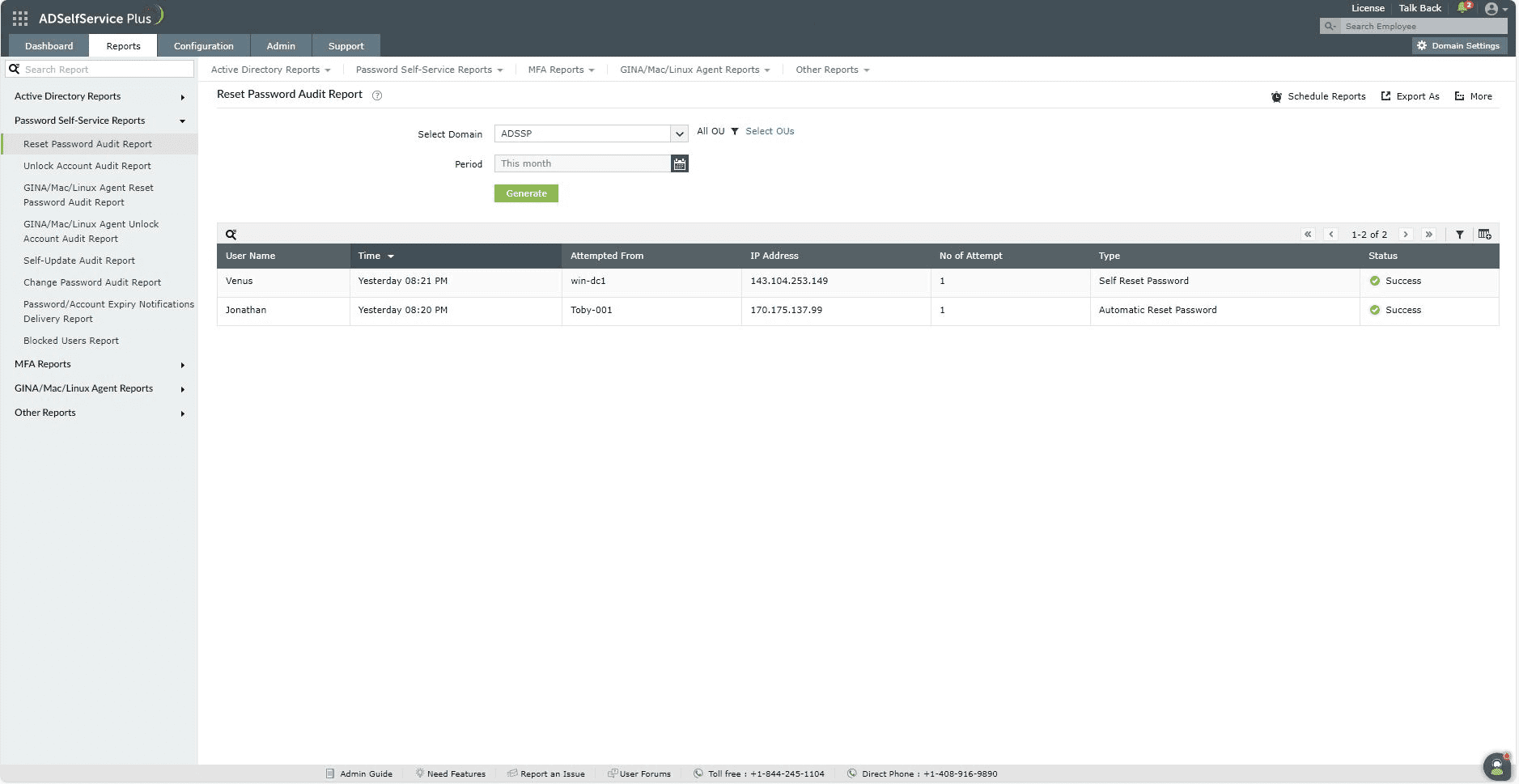
Reset password audit report
This Active Directory password audit tool tracks self-service password resets, providing comprehensive password audit active directory insights into:
- The username of those who reset passwords via ADSelfService Plus self-service portal.
- The timestamp of reset attempts.
- The number of reset attempts per username.
- The type of reset (self-service password reset or automatic password reset due to expiration).
This is optimal for Active Directory password compliance reviews and troubleshooting failed resets in your Active Directory password management workflow.
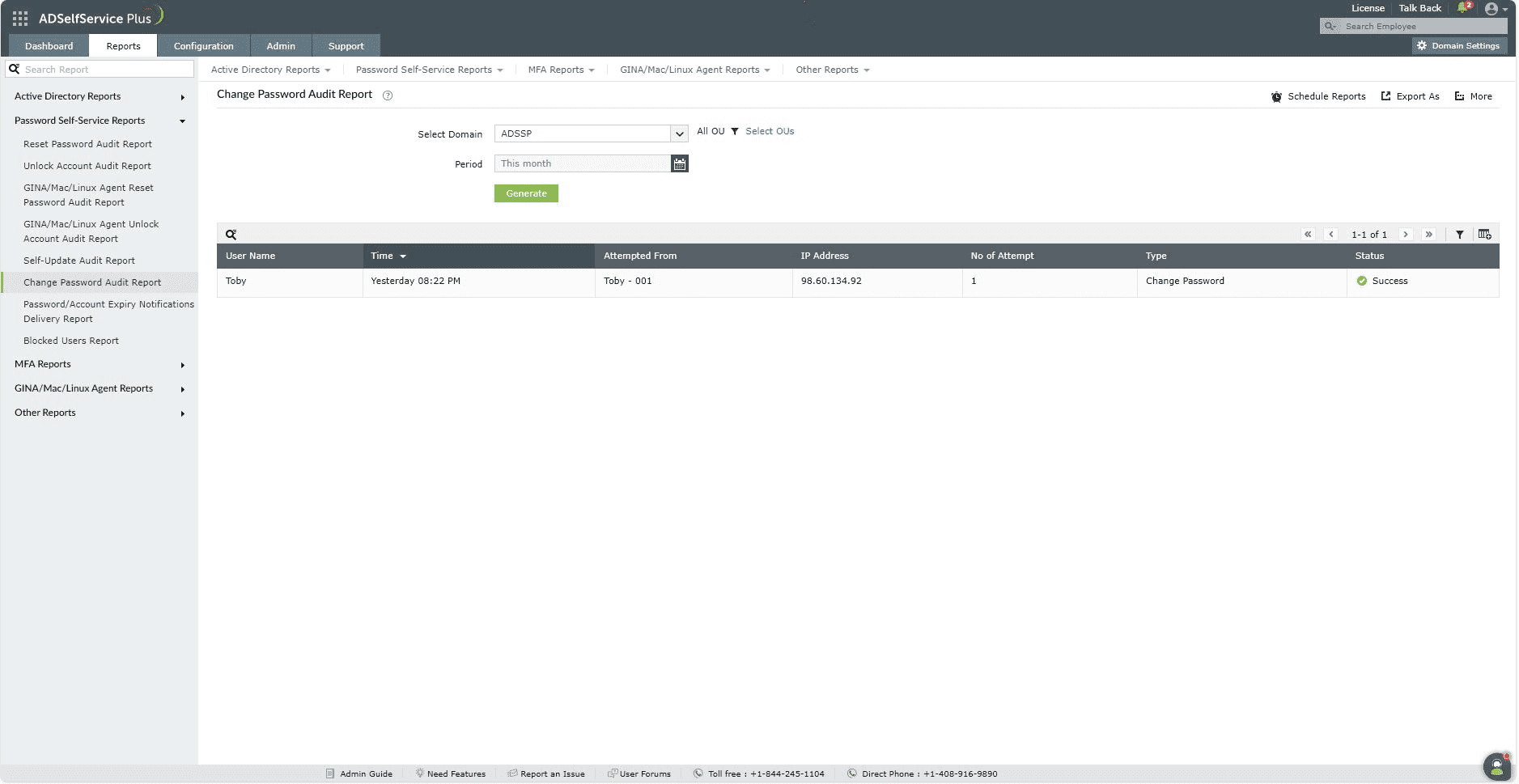
Change Password Audit Report
This essential password audit Active Directory report monitors user password changes, delivering detailed Active Directory password audit visibility into:
- The username of users who changed their passwords.
- The timestamp of the password change
- The total number of change attempts.
- The type of change (due to "User must change password at next logon" enforcement or regular user-initiated change)
This is the ideal password audit tool for tracking policy compliance and detecting unusual Active Directory password audit patterns in self-service environments.
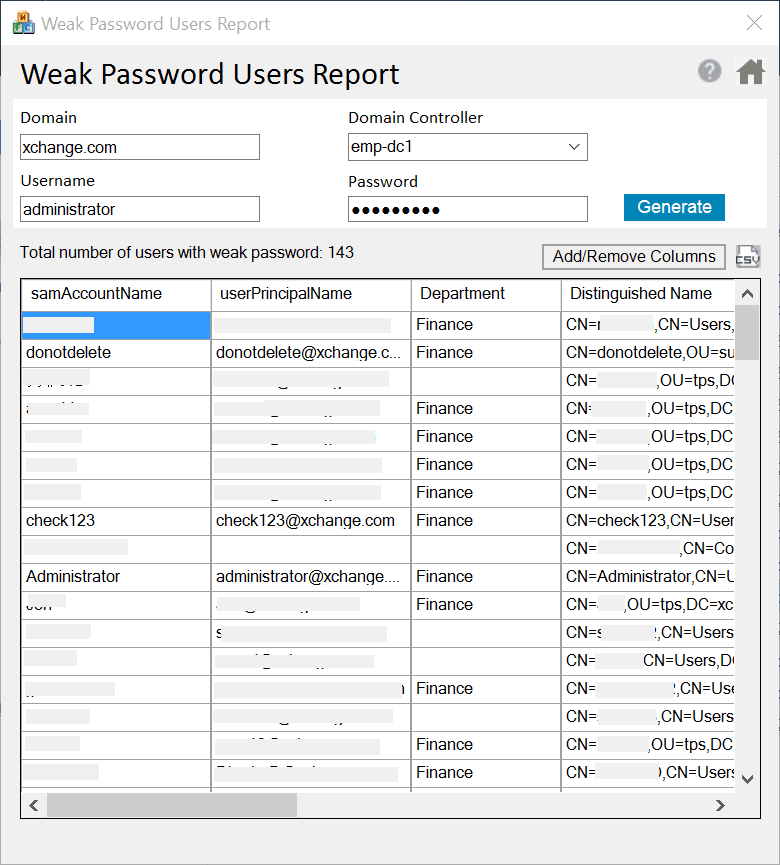
Active Directory weak password users report
The Weak Password Users Report generates a detailed list of user accounts with weak domain passwords by comparing them against a list of vulnerable and commonly used passwords.
Admins can then require these users to change their passwords the next time they log on to transform the Active Directory password audit from detection to action.
Enforce strong passwords proactively
Beyond detection, ADSelfService Plus transforms the password audit Active Directory process from defense into prevention:
- Custom advanced policies: Create unlimited policies tailored to specific organizational units, security groups, or user roles. Block keyboard sequences (qwerty), dictionary words, palindromes (abcba), repetitive characters (aaaaa), and username-derived passwords at reset time.
- Password length and history checks: Enforce minimum/maximum password lengths and prevent reuse of previous N passwords. Includes comprehensive password history tracking to maintain compliance during password audit active directory workflows.
- Real-time strength feedback: Utilize a visual password strength meter to provide instant color-coded feedback (weak/yellow, medium/orange, strong/green) during self-service resets and password changes. This guides users to create compliant passwords on their first attempt.
- Seamless hybrid coverage: Apply a consistent policy across Active Directory domains, Microsoft 365/Azure AD, and more than 100 connected SaaS applications. This ensures uniform Active Directory password audit protection in mixed environments.
Key benefits of an Active Directory password audit using ADSelfService Plus
- Streamlined auditing: The automated Active Directory password audit replaces manual log reviews.
- Improved password security: Immediate remediation insights from reports that monitor locked and vulnerable accounts, forced password resets, and enforced password policies.
- Operational efficiency: Ties the Active Directory password audit tool into self-service workflows for faster resolutions.
FAQs
A password audit evaluates how secure user passwords are and whether they comply with organizational security policies. It helps identify vulnerabilities such as weak passwords, reused credentials, dormant accounts, and policy misconfigurations.
An Active Directory password audit enables IT teams to:
- Detect passwords vulnerable to brute-force or dictionary attacks
- Ensure compliance with regulatory standards
- Reduce the risk of credential-based attacks
- Validate that password policies are enforced effectively
By performing a password audit in Active Directory, organizations can proactively strengthen their identity security posture and prevent unauthorized access before a breach occurs.
In Active Directory, a password history cannot be viewed in plain text for security reasons. Windows stores passwords as one-way cryptographic hashes, making it impossible to see previous passwords directly. However, you can enforce and verify password history policies through Group Policy.
To check password history settings:
- Open Group Policy Management Console (GPMC).
- Navigate to: Computer Configuration → Policies → Windows Settings → Security Settings → Account Policies → Password Policy
- Review the Enforce password history setting to see if users have been prevented from using previous passwords.
For deeper insights—such as identifying weak passwords and reused credentials, or policy violations—administrators rely on an Active Directory password audit tool like ADSelfService Plus.
Passwords are not stored in readable form in Active Directory. Instead, Active Directory stores passwords as hashed values using secure cryptographic algorithms. This design ensures that even administrators cannot view user passwords.
During authentication, the entered password is hashed and compared against the stored hash. Because of this architecture, password visibility is impossible—but password security can still be assessed through a password audit.
An Active Directory password audit analyzes password hashes and policy adherence to uncover risks without revealing actual credentials, making it a safe and effective approach to improving security.
Highlights of ADSelfService Plus
Password self-service
Unburden Windows AD users from lengthy help desk calls by empowering them with self-service password reset and account unlock capabilities.
Multi-factor authentication
Enable context-based MFA with 20 different authentication factors for endpoint, application, VPN, OWA, and RDP logins.
One identity with single sign-on
Get seamless one-click access to more than 100 cloud applications. With enterprise single sign-on (SSO), users can access all their cloud applications using their Windows AD credentials.
Password and account expiry notifications
Notify Windows AD users of their impending password and account expiry via email and SMS notifications.
Password synchronization
Synchronize Windows AD user passwords and account changes across multiple systems automatically, including Microsoft 365, Google Workspace, IBM iSeries, and more.
Password policy enforcer
Strong passwords resist various hacking threats. Enforce Windows AD users to adhere to compliant passwords by displaying password complexity requirements.










